Featured News
-
Mac
Your Computer Won’t Protect You
You may have seen some headlines today about a New Java Trojan that attacks Macs. It turns out that it also attacks...
-
Privacy
Unencrypted Wireless: In Like a Lion, Out Like a Lamb
[C. Nicholas Burnett, the manager for ESET LLC's tier three technical support, contributed the following guest blog article on the FireSheep plugin...
-
Scams
Scam of the Day AKA She Loves You Yeah, Yeah, Yeah
What a touching email. Mercy saw my profile and wants to know more about me. She even tells me “please don't forget...
-
Android
Picking Apps for Your Android
Sure, iPhones are a lot more stable than Androids, but there is one place that Android has it all over the iPhone…...
-
Android
The 1 Gigabyte Screen Capture
Back in the early 1990’s I had a 386 with 4 megabytes of RAM and a very large 80 megabyte hard drive....
-
Cyber Crime
Natl Research Council Says: Show Us The MONEY
Surprised to find annual cybercrime damage spread somewhere between 300 million and 54 BILLION? So is the Director of National Intelligence. Today...
-
Privacy
Adobe Flash, The Spy in Your Computer – Part 3
In the first two parts (Part 1, Part 2) of this series I discussed some of the privacy issues associated with Flash...
-
Malware
Stuxnet: Cyberwarfare’s Universal Adaptor?
Now that cyberwarfare is out of the bottle, will anyone agree to not use it? In the summer of 1945 in New...
-
Social Engineering
Imitation is not always the sincerest form of flattery
Since its release in 2007, ESET Smart Security has received many accolades for its antimalware, antispam and firewall functions. However, we have...
-
Privacy
Facebook Competitor Faces Criticism – Is Diaspora DOA?
Really – should any Alpha version be fed through a chipper-shredder like Diaspora has? The basics are simple: The basic premise behind...
-
Scams
Social Media: 5 Unexpected Threats
...a piece at Discovery News about 5 Unexpected Threats of Online Social Networking...
-
Social Engineering
Privacy? Who Cares?
In the security industry, we're sometimes over-ready to be over-prescriptive, seeing security and privacy concerns as paramount where others see them as...
-
Password
Strong passwords: deja vu all over again
Since never changing your password isn't generally a realistic option, and some sites actually prevent you from using good passwords and, even...
-
Android
Privacy is not in the Cards
I decided to download the card game Solitaire (by ZenTech Labs) on my Android based phone. Being a free app it is...
-
Scams
Earthquake in New Zealand likely to bring cybershocks
[UPDATE #1 at 12:15PM: Added more information about location of earthquake and prior scams. AG] We have just heard about the early September...
-
Android
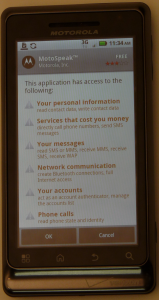
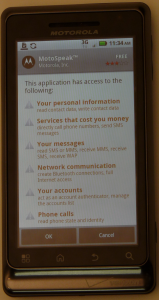
MotoSpeak and Sing and Run Random Apps?
In addition to recently getting a Droid 2, I purchased a Motorola H17txt Bluetooth headset. When used with a Blackberry or an...
-
Scams
You Have to be a Real Cool Cat!!!
You have to be a real cool cat to get into the Cambridge Who’s Who registry. A few months ago I received...
-
Malware
Open Source Malware Fingerprinting – Free Tool
In my ever-widening circle of anti-cybercrime methodology this particular approach to attribution of the criminals looting the free world makes me particularly...
-
Android
The Strange Case of the Droid 2 Password Lock
When I first got my Droid I went to set up my security. The first thing I do with a new mobile...
-
 198Android
198AndroidAndroid Application Security
Installing an application on an iPhone is a bit different than installing an application on an Android based system. With the iPhone...
The Latest
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Malware
MalwareChina-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devices
-
 Malware
MalwareNew ‘Cuckoo’ Persistent macOS Spyware Targeting Intel and Arm Macs
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Malware
MalwareHackers Increasingly Abusing Microsoft Graph API for Stealthy Malware Communications
-
 Malware
MalwareNSA, FBI Alert on N. Korean Hackers Spoofing Emails from Trusted Sources
-
 Vulnerabilities
VulnerabilitiesFour Critical Vulnerabilities Expose HPE Aruba Devices to RCE Attacks
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Vulnerabilities
VulnerabilitiesWhen is One Vulnerability Scanner Not Enough?
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Vulnerabilities
VulnerabilitiesNew “Goldoon” Botnet Targets D-Link Routers With Decade-Old Flaw
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareZLoader Malware Evolves with Anti-Analysis Trick from Zeus Banking Trojan
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024




