Featured News
-
 185Hacked
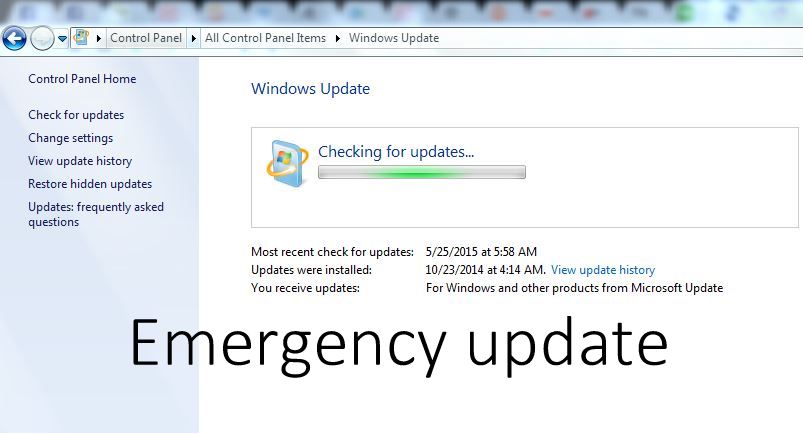
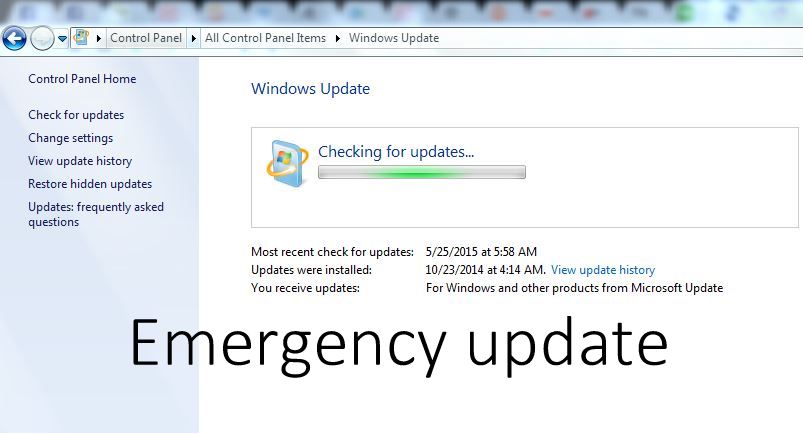
185HackedDownload this Critical Windows Update Now, Flaw Allows Hackers to Control Entire System
A newly discovered vulnerability can allow hackers to remotely execute codes and take over your entire system. A user could be tricked...
-

 215Cyber Events
215Cyber EventsAnonymous Targets Canadian Police, Crashes RCMP’s Website
This week, on July 17th, there was a police-involved shooting in Dawson Creek, British Columbia Canada, where one of the members of...
-
 133How To
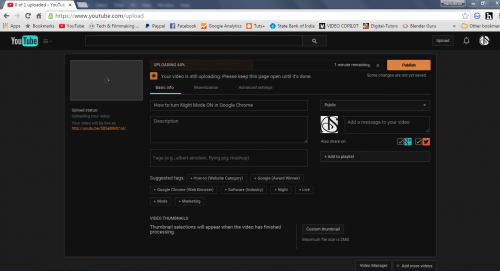
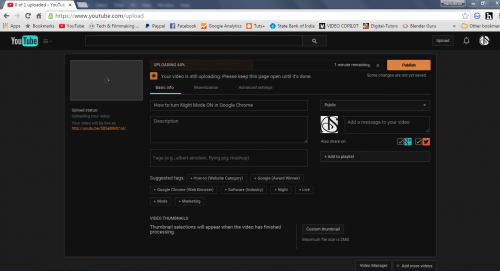
133How ToHow to turn night mode ON in Google Chrome
Google Chrome is the most used browser on the Internet as it is fast and secure. Google Chrome has many extensions in...
-
 213Geek
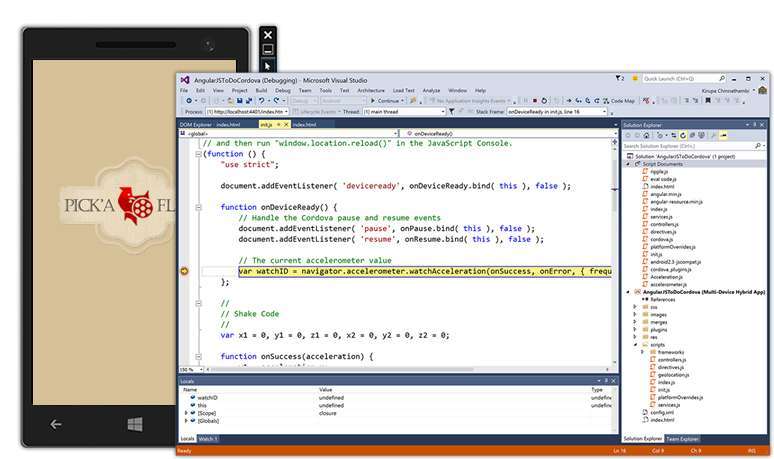
213GeekVisual Studio 2015 and .NET 4.6 Released, Download Now
Today is the Visual Studio 2015 and .NET 4.6 release day. These software from the house of Microsoft have finally graduated exiting...
-

