Featured News
-
 3.9KData Breach
3.9KData BreachLastPass Suffers Another Security Breach; Exposed Some Customers Information
Popular password management service LastPass said it’s investigating a second security incident that involved attackers accessing some of its customer information. “We...
-

 3.2KData Breach
3.2KData BreachFrench Electricity Provider Fined for Storing Users’ Passwords with Weak MD5 Algorithm
The French data protection watchdog on Tuesday fined electricity provider Électricité de France (EDF) €600,000 for violating the European Union General Data...
-

 577Data Breach
577Data BreachAustralia Passes Bill to Fine Companies up to $50 Million for Data Breaches
The Australian government has passed a bill that markedly increases the penalty for companies suffering from serious or repeated data breaches. To...
-

 921Data Security
921Data SecuritySeventy thousand individuals who police believe may have been victims of phone scams are receiving messages with instructions on what they should do next
Over 70,000 individuals are receiving text messages from the police informing them that they have been victims of online banking frauds and...
-

 4.7KVulnerabilities
4.7KVulnerabilitiesCritical RCE vulnerability in Oracle Fusion Middleware is being exploited by adversaries in the wild
Oracle Access Manager (OAM) contains a pre-authentication RCE vulnerability (CVE-2021-35587) that was fixed in January 2022. However, the vulnerability is still being...
-

 1.1KVulnerabilities
1.1KVulnerabilitiesNew Acer UEFI firmware vulnerability (CVE-2022-4020) makes Antivirus or EDR useless in Acer laptops
The security researchers at ESET found a new high-risk vulnerability in the UEFI firmware of Acer computers. Because to a security flaw...
-

 1.8KVulnerabilities
1.8KVulnerabilitiesNew Flaw in Acer Laptops Could Let Attackers Disable Secure Boot Protection
Acer has released a firmware update to address a security vulnerability that could be potentially weaponized to turn off UEFI Secure Boot...
-

 607Malware
607MalwareHackers Using Trending TikTok ‘Invisible Challenge’ to Spread Malware
Threat actors are capitalizing on a popular TikTok challenge to trick users into downloading information-stealing malware, according to new research from Checkmarx....
-

 3.2KData Breach
3.2KData BreachIrish Regulator Fines Facebook $277 Million for Leak of Half a Billion Users’ Data
Ireland’s Data Protection Commission (DPC) has levied fines of €265 million ($277 million) against Meta Platforms for failing to safeguard the personal...
-

 4.5KIncidents
4.5KIncidentsA hacker has posted data of 5.3 million Twitter accounts on a Raidforums, while another researcher confirmed another hack involving 100 million Twitter accounts
Earlier we published an article that provided details of a data breach that occurred on Twitter and affected 5.4 million accounts. Now, the...
-

 1.1KData Security
1.1KData SecurityWhat should you do if your WhatsApp number is leaked by cybercriminals in the recent WhatsApp hack
A gang of hackers has been responsible for the hacking of WhatsApp in recent days, which resulted in the disclosure of a...
-

 3.5KVulnerabilities
3.5KVulnerabilitiesResearchers Detail AppSync Cross-Tenant Vulnerability in Amazon Web Services
Amazon Web Services (AWS) has resolved a cross-tenant vulnerability in its platform that could be weaponized by an attacker to gain unauthorized...
-

 1.5KMalware
1.5KMalwareAll You Need to Know About Emotet in 2022
For 6 months, the infamous Emotet botnet has shown almost no activity, and now it’s distributing malicious spam. Let’s dive into details...
-

 2.3KVulnerabilities
2.3KVulnerabilitiesNew Zero Day Heap buffer overflow in GPUVulnerability in Google Chrome
Google sent out emergency patches for its Chrome web browser on Thursday to fix a security hole that the company says is...
-

 1.5KIncidents
1.5KIncidentsIranian hackers broke into Israeli security agency to steal surveillance footage of twin bombings in Jerusalem
Iranian hackers broke into a key Israeli security organization on Wednesday, stole surveillance tape that caught one of the twin explosions that...
-

 5.0KRansomware
5.0KRansomwareHackers Rewritten The RansomExx Ransomware in Rust Language To Evade Detection
There has recently been a discovery made by IBM Security X-Force Threat Researchers regarding a new variant of ransomware known as RansomExx...
-

 691How To
691How ToKnow your payment options: How to shop and pay safely this holiday season
'Tis the season for shopping and if you too are scouting for bargains, make sure to keep your money safe when snapping...
-

