Featured News
-

 70How To
70How To5 Systems Admin relationship tips (so you’re on talking terms again)
Want to mend your systems admin relationship? On this Systems Administration appreciation day, we give you a few tips to help mend...
-
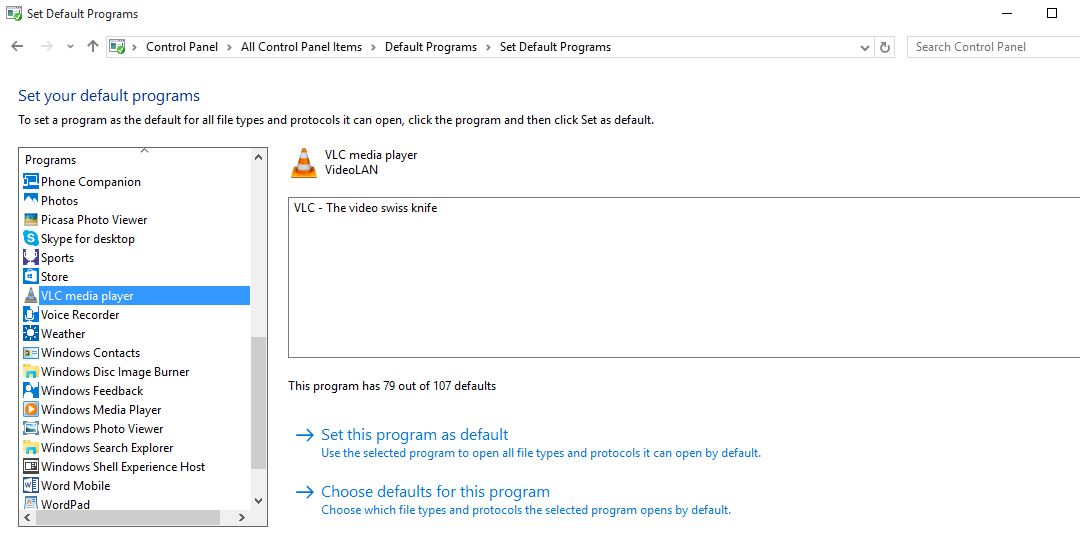
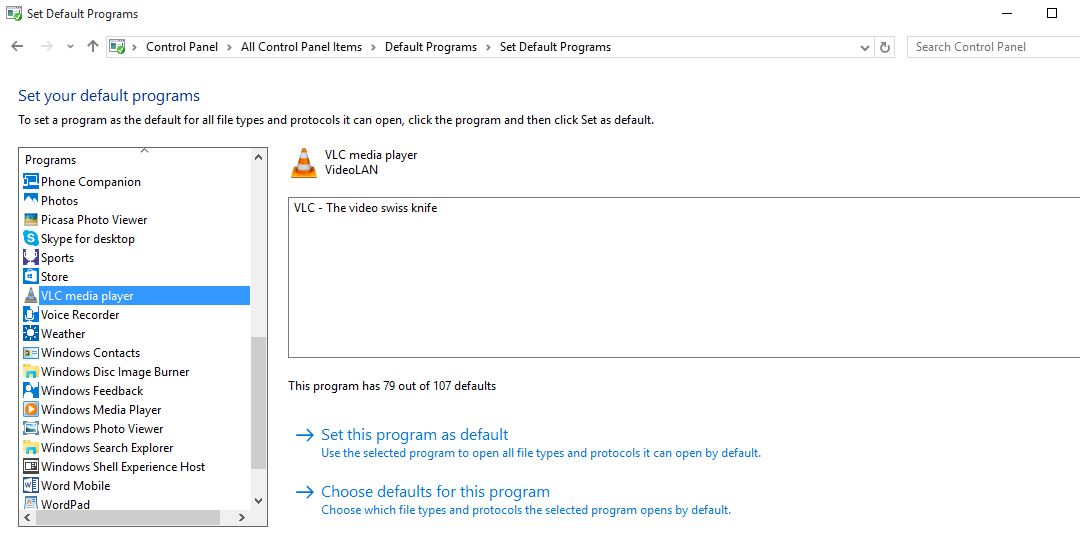 408How To
408How ToHow to Change Default Browser and Programs in Windows 10
Short Bytes : Windows 10 upgrade keeps your files, apps, and settings, but it changes your app preferences of last OS. Today...
-
 220Cyber Events
220Cyber EventsAnti-abortion Hackers Shut Down Planned Parenthood Website
On 29th July 2015, we reported how a group of anti-abortionist hackers hacked into the servers of Planned Parenthood, a pro-abortion organization. Now,...
