Search results for "Exploiting"
-

 294Geek
294GeekHackers are Exploiting New Microsoft Office Vulnerability to Drop Malware
Researchers have detected a new zero-day bug which uses a previously unknown flaw in Microsoft Word. The bug allows attackers to send malicious document...
-

 212Vulnerabilities
212VulnerabilitiesRansomware Gang Made Over $100,000 by Exploiting Apache Struts Zero-Day
For more than a month, at least ten groups of attackers have been compromising systems running applications built with Apache Struts and...
-
 264Data Security
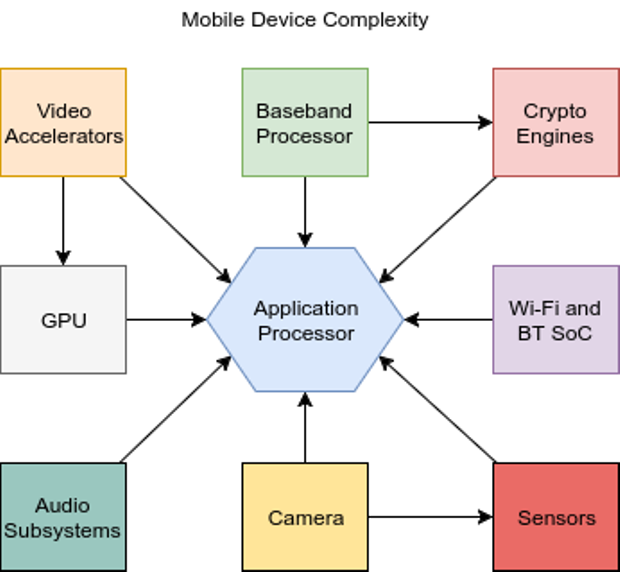
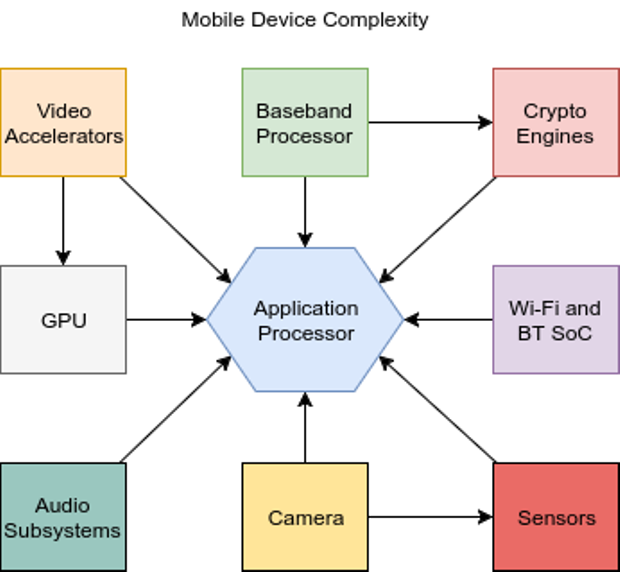
264Data SecurityOver The Air: Exploiting Broadcom’s Wi-Fi Stack (Part 1)
It’s a well understood fact that platform security is an integral part of the security of complex systems. For mobile devices, this...
-

 327Cyber Crime
327Cyber CrimeHackers can crash Google’s Nest Dropcams by exploiting Bluetooth flaws
Last year Google found some critical security flaws in Microsoft’s Edge browser and urged the company to fix these flaws within nine...
-

 97Vulnerabilities
97VulnerabilitiesExploiting Android S-Boot: Getting Arbitrary Code Exec in the Samsung Bootloader (1/2)
Samsung’s Secure Bootloader (S-Boot) for Android lies at the heart of Samsung’s chain of trust concept. An attacker who compromises S-Boot could...
-

