Featured News
-

 285Data Security
285Data SecurityHackers Can Disable House Arrest Ankle Bracelet without Raising Alert
Another blow to the law enforcement agencies – researcher from leading security group hacks his way out of ankle bracelet without raising...
-
 198Hacked
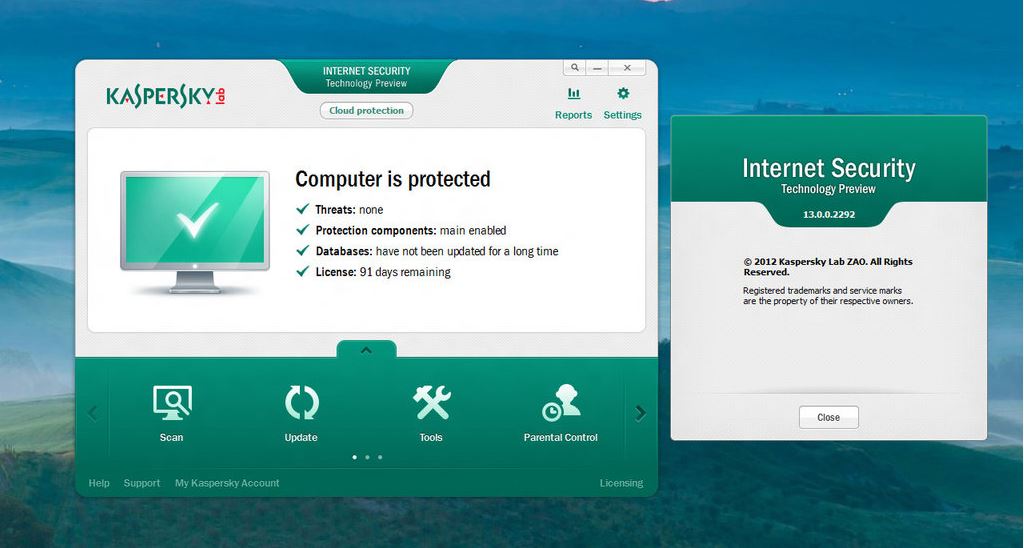
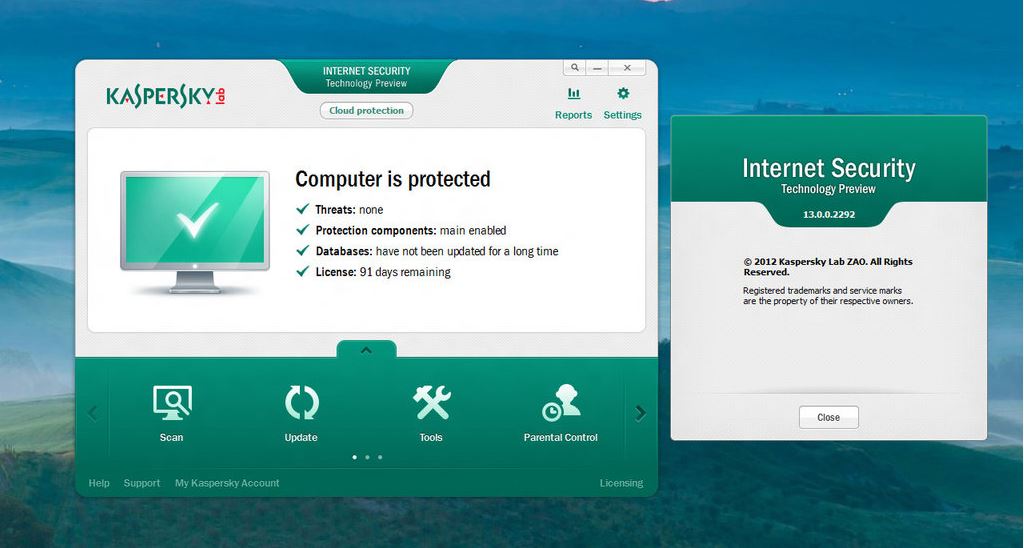
198HackedKaspersky Antivirus Made Fake Malware for More Than 10 Years – Ex-employees
Short Bytes: Two former employees of the security firm Kaspersky labs have told Reuters that the Russian company made fake malware for...
-

