Featured News
-

 3.8KMalware
3.8KMalwareNew Malvertising Campaign via Google Ads Targets Users Searching for Popular Software
Users searching for popular software are being targeted by a new malvertising campaign that abuses Google Ads to serve trojanized variants that...
-

 3.4KData Security
3.4KData SecurityWhat exactly is social engineering, and how can you safeguard yourself from becoming a victim of it?
In the world of cybercrime, social engineering refers to a method of manipulation that is used to collect sensitive information from people....
-

 4.1KIncidents
4.1KIncidentsData on 270,000 patients was stolen from the medical hospital in Louisiana by ransomware cybercriminals
During the month of October, cybercriminals broke into the computer system of a health care system in Louisiana, gaining access to the...
-

 4.2KVulnerabilities
4.2KVulnerabilitiesHacking Nintendo Switch, 3DS, and Wii console. Vulnerability allows hacking remote console by simply engaging in an online gaming session with the victim
Nintendo has secretly released a fix for a security flaw that might have allowed hackers to access compromised Switch, 3DS, and Wii...
-

 966Malware
966MalwareBitKeep Confirms Cyber Attack, Loses Over $9 Million in Digital Currencies
Decentralized multi-chain crypto wallet BitKeep on Wednesday confirmed a cyberattack that allowed threat actors to distribute fraudulent versions of its Android app...
-

 1.8KMalware
1.8KMalwareAPT Hackers Turn to Malicious Excel Add-ins as Initial Intrusion Vector
Microsoft’s decision to block Visual Basic for Applications (VBA) macros by default for Office files downloaded from the internet has led many...
-
 3.5KData Security
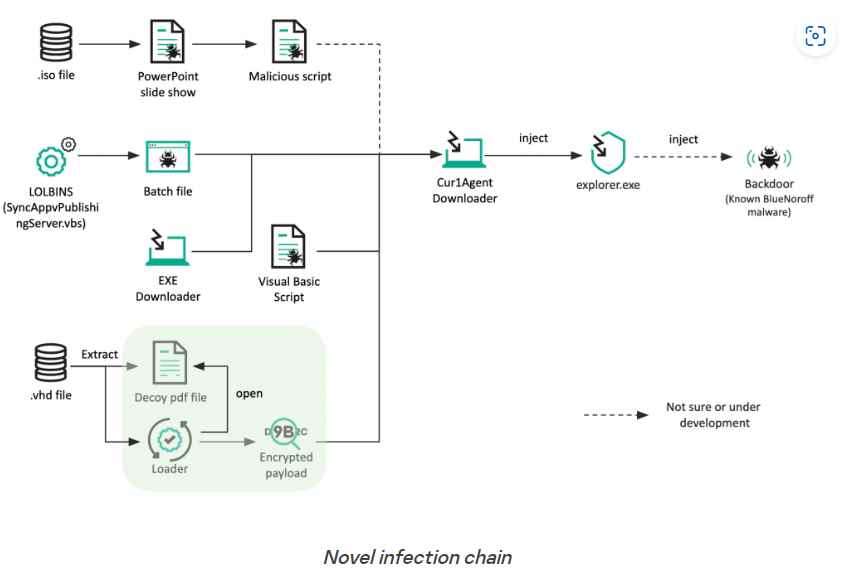
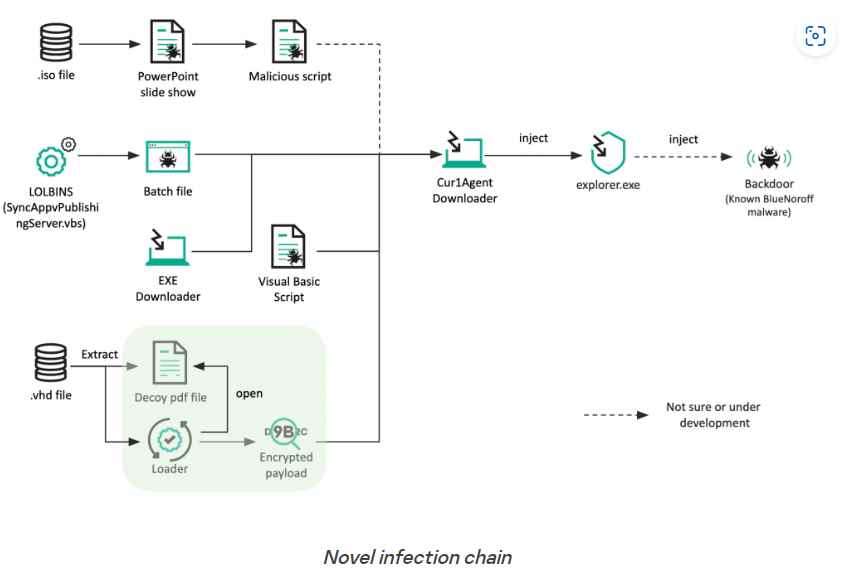
3.5KData SecurityNew attack technique uses .ISO and .VHD file formats to bypass Windows MotW Security
BlueNoroff is a part of the infamous Lazarus Group, and it has been detected incorporating new strategies into its playbook. These new strategies...
-