 216News
216NewsHacknet , a real Hacking game.
Developed by Team Fractal Alligator, an Australian one-man studio, Hacknet is “an immersive, terminal-based hacking simulator for PC.” Here’s the official...
-

 129Scams
129ScamsMicrosoft advises ‘spoofed’ Skype users to change passwords
Skype users have been advised by Microsoft to change their passwords following reports that 'spoofed' messages are being sent without user permission.
-

 180Hacked
180HackedInstagram Can Totally Hijack Your Account And Give To Some Celebrity
How cool would it be if somehow your parents were Pitt’s and ended up to name you Brad, or a simple Messi...
-

 102Cyber Crime
102Cyber Crime37 million relationship cheats could be exposed by Ashley Madison hack
The 37 million users of hacked infidelity site Ashley Madison are at risk of having their names and private details leaked, reports...
-
 382Hacked
382HackedMicrosoft: Free Windows 10 Upgrade Comes With 10 Years of Free Updates
Windows 10 is one of most talked about topics on various online forums. Microsoft is leaving no stone unturned to achieve its...
-
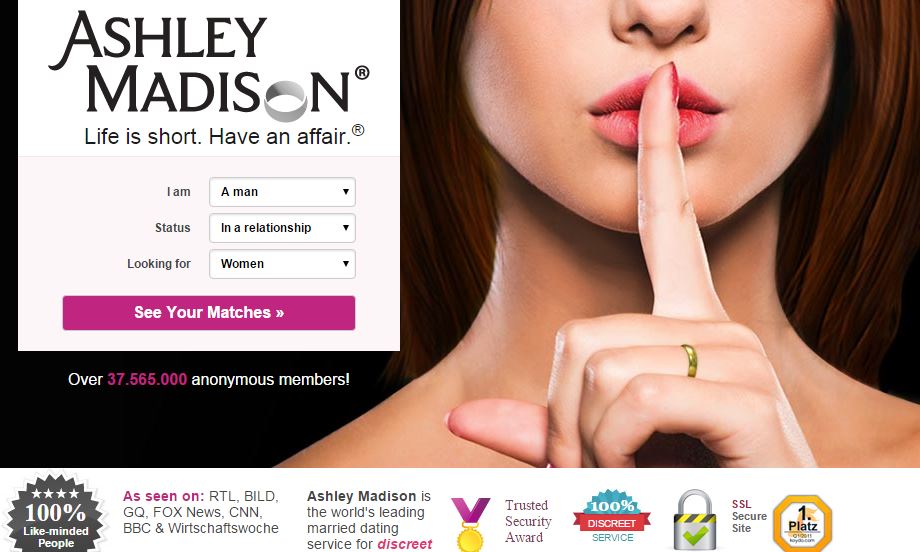
 261Hacked
261Hacked37 Million Adulterers Exposed, Online “Cheating” Site Ashley Madison Hacked
Online cheating website AshleyMadison.com has been hacked, and as a result, large chunks of data has been stolen. The compromised data has...
-
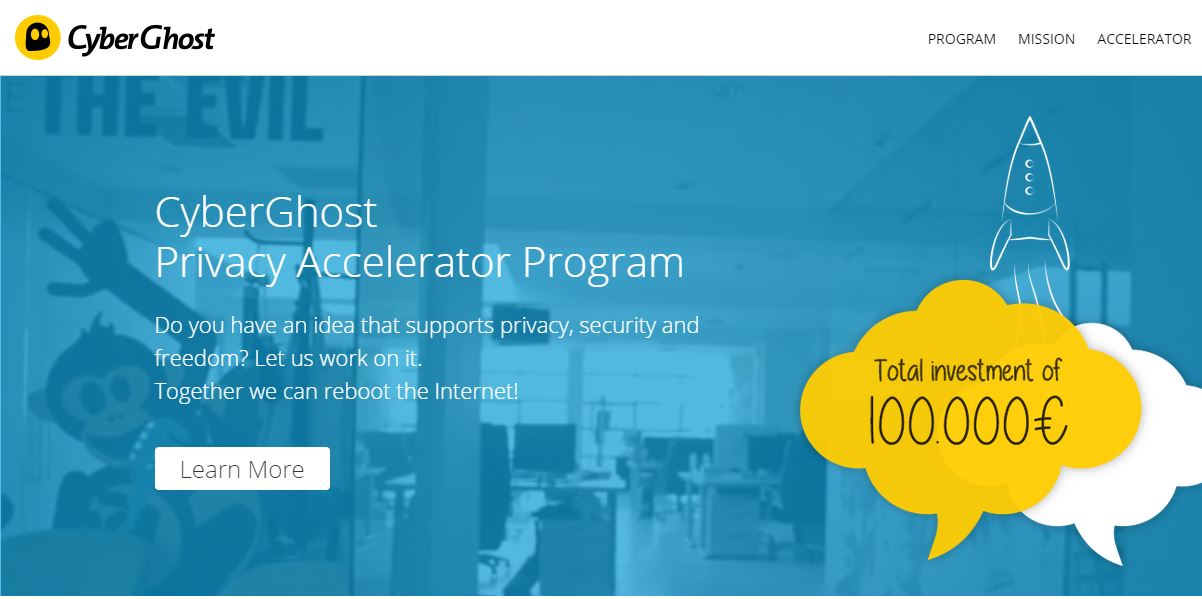
 192Hacked
192HackedCyberGhost Privacy Accelerator Program Offers €100,000 if You Can Make Web a Secure Place
“How Government secretly read your e-mails with this insane law?“ “Snowden’s Revelations: XKEYSCORE is NSA’s search engine.” “Real-Time Cyber Attacks across the globe. ““NSA’s...
-

