Featured News
-
 269Password Attacks
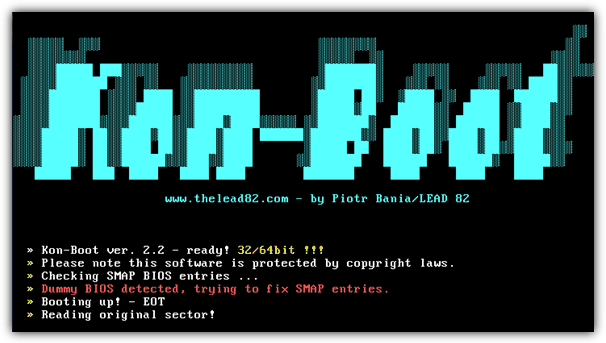
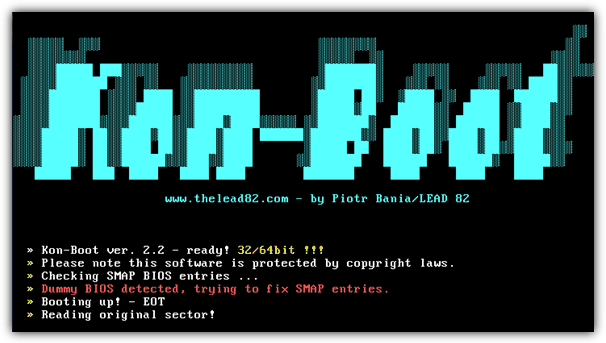
269Password AttacksKon-Boot – Bypass windows passwords
Kon-Boot is an application which will silently bypass the authentication process of Windows based operating systems. Without overwriting your old password! In...
-

 314Cyber Events
314Cyber EventsUS Department of Homeland Security Vows To Tackle DDoS Attacks
The contract between Department of Homeland Security (DHS) and Galois was signed in January. However, HackRead had a chance to discuss the contract...
-

