Featured News
-
 3.6KCyber Attack
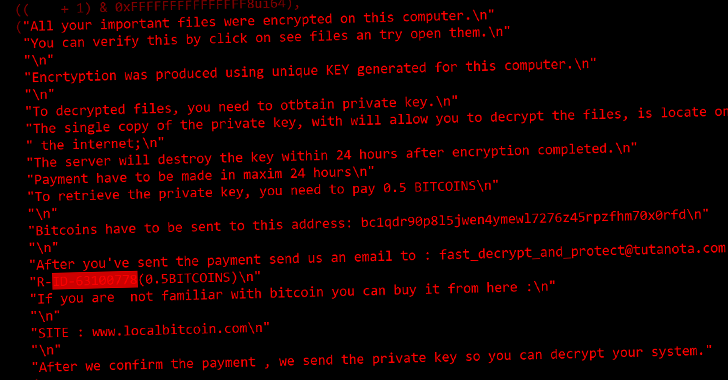
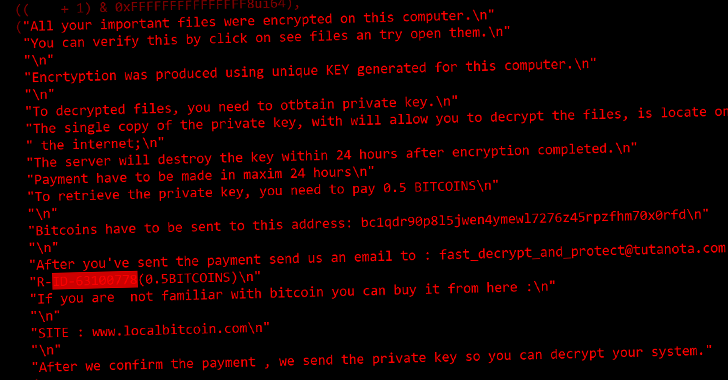
3.6KCyber AttackRussian Courts Targeted by New CryWiper Data Wiper Malware Posing as Ransomware
A new data wiper malware called CryWiper has been found targeting Russian government agencies, including mayor’s offices and courts. “Although it disguises...
-

 3.5KMalware
3.5KMalwareSiriusXM Vulnerability Lets Hackers Remotely Unlock and Start Connected Cars
Cybersecurity researchers have discovered a security vulnerability that exposes cars from Honda, Nissan, Infiniti, and Acura to remote attacks through a connected...
-
 3.5KVulnerabilities
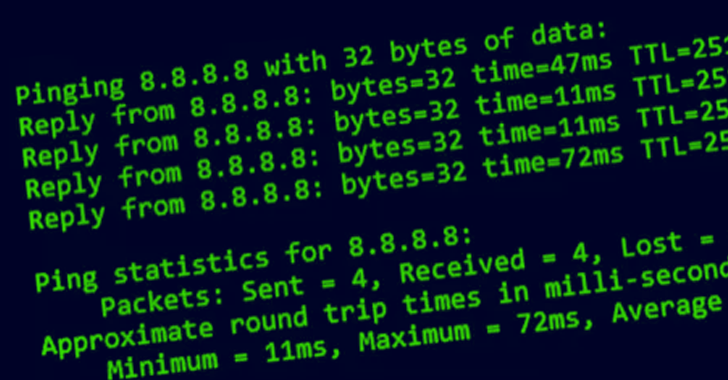
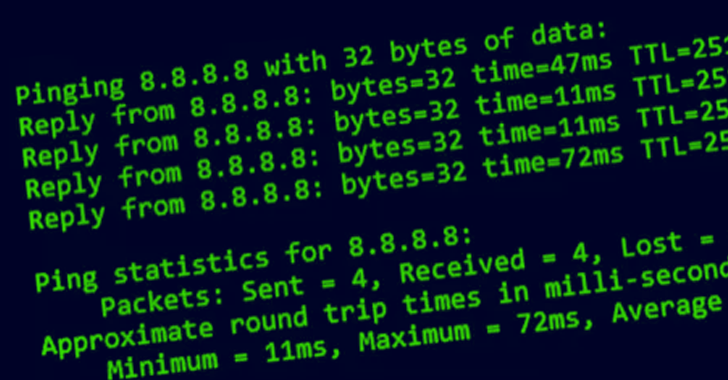
3.5KVulnerabilitiesCritical Ping Vulnerability Allows Remote Attackers to Take Over FreeBSD Systems
The maintainers of the FreeBSD operating system have released updates to remediate a security vulnerability impacting the ping module that could be...
