Featured News
-

 198Interview
198InterviewLightbulb moment: Why the Internet of Things is a security watershed
Senior research fellow Righard J. Zwienenberg on why the Internet of Things could be *the* key security issue for the foreseeable future.
-
 168Hacked
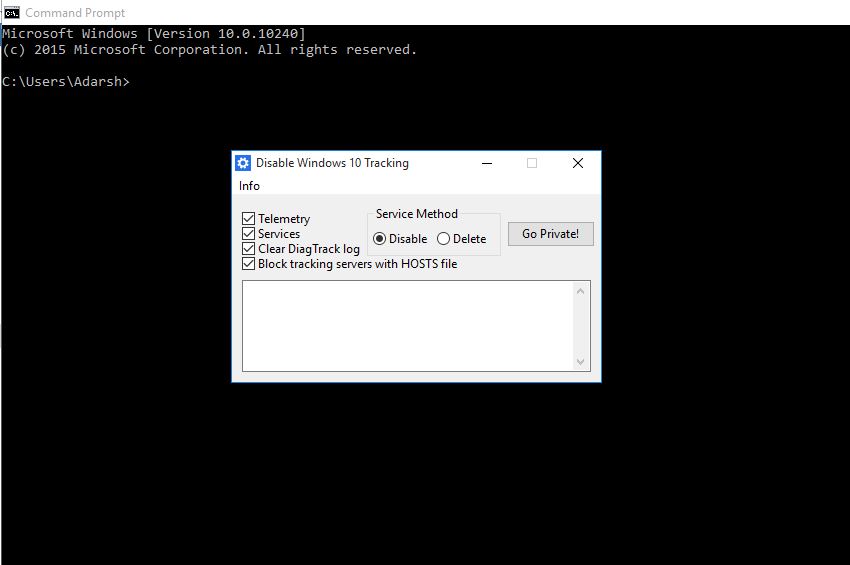
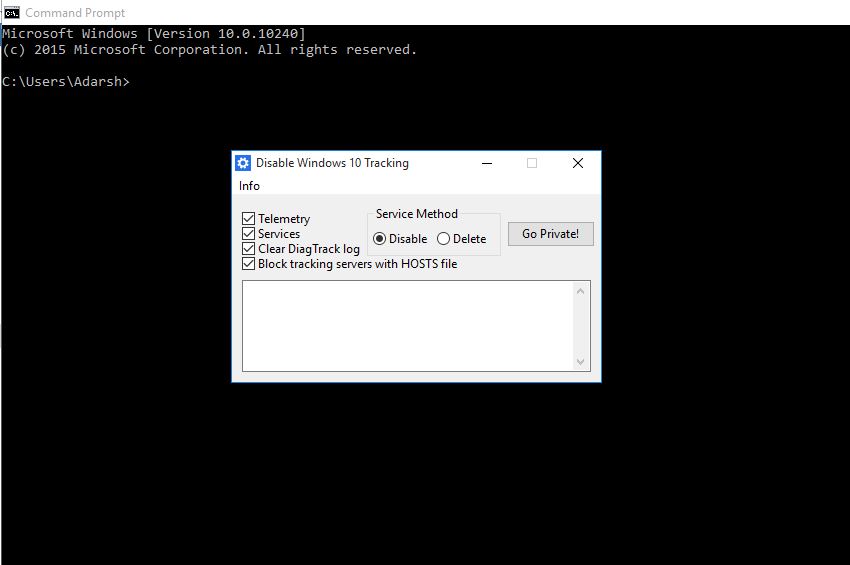
168HackedThis Open-source App Wants to Stop Windows 10 From Tracking You
Short Bytes: A developer has released an open-source tool called Disable Windows 10 Tracking to address your Windows 10 privacy concerns. This tool,...
-

 314Data Security
314Data SecurityYahoo Ad Network Hacked, Infecting Millions of Devices with Malware, Ransomware
Yahoo ad network has been exploited by a group of hackers that resulted in a serving of malware and ransomware adverts on...
-