 89News
89NewsHackers deface thousands of website by exploiting WordPress vulnerability
WordPress vulnerabilities which were discovered recently have been negatively and sometimes fatally affecting countless websites thus far. Initially, there were three flaws...
-
 100Vulnerabilities
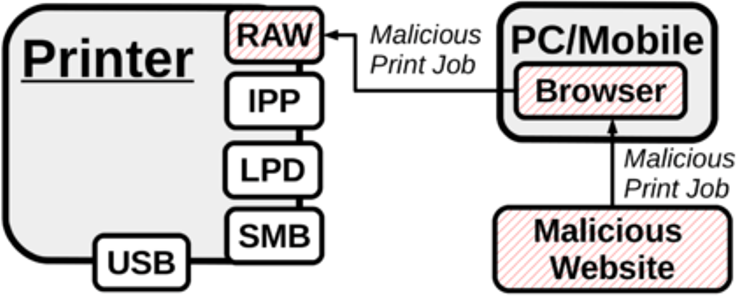
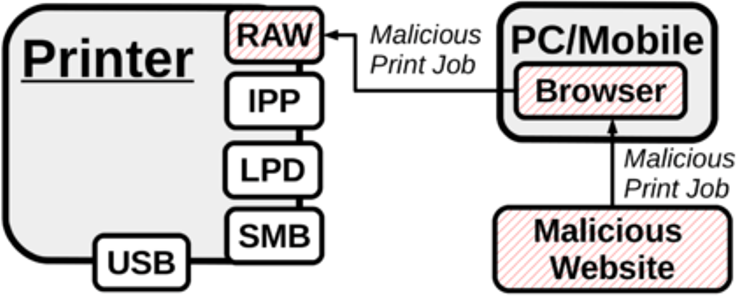
100VulnerabilitiesHacking printers exploiting Cross-site printing (XSP) attacks
A group of researchers from the University Alliance Ruhr has found a cross-site printing bug in the old PostScript language. Popular printer models...
-

 190Data Security
190Data SecurityHacker found a way to hack Facebook by exploiting the ImageMagick flaw
I want to believe that all of you know about ImageMagick and its Tragick. This issue was found in the end of...
-

