Featured News
-
 4.9KMalware
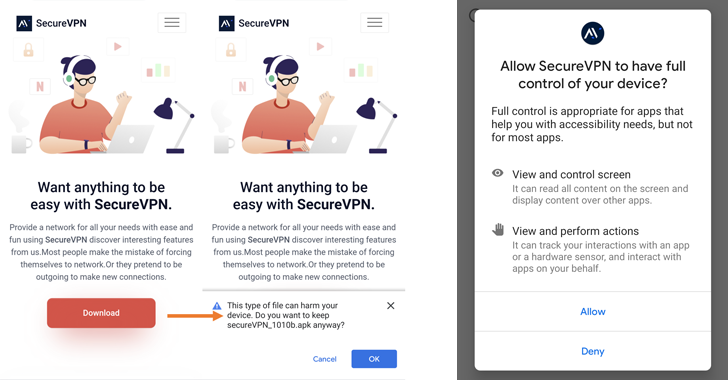
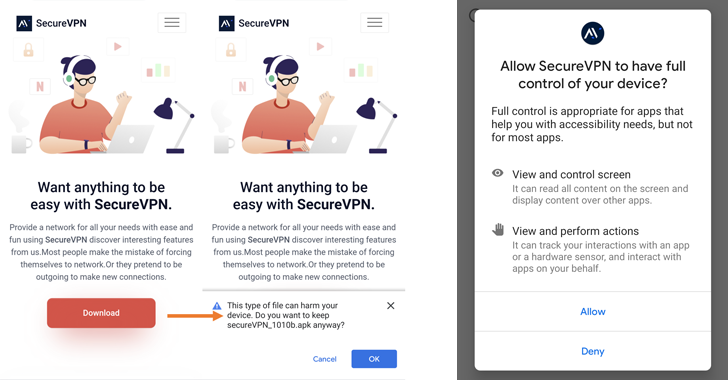
4.9KMalwareBahamut Cyber Espionage Hackers Targeting Android Users with Fake VPN Apps
The cyber espionage group known as Bahamut has been attributed as behind a highly targeted campaign that infects users of Android devices...
-

 4.0KScams
4.0KScams10 tips to avoid Black Friday and Cyber Monday scams
It pays not to let your guard down during the shopping bonanza – watch out for some of the most common scams...
-
Malware
This Android File Manager App Infected Thousands of Devices with SharkBot Malware
The Android banking fraud malware known as SharkBot has reared its head once again on the official Google Play Store, posing as...
-
 700Malware
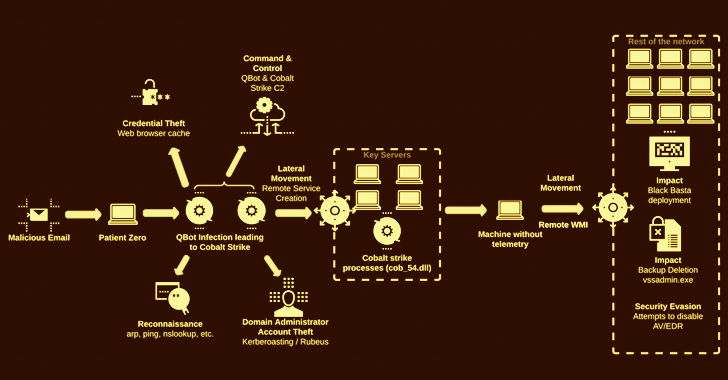
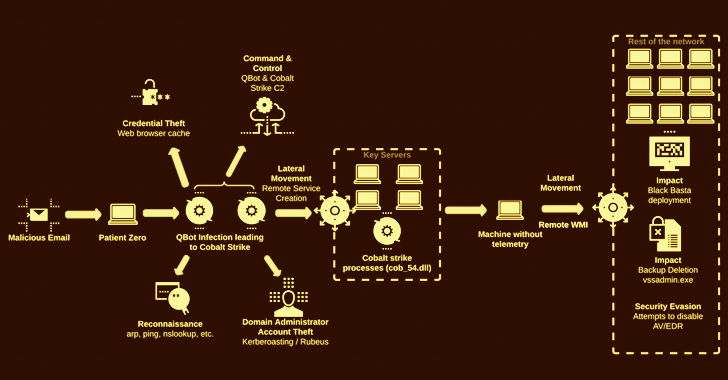
700MalwareBlack Basta Ransomware Gang Actively Infiltrating U.S. Companies with Qakbot Malware
Companies based in the U.S. have been at the receiving end of an “aggressive” Qakbot malware campaign that leads to Black Basta...
-

