All posts tagged "malware"
-

 132Malware
132MalwareMiddle Eastern hackers are using this phishing technique to infect political targets with Trojan malware
‘Moonlight’ group is likely to be involved in cyberespionage, warns Vectra Networks. A hacking group is conducting cyberespionage against targets in the...
-

 328Geek
328GeekMicrosoft Security Essentials Installer Leads to Support Scam Malware
Beware of not so old yet widespread Microsoft Security Essentials Scam that tells users to call a support number that instructs users to...
-

 225Hacked
225HackedTop 10 Most Dangerous Malware That Can Cripple Your Device
Short Bytes: Check Point has released the list of the most dangerous malware that are most prevalent in the world. This list was topped by...
-
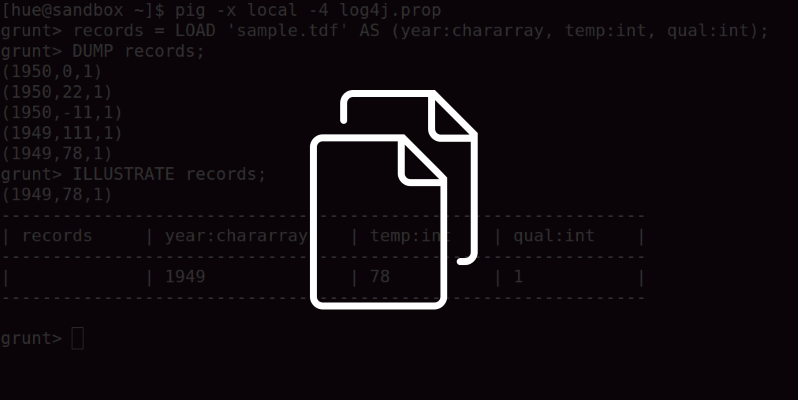
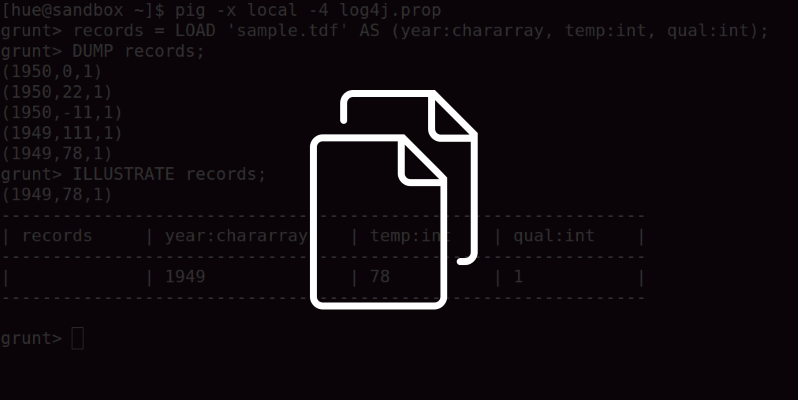 219Data Security
219Data SecurityFakeFile Trojan Opens Backdoors on Linux Computers, Except openSUSE
Trojan targets desktops, not servers or IoT devices. Malware authors are taking aim at Linux computers, more precisely desktops and not servers, with...