 223News
223NewsSri Lankan Prime Minister’s Office Website Hacked
The Sri Lankan prime minister Ranil Wickremesinghe has his office website hacked by a hacktivist who hacks for #ForSyria. A hacker going with...
-
 291How To
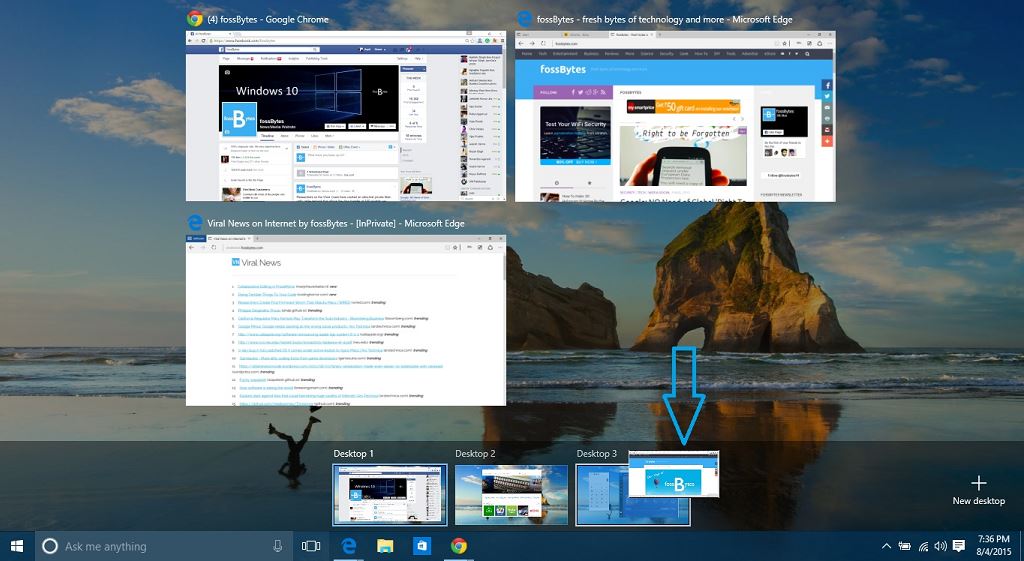
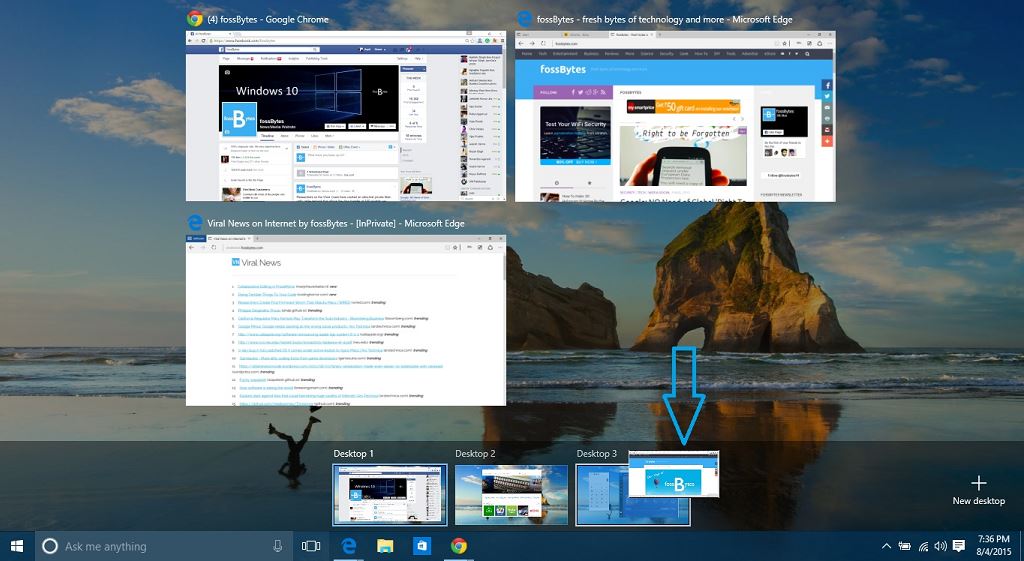
291How ToHow to Create and Use Virtual Desktops in Windows 10?
Short Bytes: Realizing the popularity of Virtual Desktops and needs of a power user, Microsoft has finally integrated this service in Windows...
-

 306News
306NewsDonald Trump’s Website Hacked with Jon Stewart Tribute
Donald Trump organization’s official website Trump.com was attacked by hackers yesterday and a message was posted in which Jon Stewart was praised...
-

 284News
284NewsFirmware Worm Permanently Infects Macs in Seconds
It has been a common understanding that Apple devices are well-protected and less vulnerable. It is also believed that Apple computers are...
-