 127Opinion
127OpinionAre you still vulnerable to Stagefright? Get your Android device checked now
Security researchers found a vulnerability in Android that could allow attackers to steal information from smartphones through remotely executed code via a...
-
 162Secure Coding
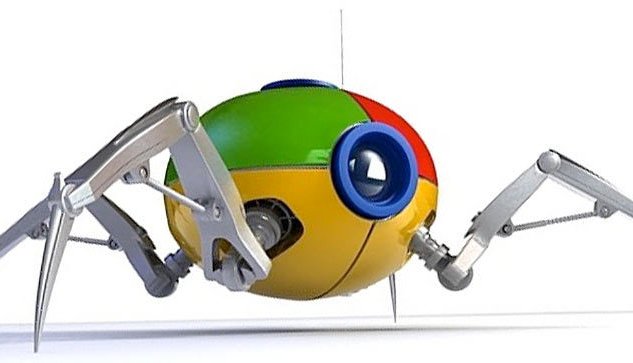
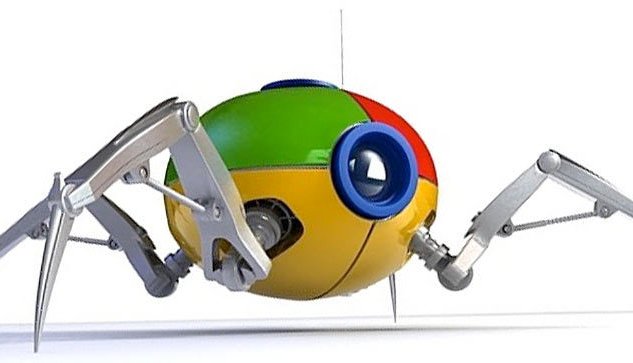
162Secure CodingBuilding your own Web Crawler
Web crawler is a program that browses the Internet (World Wide Web) in a predetermined, configurable and automated manner and performs given...
-

 302News
302NewsThis Aerial Assault Drone Can Hack Computers Inside Walled Compounds
A drone is known for killing people or for its surveillance capabilities, but an aerial assault drone with hacking capabilities? Yes, you read that...
-

 77Malware
77MalwareSignatures, product testing, and the lingering death of AV
Is it time to revalue the role of anti-malware? Maybe, but uninformed or intentionally misleading mutterings about signatures are not where to...
-

 165Surveillance
165SurveillanceExposing Facebook privacy flaw is a crime? Sure Seems Like It
Aran Khanna, a Harvard student, was deprived of a chance to intern at Facebook after he exposed a critical privacy related flaw...
-

 361Hacked
361HackedWindows 10 Sends Tons of Data Every 30 Minutes to Microsoft Even When Told Not To
Short Bytes: Microsoft has some options in Windows 10 to enable the privacy protection, but according to some latest research done by...
-

 182How To
182How ToHow to Check the Status of Popular Websites
Short Bytes: Every popular online service exposes a status page to show the status of various service they offer to end user...
-
 338How To
338How ToRevenge of Mozilla: Firefox 40 for Windows 10 Changes Cortana’s Default Bing Search
Short Bytes: Mozilla has released Firefox 40 for Windows 10 and it comes with changes in user interface trying to blend with...
-