 382News
382NewsIsraeli Security Camera Systems targeted by Pro-Hezbollah Hackers
A group claiming to have connections with Hezbollah says it hacked numerous security cameras in Israel In 2014, Izz al-Din al-Qassam Brigade of Hamas...
-
 110Data Security
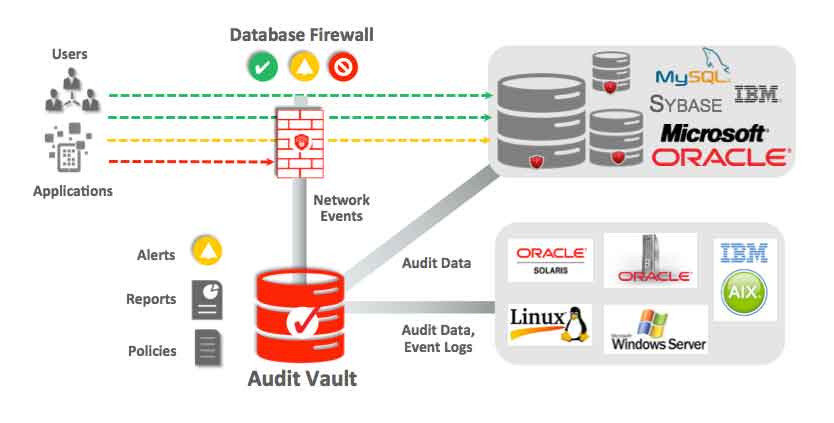
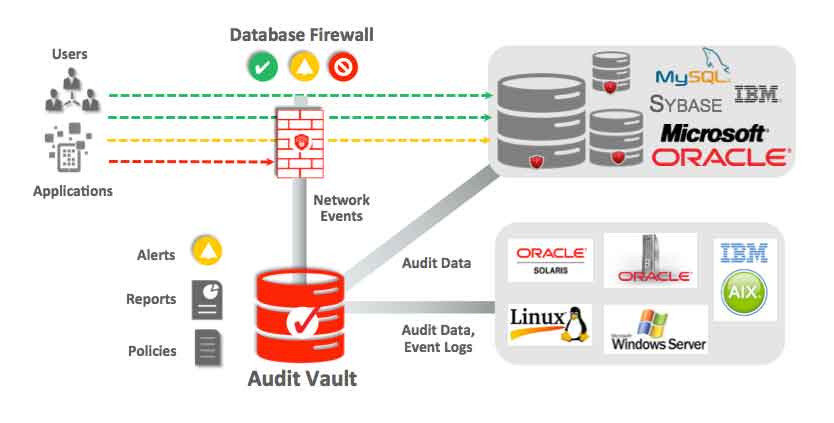
110Data SecurityHow to secure databases?
