Featured News
-

 66Cyber Crime
66Cyber CrimeDozens arrested in international Darkode crackdown
International law enforcement agencies have arrested more than 60 people suspected of carrying out cybercrime associated with the Darkode forum.
-
 264Geek
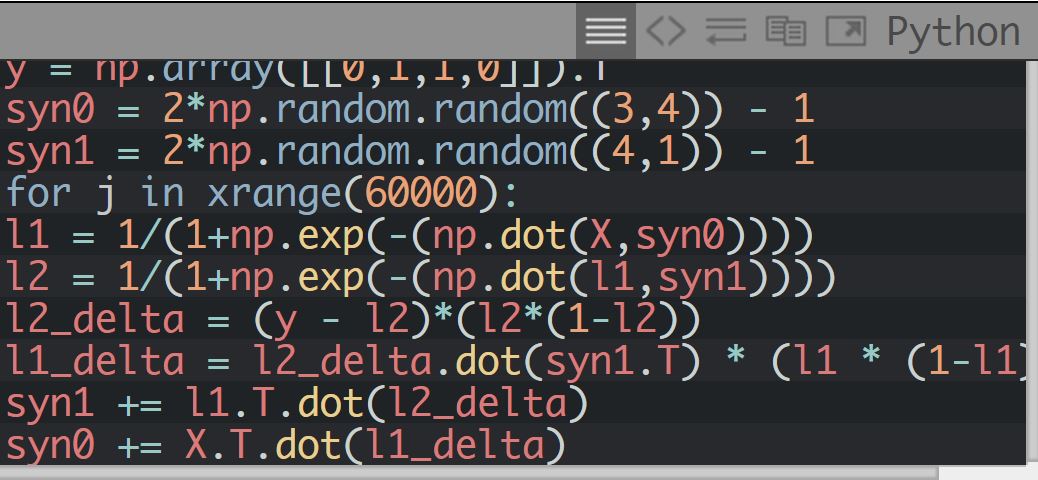
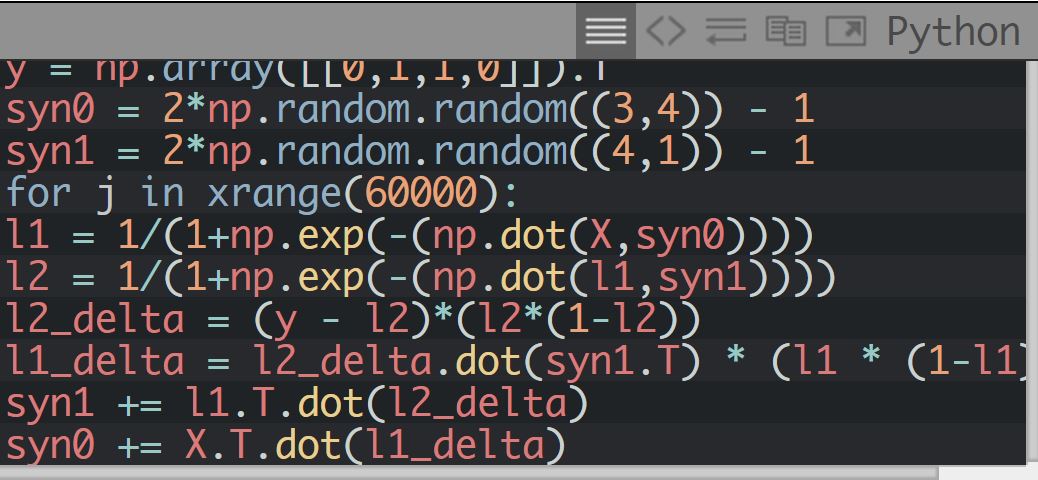
264GeekA Neural Network in 11 Lines of Python
Artificial Intelligence is getting embedded in our lives on a regular basis in form of various speech recognition software, digital assistants like...
-

 294Hacked
294HackedHow Government Secretly Reads Your Emails With This Insane Law
Today, the common public is aware, more than ever, regarding rights and privacy. Recent revelations made by whistleblowers like Edward Snowden and...
-

