Search results for "Exploiting"
-
 255Ransomware
255RansomwareNew SamSam Ransomware Attack Around the World by Exploiting Organization Network Vulnerabilities
SamSam Ransomware newly evolved with improved sophisticated capabilities and carefully selected the specific organizations such as hospitals, schools, and government sectors those...
-

 287Hacking Tutorials
287Hacking TutorialsEmail Spoofing – Exploiting Open Relay configured Public Mailservers
Email spoofing is the way of delivering forged emails to recipients.These methods are used by criminals to launch attacks like phishing or...
-
 185Hacked
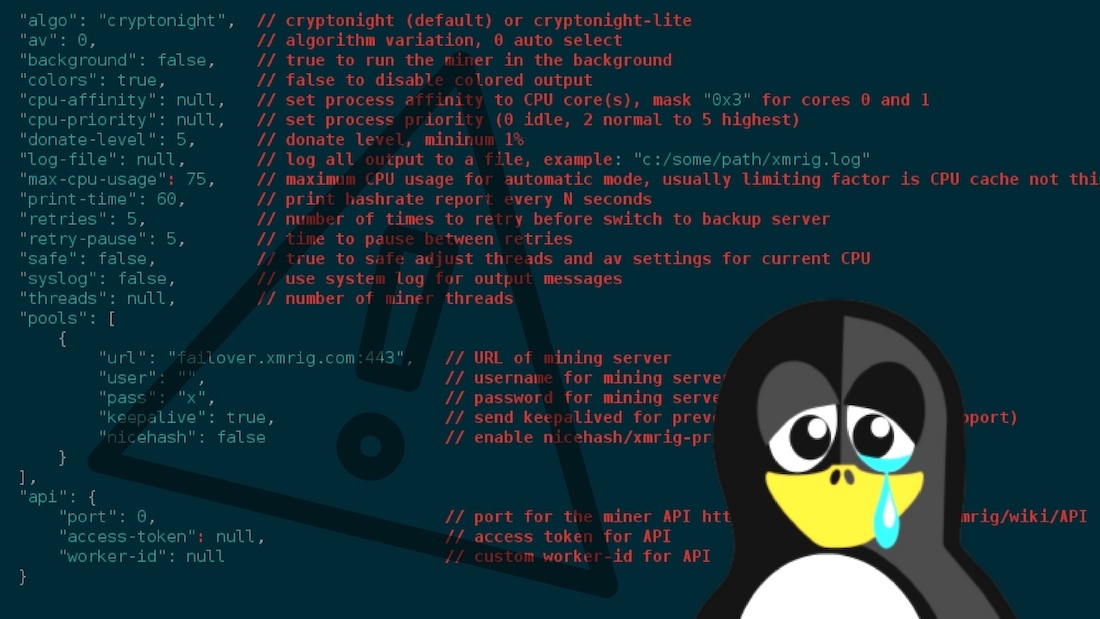
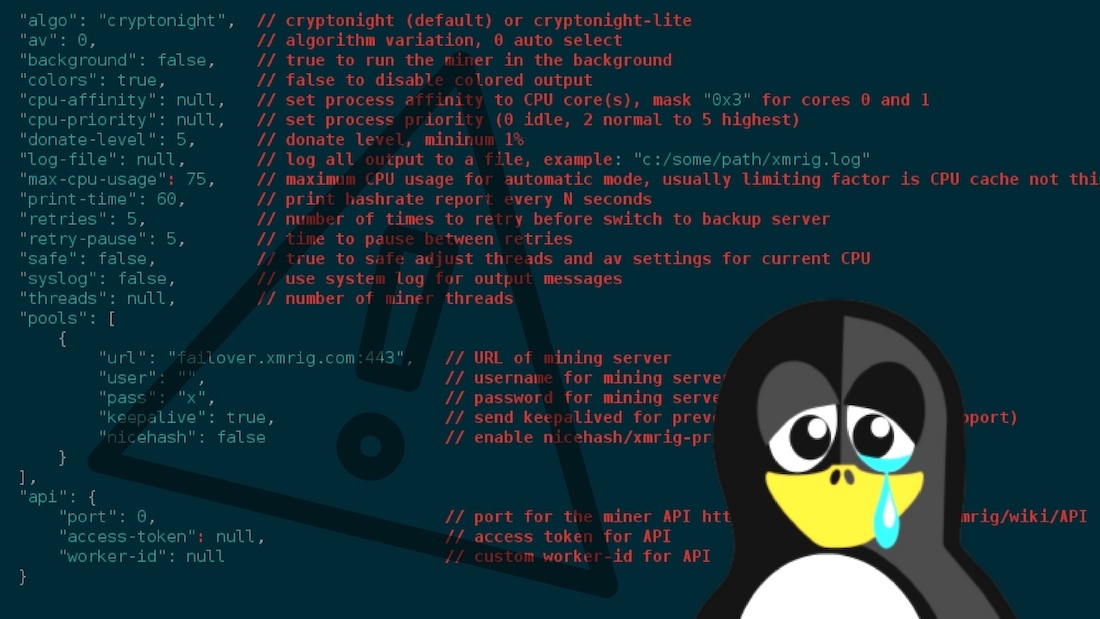
185HackedHackers Exploiting 5-year-old Flaw To Turn Linux Machines Into Cryptomining Bots
With the help of in-browser mining services like CoinHive, website owners have an easy way to hijack your CPU cycles and print...
-

