Search results for "Exploiting"
-

 764Vulnerabilities
764VulnerabilitiesFBI warns that hacking groups are actively exploiting three Fortinet vulnerabilities
The Federal Bureau of Investigation (FBI) issued a report warning that a group of hackers sponsored by national states is operating a...
-
 1.4KVulnerabilities
1.4KVulnerabilitiesMicrosoft Issues Emergency Patch as Chinese Hackers Exploiting Exchange Server Flaws
The Microsoft Security Response Center yesterday released several security updates for Microsoft Exchange Server. These updates were targeted at addressing vulnerabilities that...
-

 3.5KVulnerabilities
3.5KVulnerabilitiesStrandHogg – Hackers Aggressively Exploiting New Unpatched Android OS Vulnerability in Wide Using Malware
Newly discovered Android vulnerability dubbed “StrandHogg” being exploited in wide by unknown hackers using weaponized malware apps that posed as a legitimate...
-
 1.1KDDOS
1.1KDDOSRoboto Botnet Exploiting Linux Webmin Server RCE Vulnerability To Perform DDoS Attack
A new wave of Roboto Botnet activities being discovered that attack the Linux Webmin servers by exploiting the RCE vulnerability using vulnerability...
-

 1.0KMalware
1.0KMalwareNew Hacking Group Using Metasploit To Install Backdoor Malware On Windows By Exploiting MS Office
Researchers detect a wave of malware campaigns from a new hacking group named TA2101 that targeting various organizations in German and Italy...
-
 2.8KExploitation Tools
2.8KExploitation ToolsUAC-A-Mola – Detecting And Exploiting New and Known UAC Bypasses
UAC-A-Mola is a tool that allows security researchers to investigate new UAC bypasses, in addition to detecting and exploiting known bypasses....
-

 1.3KCyber Attack
1.3KCyber AttackFirst Cyber Attack ‘Mass Exploiting’ BlueKeep RDP Flaw Spotted in the Wild
Cybersecurity researchers have spotted a new cyberattack that is believed to be the very first but an amateur attempt to weaponize the...
-

 661Malware
661MalwareBuggy Malware Attack on WordPress Websites by Exploiting Newly Discovered Theme & Plugin Vulnerabilities
Researchers discovered an ongoing buggy malware campaign that attempts to exploit the newly discovered vulnerabilities resides in the WordPress theme and plugin....
-

 435Vulnerabilities
435VulnerabilitiesHackers are exploiting a backdoor on Fortinet SSL VPN; update now
Ethical hacking experts report that, in recent days, threat actors have been scanning the Internet looking for non updated SSL VPNs developed...
-

 183Hackers Repository
183Hackers RepositoryThefatrat a massive exploiting tool
Thefatrat a massive exploiting tool bypass most AV software An Easy tool to Generate Backdoor for bypass AV and Easy Tool...
-

 155Malware
155Malware25 Million Android Users Infected with Powerful “Agent Smith” Malware Through Exploiting Several Mobile Vulnerabilities
Researchers discovered a new Android malware called “Agent Smith” that infects nearly 25 million mobile users around the globe without letting users...
-
 392Malware
392MalwareUSCYBERCOM Warned that Hackers Exploiting Microsoft Outlook Security Vulnerability to Deliver Malware
USCYBERCOM published an alert that hackers were exploiting the CVE-2017-11774 Microsoft Outlook Security Vulnerability to deliver malware using an HTTPS domain. Microsoft...
-
 373Vulnerability Scanners
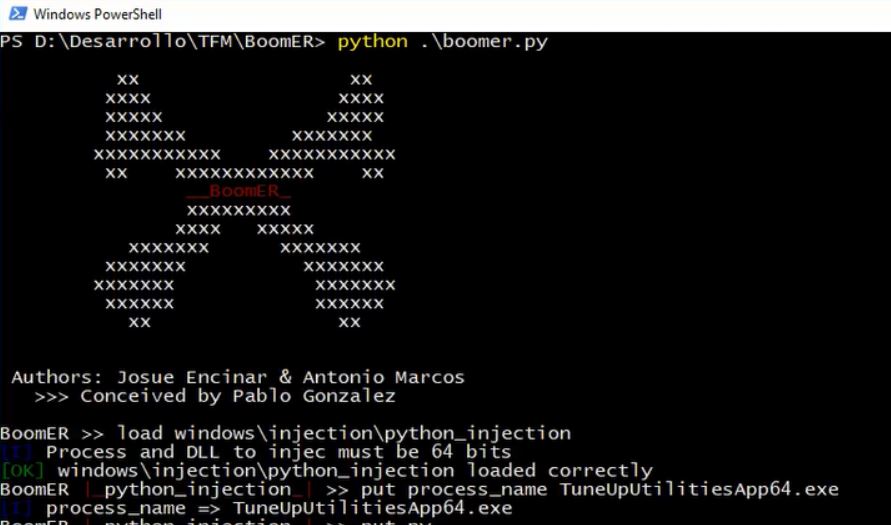
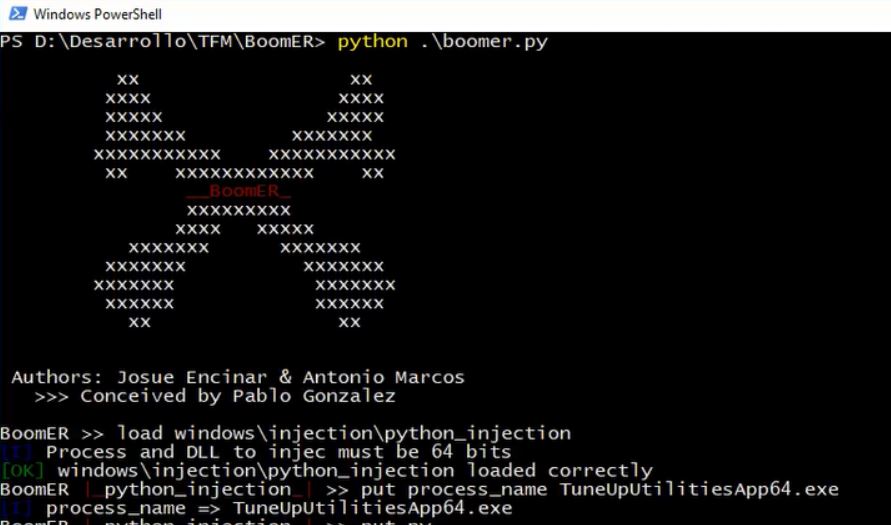
373Vulnerability ScannersBoomER – Framework for Exploiting Local Vulnerabilities
BoomER is an open source framework, developed in Python. The tool is focused on post-exploitation, with a main objective, the detection and...
-