 264Data Security
264Data SecurityProxyHam Device Providing Wi-Fi Access Anonymously is Gone
We all remember that game-changing personal hardware proxy device that guaranteed to provide you with Anonymous access to the Wi-Fi located up...
-
 470Operating Systems
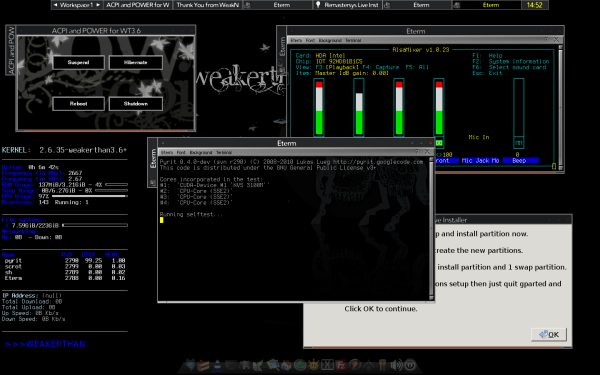
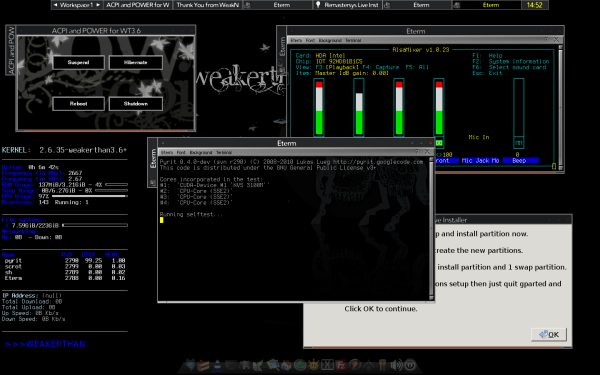
470Operating SystemsWEAKERTH4N – Another Hacking OS
Most of the hackers would have heard about Backtrack. Weakerthan is another Linux based pentesting distro which is really good.. I think Weakerthan is second...
-
Bruteforcing
Removing a PDF password
Now a days, we all save our data in a Word file or a PDF file. Some have basic information and some...
-

 294Data Security
294Data SecurityGood News: Mozilla Kicks Out Flash by Default on Firefox Browser
Mozilla Firefox has blocked Adobe Flash Player and it’s a good news. If you are a regular Firefox user you must have...
-

 333News
333News8 Technologies That Can Hack Into Your Offline Computer and Phone
Whenever your computer, smartphone device or any other Internet-capable gadget is connected to the Internet, there is always a risk of security...
-

 119Privacy
119PrivacyCheap wifi privacy device pulled with no explanation
A planned Defcon talk around a low-cost privacy device called ProxyHam has been cancelled.
-

 56Cyber Crime
56Cyber CrimeOperation Liberpy: Keyloggers and information theft in Latin America
In April, ESET’s Laboratory in Latin America received a report on an executable program named "Liberty2-0.exe." Now, it asks is there a...
-

 157Cyber Crime
157Cyber CrimeTour de France leader Chris Froome has had his data hacked, claims Team Sky
Yellow Jersey wearer targeted by critics who claim he has been using performance-enhancing drugs.
-

 226Hacked
226HackedMozilla Firefox Kills All Versions of Flash Player by Default
Just yesterday, the chief security officer at Facebook, Alex Stamos asked for the end for Adobe’s fragile and vulnerable software Flash Player...
-

 330Opinion
330OpinionSpoofed URLs: Homograph Attacks Revisited
How homograph attacks can present a spoofed, malicious link, and a case where a secure connection doesn't guarantee a safe site.
-

