Featured News
-
Cyber Crime
Hacktivism: not a get‑out‑of‑jail card?
What we're lacking here is a clear differentiation between types of "hacktivist" or, indeed, "activist": much of the commentary that's around at...
-
Password
Where there’s smoke, there’s FireWire
Forensic software developer PassWare announced a new version of its eponymous software forensics kit on Tuesday. Already several news sources are writing...
-
Hacking
50 ways to hack a website
Well, really there are far more, but the latest study from Imperva of 10 million attacks against 30 large organizations from January...
-
 135Malware
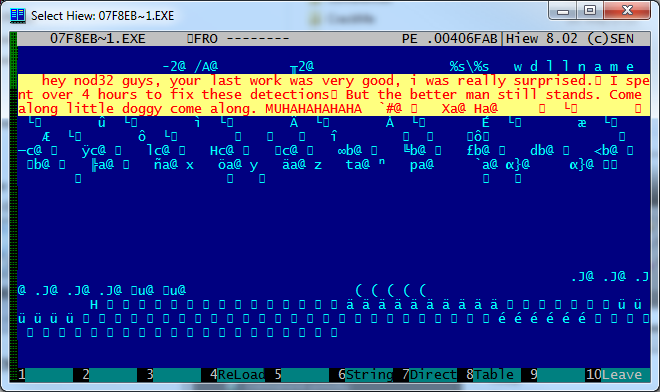
135MalwareCome along, little doggy, come along
The most common malware technique for avoiding detection is to create loads of “fresh” variants. Actually, the component that changes so frequently...
-
Hacking
Stuxnet: Broke Iranian nuclear centrifuges?
Or so the latest report from DEBKAfile states, claiming the Stuxnet worm broke numerous Iranian centrifuges by forcing them to overspeed, causing...
-
Android
Android apps: slow data leak?
With the proliferation of the data we hold on our mobile devices, it’s no wonder Neil Daswani, CTO of Dasient, says around...
-
Malware
Manga Management and Malware
...one Yasuhiro Kawaguchi was arrested yesterday on suspicion of "saving a virus on his computer," though the story suggests distribution of malware...
-
Hacking
‘Anonymous’ NATO data breach?
2 days ago, the FBI announced a series of raids resulting in arrests of alleged members of the hacking group ‘Anonymous’. Hoping...
-
 184Cyber Crime
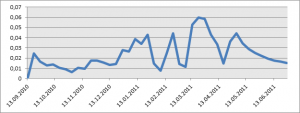
184Cyber CrimeHodprot is a Hotshot
In their presentation “Cybercrime in Russia: Trends and issues” at CARO2011 -- one of the best presentations of the workshop, in my...
-
Scams
Free WiFi: Price? All your personal information
Sitting in an airport you rarely frequent, you grab your laptop and snap out a couple e-mails to send, and look, there’s...
-
Android
1 in 20 mobile devices infected next year?
The mobile devices of late have more compute power than the full desktop PC of yesteryear, and they fit it your pocket,...
-

 174Privacy
174PrivacyFacebook Video Calls powered by Skype
With Facebook's launch of video chat powered by Skype underway and enabling a new level of communication on its platform, we take...
-
Privacy
Google: your private profile – now public
Google, in an effort to get more squarely into the center of the social networking scene, is implementing a system where private...
-
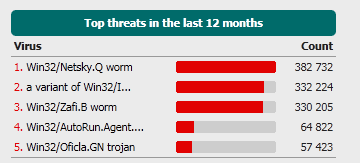
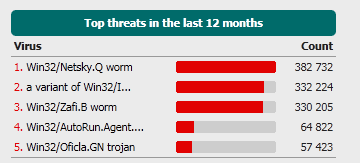 146Malware
146MalwareThe more things change, the more they stay the same
It's something of a truism, that 'old viruses never die', and that certainly seems to be the case for some of the...
-
Hacking
Arizona DPS: hacked again – still – really?
On Wednesday we heard additional documents had been leaked from the Arizona Department of Public Safety (DPS). “Will this ever end?” has...
-
Cyber Crime
Facebook Facial Recognition – A picture is worth a thousand words
Facebook recently launched a facial recognition feature that allows you and others to “tag” photos with your name. As has been the...
-
Malware
Windows Rootkit Requires Reinstall?
In a ComputerWorld article Gregg Kaiser cites a Microsoft engineer as saying that the trojan that Microsoft calls “Popureb” digs so deeply...
-
Cyber Crime
SCADA still scary
"Infrastructure Attacks: The Next Generation?" now includes the speaker notes, which hopefully makes it more interesting and useful.
-
Cyber Crime
White House to double jail time for hackers?
The Obama administration seems intent on pushing for stiffer sentences for hackers caught endangering national security to 20 years prison time, doubling...
-

 422Privacy
422PrivacyLinkedIn Privacy: An Easy How‑to Guide to Protecting Yourself
Introduction LinkedIn is a social network platform whose specialty is connecting professionals together to build relationships and create business opportunity. Recently the...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