-
 163Hacked
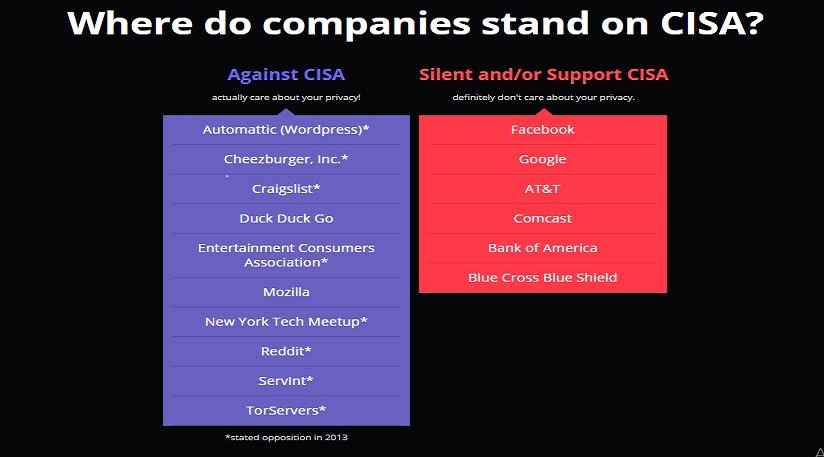
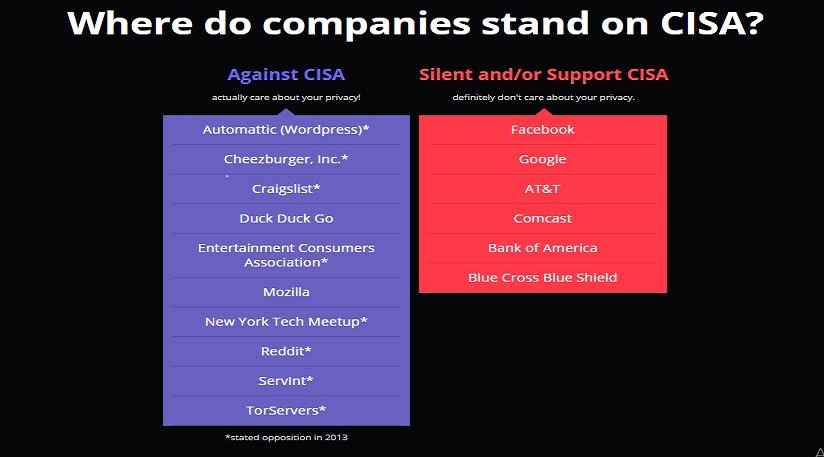
163HackedCISA Bill To Give Your Entire Personal Info To Government
Short Bytes : The recently proposed Cybersecurity Information Sharing Act (CISA) by the government looks like another surveillance law that outrightly gives...
-
 393How To
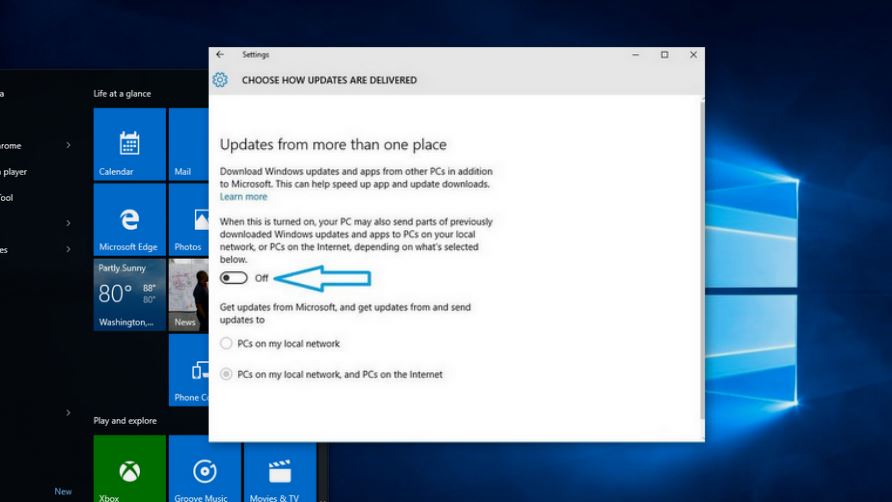
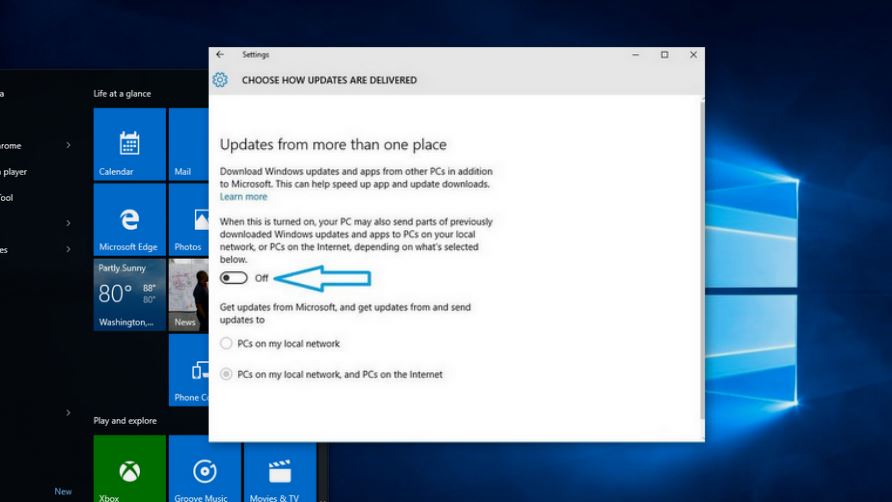
393How ToWindows 10 Steals Your Internet Bandwidth to Send Updates to Others, Disable It Here
Short Bytes: Windows 10 steals your internet bandwidth without your knowledge to share updates with others. This option is enabled by default...
-