 252Privacy
252PrivacyHow to stop pervy pics popping up on your iPhone
Don't be cyber-flashed by a pervert. Make sure that your iOS device's AirDrop settings are configured properly to protect your eyes from...
-
 284News
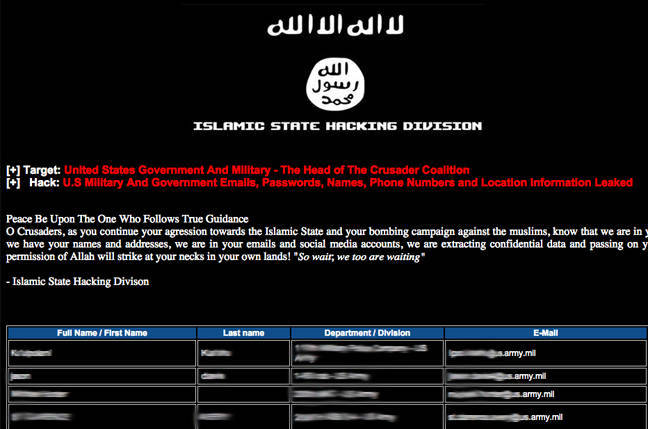
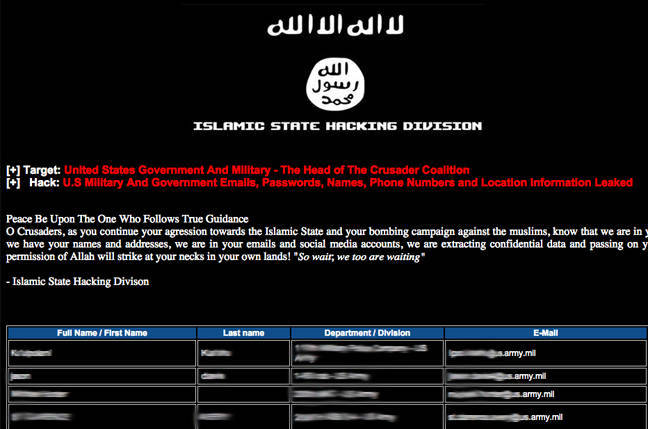
284NewsISIS Affiliated Hackers Leak Hacked Data of 1500 U.S. Military, Govt Personnel
A group of ISIS Affiliated Hackers has claimed to have hacked U.S. government servers stealing the personal data of hundreds of Government...
-
 293Geek
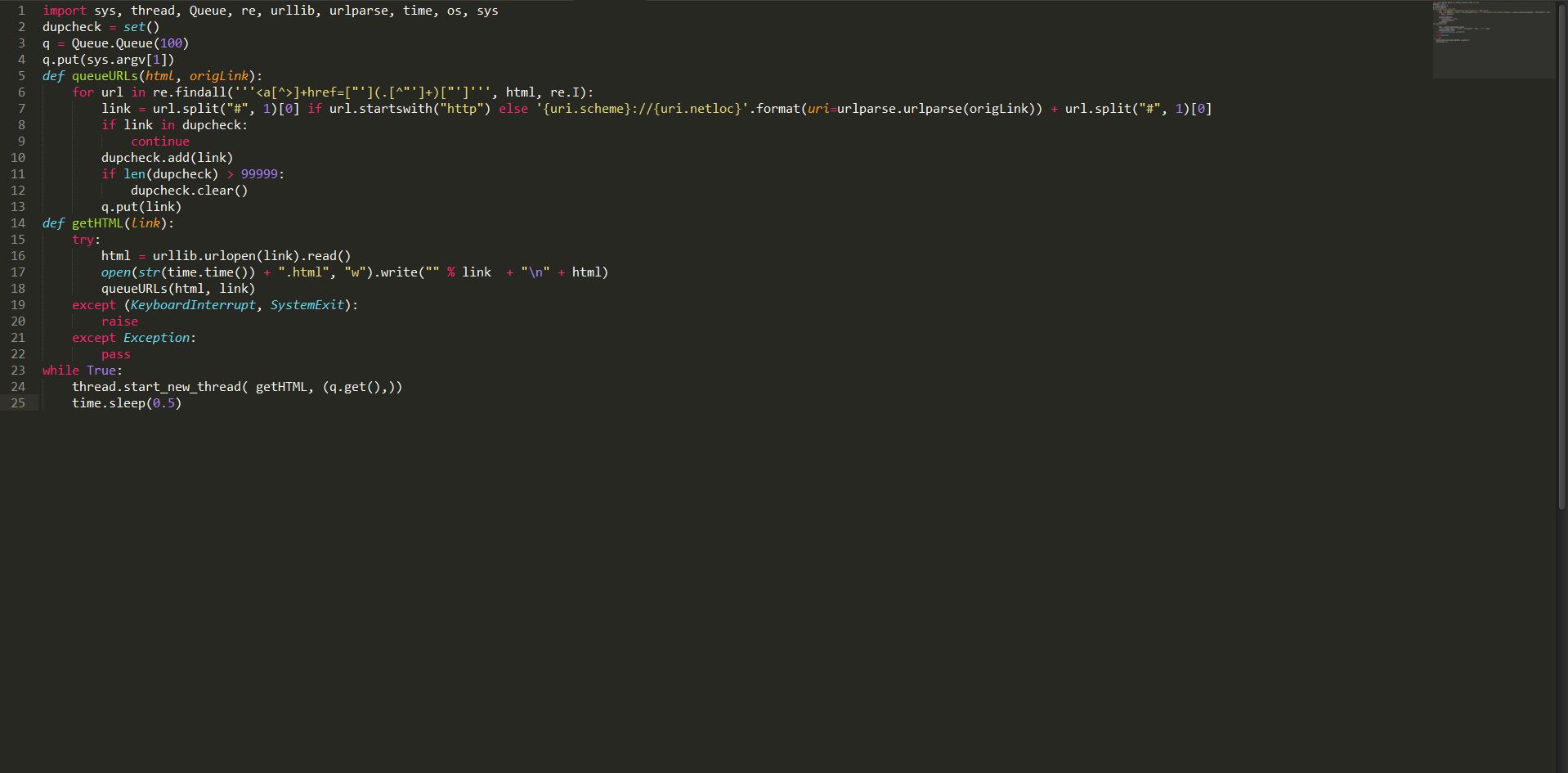
293GeekHow to Build a Basic Web Crawler in Python
Short Bytes: Web crawler is a program that browses the Internet (World Wide Web) in a predetermined, configurable and automated manner and performs...
-

