Featured News
-
 180News
180NewsAdult dating site hack reveals sexual secrets of millions, including feds and cops
An Adult Dating website AdultFriendFinder is the newest victim of a huge hack that exposed the personal information, with sexual orientation details,...
-

 308Geek
308GeekInjured Turtle Gets 1st 3D Printed Titanium Jaw Implant
A big day in the history of animal prostheses has arrived, Turkey’s medical 3D printing company provided an injured turtle with a...
-
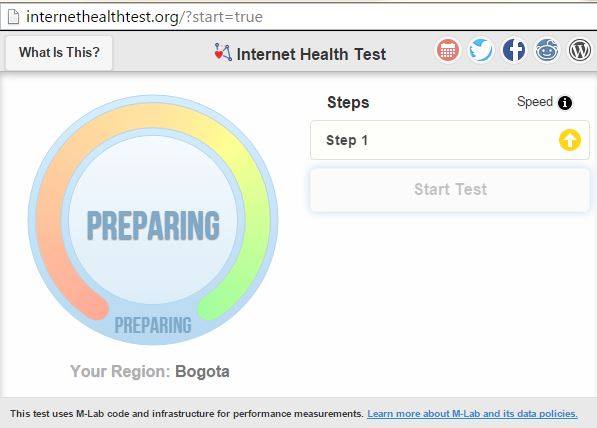
 207How To
207How ToHow to Check if Your ISP is Violating Net Neutrality and Slowing You Down
The net neutrality debate continues to evolve and now the common people have a better understanding of the topic. Here at fossBytes,...
-
 331Cyber Events
331Cyber EventsHackers leak Confidential data from Saudi Ministry of Foreign Affairs! It’s Crazy
Yemen Cyber Army claims it breached into the Saudi Ministry of Foreign Affairs server and leaked plain-text login credentials of Saudi officials...
-

 91Cyber Crime
91Cyber CrimeThe wider world of security research output: webinars
Security research is published in many forms. For example, there are live and recorded webinars that cover a range of cybersecurity topics.
-

 140Password
140PasswordGoogle reveals failure of ‘secret question’ password recall
A research paper from Google has looked into the difficulties of standard 'forgotten password' personal information verification.
-

 460Geek
460GeekMom Shames 13-year-old Daughter for acting slutty on Facebook
Denver mom Val Starks becomes enraged and publicly humiliates daughter on Facebook for posing as 19 and posting indecent pictures — Video has...
-

 98Privacy
98PrivacyAdult dating site hacked, leaking private information
Casual dating website 'Adult FriendFinder' has been hacked, leaking data from as many as 3.9 million accounts, according to an investigation by...
-

 94Password
94PasswordApple bolsters app store security with 2FA and Touch ID
A new update to the Apple Store app for iPhone and iPad has bolstered its security features, adding two-factor authentication (2FA) and...
-

 300How To
300How To5 security questions to ask before clicking on a link
Should you trust that link? We Live Security runs down five quick security questions to ask before you click on a URL.
-

 83Malware
83MalwareScareware: Fake Minecraft apps Scare Hundreds of Thousands on Google Play
ESET has discovered over 30 scareware apps available for download from the Google Play store. The apps have been installed by more...
-

 299Cyber Events
299Cyber EventsMassive US Healthcare Company Hacked, 1.1 million customers affected
Massive Healthcare Company is another victim of malicious Hacking — Currently the third Blue Cross and Blue Shield insurer targeted. Hackers have targeted...
-

 145Surveillance
145SurveillanceNSA Planned To Hack Google App Store And Install Malware On All Android Apps
As per the latest documents provided by Edward Snowden, the NSA developed a program called IRRITANT HORN for delivering malware via Samsung...
-

 71Cyber Crime
71Cyber CrimeCareFirst data breach leaves 1.1m health insurance customers vulnerable
More than 1.1 million health insurance customers have been left vulnerable by a vast data breach, after criminals gained access to a...
-

 187Tricks & How To's
187Tricks & How To'sInstall Windows in 15 minutes
We do have to spend so much time when formatting PC. We are obliged because of windows installation speed. But using simple...
-

 252Privacy
252PrivacyWhat app permissions should I be wary of?
Mobile applications increasingly want access to various functions on your smartphones and tablets, such as your location and contacts book. But some...
-