 333Vulnerabilities
333VulnerabilitiesHackers are exploiting a Microsoft SharePoint vulnerability in the wild; update now
A web application security testing revealed that threat actors are actively exploiting a remote code execution vulnerability in some versions of SharePoint...
-

 343Cyber Attack
343Cyber AttackHackers Found Exploiting Oracle WebLogic RCE Flaw to Spread Ransomware
Taking advantage of newly disclosed and even patched vulnerabilities has become common among cybercriminals, which makes it one of the primary attack...
-
 345Malware
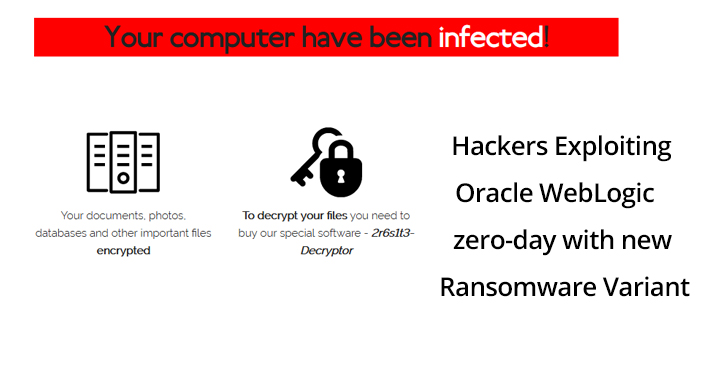
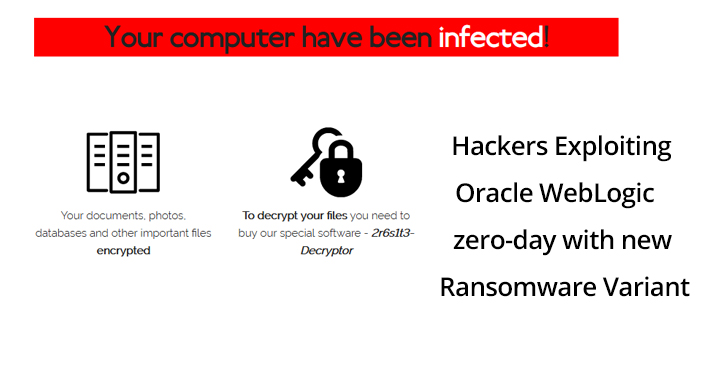
345MalwareHackers Exploiting Oracle WebLogic zero-day With New Ransomware To Encrypt User Data
Hackers exploiting the recently disclosed Oracle WebLogic Server remote code execution vulnerability to install a new variant of ransomware called “Sodinokibi.” The...
-

 256Malware
256MalwareHackers Exploiting SS7 Protocol & Inject ATM Malware to Attack Banks and Financial Sectors
The Banking and Financial sectors were hit with a constant stream of cyber attacks when compared to any of the other industries....
-

 302News
302NewsYet Another WordPress Hack Exploiting Plugin Vulnerabilities
Here comes news about another WordPress website security breach carried out by exploiting plugin vulnerabilities. Reports say that hackers have been exploiting...
-

 298Data Security
298Data SecurityHackers exploiting unpatched Chrome bug to target 500M iPhone users
In this attack, eGobbler threat group is exploiting Chrome Sandboxing bug to target iOS devices in the US and EU. Malvertising campaigns,...
-

 339Vulnerabilities
339VulnerabilitiesHackers steal users’ information by exploiting a Chrome zero-day vulnerability
These malicious files allow victims’ data collection Network security and ethical hacking specialists from the International Institute of Cyber Security report the...
-

 171Articles
171ArticlesHackers Actively Exploiting Latest Drupal RCE Flaw Published Last Week
Cybercriminals have actively started exploiting an already patched security vulnerability in the wild to install cryptocurrency miners on vulnerable Drupal websites that...