-
 265Data Security
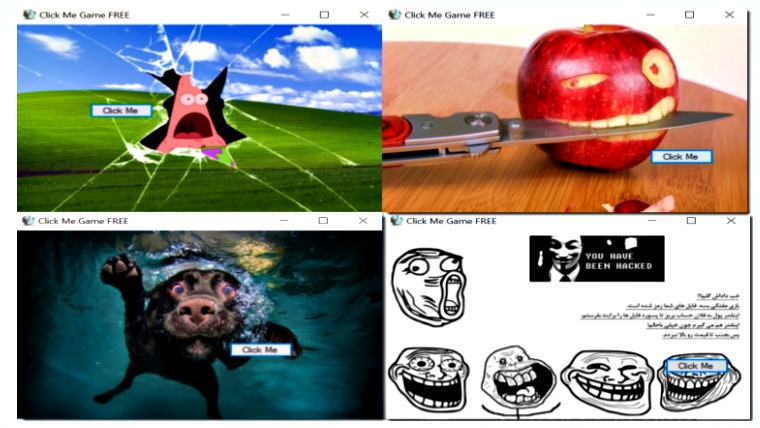
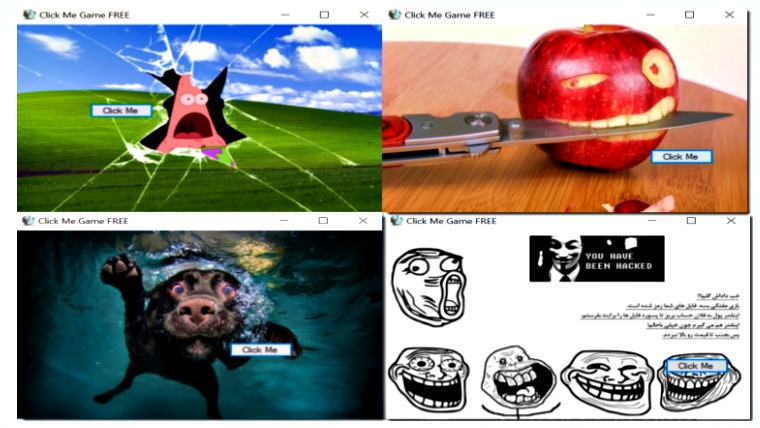
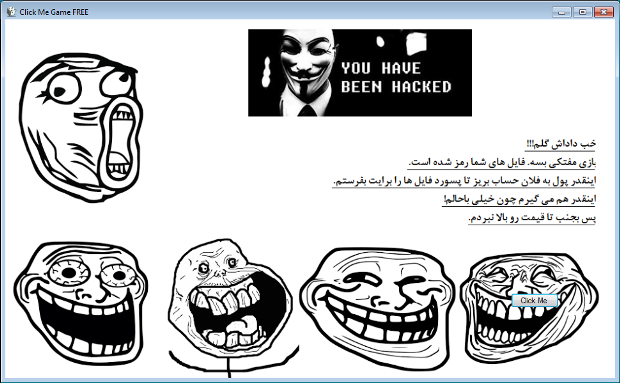
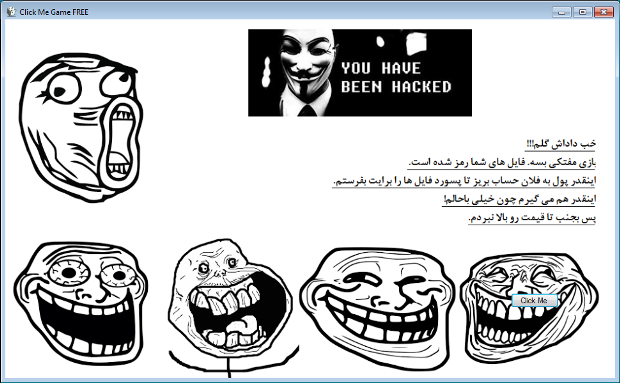
265Data SecurityNew Ransomware Asks User to Play Click Me Game while Encrypting Data
The click me game malware is developed by Iranian hacker as its readme file is written in Persian. Karsten Hahn, a malware...
-
 162Data Security
162Data SecurityIn-Development Ransomware Encrypts while Pretending to be a Click Me Game
Yesterday, GData malware analyst Karsten Hahn discovered an in-development ransomware disguised as a click me game. When executed the ransomware will launch a screen that...
-
 76Malware
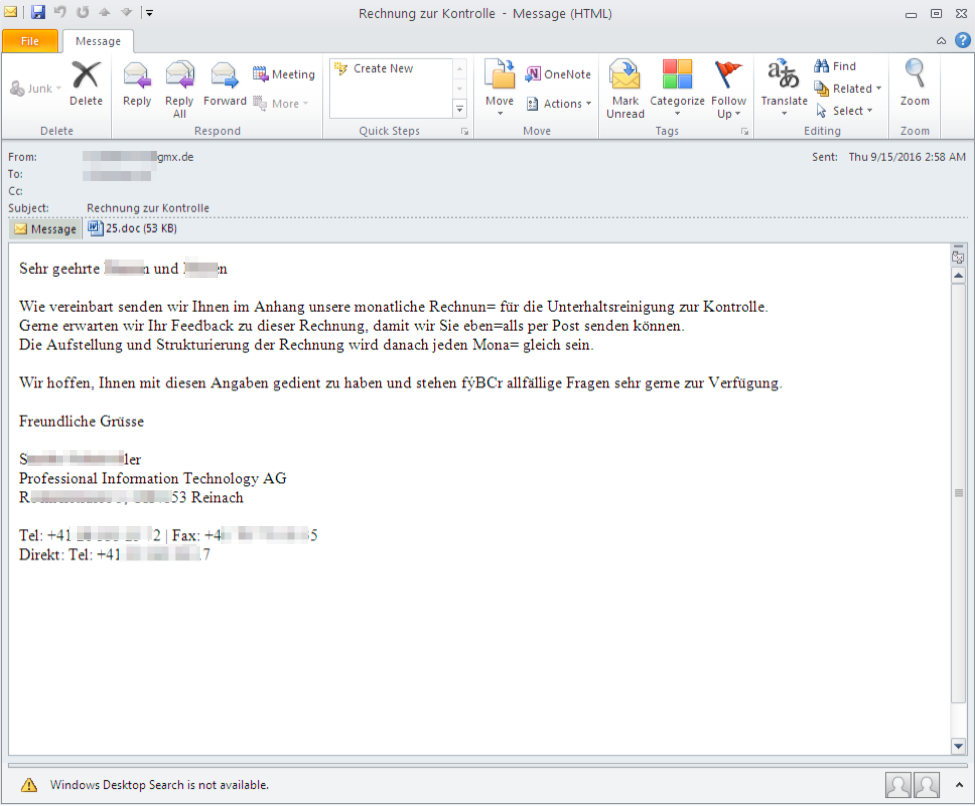
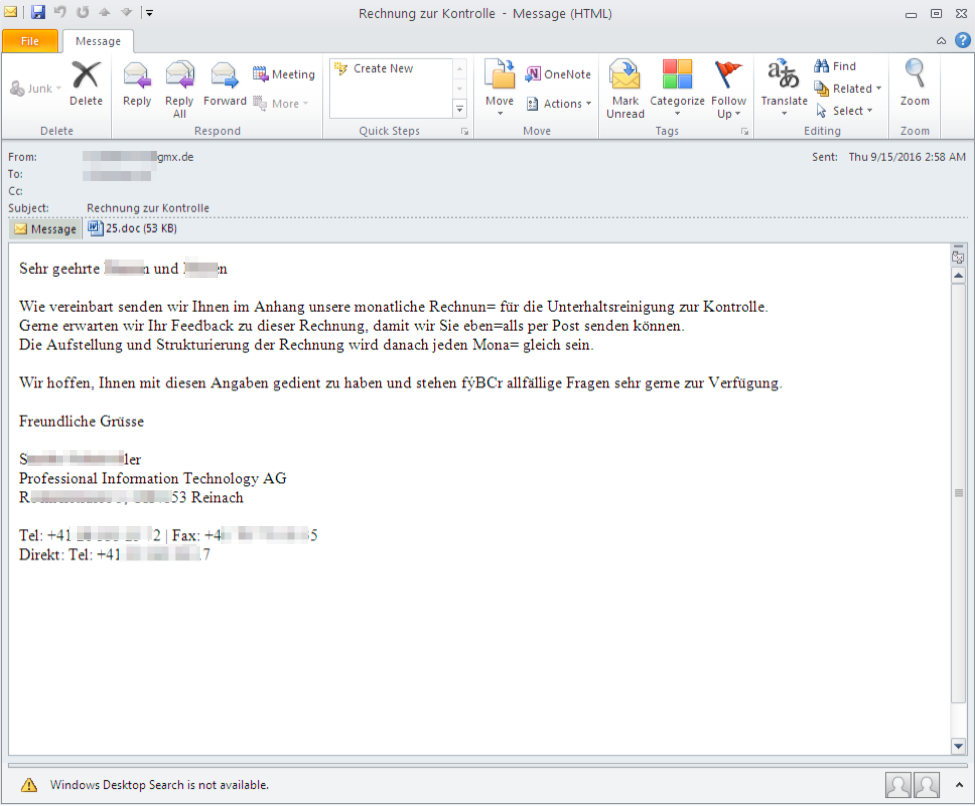
76Malware“O’zapft is!”: Cyber criminals tap into German-speaking targets in time for Oktoberfest
“Common sense” is an oft-prescribed remedy for email-based malware threats: Don’t click on unknown links, don’t enable macros in documents from unknown...
-
 134Incidents
134IncidentsFlaw in Intel chips could make malware attacks more potent
“Side channel” in Haswell CPUs lets researchers bypass protection known as ASLR. Researchers have devised a technique that bypasses a key security protection...
-
 285Vulnerabilities
285VulnerabilitiesMagento Malware Uses Steganography to Steal Payment Card Data
Malware hides credit card data inside image files. Hackers are collecting payment card data from Magento stores, hiding the stolen data inside...
-
 85Data Security
85Data SecurityNRSC hack – financial data of donors were sent to a Russian domain
NRSC hack – A platform used by the National Republican Senatorial Committee for the donations was hacked and donors’ financial data have...
-
 127Data Security
127Data SecurityCrooks Leverage Explosives to Rob ATMs Because Malware Is Overrated
Who needs complicated malware when you have dynamite.Criminals like to use explosives to break into ATMs, rather than deploy malware, a recent...
-