-

 3.1KMalware
3.1KMalwareNew Android Malware Stolen Facebook Credentials From 300,000 Victims
The mobile security firm Zimperium has recently issued a warning about a Trojan called “Schoolyard Bully,” which is actively masquerading as an...
-

 5.0KData Security
5.0KData Security6 reasons to secure your email in 2023 without investing much
Because companies either do not teach their staff enough or have inadequate email security measures in place, many firms, ranging from start-ups to...
-

 3.1KMalware
3.1KMalwareBeware that Hackers Using Malicious USB Devices to Deliver Multiple Malware
Recently, Mandiant Managed Defense discovered cyber espionage activity that focuses on the Philippines and mainly uses USB drives as an initial infection...
-

 494Vulnerabilities
494VulnerabilitiesGoogle Rolls Out New Chrome Browser Update to Patch Yet Another Zero-Day Vulnerability
Search giant Google on Friday released an out-of-band security update to fix a new actively exploited zero-day flaw in its Chrome web...
-
 1.0KData Security
1.0KData SecurityBad news! The platform certificates of many phone manufactures have been hacked. These are used to sign trusted apps on Android phones. Now these certificates are being used to certify malicious Android applications
Platform certificates, also known as platform keys, are used by OEM Android device makers to certify the core ROM images of their...
-
 3.0KData Security
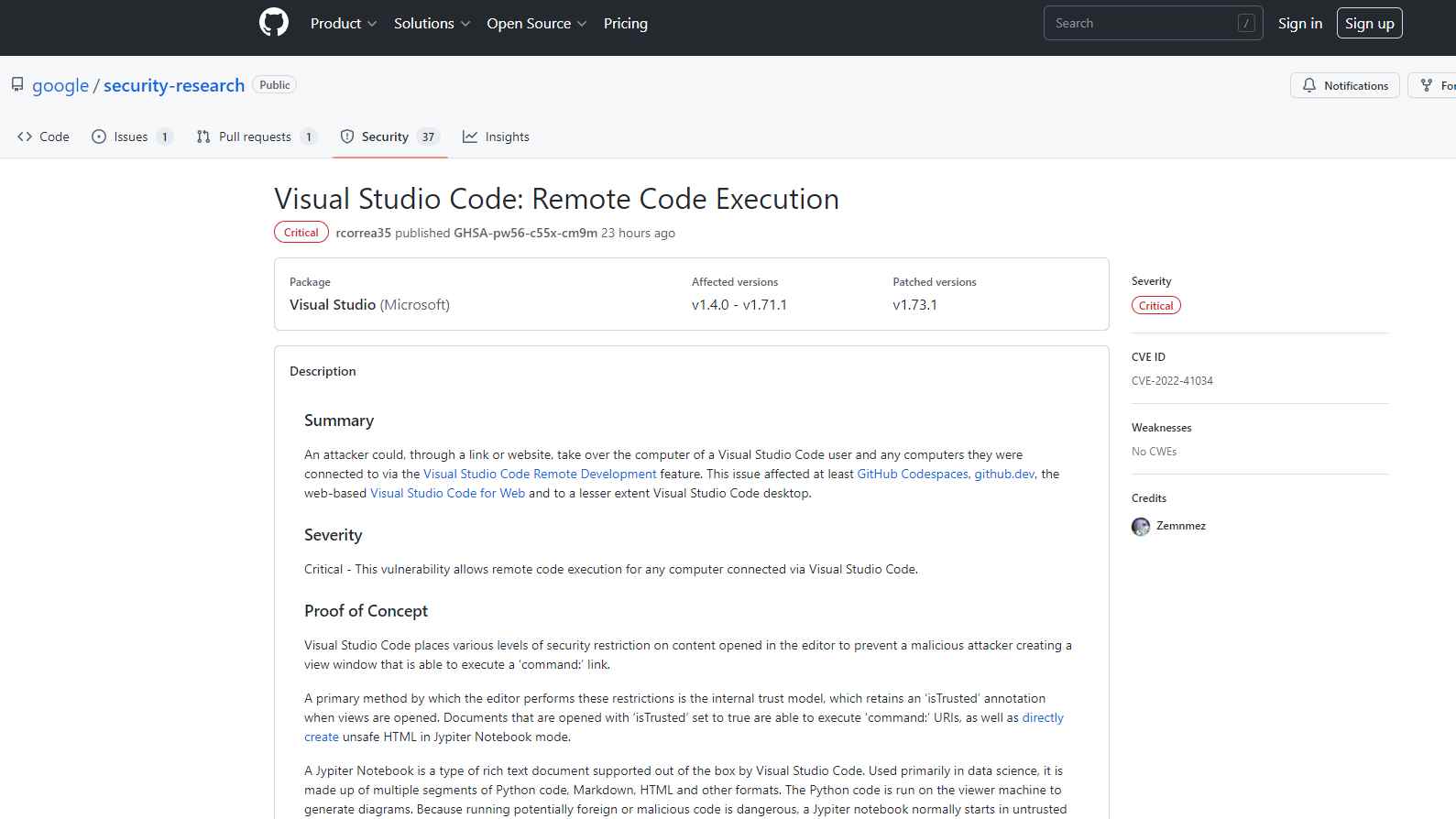
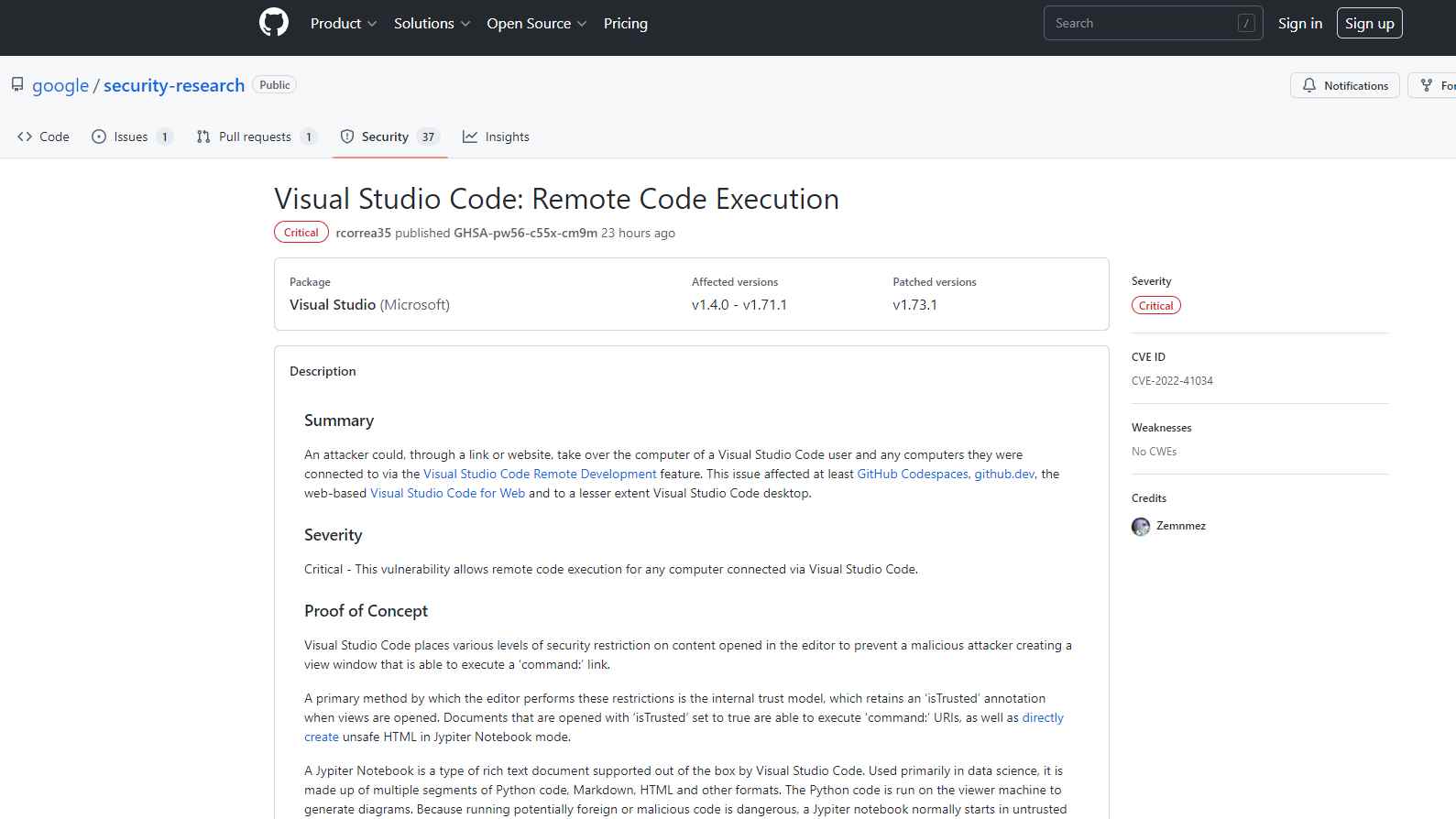
3.0KData SecurityExploit PoC for Remote code execution flaw in Visual Studio Code released
The remote code execution vulnerability that affected Visual Studio Code and was fixed by Microsoft in October was the subject of a...
