Featured News
-

 263Hacked
263HackedKali Linux 2.0 is Released, Download ISO and Torrent Files Here
Short Bytes: Kali Linux 2.0 has been released with tons of new features and it’s now based on Debian Jessie. It comes...
-

 111Cyber Crime
111Cyber CrimeHackers Steal $47 Million From American Tech Firm Ubiquiti
An unusual admission has been made by a tech firm to its investors — Posing as its employee, a hacker stole $46.7...
-

 219Data Security
219Data SecurityFacebook API Security Flaw Left 1.44 Billion Users’ Identities at Risk
A security flaw in the Facebook API allows hackers to decrypt and scan IDs, which left 1.44 billion Facebook users identities at...
-

 259How To
259How ToHow To Install Android Apps on Windows 10 Mobile
If your bored of using Windows phone then you can try this tutorial. In this article we will teach you “How To...
-

 295Data Security
295Data SecurityGas Stations Offering Internet-linked Fuel Tanks New Target for Hackers
In 2013, we at HackRead reported how oil and gas sector faces serious physical and online security threats. Now researchers have found...
-

 345How To
345How ToTop 10 Best Ways to Improve Your Wi-Fi Router’s Performance
Short Bytes: Today we are bringing you some of the best ways to improve your Wi-Fi router’s performance. This top 10 list...
-

 130How To
130How ToHow To Remove Pre-Installed Apps on Windows 10
Many users might hate these pre-installed apps in Windows 10, so we have made an article on How To Remove Pre-Installed Apps...
-
 171News
171NewsAnonymous Hacks Mexican Govt Website, Demand Justice For Rubén Espinosa
The online hacktivist Anonymous attacked the Mexican government website against the murder of Rubén Espinosa, a local photojournalist. Anonymous Mexico is all...
-

 110Opinion
110OpinionDEF CON – Upgrading your mom’s basement
If Black Hat is becoming the new RSA, then DEF CON is oozing toward Black Hat, it seems, and B-Sides is the...
-

 191Surveillance
191SurveillanceResearchers Develop Glasses To Protect You from Facial Recognition
Facial recognition software is cropping up everywhere, so it was only a matter of time before anti facial recognition tech started to catch...
-

 242Hacked
242HackedPakistani Intelligence Planning Hacking Attacks, Warns Indian Government
Short Bytes: The government of India has warned its six ministries regarding a probable Pakistani hacking attack to retrieve sensitive information from the computers...
-

 343News
343NewsHacking GPS Signals of Smartphones and In-Car Navigation System
We have already discussed that how our online connected world has become vulnerable to the hacking, which is causing our day-to-day things...
-

 364Geek
364GeekWindows 10 is Free, But Microsoft is Charging For Add-Ons/Other Features
Windows 10 is absolutely free for those who are upgrading from Windows 7 or Windows 8, but Microsoft played a clever trick...
-

 343News
343NewsHackers Turn Bus Terminal into Adult Movie Theater
Websites being the target of hackers is not a new phenomenon; we read about it every day. What one will not read...
-
 146How To
146How ToHow to Fix Windows 10 Brightness Control Not Working Issue
Short Bytes: Some Windows 10 users are experiencing a Windows 10 brightness control “not working” issue. This problem in the relevant drivers...
-

 307Hacked
307HackedFind a Bug in Windows 10, Get Up to $100,000 Microsoft Bug Bounty
Short Bytes: Microsoft has announced that it has updated its bug bounty program and increased the maximum $50,000 reward to $100,000. This...
-

 210Hacked
210HackedNow Electric Skateboards Have Been Hacked Using “FacePlant” Exploit
Short Bytes: Security researchers in Australia have exposed a serious flaw in the low energy Bluetooth controlled devices, as they hacked an...
-

 304Data Security
304Data Security7 Unexpected Hacks of 2015, Thanks To DefCon and Black Hat
This year, at DefCon 23 and Black Hat USA 2015 security conferences, hackers are going to discuss how vulnerable and severely flawed...
-