 2.8KData Security
2.8KData SecurityMost exploited API Vulnerabilities in 2022
It is common knowledge that maintaining a high level of cyber security has rapidly become one of the top priorities for businesses...
-
 5.3KVulnerabilities
5.3KVulnerabilitiesUse After Free vulnerability in Linux Kernel allows Privilege Escalation. Patch your kernel
Redhat has just just published a risk advisory about a vulnerability in the Linux Kernel that allows for local privilege escalation. This...
-
 1.2KMalware
1.2KMalwareDucktail Malware Operation Evolves with New Malicious Capabilities
The operators of the Ducktail information stealer have demonstrated a “relentless willingness to persist” and continued to update their malware as part...
-
 1.1KMalware
1.1KMalwareChrome Extension Deploy Windows Malware to Steal Cryptocurrency and Clipboard Contents
In order to steal cryptocurrency and clipboard contents, ViperSoftX was detected by the security analysts at Avast, a Windows malware that is...
-
 2.5KMalware
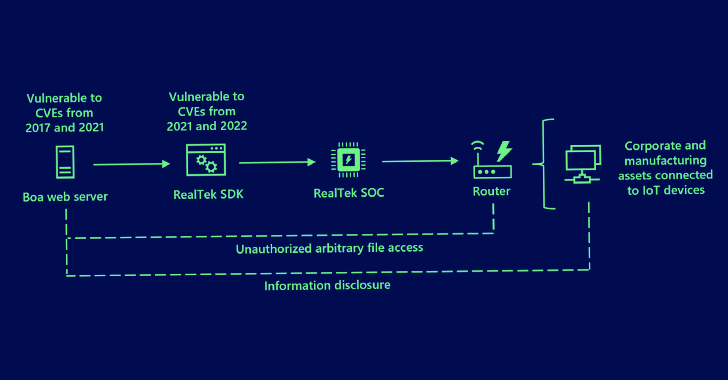
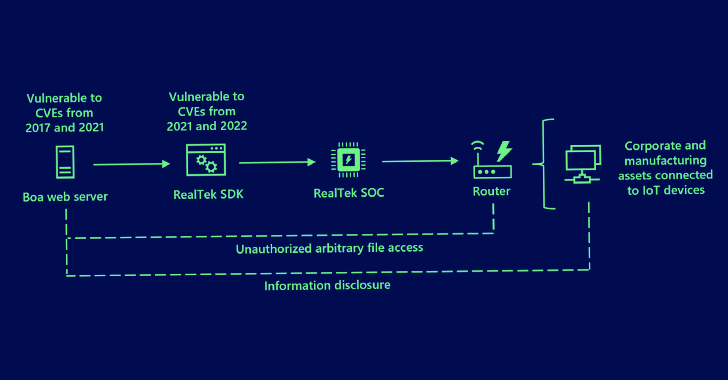
2.5KMalwareHackers Exploiting Abandoned Boa Web Servers to Target Critical Industries
Microsoft on Tuesday disclosed the intrusion activity aimed at Indian power grid entities earlier this year likely involved the exploitation of security...
-

 2.3KVulnerabilities
2.3KVulnerabilitiesVulnerabilities in Mastodon, allow to download or delete all the files on the server, including those exchanged via Direct Messages and change everyone’s profile image
Mastodon has been under the limelight as a result of the exodus of former Twitter users who left the platform in response...
-

 3.3KMalware
3.3KMalwareThis Malware Installs Malicious Browser Extensions to Steal Users’ Passwords and Cryptos
A malicious extension for Chromium-based web browsers has been observed to be distributed via a long-standing Windows information stealer called ViperSoftX. Czech-based...
-

 2.7KData Security
2.7KData Security3 Techniques that allow bypassing phishing emails through Cisco Secure Email Gateway and are being actively used by ransomware gangs
The following techniques have been made public by a researcher who wishes to remain anonymous. They can be used to bypass certain of...
-

 2.8KMalware
2.8KMalwareResearchers Warn of Cyber Criminals Using Go-based Aurora Stealer Malware
A nascent Go-based malware known as Aurora Stealer is being increasingly deployed as part of multiple campaigns designed to steal sensitive information...
-