Databases can be a treasure trove of confidential data. Normally most databases contain confidential information, private data of companies, people, intellectual property,...
-
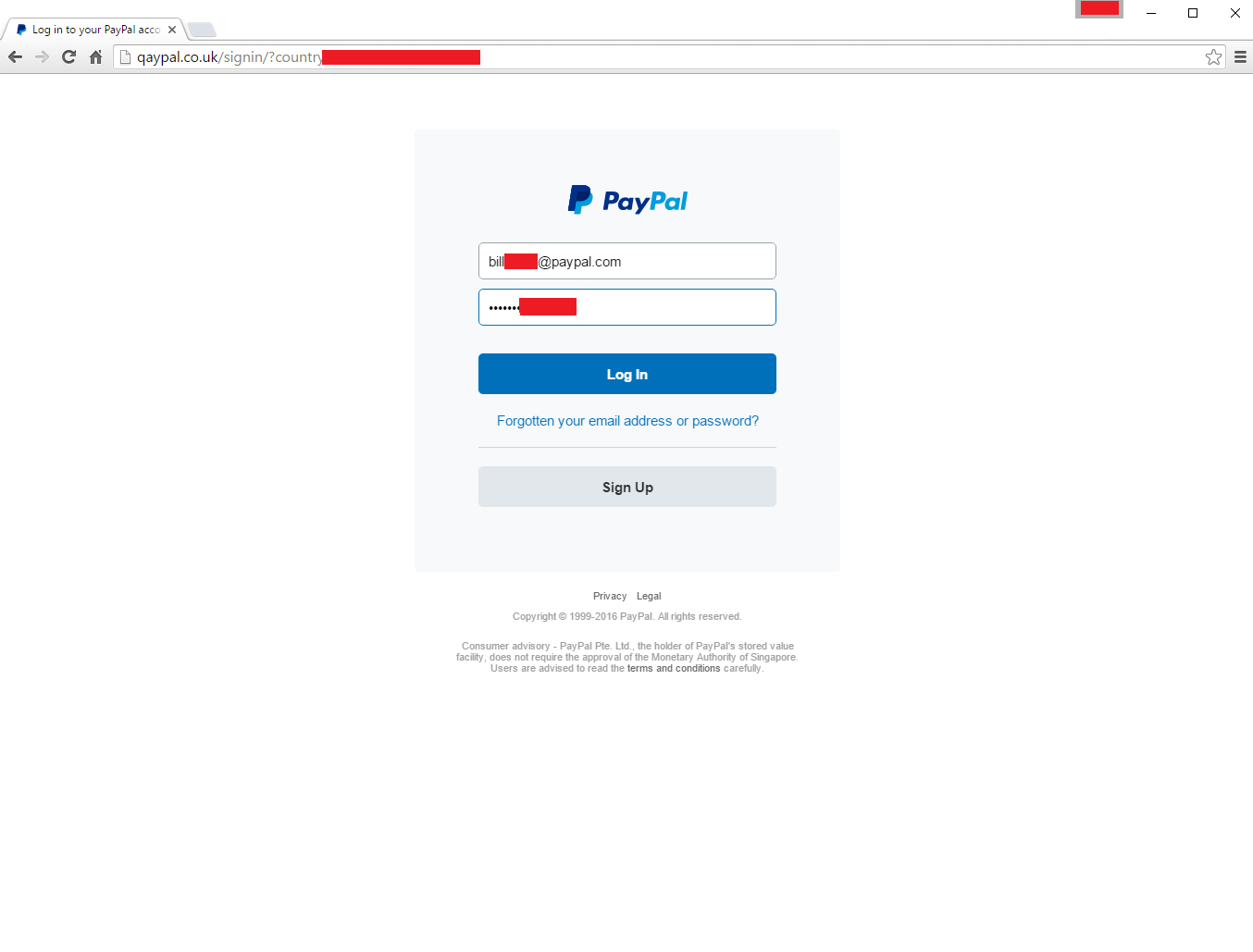
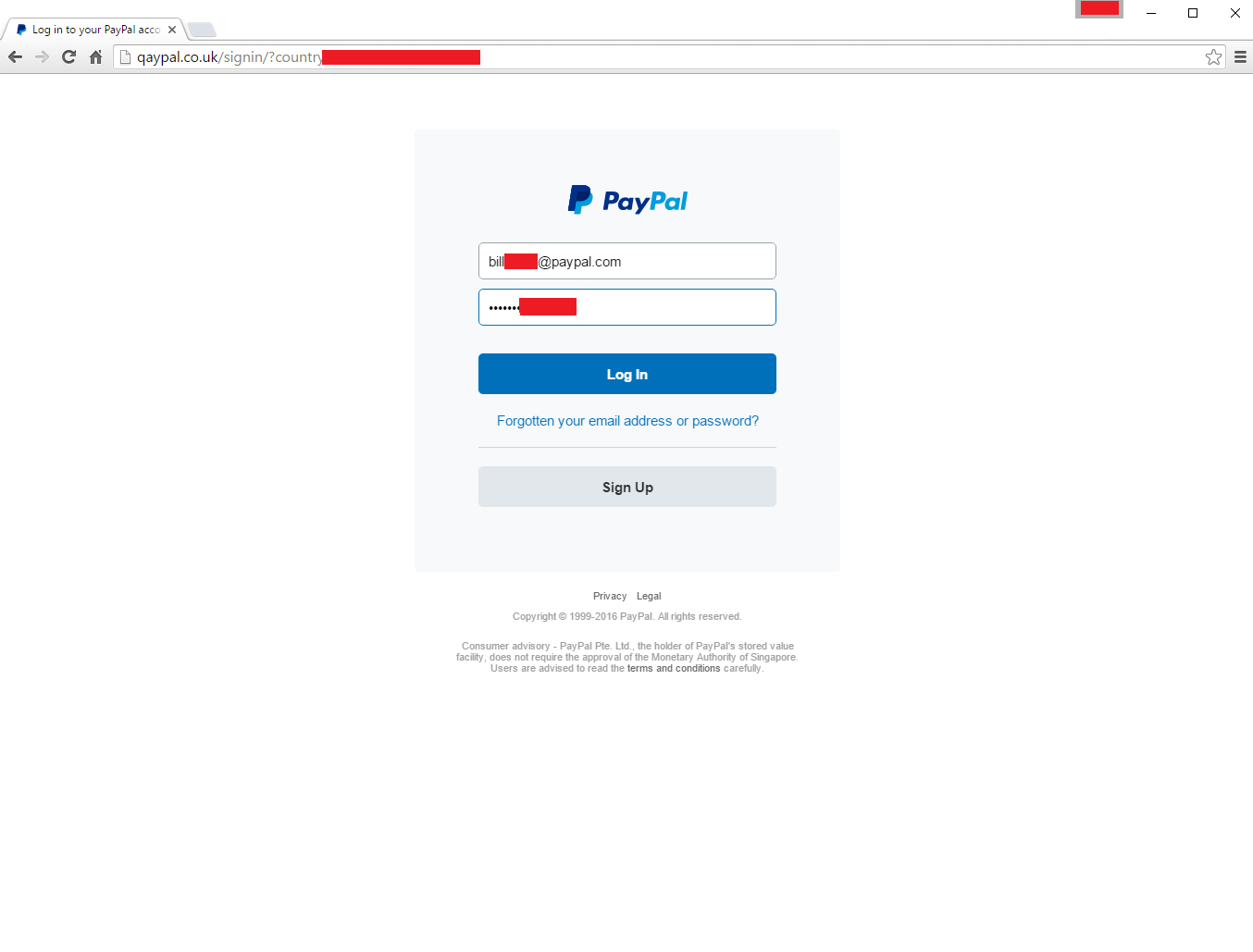 210How To
210How ToHow hackers hack your Paypal account
Today when I was checking my Inbox I got this mail from Service Paypal saying that, ” Your account has been limited...
-