 246News
246NewsTiny Drones Using Insect-Like Vision for Better Navigation
Researchers and designers are working together to design tiny bug-sized drones but what’s giving them a hard time is their navigation system....
-
 195Geek
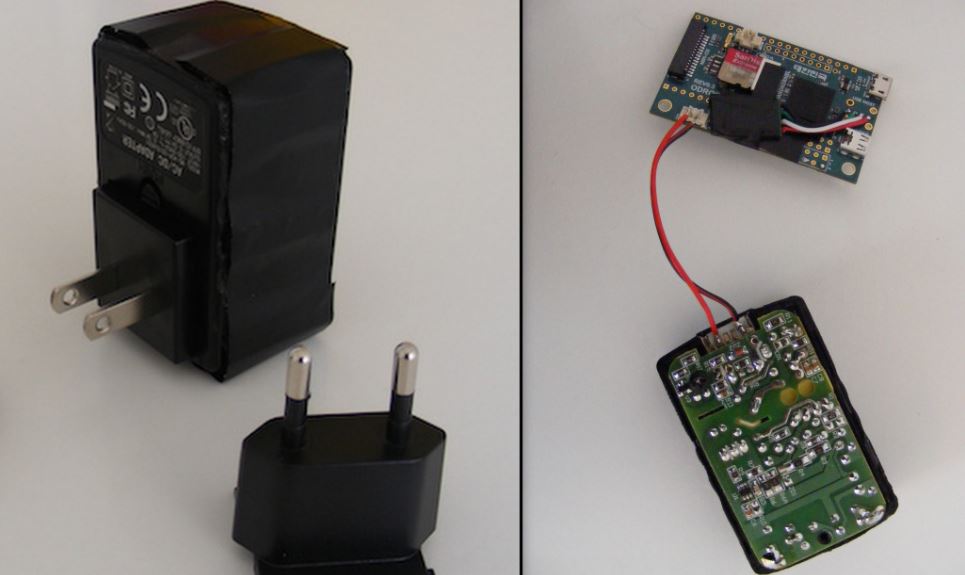
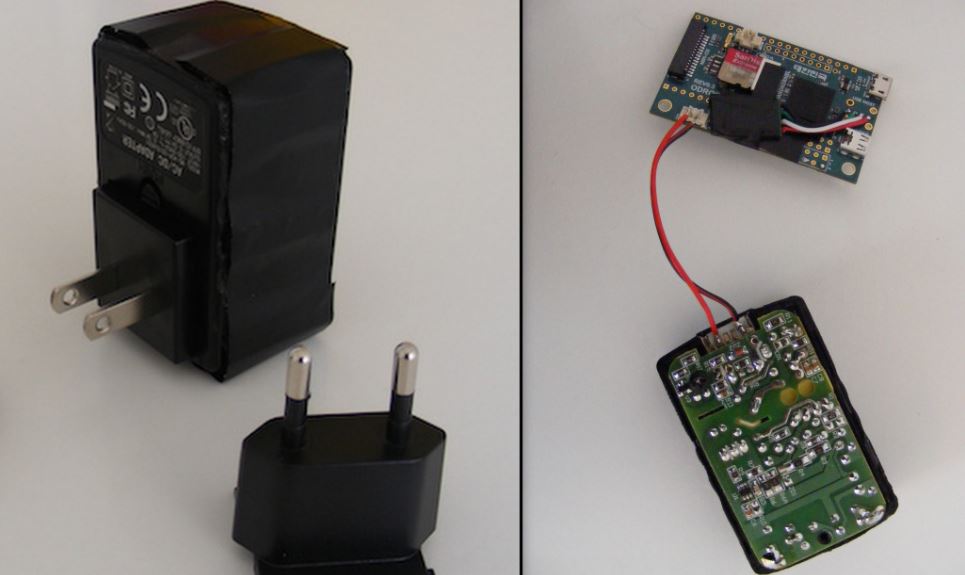
195GeekHow to Convert a USB Charger Into a Linux Computer
Short Bytes: This DIY from Chris Robinson of NODE will show you how to make your own Linux computer from a USB...
The Latest
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareMalicious Google Ads Pushing Fake IP Scanner Software with Hidden Backdoor
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesGenAI: A New Headache for SaaS Security Teams