 132Privacy
132PrivacyHacker sends woman pictures of herself from her own webcam
Hacker sends woman images of herself and her boyfriend, which were captured through their own webcam.
-
 247Lists
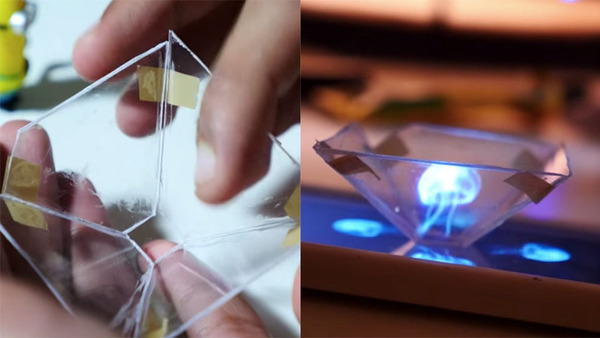
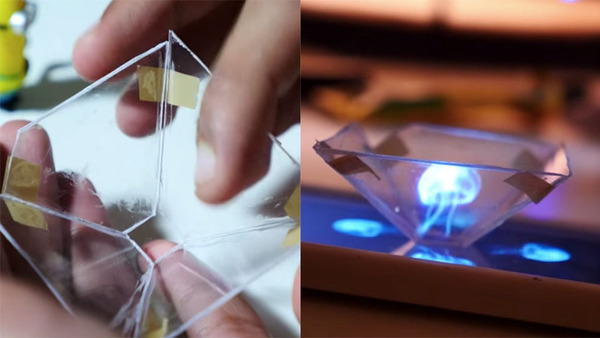
247ListsHow To Make 3D Hologram At Home By the Easiest Method
Short Bytes : Using some stationary items and glass/plastic sheet, you can make 3D hologram at home. Place a pyramidal frustum over...
-

 479Hacked
479HackedExistence of ECHELON Confirmed, Top-Secret NSA Program for Spying on You
A radome at RAF Menwith Hill, a site with satellite uplink capabilities believed to be used by ECHELON (Wikipedia) Short Bytes :...
-
 163Hacked
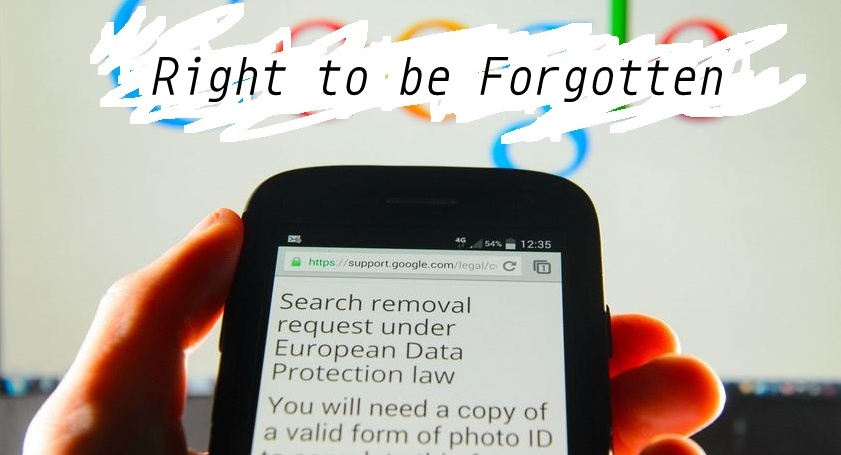
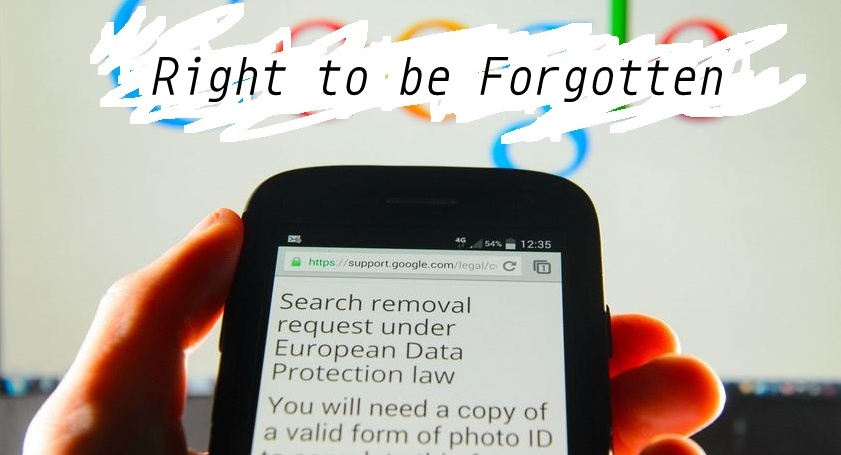
163HackedGoogle: NO Need of Global ‘Right To Be Forgotten’
Short Bytes : Google has written in a new blog post that it won’t be complying with the new French order to...
-