 3.8KData Security
3.8KData SecurityAustralian government is looking to hire hackers for its “hack back” program to disrupt ransomware gangs
Recent data breaches have driven fast reforms to Australia’s cybersecurity and data protection rules, and the most recent development looks to be...
-
 476Tutorials
476TutorialsTop 8 Free Tools for security testing and audit of your Kubernetes cluster in 2022
Docker is a technology for containerization, while Kubernetes is a tool for orchestrating container deployments. In the subsequent subsections, we will discuss...
-
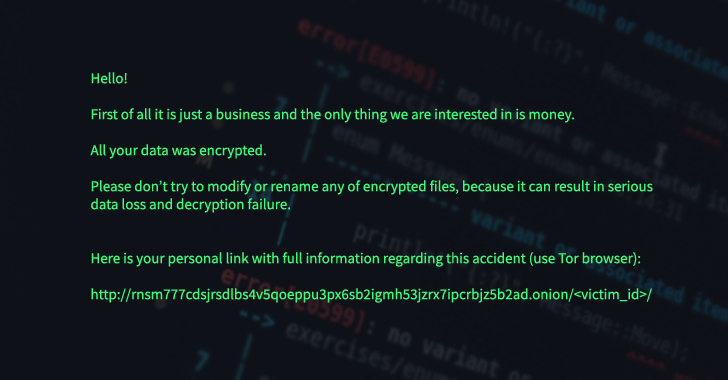
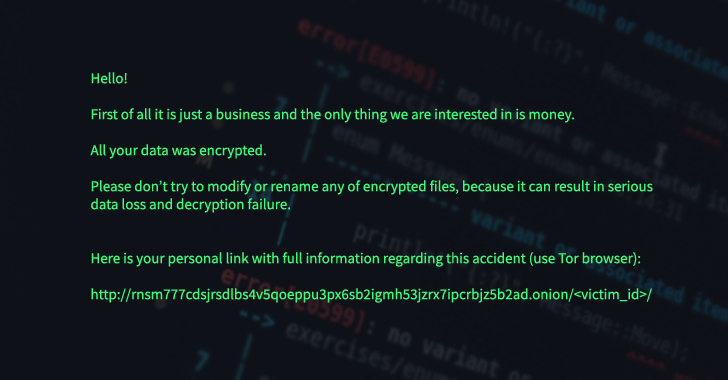 4.2KMalware
4.2KMalwareNew RansomExx Ransomware Variant Rewritten in the Rust Programming Language
The operators of the RansomExx ransomware have become the latest to develop a new variant fully rewritten in the Rust programming language,...
The Latest
-
 Malware
MalwareKimsuky Using TRANSLATEXT Chrome Extension to Steal Sensitive Data
-
 Vulnerabilities
VulnerabilitiesGitLab Releases Patch for Critical CI/CD Pipeline Vulnerability and 13 Others
-
 Malware
Malware8220 Gang Exploits Oracle WebLogic Server Flaws for Cryptocurrency Mining
-
 Vulnerabilities
VulnerabilitiesResearchers Warn of Flaws in Widely Used Industrial Gas Analysis Equipment
-
 Malware
MalwareRust-Based P2PInfect Botnet Evolves with Miner and Ransomware Payloads
-
 Vulnerabilities
VulnerabilitiesPrompt Injection Flaw in Vanna AI Exposes Databases to RCE Attacks
-
 Malware
MalwareRussian National Indicted for Cyber Attacks on Ukraine Before 2022 Invasion
-
 Vulnerabilities
VulnerabilitiesCritical SQLi Vulnerability Found in Fortra FileCatalyst Workflow Application
-
 Vulnerabilities
VulnerabilitiesExploit Attempts Recorded Against New MOVEit Transfer Vulnerability – Patch ASAP!
-
 Vulnerabilities
VulnerabilitiesPractical Guidance For Securing Your Software Supply Chain
-
 Vulnerabilities
VulnerabilitiesApple Patches AirPods Bluetooth Vulnerability That Could Allow Eavesdropping
-
 Malware
MalwareNew Credit Card Skimmer Targets WordPress, Magento, and OpenCart Sites
-
 Malware
MalwareNew Medusa Android Trojan Targets Banking Users Across 7 Countries
-
 Vulnerabilities
VulnerabilitiesOver 110,000 Websites Affected by Hijacked Polyfill Supply Chain Attack
-
 Vulnerabilities
VulnerabilitiesNew Attack Technique Exploits Microsoft Management Console Files
-
 Vulnerabilities
VulnerabilitiesHow to Cut Costs with a Browser Security Platform
-
 Malware
MalwareMultiple WordPress Plugins Compromised: Hackers Create Rogue Admin Accounts
-
 Vulnerabilities
VulnerabilitiesGoogle Introduces Project Naptime for AI-Powered Vulnerability Research
-
 Vulnerabilities
VulnerabilitiesCritical RCE Vulnerability Discovered in Ollama AI Infrastructure Tool
-
 Vulnerabilities
VulnerabilitiesRedJuliett Cyber Espionage Campaign Hits 75 Taiwanese Organizations