 3.4KMalware
3.4KMalwareLuna Moth Gang Invests in Call Centers to Target Businesses with Callback Phishing Campaigns
The Luna Moth campaign has extorted hundreds of thousands of dollars from several victims in the legal and retail sectors. The attacks...
-

 1.9KRansomware
1.9KRansomwareHackers Use New Ransomware that Encrypts Files & Steals Tokens From Victim’s Machine
Security researchers at Cyble recently identified that the authors of ransomware now have access to a brand new malicious tool – AXLocker...
-

 4.5KCyber Attack
4.5KCyber AttackDaixin Ransomware Gang Steals 5 Million AirAsia Passengers’ and Employees’ Data
The cybercrime group called Daixin Team has leaked sample data belonging to AirAsia, a Malaysian low-cost airline, on its data leak portal....
-

 858Malware
858MalwareGoogle Wins Lawsuit Against Russians Linked to Blockchain-based Glupteba Botnet
Google has won a lawsuit filed against two Russian nationals in connection with the operation of a botnet called Glupteba, the company...
-

 2.2KMalware
2.2KMalwareChinese Hackers Using 42,000 Phishing Domains To Drop Malware On Victims Systems
An extensive phishing campaign targeting businesses in numerous upright markets, including retail, was discovered by Cyjax recently in which the attackers exploited...
-

 608Data Breach
608Data BreachIndian Government Publishes Draft of Digital Personal Data Protection Bill 2022
The Indian government on Friday released a draft version of the much-awaited data protection regulation, making it the fourth such effort since...
-
 971Malware
971MalwareMicrosoft Warns of Hackers Using Google Ads to Distribute Royal Ransomware
A developing threat activity cluster has been found using Google Ads in one of its campaigns to distribute various post-compromise payloads, including...
The Latest
-
 Malware
MalwareKimsuky Using TRANSLATEXT Chrome Extension to Steal Sensitive Data
-
 Vulnerabilities
VulnerabilitiesGitLab Releases Patch for Critical CI/CD Pipeline Vulnerability and 13 Others
-
 Malware
Malware8220 Gang Exploits Oracle WebLogic Server Flaws for Cryptocurrency Mining
-
 Vulnerabilities
VulnerabilitiesResearchers Warn of Flaws in Widely Used Industrial Gas Analysis Equipment
-
 Malware
MalwareRust-Based P2PInfect Botnet Evolves with Miner and Ransomware Payloads
-
 Vulnerabilities
VulnerabilitiesPrompt Injection Flaw in Vanna AI Exposes Databases to RCE Attacks
-
 Malware
MalwareRussian National Indicted for Cyber Attacks on Ukraine Before 2022 Invasion
-
 Vulnerabilities
VulnerabilitiesCritical SQLi Vulnerability Found in Fortra FileCatalyst Workflow Application
-
 Vulnerabilities
VulnerabilitiesExploit Attempts Recorded Against New MOVEit Transfer Vulnerability – Patch ASAP!
-
 Vulnerabilities
VulnerabilitiesPractical Guidance For Securing Your Software Supply Chain
-
 Vulnerabilities
VulnerabilitiesApple Patches AirPods Bluetooth Vulnerability That Could Allow Eavesdropping
-
 Malware
MalwareNew Credit Card Skimmer Targets WordPress, Magento, and OpenCart Sites
-
 Malware
MalwareNew Medusa Android Trojan Targets Banking Users Across 7 Countries
-
 Vulnerabilities
VulnerabilitiesOver 110,000 Websites Affected by Hijacked Polyfill Supply Chain Attack
-
 Vulnerabilities
VulnerabilitiesNew Attack Technique Exploits Microsoft Management Console Files
-
 Vulnerabilities
VulnerabilitiesHow to Cut Costs with a Browser Security Platform
-
 Malware
MalwareMultiple WordPress Plugins Compromised: Hackers Create Rogue Admin Accounts
-
 Vulnerabilities
VulnerabilitiesGoogle Introduces Project Naptime for AI-Powered Vulnerability Research
-
 Vulnerabilities
VulnerabilitiesCritical RCE Vulnerability Discovered in Ollama AI Infrastructure Tool
-
 Vulnerabilities
VulnerabilitiesRedJuliett Cyber Espionage Campaign Hits 75 Taiwanese Organizations