 240Hacked
240HackedThousands of Apps Will Crash When Android M Goes Live, Here’s Why
Short Bytes: A flaw has been reported in thousands of Android apps that will crash them when Android M goes live. The...
-
 299Geek
299GeekHackers Sending Fake Windows 10 Upgrade Ransomware Email, Encrypts Every File
It has not been a week, yet hackers have begun to exploit existing Windows users’ computer by sending them a ransomware, via...
-

 117Data Security
117Data SecurityWindows 10 Uses Your Bandwidth to Send Updates to Other Users
We all are aware that Microsoft has recently released the latest version of Windows i.e. Windows 10 which is available as a...
-

 340News
340NewsAnti-ISIS Kurdish Hacker Targets Etowah County Sheriff’s Office Website
MuhmadEmad, a Kurdish hacker known for his anti-ISIS views is back in news and this time with yet another high-profile hack —...
-
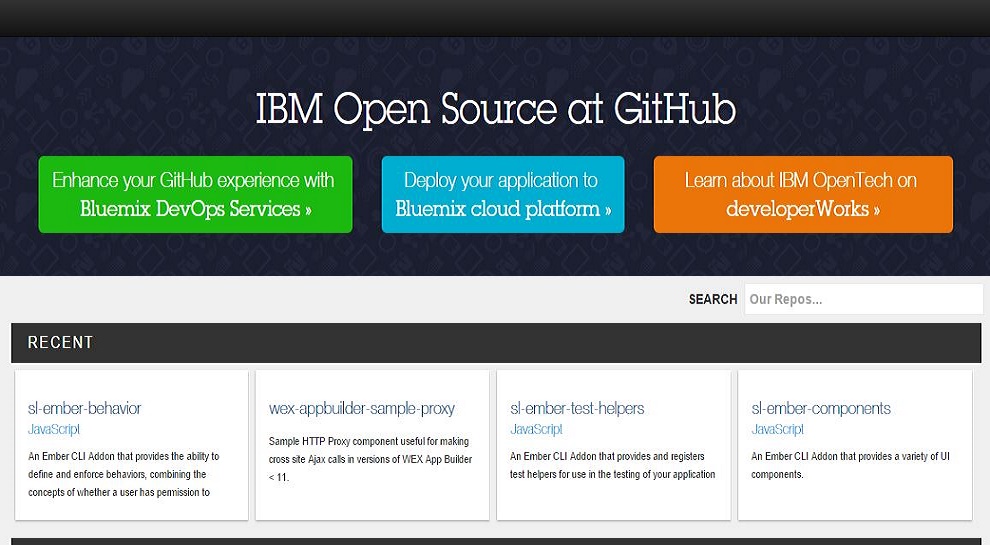
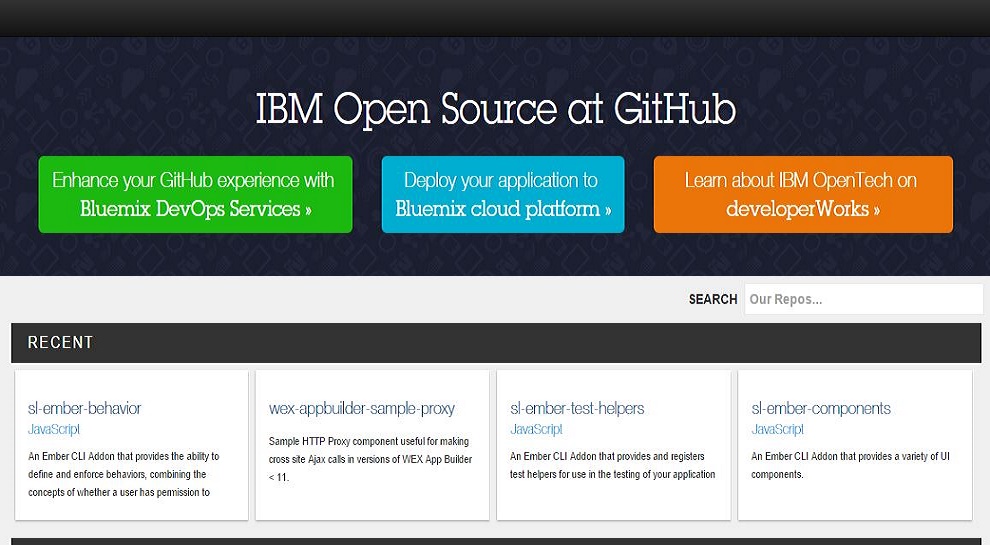 199Geek
199GeekIBM Open Sources 50 Projects, Launches developerWorks Open
Short Bytes: Technology pioneer IBM has open sourced 50 tools and apps. These tools cover a large interest area varying from Cloud, Analytics, IoT,...