 270Data Security
270Data SecurityComputer Controlled Sniper Rifle Hacked, 1000 Rifles Left Vulnerable
Recently we reported that some security researchers managed to hack into the Jeep’s onboard entertainment system to remotely take over the vehicle’s...
-
 310Hacked
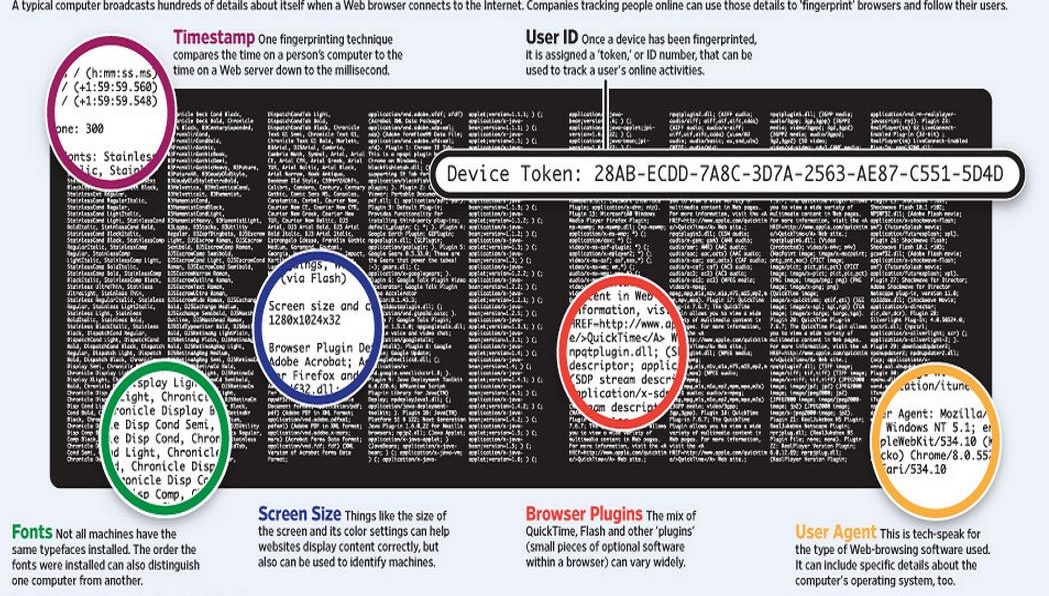
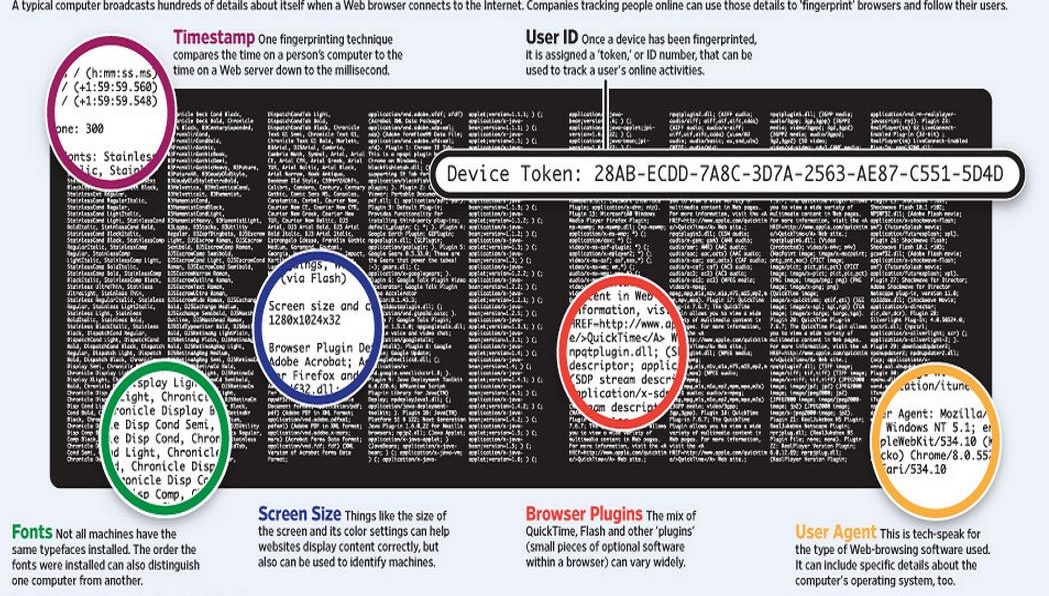
310HackedWhat is Traffic Fingerprinting and How it is Used to Attack Tor Network
Short Bytes: Traffic fingerprinting is a technique used to sniff the web traffic by analyzing the data packets’ flow pattern- without removing...
-