 205Cyber Events
205Cyber EventsFBI chief fears ISIS gearing up for cyberattacks on US, claims “it’s coming”
The FBI chief James Comey is worried about possible cyber attacks by the ISIS group on critical infrastructure in the United States — Comey believes...
-
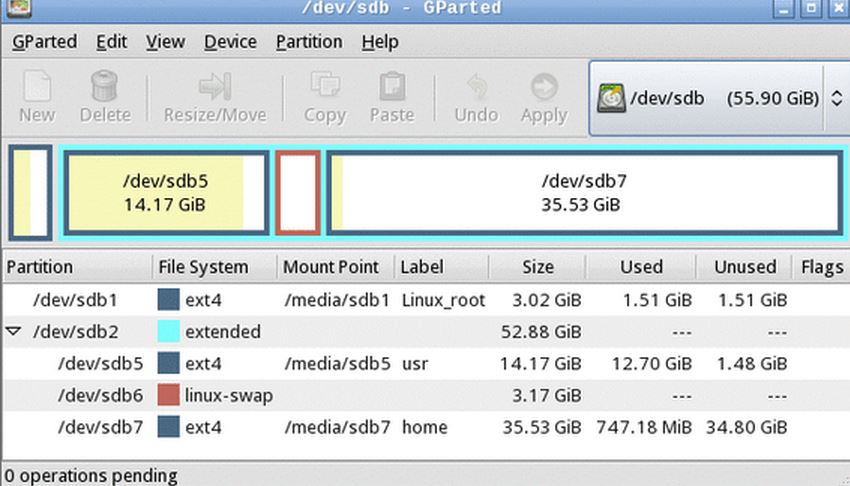
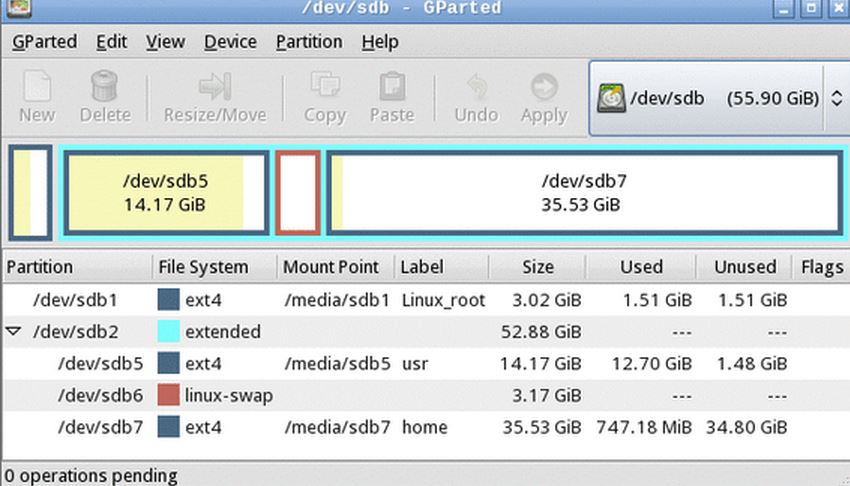 280Geek
280GeekHow to Auto Mount Partitions On Boot in Linux Easily
Unlike Windows, Linux does not mounts file systems automatically on computer startup. You have to mount each partition manually after boot. This...
-

 192Cyber Crime
192Cyber CrimePayPal Users hit with ‘Payment Made without Permission’ Phishing Scam Email
Another day — Another PayPal Phishing scam! There’s an email claiming that PayPal is considering a payment reversal. Allegedly, a payment was made...
-

 274Cyber Events
274Cyber EventsAnonymous Steals 1 Terabyte Passwords From Expo 2015 in Italy
Anonymous Italian attackers continue to haunt the Expo 2015 Universal Exposition being hosted in Milan as it faces an array of attacks...
The Latest
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Malware
MalwareChina-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devices
-
 Malware
MalwareNew ‘Cuckoo’ Persistent macOS Spyware Targeting Intel and Arm Macs
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Malware
MalwareHackers Increasingly Abusing Microsoft Graph API for Stealthy Malware Communications
-
 Malware
MalwareNSA, FBI Alert on N. Korean Hackers Spoofing Emails from Trusted Sources
-
 Vulnerabilities
VulnerabilitiesFour Critical Vulnerabilities Expose HPE Aruba Devices to RCE Attacks
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Vulnerabilities
VulnerabilitiesWhen is One Vulnerability Scanner Not Enough?
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Vulnerabilities
VulnerabilitiesNew “Goldoon” Botnet Targets D-Link Routers With Decade-Old Flaw
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareZLoader Malware Evolves with Anti-Analysis Trick from Zeus Banking Trojan
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024