 241Cyber Crime
241Cyber CrimeScammers Targeting Facebook Users with Airline Scams
Scammers have become amusingly very popular in this day and age — They are the reason why holiday makers won’t keep their...
-
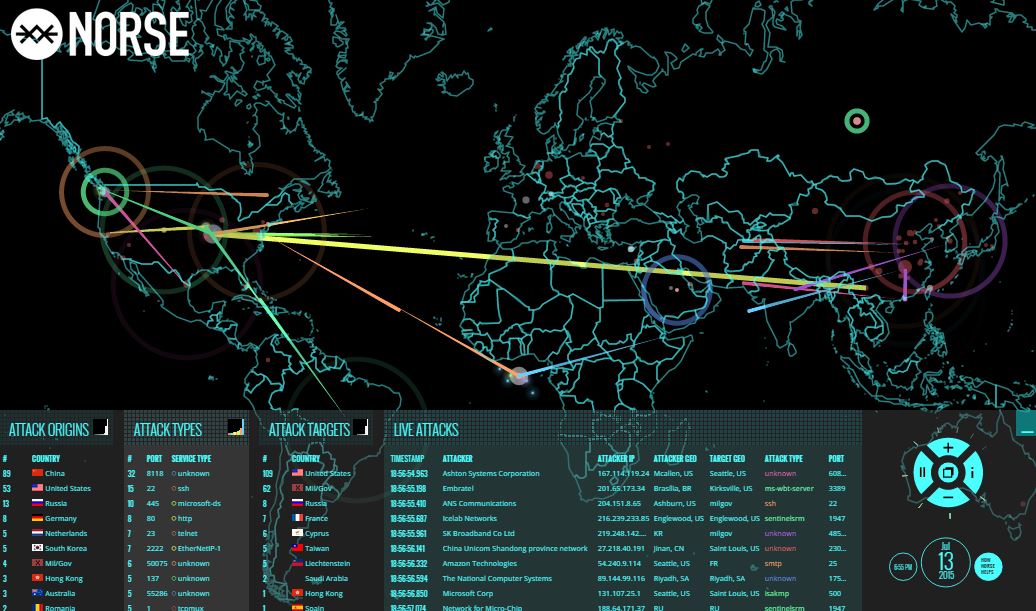
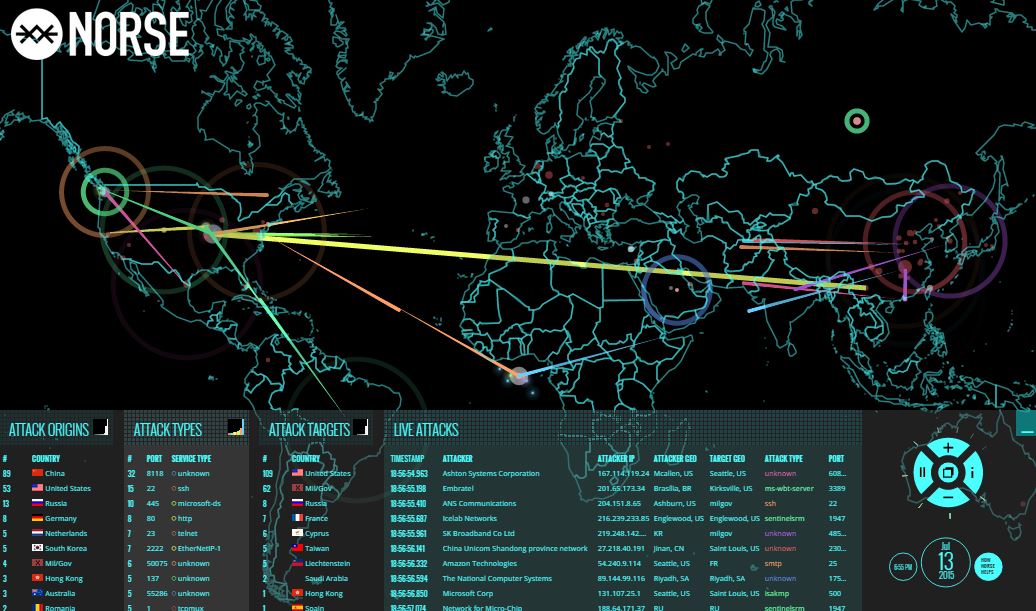 555Hacked
555HackedThis Real-Time Cyber-Attack Map Shows the Truth of Global Cyber War
This real-time global cyber attack map is trending in the social media since couple of days. Colorful lasers depict the attacks that...
-

