Featured News
-

 4.7KMalware
4.7KMalwareCybercrime (and Security) Predictions for 2023
Threat actors continue to adapt to the latest technologies, practices, and even data privacy laws—and it’s up to organizations to stay one...
-

 615Malware
615MalwareBeware of Highly Sophisticated DarkTortilla Malware Distributed Via Phishing Sites
Cyble Research and Intelligence Labs (CRIL) detected threat Actors (TAs) distributing the malware DarkTortilla. Since 2015, the complex .NET-based malware known as DarkTortilla...
-

 2.9KKids Online
2.9KKids OnlineHow to set up parental controls on your child’s new smartphone
Give yourself peace of mind and help create a safe online space for your child using Android or iOS parental controls
-
 4.4KMalware
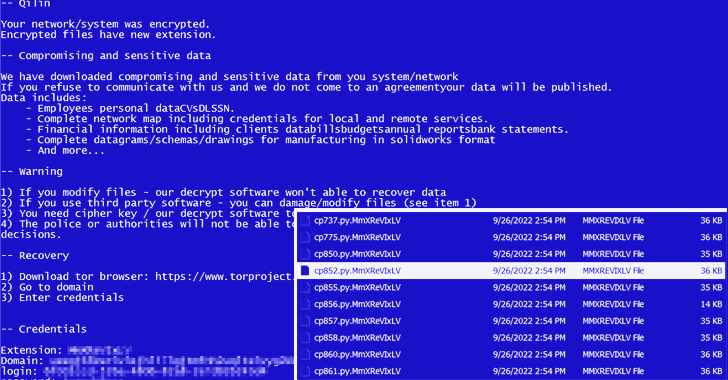
4.4KMalwareNew Agenda Ransomware Variant, Written in Rust, Aiming at Critical Infrastructure
A Rust variant of a ransomware strain known as Agenda has been observed in the wild, making it the latest malware to...
-
 776Cyber Attack
776Cyber AttackFacebook Cracks Down on Spyware Vendors from U.S., China, Russia, Israel, and India
Meta Platforms disclosed that it took down no less than 200 covert influence operations since 2017 spanning roughly 70 countries across 42...
-

 2.3KLeaks
2.3KLeaksWhich team is responsible for debriefing after a cyber attack?
Cybersecurity is a rapidly growing field with a lot of potential. Not only do cyberattacks have the potential to devastate an organization...
-

 3.6KMalware
3.6KMalwareHackers Use Trojanized Windows 10 Installer To Attack Against Government Entities
Mandiant recently identified that in a targeted attack on Ukrainian government entities, trojanized ISO files were used by threat actors to cloak...
-

 4.3KVulnerabilities
4.3KVulnerabilitiesSamba Issues Security Updates to Patch Multiple High-Severity Vulnerabilities
Samba has released software updates to remediate multiple vulnerabilities that, if successfully exploited, could allow an attacker to take control of affected...
-

 2.3KData Breach
2.3KData BreachOver 9 Million Credit Card Data Exposed from Leading Payment Systems
An open and unprotected database with 9,098,506 records of credit card transactions was discovered recently by security researcher Jeremiah Fowler and the...
-

 2.7KIncidents
2.7KIncidentsBiggest electricity, water, and gas company in Colombia Empresas Públicas de Medellín (EPM) suffers ransomware attack
EPM is one of the main public suppliers of electricity, water, and gas in Colombia, and it serves 123 towns. It also...
-
 4.4KData Security
4.4KData SecurityExploit code for remotely executing code on victim device exploiting Foxit PDF Reader Vulnerability
Researchers from HackSys Inc. have provided further information on a security issue in the code execution of Foxit PDF Reader. On vulnerable...
-

 3.7KPhishing
3.7KPhishingFacebook Infrastructure Used by Hackers in Phishing Attack Chain
A Meta-Phish attack that could lead to the loss of personally identifiable information (PII), login information, and a Facebook profile link was...
-

 5.0KKids Online
5.0KKids OnlineHelp! My kid has asked Santa for a smartphone
The time has come for your child to receive their first smartphone. Before handing it over, however, make sure to help them...
-

 3.1KIncidents
3.1KIncidentsAustralian telecom company TPG hacked as threat actor got access to a server that hosts the email accounts of 15,000 clients
This week, an announcement was made by TPG Telecom in Australia stating that an unidentified threat actor had acquired unauthorized access to...
-

 4.9KData Security
4.9KData Security8 social media influencers arrested for using Twitter & Discord to manipulate exchange-traded stocks and making $114 million
The Securities and Exchange Commission (SEC) has just announced that it will be filing charges against eight individuals in connection with a...
-
 2.3KVulnerabilities
2.3KVulnerabilitiesMicrosoft Reclassifies SPNEGO Extended Negotiation Security Vulnerability as ‘Critical’
Microsoft has revised the severity of a security vulnerability it originally patched in September 2022, upgrading it to “Critical” after it emerged...
-