 267Data Security
267Data SecurityResearchers Show How To Hack Corvette with A Text Message
A video demonstration by the University of California researchers how a simple text message can control your car. The months of July and August have...
-
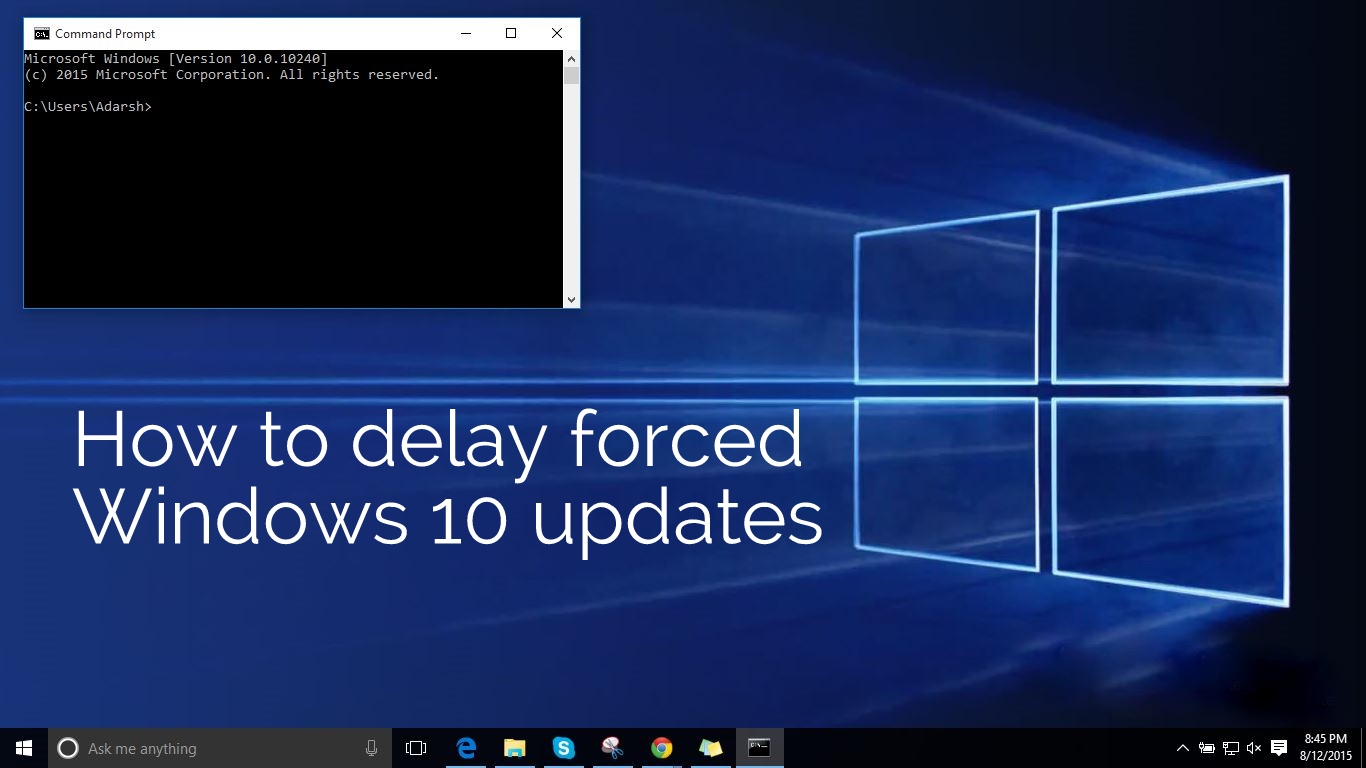
 398How To
398How ToHow To Delay Forced Windows 10 Updates By Enabling Metered Connection Option
Short Bytes: With Windows 10, Microsoft has also overhauled the Windows Update process. You might already be knowing their no way of pausing...
-

 350Data Security
350Data SecurityWindows 10 Security Flaw Could Be Used To Exploit User Credentials
The first ever security flaw in Windows 10 is here — A team of security researchers have found a vulnerability in the...
-

 304News
304NewsCover Your Cams: Webcam of This Couple Got Hacked While Watching Netflix
Earlier we reported how hackers are using Remote Access Trojan (RAT) to get into your computer and record your online activity including your webcam...
-

 327Hacked
327HackedTop 10 Websites/Services To Protect Your Online Privacy
Short Bytes: In the world of cyber threats and privacy breaches, here’s a list of 10 websites and services you should know to...
-

 251Wifi Hacking
251Wifi HackingHacking WiFi – Selecting the best strategy
Not every hack will work under every circumstance, so choosing the right strategy is more likely to lead to success and less...
-

 248Hacking Tutorials
248Hacking TutorialsOllydbg – Cracking software like a pro
If you’ve ever wondered how software pirates can take software and crack it time and time again, even with security in place,...
The Latest
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareMalicious Google Ads Pushing Fake IP Scanner Software with Hidden Backdoor
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesGenAI: A New Headache for SaaS Security Teams




