Featured News
-
 225Data Security
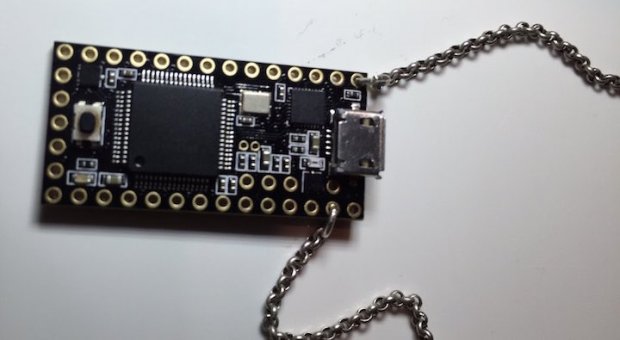
225Data SecurityUSBDriveby: A Necklace That Can Hack Your PC In Just 60 Seconds
Short Bytes: In a video found on the YouTube channel of Samy Kamkar, a USB drive beaded in a necklace has been shown...
-

 272Geek
272GeekInternet is Trolling Donald Trump: Loser.com Redirects To Trump’s Wikipedia Page
Loser.com domain owner is not a fan of Donald Trump ? Just like itanimulli.com (reverse of illuminti.com) redirects users to the official website of the...
-
 288Data Security
288Data SecuritySeries of Security Bugs Force Malwarebytes to Start Bug Bounty Program
Good news for security researchers you can now earn some good money by reporting security bugs to Malwarebytes — Thanks to its...
-

 204Cyber Events
204Cyber EventsHeydays for Bitcoin Over? EC Eager to Ban Anonymous Virtual Currency Transactions
The European Commission (EC) has decided to end anonymous virtual currency Bitcoin trading to track money-laundering that “helps terrorist group funding”. The...
-

 312Geek
312Geek2016 Best Hacking Apps for Android Phones
In a world where everything which your computer can do, can be done on your smartphone, hacking cannot be left behind. The...
-

 154Data Security
154Data SecurityDMA Locker: New Ransomware, But No Reason To Panic
DMA Locker is another ransomware that appeared at the beginning of this year. For now it has been observed to be active...
-