 2.7KMalware
2.7KMalwareHackers Deploy New Information Stealer Malware onto Python Developers’ Machines
Researchers at Phylum recently discovered that hackers had been injecting information stealer malware into Python developers’ machines in order to steal their...
-

 2.7KLeaks
2.7KLeaksHow to delete an account from Instagram?
We all have social media accounts and use them to share photos, videos, and thoughts with the world. But what if you...
-

 726Malware
726MalwareZerobot botnet can now hack into Apache, Apache Spark servers
Malware activities carried out by botnets pose a danger to devices and networks that is always developing. Due to the fact that...
-
 1.6KVulnerabilities
1.6KVulnerabilitiesLinux Kernel has a Remote Code Execution Zero Day Vulnerability with CVSS score of 10
The use after free vulnerability, which is linked to ksmbd, affects computers running Linux distributions powered by kernels earlier than 5.15.61. This...
-
 3.4KMalware
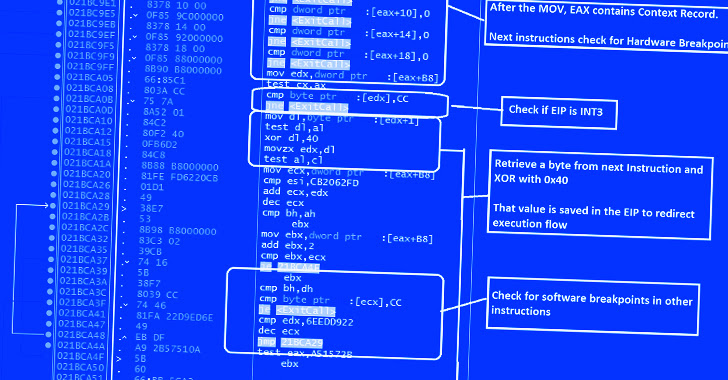
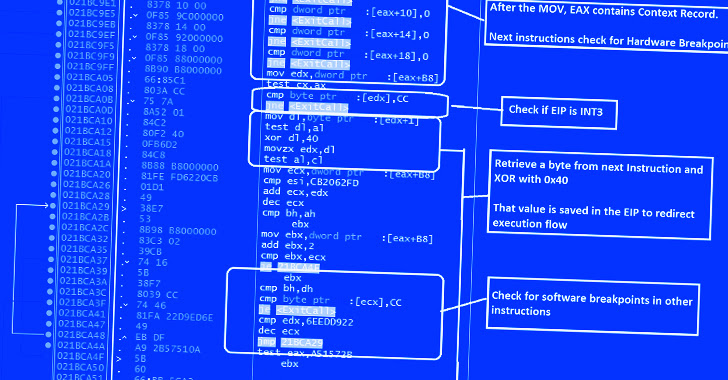
3.4KMalwareGuLoader Malware Utilizing New Techniques to Evade Security Software
Cybersecurity researchers have exposed a wide variety of techniques adopted by an advanced malware downloader called GuLoader to evade security software. “New...
-
 3.0KMalware
3.0KMalware2022 Top Five Immediate Threats in Geopolitical Context
As we are nearing the end of 2022, looking at the most concerning threats of this turbulent year in terms of testing...
-

 1.3KMalware
1.3KMalwarePrivateLoader PPI Service Found Distributing Info-Stealing RisePro Malware
The pay-per-install (PPI) malware downloader service known as PrivateLoader is being used to distribute a previously documented information-stealing malware dubbed RisePro. Flashpoint...
-

 1.8KMalware
1.8KMalwareW4SP Stealer Discovered in Multiple PyPI Packages Under Various Names
Threat actors have published yet another round of malicious packages to Python Package Index (PyPI) with the goal of delivering information-stealing malware...
-

