Featured News
-
Scams
Coreflood Reduced to a Backwater
Here’s a little information from ESET’s point of view about the Coreflood botnet, whose C&C (Command and Control) servers were taken down...
-
Privacy
Facebook Ads: the Likes of You
Many Facebook users are annoyed to discover that their names and faces can be used in sponsored FB ads. Indeed, according to...
-
Cyber Crime
Another VB Cybercrime Seminar
One that will be of most interest to our readers in the UK, I guess. Our friends at Virus Bulletin are holding another...
-
Scams
Disaster Scams and Resources
I've added some commentary and resources on the Japan earthquake/tsunami disasters to an independent blog I maintain that specializes in hoaxes, scams and...
-
Social Engineering
Email malware: blast from the past
...today I'm waxing nostalgic about a piece of malware. Not one of those anniversaries that have filled so many blogs, articles and...
-
Cyber Crime
Stuxnet analyses: more jaw‑jaw*, more cyberwar, less precision
Added 5th March 2011 to the Stuxnet resources page at http://blog.eset.com/?p=5945...
-
Android
Androids and Gingerbread Men
...all the relevant malware they've seen uses exploits that are restricted to Android OS 2.2 and below...
-
Password
Social Security Numbers: deja vu all over again
Social Security Numbers: Identification is STILL not Authentication...
-
Android
The Terrifying Android
At a time when Gartner estimates that we'll have downloaded 17.7 billion + mobile apps worldwide by the end of this year,...
-
Malware
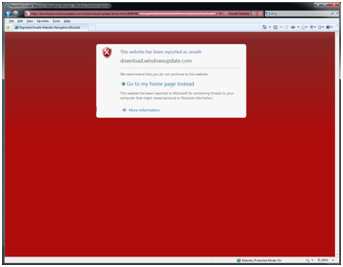
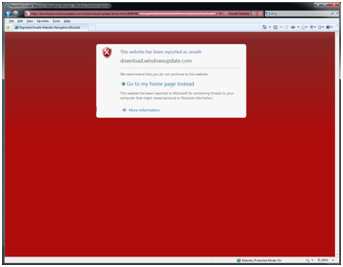
Anatomy of a Biting Bunny – The Infected Microsoft Catalog Update
Aryeh Goretsky posted a blog about a trojan program in a Microsoft catalog update. I thought it might be a little interesting...
-
 130Malware
130MalwareTrojan in Microsoft Update Catalog – A Bunny Bites Back
UPDATE #1 Randy Abrams has posted a follow-up article, Anatomy of a Biting Bunny – The Infected Microsoft Catalog Update with additional information...
-
Windows
Microsoft’s recent MHTML Vulnerability – Follow up
Just a quick follow up on the Microsoft Security Advisory (2501696) post that my colleague Randy Abrams wrote about on January...
-
Android
The Sound of a Credit Card
A recent article at http://www.thinq.co.uk/2011/1/20/android-trojan-captures-credit-card-details/#ixzz1Bb8RGsWS describes how an attack against Android based phones might be able to capture your credit card information...
-
Social Engineering
Phone Scams and Panic Attacks
...many scams work by panicking victims into taking some unwise action, whether it's parting with their credit card details or opening a...
-
Privacy
Facebook Security Lockdown Guide
..."It" is a ZDNet article - well, more like a slide show - by Zack Whittaker, called January 2011: The Definitive Facebook...
-
Android
The Droid Army
The Lookout Mobile Security company is reporting a new trojan horse program that runs on Android based phones. The novel thing about...
-
Malware
What are Heuristics?
It is generally well-understood that antimalware programs—the software which detects computer viruses, worms, trojan horses and other threats to your system—work by...
-
Social Engineering
How to Fool a Security Researcher
...Andrew Lee conducted a fun but disquieting thought experiment in the course of an amusing and informative presentation on user education at...
-
Scams
Stealing from Santa (Scammers’ Holiday Season)
My colleague Urban Schrott, from ESET Ireland, wrote a nice feature article for our monthly ThreatSense report (which should be available shortly...
-
Social Engineering
Boonana Threat Analysis
Our interim analysis of a version of the malware we detect as Java/Boonana.A or Win32/Boonana.A (depending on the particular component of this...
The Latest
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Malware
MalwareChina-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devices
-
 Malware
MalwareNew ‘Cuckoo’ Persistent macOS Spyware Targeting Intel and Arm Macs
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Malware
MalwareHackers Increasingly Abusing Microsoft Graph API for Stealthy Malware Communications
-
 Malware
MalwareNSA, FBI Alert on N. Korean Hackers Spoofing Emails from Trusted Sources
-
 Vulnerabilities
VulnerabilitiesFour Critical Vulnerabilities Expose HPE Aruba Devices to RCE Attacks
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Vulnerabilities
VulnerabilitiesWhen is One Vulnerability Scanner Not Enough?
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Vulnerabilities
VulnerabilitiesNew “Goldoon” Botnet Targets D-Link Routers With Decade-Old Flaw
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareZLoader Malware Evolves with Anti-Analysis Trick from Zeus Banking Trojan
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024