 201Cyber Crime
201Cyber CrimeUnited Airlines customer flight records breached
United Airlines customer flight records have been lost in a data breach it has been reported.
-

 265News
265NewsUnited Airlines Hacked by Same Chinese Group Behind The OPM Breach
From cars to trains from computers to planes, anything connected with the Internet is vulnerable to cyber attacks. It is believed that a...
-

 158Hacked
158HackedHackers Can Hack Smart Sniper Rifles Running on Linux And Change Its Target
Images: Wired Short Bytes : Security researchers have found a way to hack the Tracking Point sniper rifles. These “smart” snipers run...
-

 272Hacked
272HackedExperts Explain The Car Hack Process – How to Hack a Car
Short Bytes : The recent Fiat Chrysler car hack exposed the vulnerabilities and the extent to which insecure IoT can be dangerous....
-

 359How To
359How ToHow to Regain Up To 20GB Disk Space After Windows 10 Upgrade?
If you have got the latest Windows 10 upgrade, you will notice about 15-20GB space missing from your disk drive. These files...
-

 369How To
369How ToHow to Install Windows 10 Without Windows Update
Short Bytes: After rolling out the Windows 10 upgrade, Microsoft has released Windows 10 ISO files. If you don’t want to go...
-

 211News
211NewsGoogle, MSN Domains for Pitcairn Islands Hacked By Bangladeshi Hackers
On July 25, 2015, we reported how a group of Morrocan hackers hacked and defaced the official domains of Google, Microsoft and...
-
 267Geek
267GeekLinux Based Solus OS Now Boots in Flat 1.2 Seconds
Short Bytes : The developer team behind Linux-based Solus distro has achieved a remarkable feat as they brought down the boot time...
-

 180Hacked
180Hacked5 Best Free Android Antivirus Apps of 2015
Short Bytes : Your smartphone is at the equal risk of getting infected by malware as is your computer. Hers’s a list...
-