 262Lists
262ListsTop 5 Billionaires In The Technology World
Short Bytes: It’s time to meet the top five billionaires in the technology world. They are the people who have superpowers to change...
-

 312Geek
312GeekApple’s “Find My iPhone” Saves a Life!
A smartphone can take a life and it can also save a life — This time, it has saved a life. Technology has once...
-
 303Geek
303GeekRun This Single Command In Terminal To Get Geeky Weather Reports
Short Bytes: If you are a coder who is in love with his/her work, then outside weather doesn’t matter much to you....
-

 272Geek
272GeekApple Tips & Tricks: How To Unlock iPhone To Use it on Another Carrier
Are you wondering how to unlock your iPhone so you can use it with another carrier? Then wonder no more! Although initially...
-
 204Geek
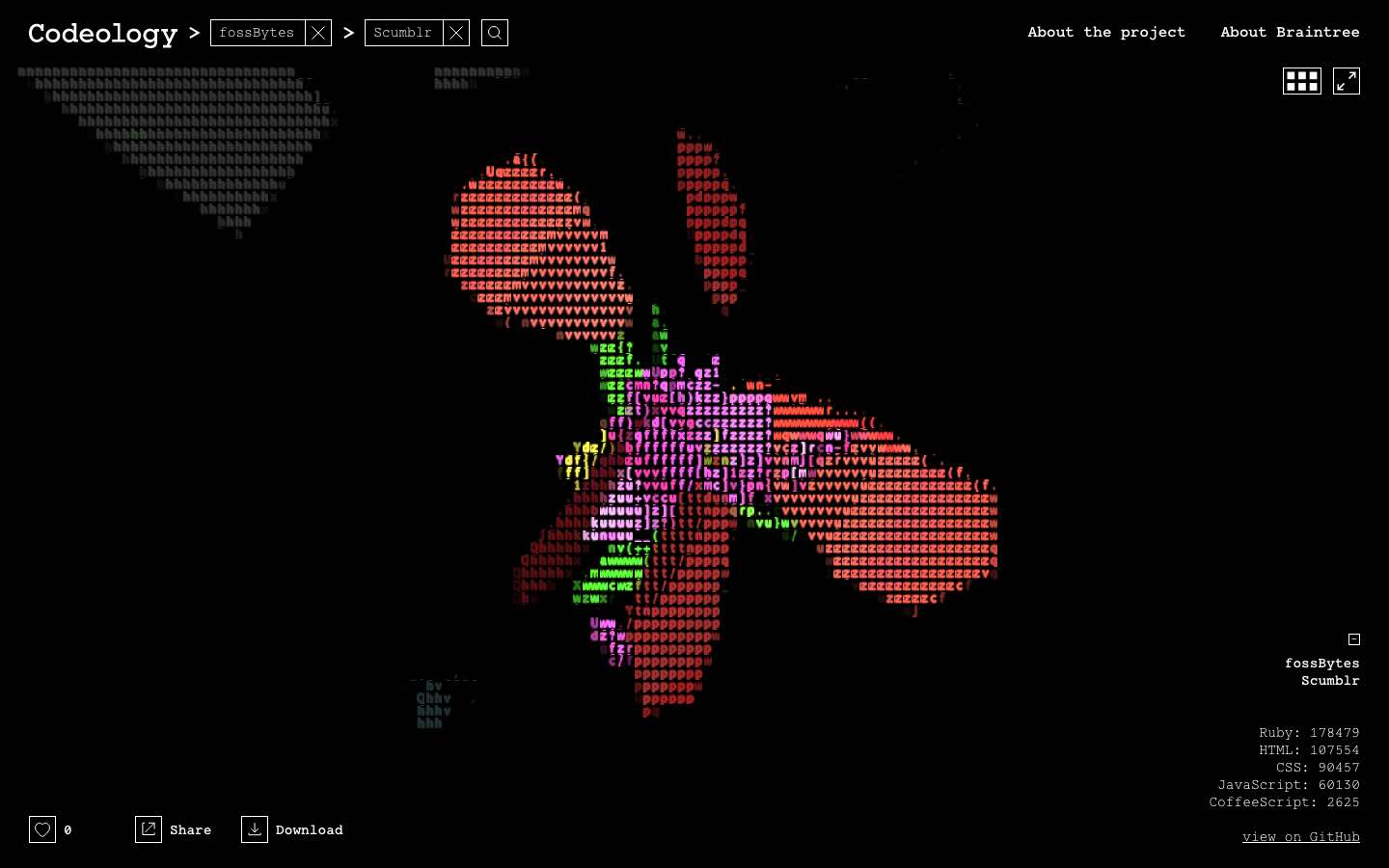
204GeekA Programmer’s Dream: This Is What Your Code Actually Looks Like On GitHub
Short Bytes: Codeology is an online visualization program that allows you to see your GitHub project in front of your eyes. Give...
-