 281Geek
281GeekNew Android Malware Asks for Selfies; Steals Credit Card Details
Your Selfie can Land You In Great Trouble — Researchers Discover New Malware that Asks for User’s Selfie to Carry Out Identity...
-

 274Cyber Crime
274Cyber CrimeCriminals Use Explosives to Crack Open ATMs; 492 Attacked So Far
Forget ATM malware, criminals are using explosive to crack ATM machines and steal thousands of Euros in Europian countries. It is definitely...
-

 340News
340NewsDangerous Pork Explosion backdoor found in Android Devices
Android Smartphones from Foxconn Manufacturer Plagued with Dangerous Security Flaw known as Pork Explosion. Android operating system has become quite vulnerable to...
-

 129Incidents
129IncidentsBeware of all-powerful DDoS malware infecting cellular gateways, feds warn
Sierra Wireless confirms that devices it manufactures were infected by Mirai. This week, the US government-backed ICS-CERT warned that the troubling new generation...
-

 80Data Security
80Data SecurityAndroid Banking Trojan Asks for Selfie With Your ID
In the first half of 2016 we noticed that Android banking Trojans had started to improve their phishing overlays on legitimate financial apps to...
-
 310Data Security
310Data SecurityCryPy Ransomware Encrypts Each File Individually with a Special Key
New Ransomware CryPy Can Encrypt Each File Individually with a Special Key — The C&C of this ransomware is hosted on a hacked...
-

 137Vulnerabilities
137VulnerabilitiesExecutable Files, Old Exploit Kits Top Most Effective Attack Methods
Researchers for the new ‘Hacker’s Playbook’ analyzed 4 million breach methods from an attacker’s point of view to gauge the real risks...
-
 323Data Security
323Data SecurityWinRar and TrueCrypt Installer Dropping Malware on Users’ PCs
Be careful when you download WinRar or TrueCrypt installer – Researchers have found several websites distributing malware infected files for both installers. A...
-

 332Data Security
332Data SecurityCerber Ransomware Encrypts Files, Kills Database Process Servers
You may know Cerberus often called the “hound of Hades”, a monstrous multi-headed dog but in this case, Cerber is one nasty...
-

 364Data Security
364Data SecurityMac Malware Can Spy on You Through Webcam: Ex-NSA Hacker
If you are a Mac user you need to be extra careful – Other than covering your webcam there is a tool...