 3.3KIncidents
3.3KIncidentsChristmas Casino heist: BetMGM hacked, data of 1.57 million gamblers leaked , while data of 68,000 DraftKings customers also hacked
BetMGM, an online sports betting website owned by MGM Resorts, announced a data breach on the same day hackers attempted to sell...
-
 2.4KVulnerabilities
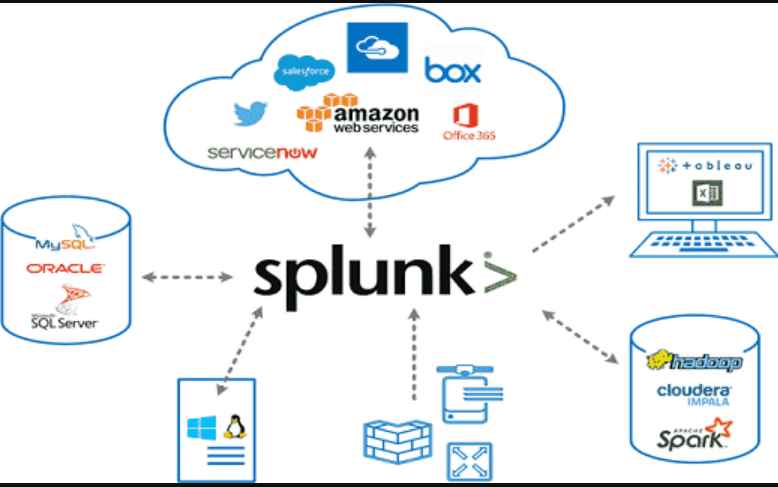
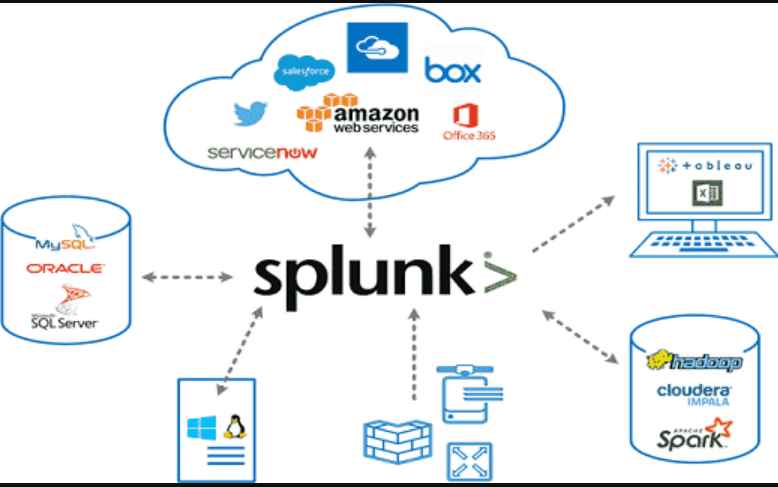
2.4KVulnerabilitiesExploit code for Splunk vulnerability published, allows remote code execution on the system
Splunk Inc. is a San Francisco, California-based American software firm that develops Web-based software for finding, monitoring, and analyzing machine-generated data. Splunk...
-
 3.2KMalware
3.2KMalwareVice Society Ransomware Attackers Adopt Robust Encryption Methods
The Vice Society ransomware actors have switched to yet another custom ransomware payload in their recent attacks aimed at a variety of...
-
 4.8KData Breach
4.8KData BreachLastPass Admits to Severe Data Breach, Encrypted Password Vaults Stolen
The August 2022 security breach of LastPass may have been more severe than previously disclosed by the company. The popular password management...
-
 1.2KMalware
1.2KMalwareKmsdBot Botnet Leverages SSH to Compromise Systems and to Launch DDoS Attacks
Researchers from Akamai have continued to study the cryptomining botnet KmsdBot and have looked at its attack flow. It is believed that...
The Latest
-
 Malware
MalwareKimsuky Using TRANSLATEXT Chrome Extension to Steal Sensitive Data
-
 Vulnerabilities
VulnerabilitiesGitLab Releases Patch for Critical CI/CD Pipeline Vulnerability and 13 Others
-
 Malware
Malware8220 Gang Exploits Oracle WebLogic Server Flaws for Cryptocurrency Mining
-
 Vulnerabilities
VulnerabilitiesResearchers Warn of Flaws in Widely Used Industrial Gas Analysis Equipment
-
 Malware
MalwareRust-Based P2PInfect Botnet Evolves with Miner and Ransomware Payloads
-
 Vulnerabilities
VulnerabilitiesPrompt Injection Flaw in Vanna AI Exposes Databases to RCE Attacks
-
 Malware
MalwareRussian National Indicted for Cyber Attacks on Ukraine Before 2022 Invasion
-
 Vulnerabilities
VulnerabilitiesCritical SQLi Vulnerability Found in Fortra FileCatalyst Workflow Application
-
 Vulnerabilities
VulnerabilitiesExploit Attempts Recorded Against New MOVEit Transfer Vulnerability – Patch ASAP!
-
 Vulnerabilities
VulnerabilitiesPractical Guidance For Securing Your Software Supply Chain
-
 Vulnerabilities
VulnerabilitiesApple Patches AirPods Bluetooth Vulnerability That Could Allow Eavesdropping
-
 Malware
MalwareNew Credit Card Skimmer Targets WordPress, Magento, and OpenCart Sites
-
 Malware
MalwareNew Medusa Android Trojan Targets Banking Users Across 7 Countries
-
 Vulnerabilities
VulnerabilitiesOver 110,000 Websites Affected by Hijacked Polyfill Supply Chain Attack
-
 Vulnerabilities
VulnerabilitiesNew Attack Technique Exploits Microsoft Management Console Files
-
 Vulnerabilities
VulnerabilitiesHow to Cut Costs with a Browser Security Platform
-
 Malware
MalwareMultiple WordPress Plugins Compromised: Hackers Create Rogue Admin Accounts
-
 Vulnerabilities
VulnerabilitiesGoogle Introduces Project Naptime for AI-Powered Vulnerability Research
-
 Vulnerabilities
VulnerabilitiesCritical RCE Vulnerability Discovered in Ollama AI Infrastructure Tool
-
 Vulnerabilities
VulnerabilitiesRedJuliett Cyber Espionage Campaign Hits 75 Taiwanese Organizations