 60Cyber Crime
60Cyber CrimeEuropean firms’ financial departments the target of cyberattacks
Two major cyberattacks have siphoned over $50 million and nearly $80 million from a Belgian bank and an Austrian aircraft parts manufacturer,...
-
 160Incidents
160IncidentsComodo Internet Security Installs New Browser by Force, Disables All Web Security
The Comodo app also replaces links and hijacks DNS. Developers have exposed the fact that Comodo Internet Security is actually a security threat...
-
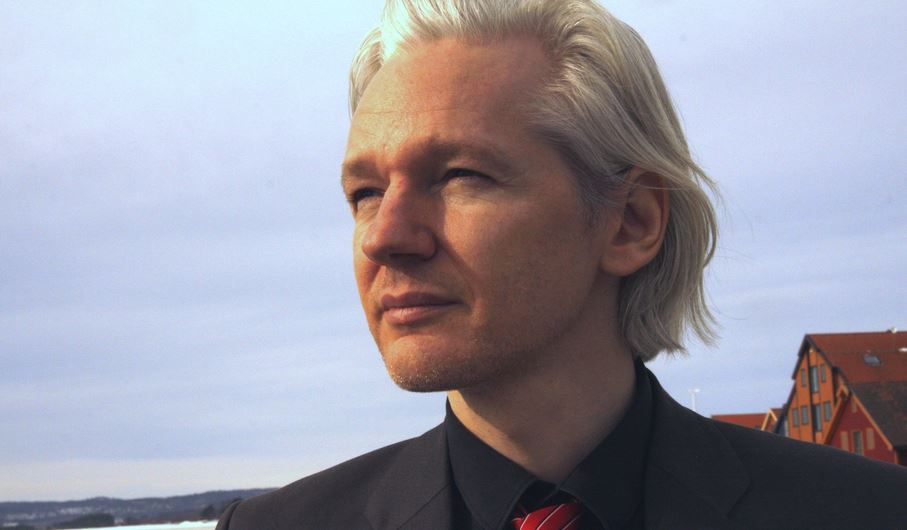
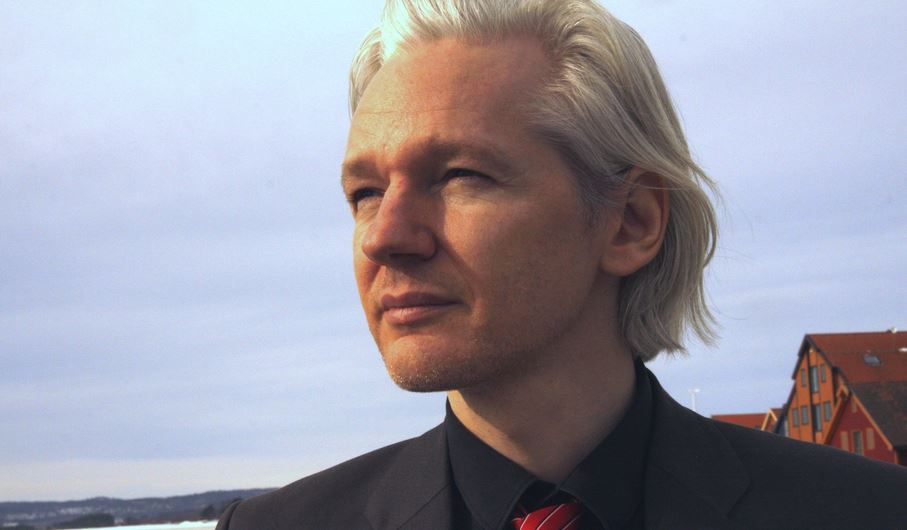 255Hacked
255HackedWikiLeaks Founder Julian Assange Could Be A Free Man This Friday, Thanks to United Nations
Short Bytes: The UN is expected to announce its decision on WikiLeaks founder Julian Assange’s release on Friday. The whistleblower website has...
-
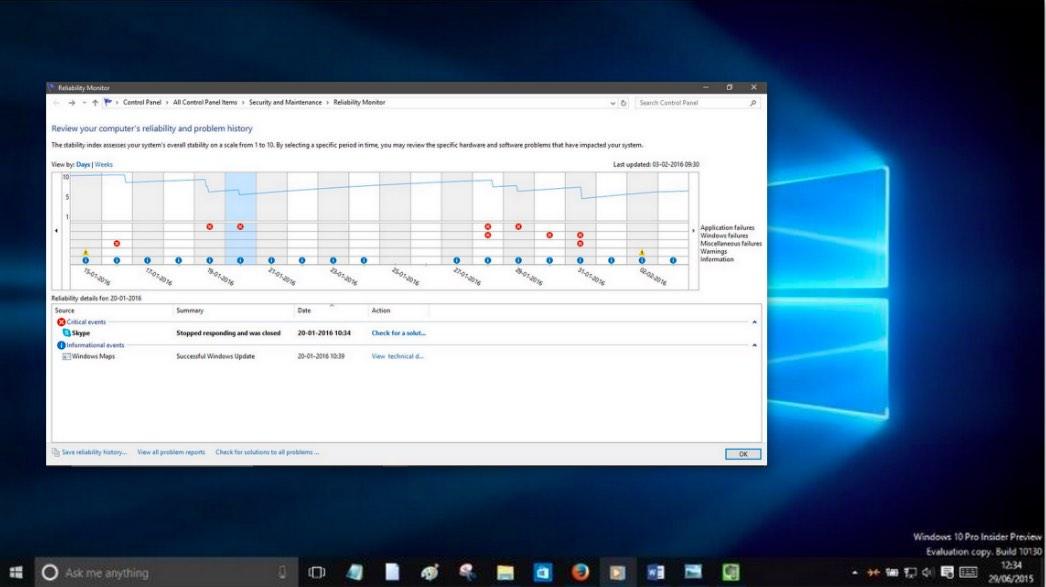
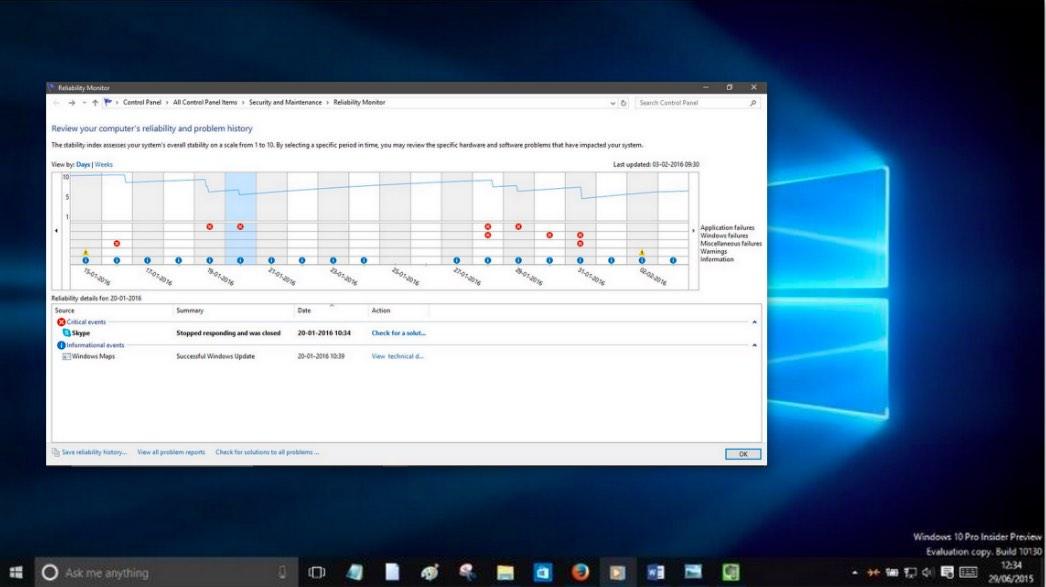 313How To
313How ToTroubleshoot Your PC Using Windows Reliability Monitor
Short Bytes: Windows 10 comes with an inbuilt tool called “Reliability Monitor” using which a user can troubleshoot a personal computer for...
-