-
 3.6KMalware
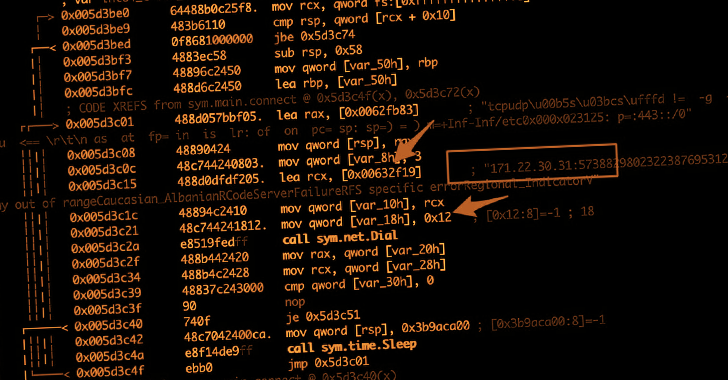
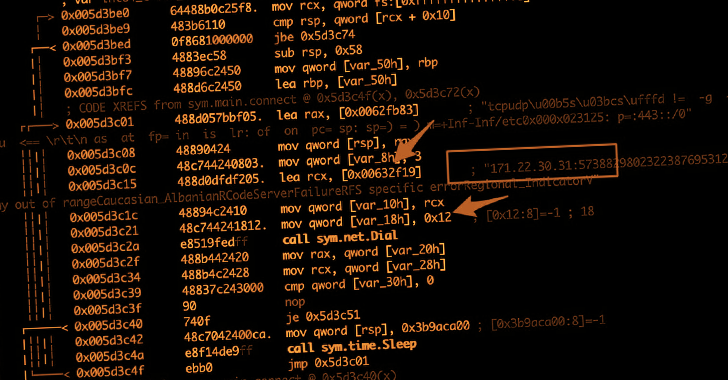
3.6KMalwareAccidental Syntax Error Leads to Kill The Cryptomining botnet Malware “KmsdBot”
It turns out that Akamai’s team of researchers accidentally killed a newly discovered cryptocurrency mining botnet known as KmsdBot during the investigation....
-
 4.7KVulnerabilities
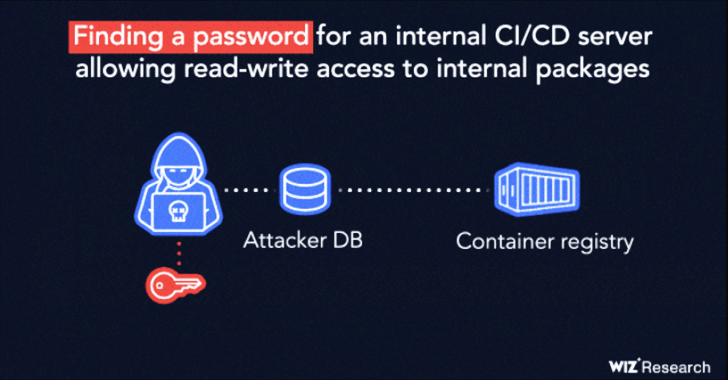
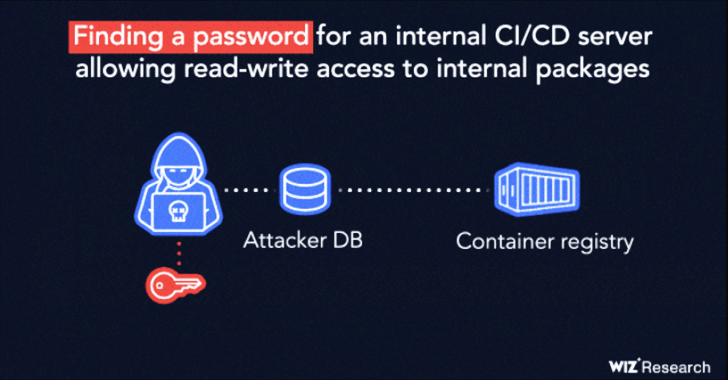
4.7KVulnerabilitiesResearchers Disclose Supply-Chain Flaw Affecting IBM Cloud Databases for PostgreSQL
IBM has fixed a high-severity security vulnerability affecting its Cloud Databases (ICD) for PostgreSQL product that could be potentially exploited to tamper...