 199Data Security
199Data SecurityCerber Ransomware Infecting Devices by Exploiting Flaws in Web Browsers
There is a fresh ransomware campaign circulating on the web that is spreading Cerber ransomware. This campaign is quite dangerous because it...
-
 200Data Security
200Data SecurityHacking Ubuntu Linux distro exploiting the CrashDB code injection issue
The exploitation of the CrashDB code injection issue could allow an attacker to remotely execute arbitrary code on machines running Ubuntu Linux...
-
 153Vulnerabilities
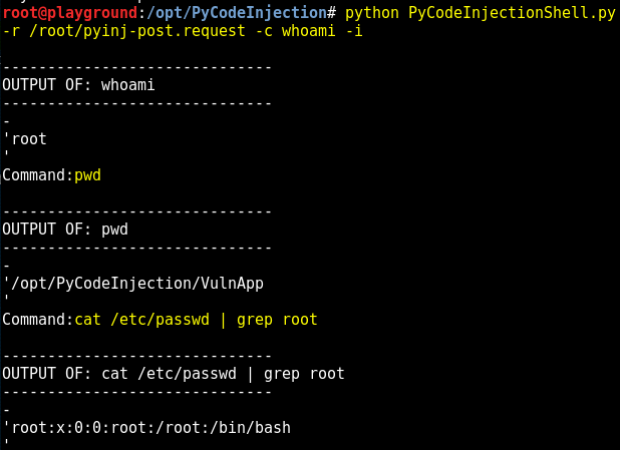
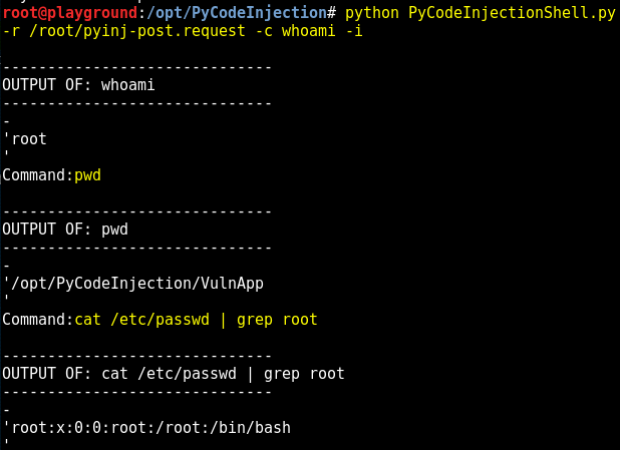
153VulnerabilitiesExploiting Python Code Injection in Web Applications
A web application vulnerable to Python code injection allows you to send Python code though the application to the Python interpreter on...
-
 211Data Security
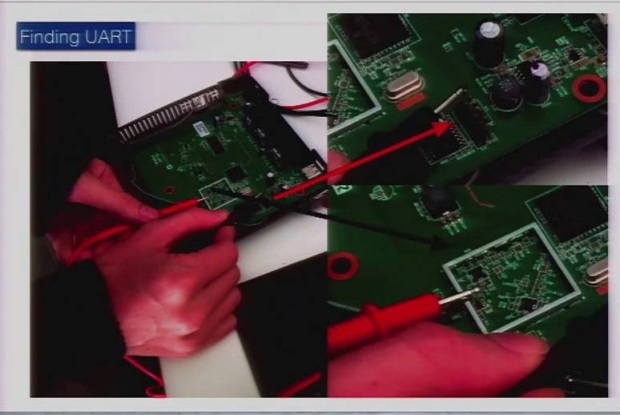
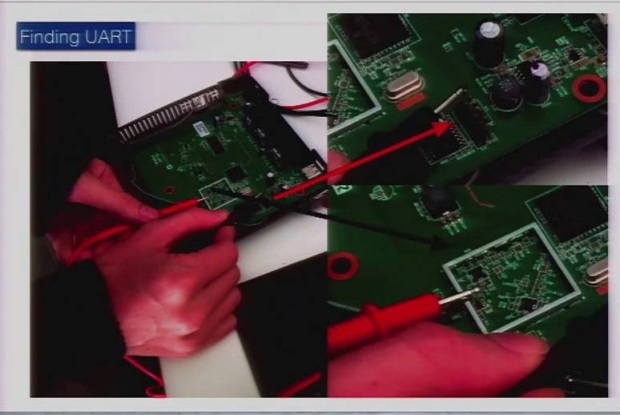
211Data SecurityReversing and Exploiting Embedded Devices (Walking the software and hardware stack)
As technology matures and microprocessors are becoming cheap we are starting to see a trend of products that are now ?smart.? The...
-
 191Incidents
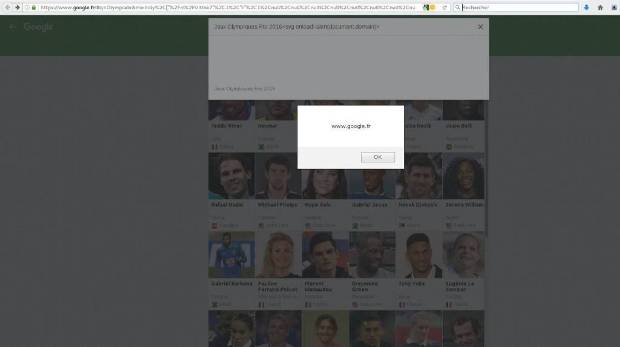
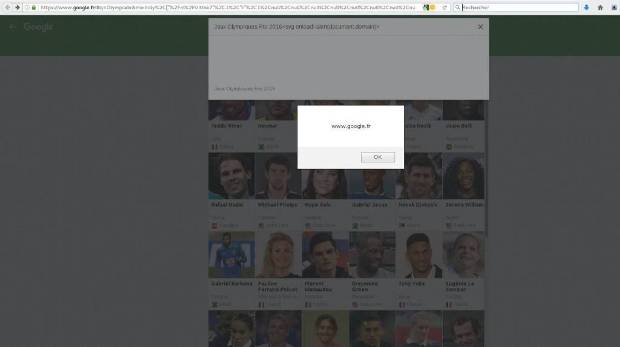
191IncidentsHow to hack Google FR by exploiting a cross-site scripting flaw
The security expert Issam Rabhi (@issam_rabhi) has discovered a cross-site scripting vulnerability in Google France. The giant already fixed it. A security...
-
 289Vulnerabilities
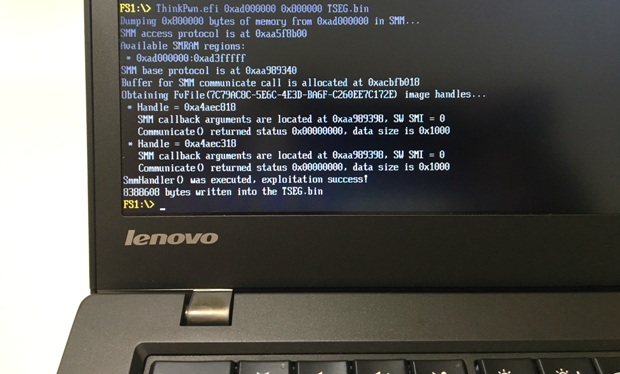
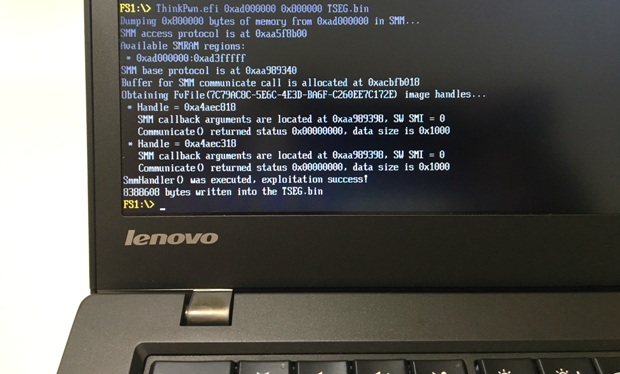
289VulnerabilitiesExploring and exploiting Lenovo firmware secrets
Hi, everyone! In this article I will continue to publish my research of Lenovo ThinkPad’s firmware. Previously I shownhow to discover and...
-
 152Data Security
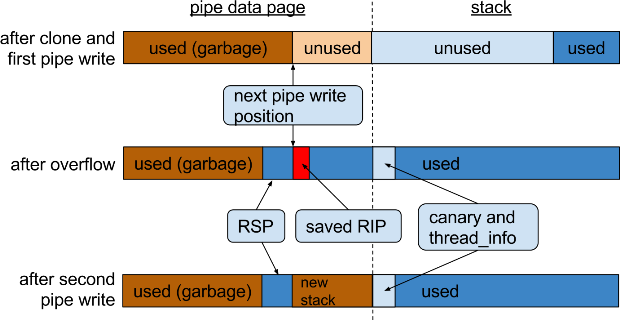
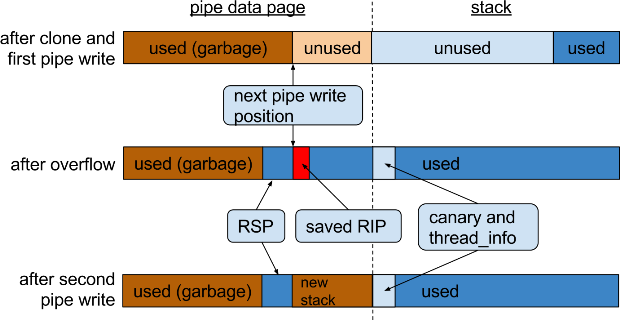
152Data SecurityExploiting Recursion in the Linux Kernel
On June 1st, I reported an arbitrary recursion bug in the Linux kernel that can be triggered by a local user on...
-