 262Data Security
262Data SecurityResearchers Found Critical Vulnerability in LG’s Update Center Application
The LG Update Center Application faces yet another threat of cyber attack as was discovered by SEARCH-LAB Ltd in November 2014. A...
-

 255News
255NewsMalaysian Police Facebook, Twitter Accounts Hacked by Pro-ISIS Hackers
The Malaysian Police Facebook and Twitter added to the list of targeted government social media accounts — Monday afternoon saw the pages...
-
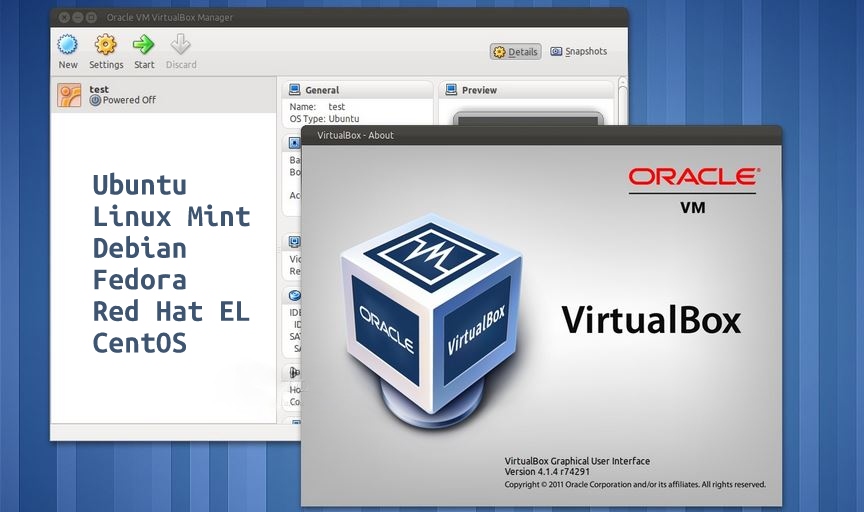
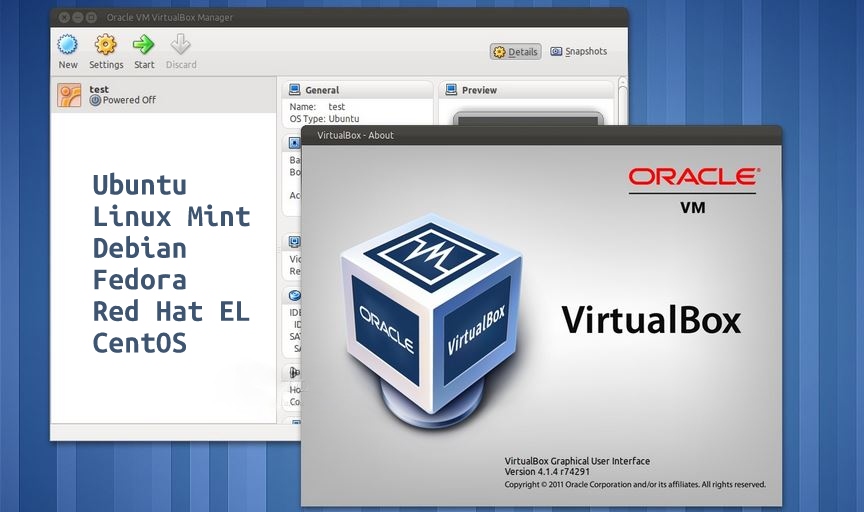 293Geek
293GeekHow to Install VirtualBox 5.0 In Ubuntu, Debian, Linux Mint, RHEL, CentOS and Fedora
Virtual Machines are software that are used to run other operating systems within a pre-installed operating system. This self-contained OS runs as...
-

 921Cyber Crime
921Cyber CrimeBarclays compensates customers after personal data trove uncovered
Barclays bank is to pay out around £500,000 in compensation to 2,000 customers whose personal data was found on a USB stick...
-

 205Geek
205GeekAmazon Launches AWS Device Farm, Now Test Your Apps on Real Devices
To benefit the hard-working app developers and programmers, Amazon is starting a cloud-based service named AWS Device Farm. AWS Device Farm will...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