 122Malware
122MalwareAndroid Malware About to Get Worse: GM Bot Source Code Leaked
IBM X-Force threat intelligence has found that the source code for Android malware GM Bot was leaked on an underground board in...
-

 264News
264NewsHacker Shows How To Hack Wireless Burglar Alarm System Like A Pro
SimpliSafe Alarm Systems’ Inherent Vulnerability Exposes Hazards of Wireless Security Devices Digital age has brought along countless blessings and conveniences for the...
-

 384Vulnerabilities
384VulnerabilitiesHow to Use NMAP 7 to Discover Vulnerabilities, Launch DoS Attacks and More!
NMAP is an essential tool in any hacker’s arsenal. Originally written by Gordon Lyon aka Fydor, it’s used to locate hosts and...
-
 140Vulnerabilities
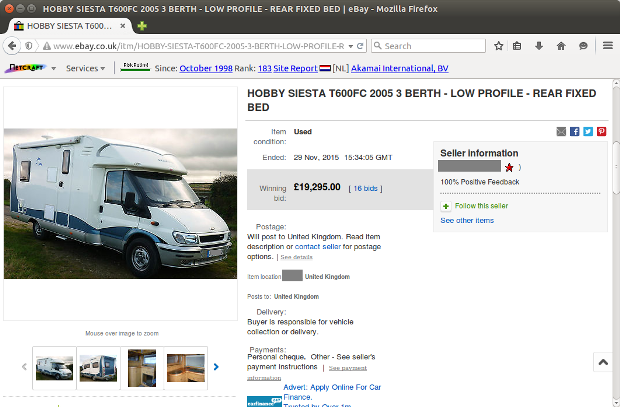
140VulnerabilitiesJSF*** eBay XSS Bug Exploited in the Wild, Despite the Company’s Fix
Attackers exploit eBay’s lackluster security policy. The JSF*** XSS bug that cyber-security firm Check Point discovered two weeks ago is being used in...
-
 90Incidents
90IncidentsMan admits he stole nude celebrity pics from Apple and Gmail accounts
Phishing scheme gained illegal access to accounts storing 161 nude images. An Oregon man has admitted he tricked hundreds of people into divulging...
-

 335Geek
335GeekWhich Phone is More Vulnerable to Hacking – iPhone or Android?
iOS users take on Android while Android users criticize Apple — But which OS is actually secure? It is a fact that...
-

 197News
197NewsAnonymous To Hit Israeli Military Against Detention of Palestinian Journalist
Al-Qeeq’s Detention Enrages Anonymous- Widespread DDoS Campaigns Planned Against Israel Army The online hacktivist Anonymous is known for targeting Israeli cyberspace including government,...
-

 187Geek
187GeekSelfie Crazy Tourists Responsible for Tragic Death of Rare Baby Dolphin
It takes nothing to go so low and kill a beautiful creature of nature for the sake of fun Suppose you are...
-

 148Data Security
148Data SecurityProtect your iPhone from the clutches of the FBI by switching to longer passcodes
Protect your iPhone from the clutches of the FBI by switching to longer passcodes The on-going tussle between the FBI and Apple...
-

 300Opinion
300OpinionThe Four “A”s of Account Management
It's said that the biggest vulnerabilities in a network environment are its users. If only there was a way to control those...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage




