Featured News
-
Password
Much Ado About Facebook
The Reuters news agency reported earlier today a sudden increase in violent and pornographic images and videos on Facebook. A quick review...
-
Cyber Crime
AVAR Hong Kong security conference 2011 – in 30 seconds
Well, okay, if you happen to be an extremely fast reader. The Association of Anti Virus Asia Researcher’s (AVAR) 14th AVAR Conference...
-
Cyber Crime
Anonymous – is hacktivism here to stay?
Months back a rather vocal series of micro-hacktivist groups formed a somewhat larger, more vocal pseudo-organized non-organization ruled essentially democratically via IRC...
-

 200Cyber Events
200Cyber EventsChina’s Huawei to Invest in Iran
When Western companies were asked to quit their operation from Iran, Huawei, Chinese telecommunication giant decided to help Iran in installing surveillance...
-
Social Engineering
Facebook video scam: 15 seconds? Don’t watch it at all
[Update: For more articles about Facebook security click here. To help you protect yourself on Facebook and Twitter, ESET provides a free...
-
Password
Stolen password checking: a question of trust
How do you know a service is legitimate and safe? We all have to trust by proxy sometimes, but it just doesn't...
-
 178Malware
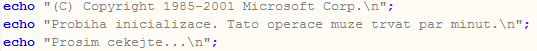
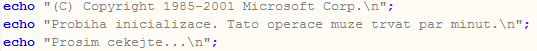
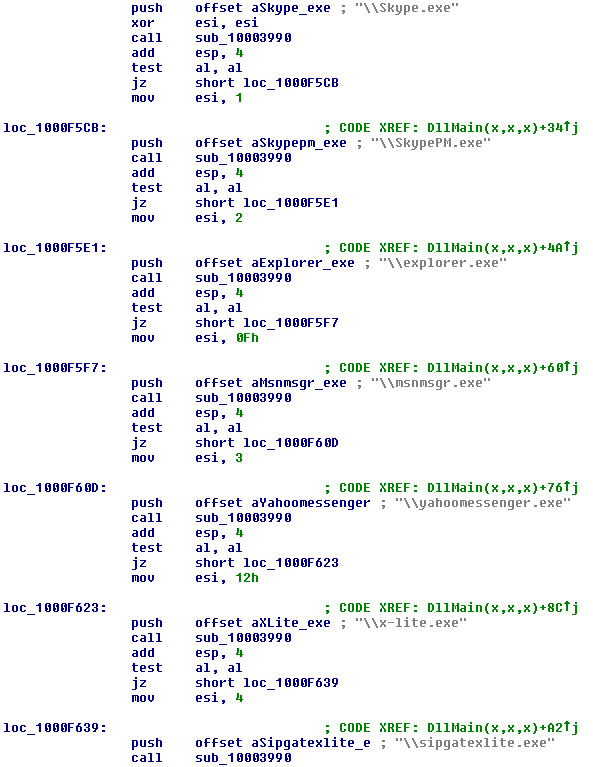
178MalwareMade in the Czech Republic: a PHP Autorun worm
Recently, a new data-stealing worm caught our attention. The reason why it stands out from many similar amateur creations is that its...
-
 186Malware
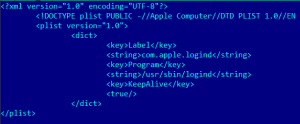
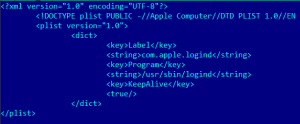
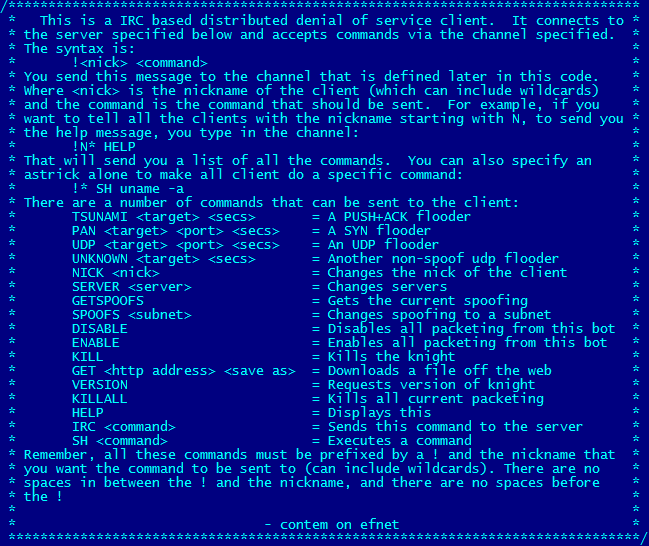
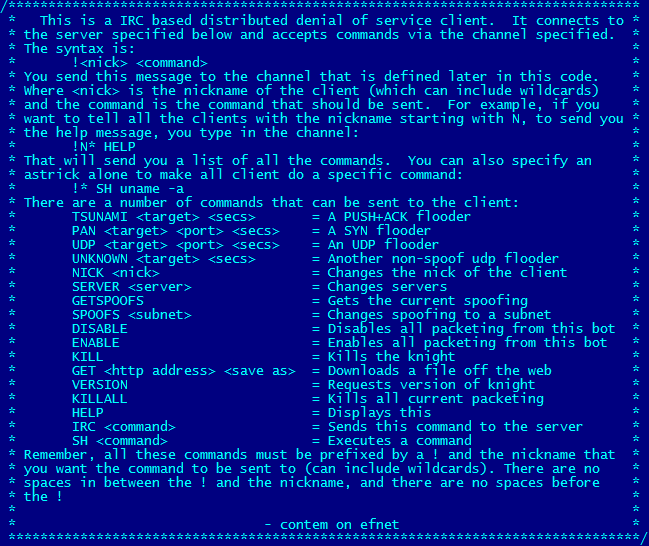
186MalwareUpdates on OSX/Tsunami.A, a Mac OS X Trojan
Yesterday, ESET announced the discovery of a new threat against the Apple Mac OS X platform. Today, we have found a new...
