Search results for "Exploiting"
-

 667Malware
667MalwareBeastmode DDoS Botnet Exploiting New TOTOLINK Bugs to Enslave More Routers
A variant of the Mirai botnet called Beastmode has been observed adopting newly disclosed vulnerabilities in TOTOLINK routers between February and March...
-

 4.8KVulnerabilities
4.8KVulnerabilitiesFBI Warns that Hackers Gain Network Access by Exploiting MFA and “PrintNightmare” Vulnerability
The CSA and FBI have collaboratively conducted various types of analysis over hacking activity. There have been speculations on Russian State-Sponsored threat...
-

 1.7KMalware
1.7KMalwareHackers Exploiting Infected Android Devices to Register Disposable Accounts
An analysis of SMS phone-verified account (PVA) services has led to the discovery of a rogue platform built atop a botnet involving...
-

 1.1KData Security
1.1KData SecurityHackers are exploiting Universal Plug and Play (UPnP) to turn routers into a proxy server used to carry out cyber attacks
Cybersecurity specialists from Akamai reported the detection of a malicious campaign based on the abuse of Universal Plug and Play (UPnP) protocols...
-

 2.2KVulnerabilities
2.2KVulnerabilitiesThreat actors are actively exploiting a critical vulnerability, CVE-2021-20038, in SonicWall Secure Mobile Access (SMA) gateways. Update immediately
Cybersecurity specialists report that hacking groups are actively exploiting CVE-2021-20038, a severe vulnerability in SonicWall Secure Mobile Access (SMA) gateways, fixed in...
-

 2.2KVulnerabilities
2.2KVulnerabilitiesChinese Hackers Exploiting Log4Shell Vulnerability & Attack Internet-Facing Systems
The Chinese hackers are actively exploiting the Log4Shell Vulnerability in the Log4j library and it is identified as “CVE-2021-44228.” Microsoft experts have...
-

 2.9KVulnerabilities
2.9KVulnerabilitiesChinese Hackers Exploiting Log4Shell Vulnerability & Attack Internet-Facing Systems
The Chinese hackers are actively exploiting the Log4Shell Vulnerability in the Log4j library and it is identified as “CVE-2021-44228.” Microsoft experts have...
-
 3.5KMalware
3.5KMalwareNew Zloader Banking Malware Campaign Exploiting Microsoft Signature Verification
An ongoing ZLoader malware campaign has been uncovered exploiting remote monitoring tools and a nine-year-old flaw concerning Microsoft’s digital signature verification to...
-

 4.1KCyber Attack
4.1KCyber AttackMicrosoft Warns of Continued Attacks Exploiting Apache Log4j Vulnerabilities
Microsoft is warning of continuing attempts by nation-state adversaries and commodity attackers to take advantage of security vulnerabilities uncovered in the Log4j...
-

 841Cyber Crime
841Cyber CrimeConti Ransomware Group Exploiting Log4j Vulnerability
These attacks started on December 13th in which the Conti gang focused on targeting VMWare vCenter servers vulnerable to Log4Shell attacks. Advanced...
-

 389Vulnerabilities
389VulnerabilitiesCybercriminals are exploiting Owowa IIS module to take control of exposed servers
A report by the security firm Kaspersky details the detection of a hacking group using an Internet Information Services (IIS) web server...
-

 1.7KRansomware
1.7KRansomwareHackers Exploiting Log4j2 Vulnerability in The Wild To Deploy Ransomware
An emergency security update has been released recently by the Apache Software Foundation to fix a 0-day vulnerability in the popular Log4j...
-

 5.3KData Security
5.3KData SecurityCanada shuts down 4,000 government websites fearing cyberattacks exploiting a critical vulnerability in Log4j
As a preventive measure, Quebec, Canada, decided to shut down some 4,000 government websites due to the risk of exploitation of a...
-