-

 4.9KVulnerabilities
4.9KVulnerabilitiesHackers Exploiting Redis Vulnerability to Deploy New Redigo Malware on Servers
A previously undocumented Go-based malware is targeting Redis servers with the goal of taking control of the infected systems and likely building...
-
 3.8KMalware
3.8KMalwareCuba Ransomware Extorted Over $60 Million in Ransom Fees from More than 100 Entities
The threat actors behind Cuba (aka COLDDRAW) ransomware have received more than $60 million in ransom payments and compromised over 100 entities...
-
 4.9KVulnerabilities
4.9KVulnerabilitiesZero day Privilege escalation flaw CVE-2022-4139 (CVSS score: 7.0), impacts Linux kernel
A recently discovered security flaw in the Linux kernel might be exploited locally by an attacker to get elevated privileges on susceptible...
-

 4.6KIncidents
4.6KIncidentsLASTPASS: The world’s most popular password manager hacked third time along with GoTo (formerly known as LogMeIn)
Another data breach has occurred this year as a direct result of the master password vault known as “LastPass.” According to LastPass,...
-
 5.3KMalware
5.3KMalwareGoogle Accuses Spanish Spyware Vendor of Exploiting Chrome, Firefox, & Windows Zero-Days
A Barcelona-based surveillanceware vendor named Variston IT is said to have surreptitiously planted spyware on targeted devices by exploiting several zero-day flaws...
-

 1.8KData Breach
1.8KData BreachHackers Leak Another Set of Medibank Customer Data on the Dark Web
Medibank on Thursday confirmed that the threat actors behind the devastating cyber attack have posted another dump of data stolen from its...
-
 3.9KVulnerabilities
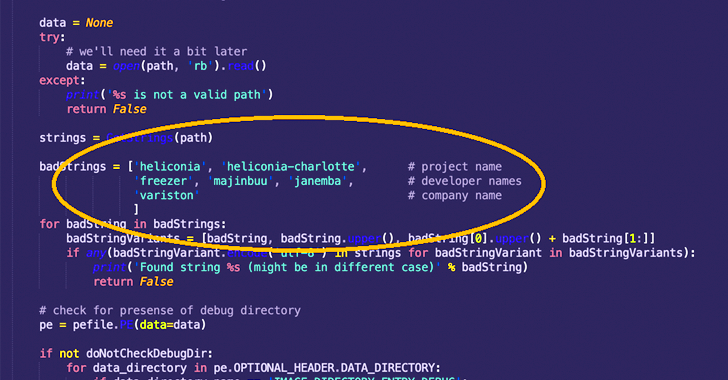
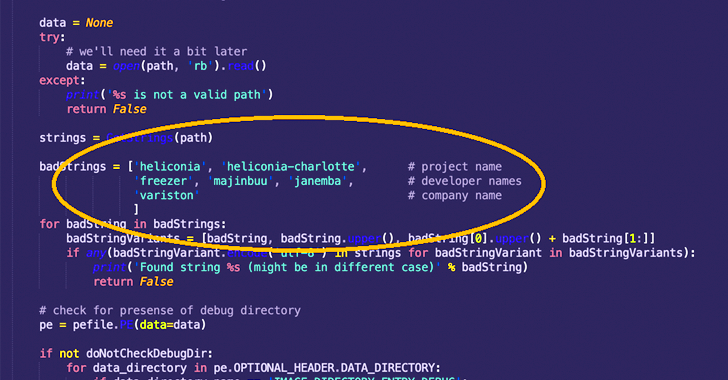
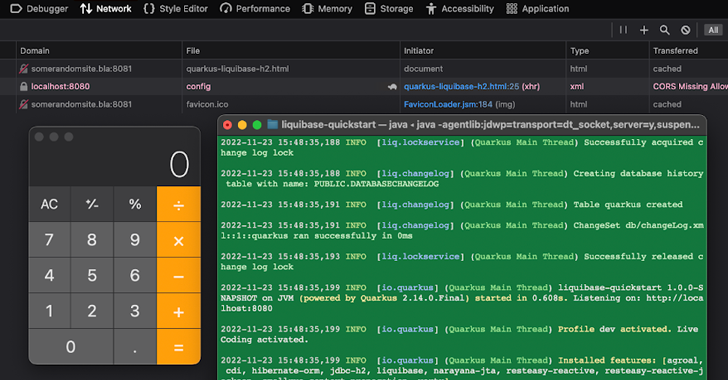
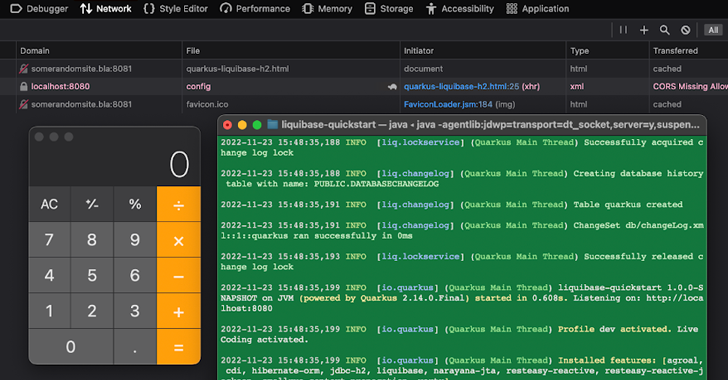
3.9KVulnerabilitiesResearchers Disclose Critical RCE Vulnerability Affecting Quarkus Java Framework
A critical security vulnerability has been disclosed in the Quarkus Java framework that could be potentially exploited to achieve remote code execution...
-
 3.6KMalware
3.6KMalwareSchoolyard Bully Trojan Apps Stole Facebook Credentials from Over 300,000 Android Users
More than 300,000 users across 71 countries have been victimized by a new Android threat campaign called the Schoolyard Bully Trojan. Mainly...
