Featured News
-
Scams
419: UK lets the Good Times Roll
...It's a 419 (Advance Fee Fraud) message, of course. Stripped of the pseudo-governmental flim-flam, the core of the message is that they...
-
Cyber Crime
#1 Bitcoin Exchange Data Breached
Mt. Gox, the most popular Bitcoin exchange, has had a database compromised and user information stolen, sparking rapid devaluation and temporary exchange...
-
Hacking
Got Hacked? You have 48 hours to fess up
Or so the current legislation being proposed in a U.S. House of Representative subcommittee would like it. A hearing scheduled for today...
-
Hacking
I Can Neither Confirm nor Deny
As website appear to fall to hacks like the rain falls in Seattle, the question du jour doesn’t change from day to...
-
Cyber Crime
The Next Stuxnet
...the 'next Stuxnet' probably won't be any such thing, whatever we may choose to call it...
-
Cyber Crime
Why the IMF breach?
In the absence of any detailed information from the IMF itself, it's not surprising that most of the surmise around the attack...
-
 212Password
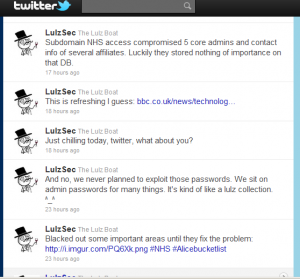
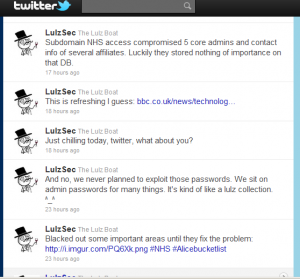
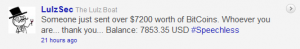
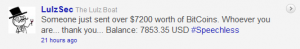
212PasswordLulzSec lulls the NHS: not such bad lads?
...on the Twitter account owned by LulzSec that they had turned their attention to the NHS. Curiously enough, they seem to have...
-
Password
A Nice Pair of Breaches
...here's a blog in stark contrast to Urban Schrott's blog about good password practice in Ireland ... Troy Hunt ran an analysis...
-
Cyber Crime
Passwords, passphrases and past caring
First: a link to another article for SC Magazine's Cybercrime Corner on password issues: Good passwords are no joke. However good your...
-
 144Cyber Crime
144Cyber CrimeBoys will be boys…
...whatever the hacker community's personal taste is in games and consoles, gamers are a tempting target...
-
 112Cyber Crime
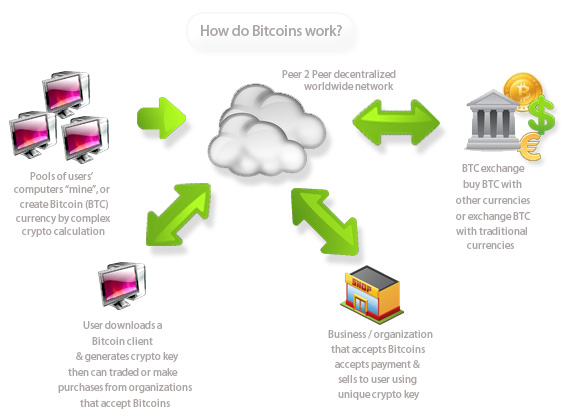
112Cyber CrimeBitcoin: P2P underground cyber currency?
Bitcoins, a self-generated hash-based peer-to-peer currency with no centralized regulating body, are on a stratospheric trajectory, will it replace traditional legal tender...
-
Cyber Crime
North Korea’s Overseas Cyber Warrior Training
It appears North Korea is expanding their cyber warrior savvy in a plan that includes sending the best and brightest of young...
-
 327Mac
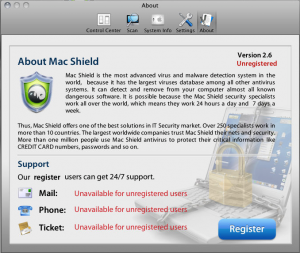
327MacMacDefender undergoes a name change, MacShield
The MacDefender malware has morphed again, now taking the guise of "MacShield." As in the case of its oldest sibling MacDefender,...
-
Cyber Crime
Real War – The Next Cyber Frontier
Cyber Security pundits have been keenly watching the development of nascent state targeted attacks such as the Stuxnet worm with interest for...
-

 142Malware
142MalwareCalling Android Smartphone Zombies
Android Smartphones are under attack again by rogue applications that once installed are reading information from the phone and sending it back...
-
Mobile Security
Mobile Devices Favor Malware and Phishing
A while back a malicious program called DroidDream was found on the Google Marketplace. The thing about DroidDream is that it exploited...
-

 116Cyber Crime
116Cyber CrimeScams and the Beautiful Game
We like to give you plenty of warning when we suspect that something unpleasant is coming down the pike, even if it’s...
-
 160Cyber Crime
160Cyber CrimeProtecting Consumers from Rogue Online Pharmacies
Over the past couple of years rogue online pharmacies have been advertising their domains on search engines and promoting themselves through search...
-

 131Cyber Crime
131Cyber CrimeLockheed Martin breached by unknown digital assailants
In an unfortunate series of events related to the RSA SecurID technology, reports are coming in that Lockheed Martin's networks have been...
-
Cyber Crime
An ethical dilemma
Update: It seems like the initial article is inaccurate and that Paul Rellis never made any such comments about a 14 year...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