 198Privacy
198Privacy‘Keystroke Biometrics’ exploit defeats Tor privacy
Security researchers have created a practical privacy attack out of a well-known theory around user behaviour. The attack appears to defeat privacy...
-
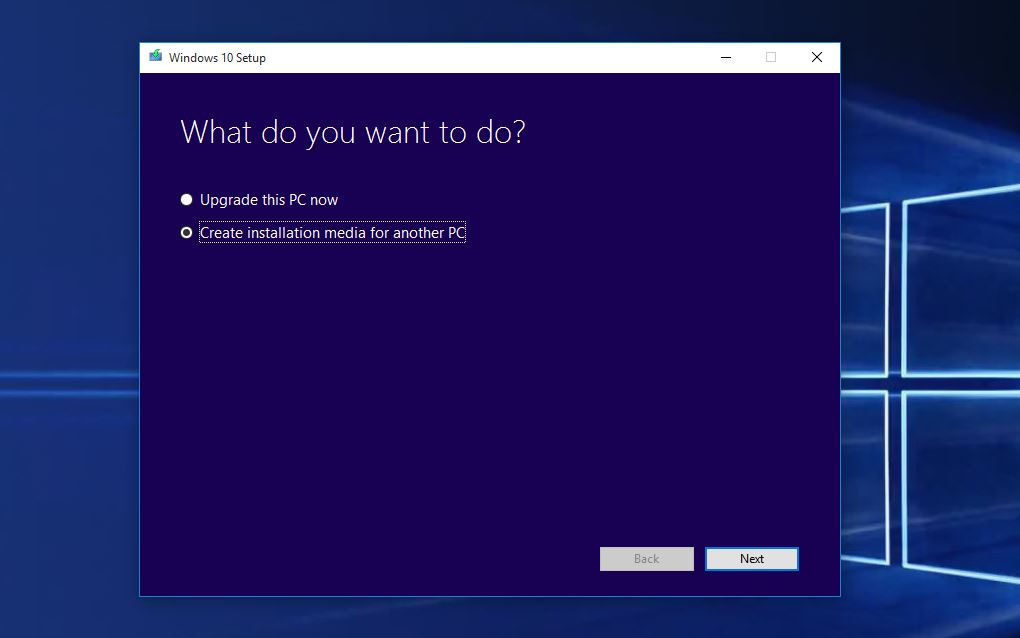
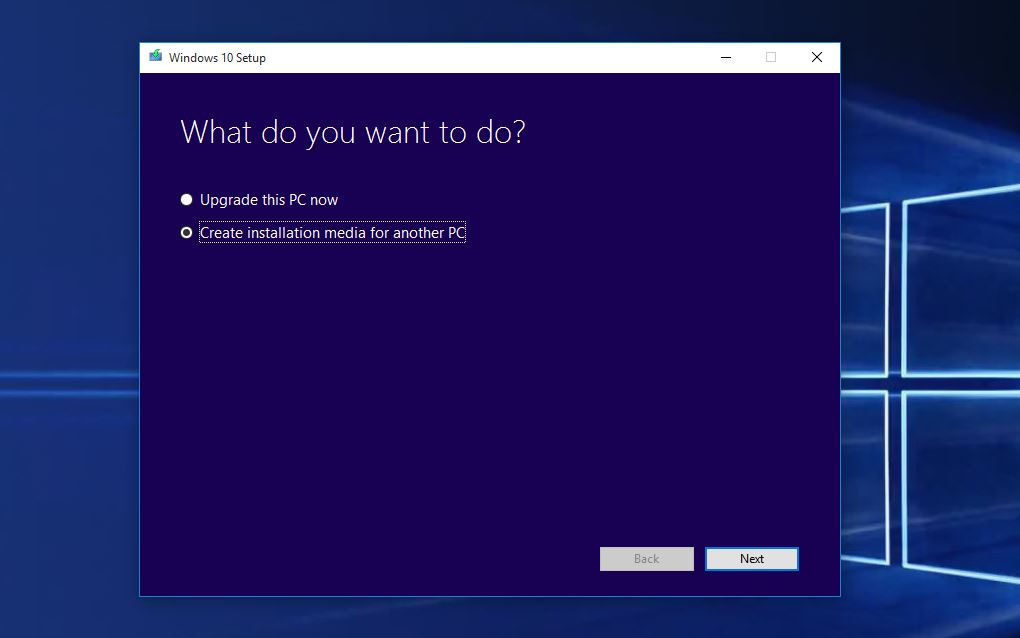 335How To
335How ToHow To Perform A Clean Windows 10 Installation Using ISO Files
Short Bytes: Microsoft has released Windows 10 ISO files for performing a clean install on your PCs after the Windows 10 upgrade....
-

 101Cyber Crime
101Cyber CrimeMoonpig warns of password breach – but it may be more than their users who are at risk
Moonpig, the online personalised card company, has blocked the accounts of an unspecified number of customers after users' details were published online.
-

 104How To
104How ToHow to shop online safely during the summer sales
The summer sales are upon us and there are plenty of good deals to be had online, but internet shopping is not...
The Latest
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareMalicious Google Ads Pushing Fake IP Scanner Software with Hidden Backdoor
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesGenAI: A New Headache for SaaS Security Teams