 2.5KMalware
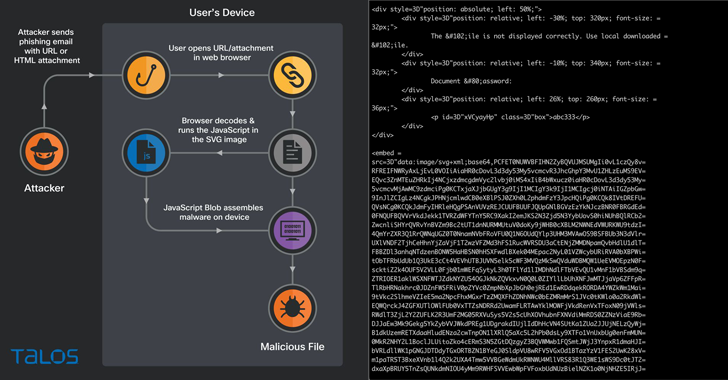
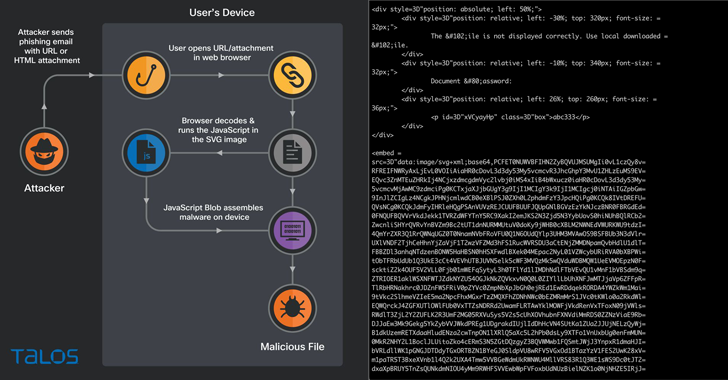
2.5KMalwareHackers Use SVG Images to Install QBot Malware on Windows Systems
To perform HTML smuggling, the QBot malware phishing campaigns utilize SVG image files as a method of distribution. This method creates a...
-
 4.1KVulnerabilities
4.1KVulnerabilitiesTop 5 Web App Vulnerabilities and How to Find Them
Web applications, often in the form of Software as a Service (SaaS), are now the cornerstone for businesses all over the world....
-
 3.7KCyber Attack
3.7KCyber AttackFBI Charges 6, Seizes 48 Domains Linked to DDoS-for-Hire Service Platforms
The U.S. Department of Justice (DoJ) on Wednesday announced the seizure of 48 domains that offered services to conduct distributed denial-of-service (DDoS)...
-
 4.1KMalware
4.1KMalwareHacking Using SVG Files to Smuggle QBot Malware onto Windows Systems
Phishing campaigns involving the Qakbot malware are using Scalable Vector Graphics (SVG) images embedded in HTML email attachments. The new distribution method...
The Latest
-
 Malware
MalwareKimsuky Using TRANSLATEXT Chrome Extension to Steal Sensitive Data
-
 Vulnerabilities
VulnerabilitiesGitLab Releases Patch for Critical CI/CD Pipeline Vulnerability and 13 Others
-
 Malware
Malware8220 Gang Exploits Oracle WebLogic Server Flaws for Cryptocurrency Mining
-
 Vulnerabilities
VulnerabilitiesResearchers Warn of Flaws in Widely Used Industrial Gas Analysis Equipment
-
 Malware
MalwareRust-Based P2PInfect Botnet Evolves with Miner and Ransomware Payloads
-
 Vulnerabilities
VulnerabilitiesPrompt Injection Flaw in Vanna AI Exposes Databases to RCE Attacks
-
 Malware
MalwareRussian National Indicted for Cyber Attacks on Ukraine Before 2022 Invasion
-
 Vulnerabilities
VulnerabilitiesCritical SQLi Vulnerability Found in Fortra FileCatalyst Workflow Application
-
 Vulnerabilities
VulnerabilitiesExploit Attempts Recorded Against New MOVEit Transfer Vulnerability – Patch ASAP!
-
 Vulnerabilities
VulnerabilitiesPractical Guidance For Securing Your Software Supply Chain
-
 Vulnerabilities
VulnerabilitiesApple Patches AirPods Bluetooth Vulnerability That Could Allow Eavesdropping
-
 Malware
MalwareNew Credit Card Skimmer Targets WordPress, Magento, and OpenCart Sites
-
 Malware
MalwareNew Medusa Android Trojan Targets Banking Users Across 7 Countries
-
 Vulnerabilities
VulnerabilitiesOver 110,000 Websites Affected by Hijacked Polyfill Supply Chain Attack
-
 Vulnerabilities
VulnerabilitiesNew Attack Technique Exploits Microsoft Management Console Files
-
 Vulnerabilities
VulnerabilitiesHow to Cut Costs with a Browser Security Platform
-
 Malware
MalwareMultiple WordPress Plugins Compromised: Hackers Create Rogue Admin Accounts
-
 Vulnerabilities
VulnerabilitiesGoogle Introduces Project Naptime for AI-Powered Vulnerability Research
-
 Vulnerabilities
VulnerabilitiesCritical RCE Vulnerability Discovered in Ollama AI Infrastructure Tool
-
 Vulnerabilities
VulnerabilitiesRedJuliett Cyber Espionage Campaign Hits 75 Taiwanese Organizations