 4.8KData Security
4.8KData SecurityHackers actively exploiting 0-day in Ubiquitous Apache Log4j tool
Apache has released Log4j version 2.15.0 to address the critical RCE vulnerability and users are urged to apply the update immediately. The...
-
 2.7KGeek
2.7KGeekAttackers exploiting Windows Installer vulnerability despite patching
According to Cisco Talos, abusing the flaw would allow an attacker with limited access to get higher privileges and become an administrator....
-

 1.3KCyber Attack
1.3KCyber AttackU.S., U.K. and Australia Warn of Iranian Hackers Exploiting Microsoft, Fortinet Flaws
Cybersecurity agencies from Australia, the U.K., and the U.S. on Wednesday released a joint advisory warning of active exploitation of Fortinet and...
-
 1.2KData Security
1.2KData SecurityMirai botnet exploiting Azure OMIGOD vulnerabilities
The infamous Mirai botnet lets threat actors use compromised devices to carry out large-scale and crippling DDoS attacks. Critical Microsoft Azure vulnerabilities...
-

 1.9KIncidents
1.9KIncidentsHow an invisible hacker leaked IIT-JEE and NEET exams papers exploiting vulnerabilities in iON platform TCS?
A recent report claims that the iON TCS platform was compromised, resulting in the leak of multiple details about the JEE Mains...
-

 3.0KVulnerabilities
3.0KVulnerabilitiesHackers Actively Exploiting 0-Day in WordPress Plugin Installed on Over 17,000 Sites
Fancy Product Designer, a WordPress plugin installed on over 17,000 sites, has been discovered to contain a critical file upload vulnerability that’s...
-

 2.9KCyber Attack
2.9KCyber AttackTop 12 Security Flaws Russian Spy Hackers Are Exploiting in the Wild
Cyber operatives affiliated with the Russian Foreign Intelligence Service (SVR) have switched up their tactics in response to previous public disclosures of...
-
 2.2KMalware
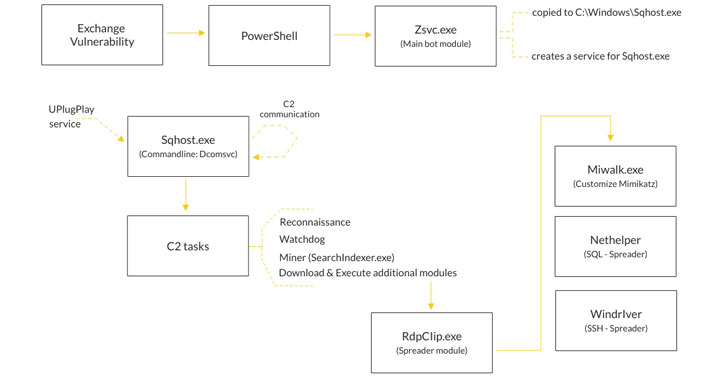
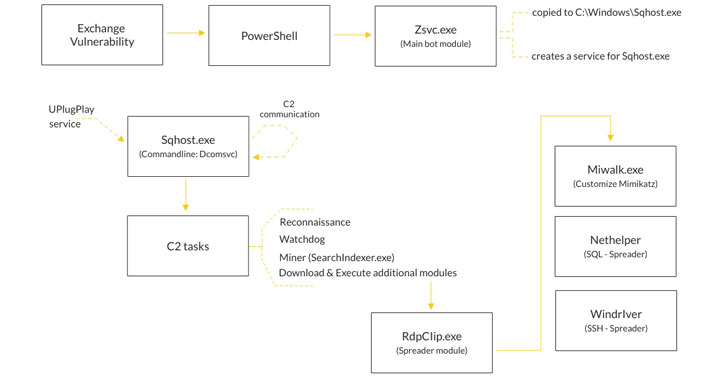
2.2KMalwarePrometei Botnet Exploiting Unpatched Microsoft Exchange Servers
Attackers are exploiting the ProxyLogon Microsoft Exchange Server flaws to co-opt vulnerable machines to a cryptocurrency botnet named Prometei, according to new...