 274Geek
274GeekTop Netflix Open Source Projects You Must Know
This is the 3rd post in the series covering top open source projects by most popular companies in the world. Today, we...
-
 328News
328NewsCyberwar: Pakistani President’s Website Hacked by Bangladeshi Hackers
Pakistani President Mamnoon Hussain’s website has been hacked by Bangladeshi hackers — 72 other Pakistani government websites have been hacked as well....
-

 226Data Security
226Data SecurityWindows XP Anti-Malware Support Terminated – 180 Million Users Left Vulnerable
Millions of Windows XP users are now left vulnerable to malware attacks as Microsoft has decided to terminate support and security updates...
-

 308Hacked
308HackedThis Hacked Gun Mounted Drone Shoots Bullet in Terrifying Video
The world is getting scarier each day. And I don’t mean the terrorist attacks or cyber threats or global warming, or least...
-
 335Hacked
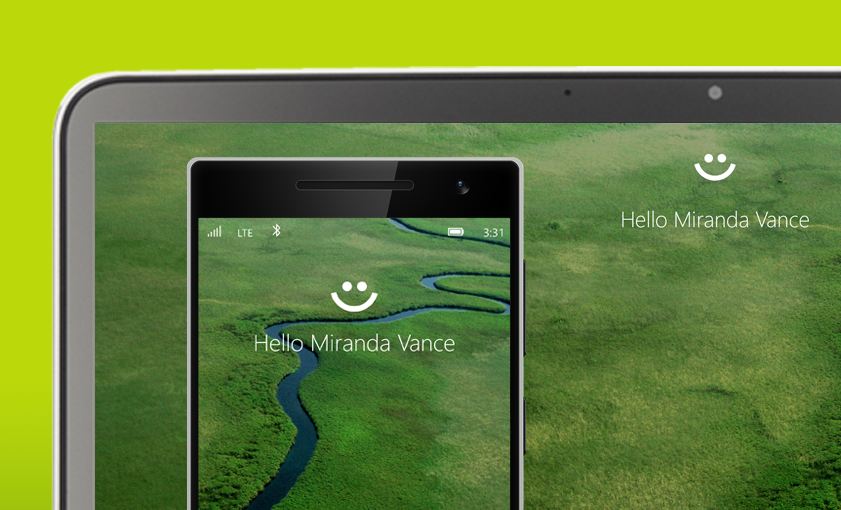
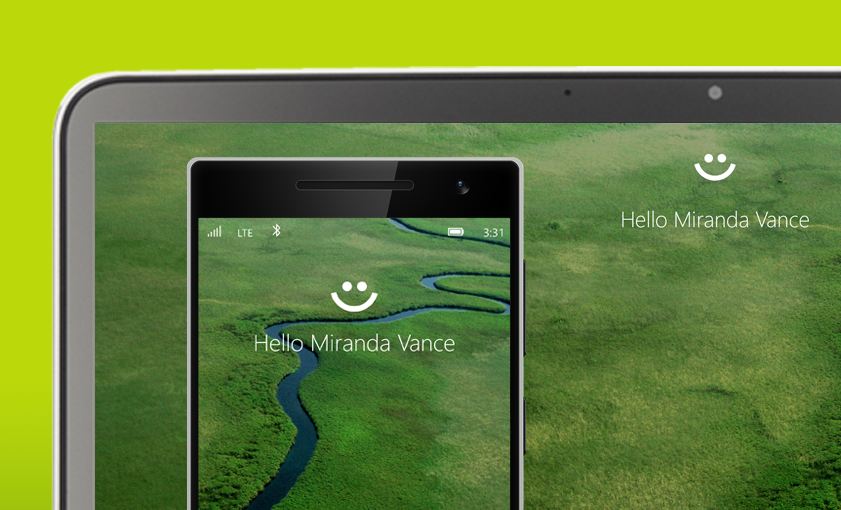
335HackedComplete List of PCs Supporting Windows Hello, the Password Killer Feature of Windows 10
With Windows 10’s Windows Hello feature, you will be able to log into your PCs without any password. Windows Hello users to...
-