-
 129Malware
129MalwareLinux Tsunami hits OS X
We’ve just come across an IRC controlled backdoor that enables the infected machine to become a bot for Distributed Denial of Service...
-
 198Cyber Crime
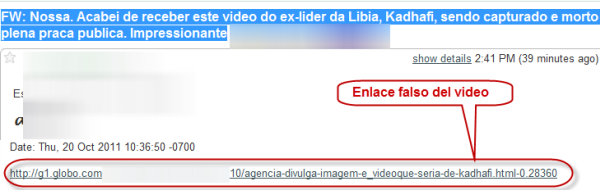
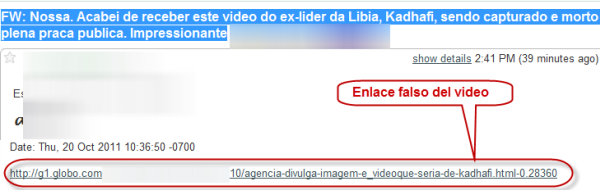
198Cyber CrimeGaddafi search poisoning
Here's an example of search poisoning somewhat similar to that predicted by Stephen Cobb. It uses the death of Gaddafi as a...
-
Social Engineering
Facebook, Privacy, and Defence in Depth
Symantec's transient false positive detection of Facebook as a malicious site leads to serious thoughts about Facebook and privacy...
-
 125Scams
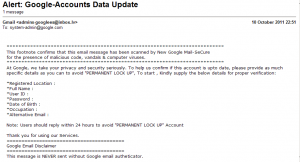
125ScamsGoogle Eye Phish: Bait Me A Hook In The Morning
...I've been seeing quite a few scrawny, toothless piranha mailed from email addresses that are often spoofed but invariably dubious like google.phishing.team@a_latvian_mail_provider.com...
-
Malware
Virus Bulletin 2011: Fake but free…
ESET had quite a strong representation at Virus Bulletin this year in Barcelona, as David Harley mentioned in his post prior to...
-
 164Malware
164MalwareGerman Policeware: Use the Farce…er, Force…Luke
On Saturday, another controversial report of a “government trojan” appeared. This time it is the German government that has been accused by...
-
Malware
Android vulnerability patch time lag causes malware opportunity
One of the blessings of Open Source initiatives is the rapidity with which coders can release quality collaborative code. This is one...
-
Malware
Kids’ computer game malware – Scammers stoop to new lows
There’s a new batch of malware making the rounds, this time directed at spreading banking malware through childrens’ games. Though it’s hard...
-
Cyber Crime
U.S. Government – Security incidents up 650% over 5 years
Citing weaknesses in security controls at 24 major agencies, a new report by the U.S. Government Accountability Office (GAO) charts the stellar...
-
Cyber Crime
Which anonymizing VPN is really anonymous?
On the heels of the arrest of Cory Kretsinger, aka “Recursion”, for one of the Sony data breaches, following an FBI request...
-
Mac
New Apple OS X Malware: Fake Adobe Flash Installer
A new attack against Apple Mac OS X Lion (10.7) has been detected by Intego. The threat is a Trojan, dubbed Flashback,...
-
 186Malware
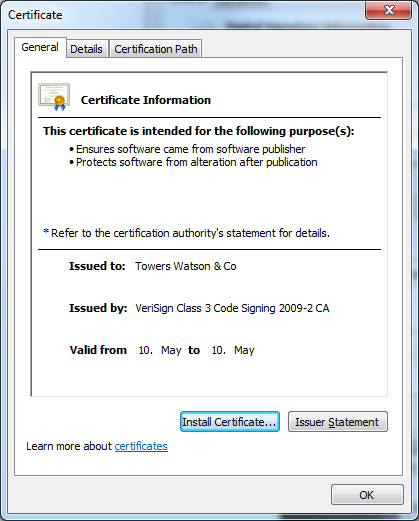
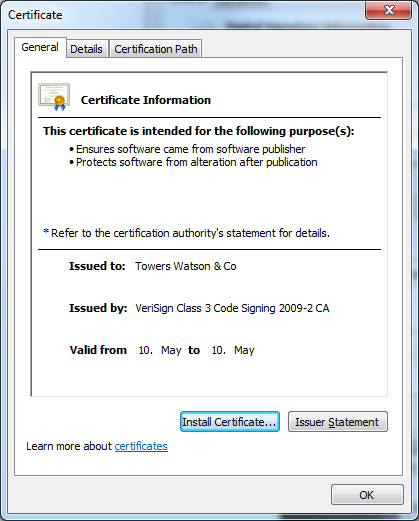
186MalwareTowering Qbot Certificates
New stolen digital certificates are used by the multi-purpose backdoor Qbot. The criminals behind the Qbot trojan are certainly not inactive. As...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