-
 1.2KMalware
1.2KMalwareResearchers ‘Accidentally’ Crash KmsdBot Cryptocurrency Mining Botnet Network
An ongoing analysis into an up-and-coming cryptocurrency mining botnet known as KmsdBot has led to it being accidentally taken down. KmsdBot, as...
The Latest
-
 Malware
MalwareKimsuky Using TRANSLATEXT Chrome Extension to Steal Sensitive Data
-
 Vulnerabilities
VulnerabilitiesGitLab Releases Patch for Critical CI/CD Pipeline Vulnerability and 13 Others
-
 Malware
Malware8220 Gang Exploits Oracle WebLogic Server Flaws for Cryptocurrency Mining
-
 Vulnerabilities
VulnerabilitiesResearchers Warn of Flaws in Widely Used Industrial Gas Analysis Equipment
-
 Malware
MalwareRust-Based P2PInfect Botnet Evolves with Miner and Ransomware Payloads
-
 Vulnerabilities
VulnerabilitiesPrompt Injection Flaw in Vanna AI Exposes Databases to RCE Attacks
-
 Malware
MalwareRussian National Indicted for Cyber Attacks on Ukraine Before 2022 Invasion
-
 Vulnerabilities
VulnerabilitiesCritical SQLi Vulnerability Found in Fortra FileCatalyst Workflow Application
-
 Vulnerabilities
VulnerabilitiesExploit Attempts Recorded Against New MOVEit Transfer Vulnerability – Patch ASAP!
-
 Vulnerabilities
VulnerabilitiesPractical Guidance For Securing Your Software Supply Chain
-
 Vulnerabilities
VulnerabilitiesApple Patches AirPods Bluetooth Vulnerability That Could Allow Eavesdropping
-
 Malware
MalwareNew Credit Card Skimmer Targets WordPress, Magento, and OpenCart Sites
-
 Malware
MalwareNew Medusa Android Trojan Targets Banking Users Across 7 Countries
-
 Vulnerabilities
VulnerabilitiesOver 110,000 Websites Affected by Hijacked Polyfill Supply Chain Attack
-
 Vulnerabilities
VulnerabilitiesNew Attack Technique Exploits Microsoft Management Console Files
-
 Vulnerabilities
VulnerabilitiesHow to Cut Costs with a Browser Security Platform
-
 Malware
MalwareMultiple WordPress Plugins Compromised: Hackers Create Rogue Admin Accounts
-
 Vulnerabilities
VulnerabilitiesGoogle Introduces Project Naptime for AI-Powered Vulnerability Research
-
 Vulnerabilities
VulnerabilitiesCritical RCE Vulnerability Discovered in Ollama AI Infrastructure Tool
-
 Vulnerabilities
VulnerabilitiesRedJuliett Cyber Espionage Campaign Hits 75 Taiwanese Organizations