 342Data Security
342Data SecurityHackers can Send Fake Emergency Alerts by Exploiting 4G LTE Protocol Flaws
Researchers at the Purdue University and the University of Iowa, USA, have managed to break the key 4G LTE protocols for generation...
-
 227Incidents
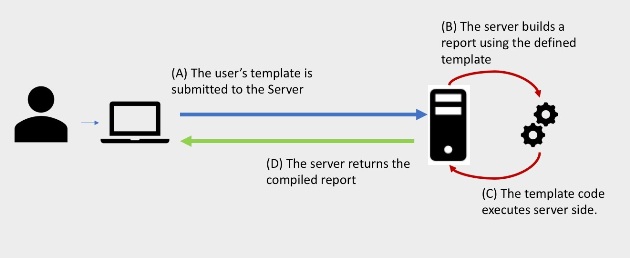
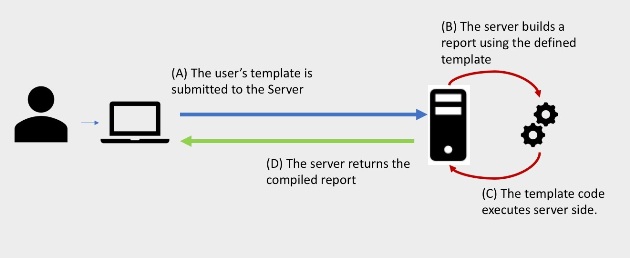
227IncidentsExploiting Custom Template Engines
Introduction When performing an application assessment one of the areas within an app I pay particular attention to is any ability to...
-

 300News
300NewsHackers Are Exploiting Telegram Messenger Zero Day Flaw To Spread Malware
Telegram Messenger zero day flaw in the version of the desktop telegram encrypted telegram end to the end application that has been...
-
 293News
293NewsHackers Are Exploiting Three Microsoft Flaws For Spreading Zyklon Malware
Security researchers have identified a new in-kind Zyklon malware campaign that spreads advanced botnet malware using at least three newly disclosed vulnerabilities...
-
 236Articles
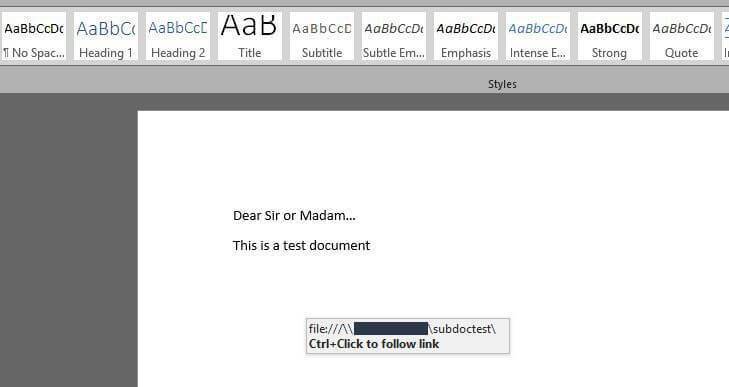
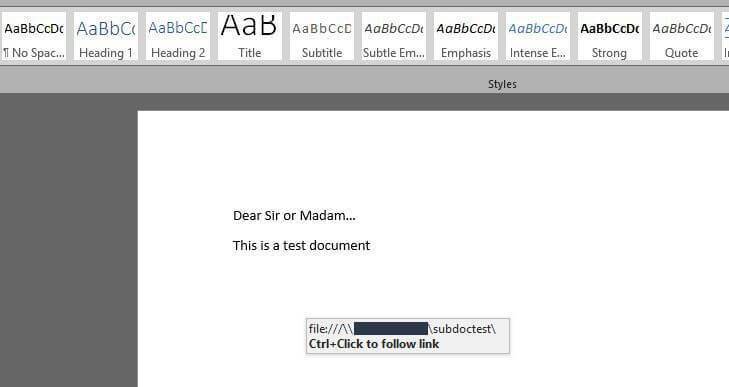
236ArticlesAttackers Can Steal Windows Credentials By Exploiting The subDoc Feature In Microsoft Word
Security researchers from Rhino Labs (a US-based cyber-security firm) have found that cyber criminals can use a Microsoft Word feature dubbed subDoc to fool...
-