 269Geek
269GeekMicrosoft Now Providing Support for Linux Users in Azure
Microsoft Azure cloud platform is very popular among Linux users and now Microsoft has announced that it will be offering limited support...
-
 162Hacked
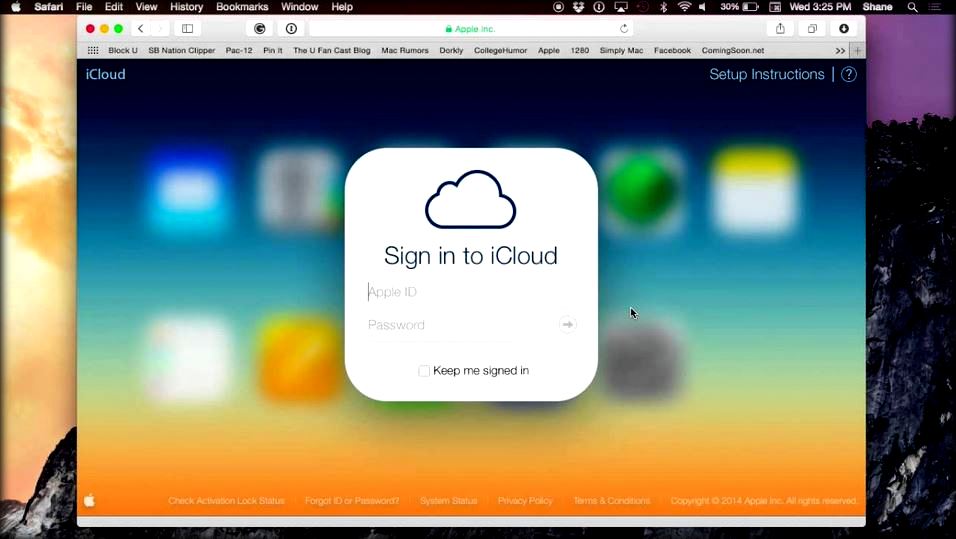
162HackedHow Apple’s iCloud Drive Deletes Your Files Without Any Warning
iCloud Drive is one of the most-used Apple services as it’s a Dropbox-like solution to keep all your devices’ data in sync....
-

 60Cyber Crime
60Cyber CrimeHuge Morrisons data breach due to employee with grudge, court hears
A Morrisons employee with a grudge was responsible for posting personal data of nearly 100,000 staff onto the internet, a court heard.
-

 311Hacked
311HackedFBI Used Hacking Team’s Help to Track Tor User
Earlier this month, as a part of the massive breach at the infamous Hacking Team, numerous documents were leaked. Since then, analysts...
The Latest
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareMalicious Google Ads Pushing Fake IP Scanner Software with Hidden Backdoor
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesGenAI: A New Headache for SaaS Security Teams