-
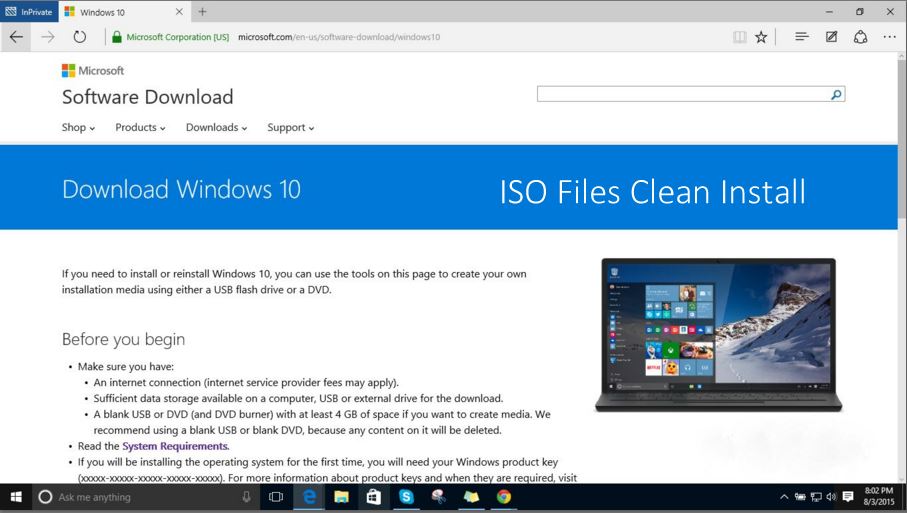
 260How To
260How ToDon’t Perform Clean Install of Windows 10 WITHOUT Upgrading First
Short Bytes: I’m writing this article to warn the users who are trying to perform clean install of Windows 10 on their...
-
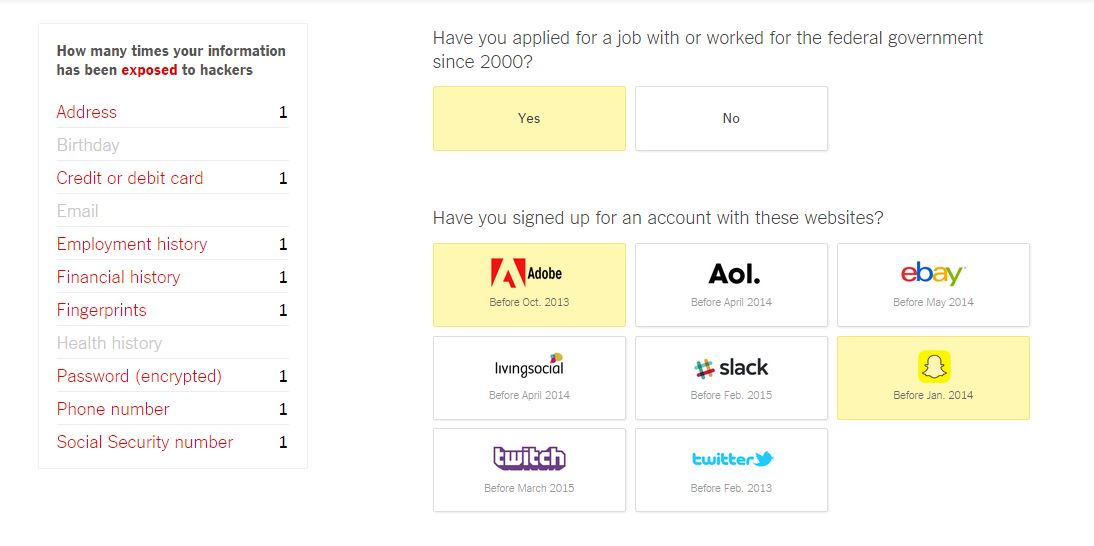
 269Hacked
269HackedHow Many Times Has Your Data Been Exposed to Hackers? Take The Quiz And Know
Short Bytes: The New York Times has come up with a quiz that will tell you if your personal information has been...
-
 375How To
375How ToHow to Downgrade Windows 10 to Windows 7 or 8.1 in Simple Steps
Short Bytes: What if you don’t like Windows 10? There are simple ways to downgrade from Windows 10 to Windows 7 or...
-

 195Cyber Events
195Cyber EventsAnonymous Brings Down Taiwan Government Websites
The online hacktivist Anonymous has shut down Taiwan government websites and has termed the act as “just the beginning” of a series...
The Latest
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareMalicious Google Ads Pushing Fake IP Scanner Software with Hidden Backdoor
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesGenAI: A New Headache for SaaS Security Teams