 215Data Security
215Data SecurityWikileaks’ Julian Assange could be a free man this Friday, Thanks to UN
Wikileaks founder Julain Assange can be a free man this Friday — His fate depends on the decision from United Nation’s Working Group...
-
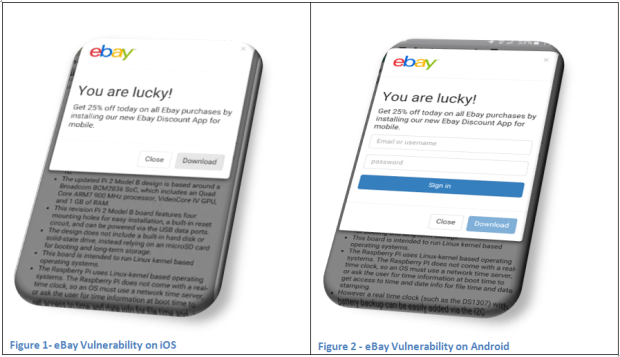
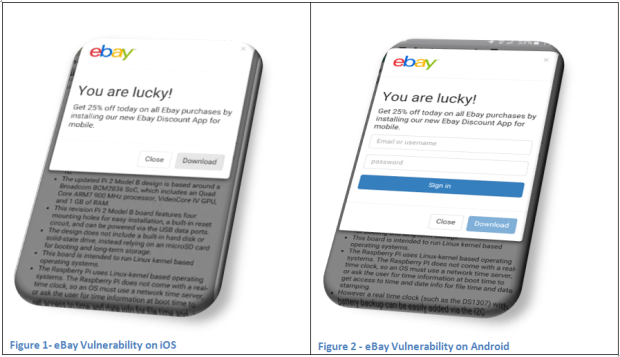 215Incidents
215IncidentseBay Flaw Lets Attackers Push Malware and Launch Phishing Sites
JSF**k JavaScript library abused to deliver malware. Security researchers have alerted eBay’s staff about a vulnerability in its online platform that lets...
-

 197Cyber Crime
197Cyber CrimeHackers Target Pastebin.com with Powerful DDoS Attack
Pastebin.com faced heavy DDoS attacks which forced the platform to go offline. Pastebin.com is a world renowned online platform where users can...
-

 249Geek
249Geek‘SNAP’ Vulnerability Affecting Millions of LG G3 Smartphones Users
Millions of LG G3 smartphone users are at risk of losing critical personal data due to a severe security weakness dubbed as...
-

 206Hacked
206HackedObama’s $6bn Security Firewall EINSTEIN Is Not Good Enough To Protect The US Government
Short Bytes: The U.S. government is working on a firewall named EINSTEIN intrusion detection system that is expected to keep the federal agencies safe...
-

 318Cyber Crime
318Cyber CrimeCrooks Sending Phishing Links in Text Messages To Steal PayPal Account
Text Messages are a Hacker’s Latest Weapon to Dole out PayPal Phishing Scams. The easiest way cybercriminals can try to hack your...
-

 239Geek
239Geek11 Skills And Programming Languages To Become A Professional Web Developer
Short Bytes: Apart from learning the basic skills like HTML and CSS, the road to becoming a successful web developer needs some...
-
 345Malware
345MalwareAndroid has some critical remotely‑exploitable security holes. But can you get the patch?
Remote code execution vulnerabilities have been found in the Android operating system, and patches released for Nexus devices. But what about your...
-

 154Malware
154MalwareEmail from your photocopier? It could be a malware attack
Twenty years ago, the first Word macro malware spread across the planet. Embedded inside a Word document, and rather unhelpfully given a...
-

 147Data Security
147Data SecurityMicrosoft makes Windows 10 a ‘recommended update’ for Windows 7 and 8.1 users
Microsoft has been accused of pushing Windows 10 rather aggressively, and the company’s latest move is going to do nothing to silence...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