 160Vulnerabilities
160VulnerabilitiesWeb Trackers are now Exploiting Password Managers to Track User Behavior
Password Managers have been around for quite some time, and most of us rely on them for managing our passwords across several...
-

 202Cyber Attack
202Cyber AttackSatori IoT Botnet Is Exploiting Zero Day To Zombify Huawei Routers
Although the original creator of the infamous Mirai IoT botnet was arrested and sent to prison, botnet options are known because of...
-

 182Cyber Attack
182Cyber AttackHackers Are Making $63,000 In 3 Months By Exploiting Microsoft Servers To Mine Monero
Mining cryptocurrencies like mine monero can be a costly investment as they require a monstrous amount of computing power, so hackers have begun...
-
 212Vulnerabilities
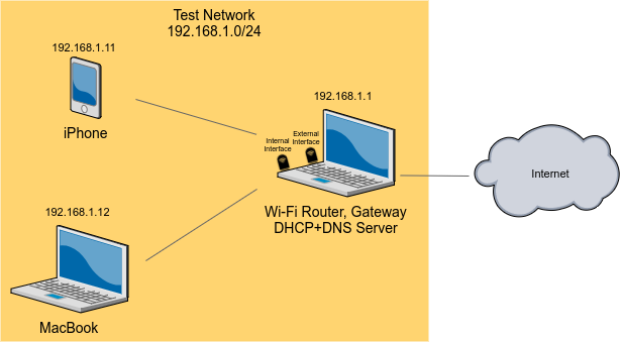
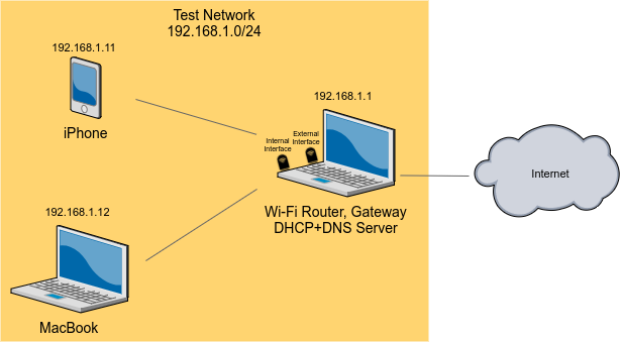
212VulnerabilitiesExploiting The Wi-Fi Stack on Apple Devices
Earlier this year we performed research into Broadcom’s Wi-Fi stack. Due to the ubiquity of Broadcom’s stack, we chose to conduct our...
-

 196Vulnerabilities
196VulnerabilitiesResearchers demonstrate how to steal Bitcoin by exploiting SS7 issues
Hackers have exploited security weaknesses in SS7 protocol to break into a GMail account, take control of a bitcoin wallet and steal...
-