 298Data Security
298Data SecurityHackers Can Steal Mitsubishi Outlander Hybrid Car By Exploiting WiFi Access Point
Mitsubishi’s Outlander Hybrid Car’s Alarm Vulnerable to Hack due to Wi-Fi access point issue Researcher and security expert Ken Munro has revealed...
-

 443How To
443How ToExploiting 1‑byte buffer overflows
Matías Porolli shows how exploit another classic buffer overflow vulnerability, in which the ebp register is moved to execute an arbitrary code.
-
 101Data Security
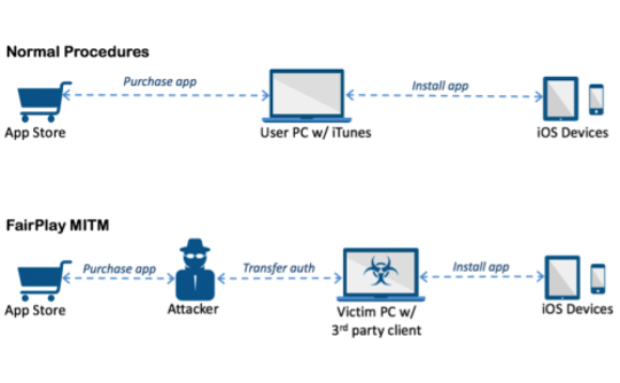
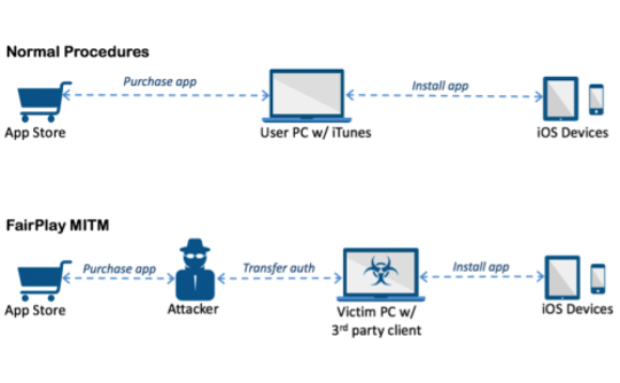
101Data SecurityAceDeceiver: First iOS Trojan Exploiting Apple DRM Design Flaws to Infect Any iOS Device
We’ve discovered a new family of iOS malware that successfully infected non-jailbroken devices we’ve named “AceDeceiver”. What makes AceDeceiver different from previous iOS...
-
 270Vulnerabilities
270VulnerabilitiesElasticZombie Botnet – Exploiting Elasticsearch Vulnerabilities
With the rise of inexpensive Virtual Servers and popular services that install insecurely by default, coupled with some juicy vulnerabilities, like CVE-2015-5377...
-
 185Data Security
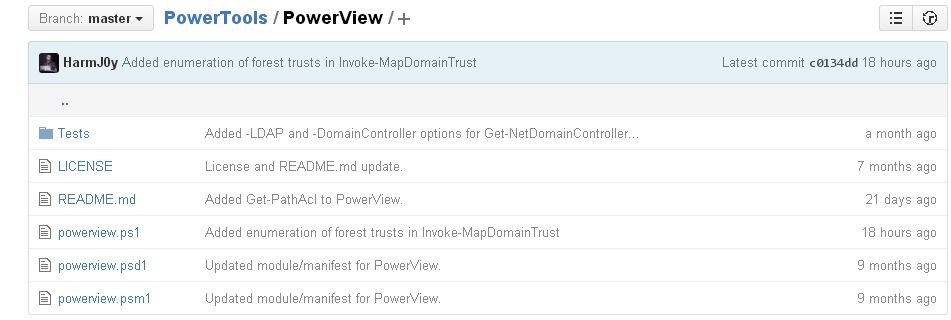
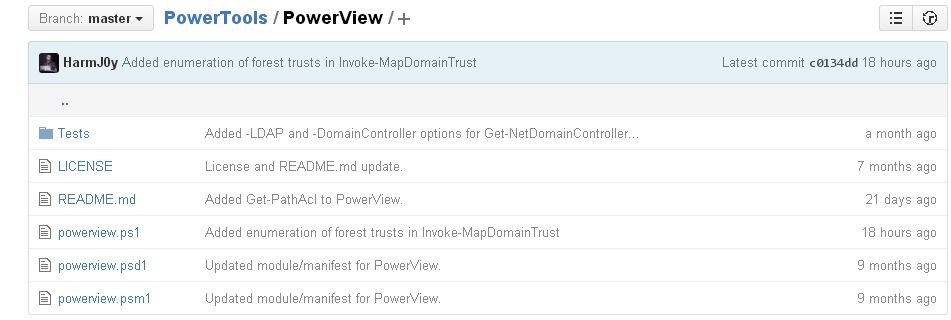
185Data SecurityHacking and exploiting Active Directory Permissions
PowerView is a PowerShell tool to achieve network information on Windows domains for cyber security services and ethical hacking training professionals. It...
-

 323Data Security
323Data SecurityHacker Steals, Drives Away Jaguar XFR Exploiting Flaw in Wireless System
A silver Jaguar XFR parked in a parking lot in Auckland, New Zealand was stolen with the help of a hacking device that sends...