 539News
539NewsBashware lets malware evade detection by exploiting Windows 10′ Linux Shell
Bashware Technique Can Exploit Windows Subsystem for Linux (WSL) to Hide Malware Making 400 Million Computers Vulnerable. Security firm Checkpoint’s researchers Gal...
-
 204Malware
204MalwarePowerPoint Slide Show Infected by New Malware that Exploiting Zero-day RCE Vulnerability
New Malware that abuses MS Power point slide show by Exploiting the CVE-2017-0199 (Zero-day remote code execution vulnerability) flow Exists in Windows OLE...
-

 258News
258NewsShips Can Be Hacked By Exploiting VSAT Communication System
Satellite antenna systems are not spared from vulnerabilities and are quite prone to cyber-attacks, which makes devices and machinery from which these...
-

 283Vulnerabilities
283VulnerabilitiesThe Weak Bug – Exploiting a Heap Overflow in VMware
Introduction In march 2017, I took part in the pwn2own contest with team Chaitin Security Research Lab. The target I was focused on was...
-
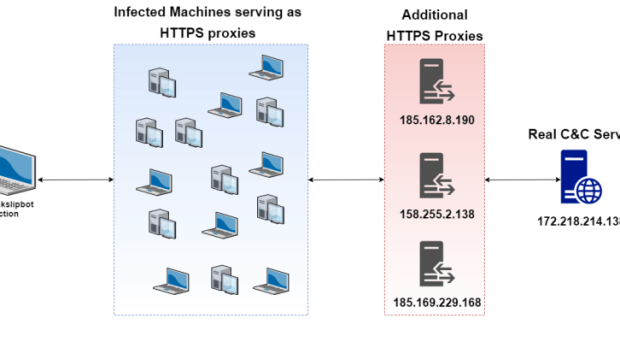
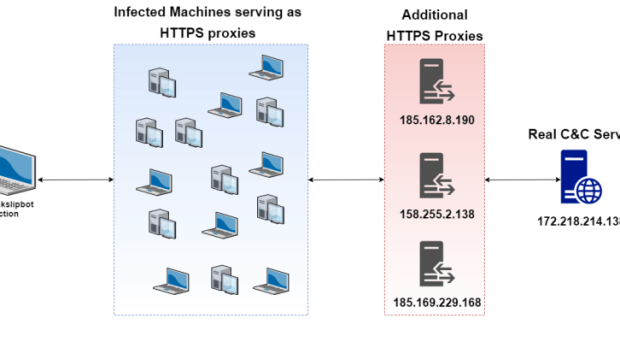 154Incidents
154IncidentsPinkslipbot banking Trojan exploiting infected machines as control servers
Pinkslipbot banking Trojan is a banking Trojan that uses a complicated multistage proxy for HTTPS-based control server communication. Security researchers at McAfee Labs...
-
 112Vulnerabilities
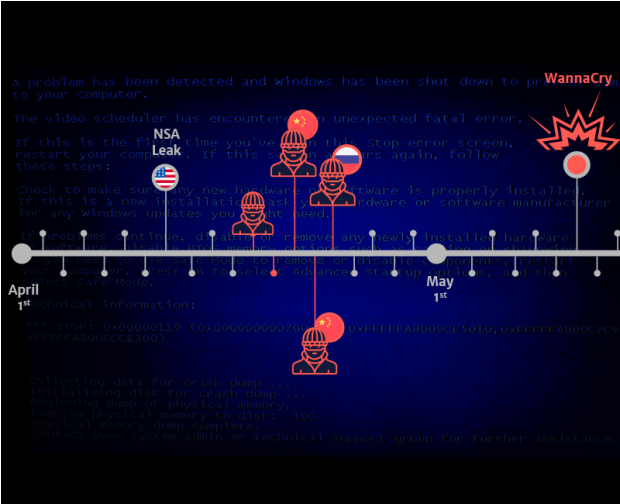
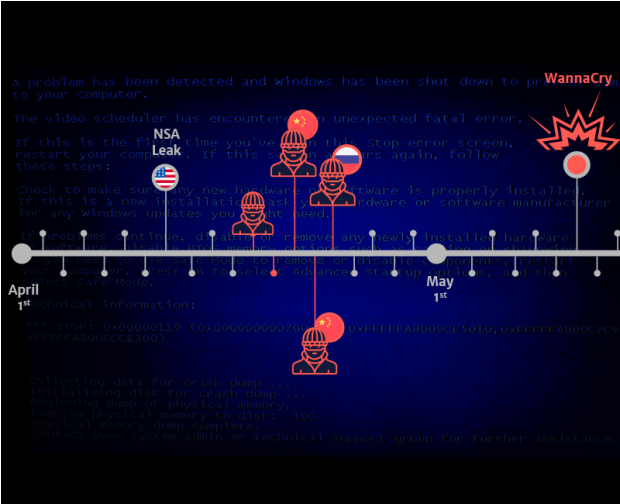
112VulnerabilitiesMultiple Groups Have Been Exploiting ETERNALBLUE Weeks Before WannaCry
We have found evidence of much more sophisticated actors leveraging the NSA ETERNALBLUE exploit to infect, install backdoors and exfiltrate user credentials...
-
 184Vulnerabilities
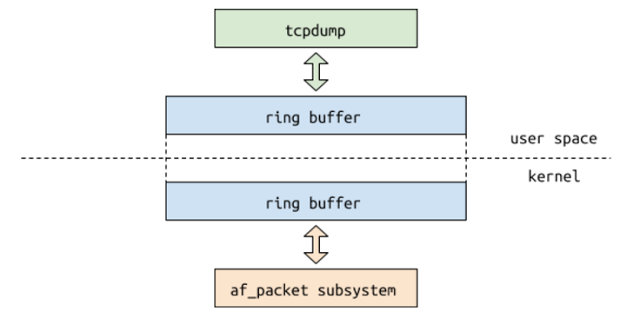
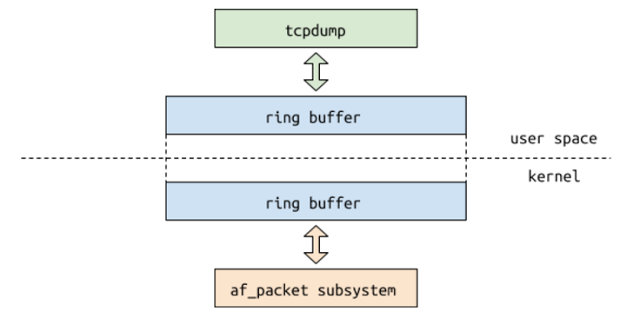
184VulnerabilitiesExploiting the Linux kernel via packet sockets
Lately I’ve been spending some time fuzzing network-related Linux kernel interfaces with syzkaller. Besides the recently discovered vulnerability in DCCP sockets, I...
-
 192Vulnerabilities
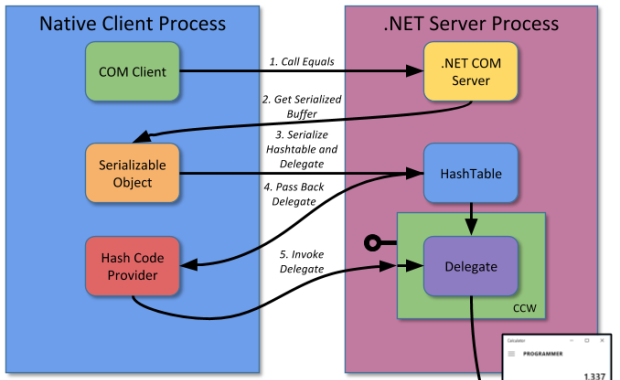
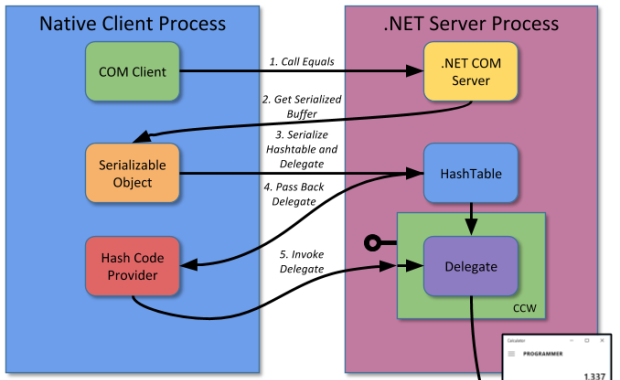
192VulnerabilitiesExploiting .NET Managed DCOM
One of the more interesting classes of security vulnerabilities are those affecting interoperability technology. This is because these vulnerabilities typically affect any...






