Search results for "Exploits"
-
 264Hacking Tools
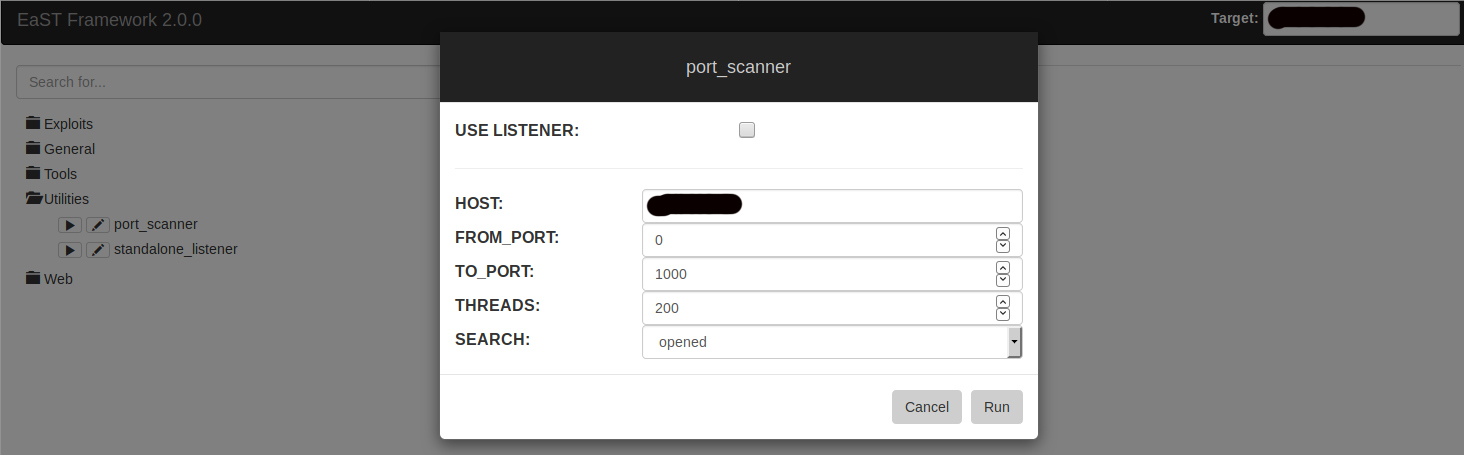
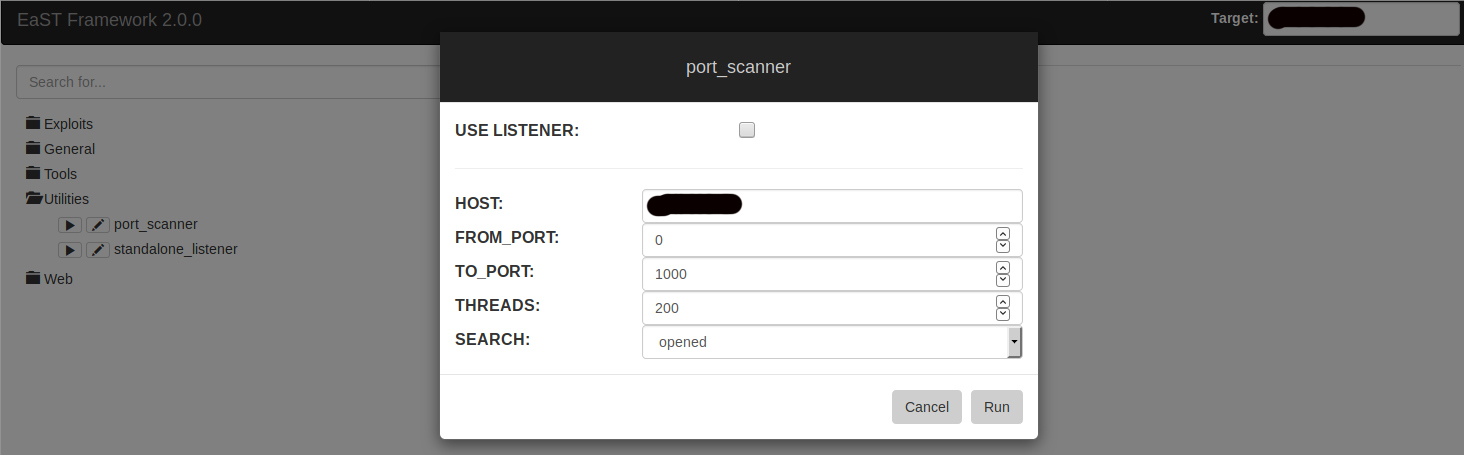
264Hacking ToolsEaST – Open Source Exploits and Security Tools Framework
East is a Python based security framework toolkit. It acts as a HTTP server and contains a wide range of different exploits...
-
 221Data Security
221Data SecurityApache Struts & SonicWall’s GMS exploits key targets of Mirai & Gafgyt IoT malware
Security researchers at Palo Alto Networks’ Unit 42 have discovered modified versions of the notorious Mirai and Gafgyt Internet of Things (IoT)...
-

 336Hacked
336HackedDefcon 2018: Hacker Exploits Vulnerabilities In macOS With “Invisible Clicks”
At Defcon 2018, ex-NSA staffer and a popular Mac hacker Patrick Wardle presented his research work which involved bypassing the layers of...
-

 361Data Security
361Data SecurityZombieBoy cryptomining malware exploits CVEs to evade detection
ZombieBoy malware makes $1,000 Monero on a monthly basis. An independent security expert James Quinn has discovered a new family of cryptominers that...
-

 230Vulnerabilities
230VulnerabilitiesZerodium pays up to $500 000 for zero-day exploits
The sale of zero-day exploits is a very profitable business that most people completely ignore. The International Institute of Cyber Security talks...
-

 193Data Security
193Data SecurityRedisWannaMine Unveiled: New Cryptojacking Attack Powered by Redis and NSA Exploits
Recently cryptojacking attacks have been spreading like wildfire. At Imperva we have witnessed it firsthand and even concluded that these attacks hold roughly...
-

 307Malware
307MalwareNew Cryptocurrency Mining Malware “MassMiner” Attacking Web Servers Using various Powerful Exploits
Newly discovered cryptocurrency mining malware called MasssMiner using various powerful exploits to compromise web servers to mine monero Cryptocurrency around the world....
-

 328Pentest
328PentestExploit Pack V10.07 Released with More than 38.000+ Exploits Including Zero-Days
Exploit Pack is a well-integrated open source tool for conducting professional penetration tests. As like any other penetration testing tool it requires...
-
 217News
217NewsMaster Key Hack Exploits Flaw in Key System to Unlock Hotel Rooms
The master key hack has the capability of unlocking not hundreds or thousands but millions of hotel rooms, claim F-Secure security researchers....
-

 321Data Security
321Data SecurityPyRoMine malware disables security & mines Monero using NSA exploits
The IT security researchers at Fortinet have discovered a dangerous new malware that not only mines Monero cryptocurrency but also disables security features...
-
 277Malware
277MalwareHackers Distributing Variety of New Exploits and Malware via Microsoft Office Document Exploit Kit
Newly discovered Microsoft office document exploit kit contains a variety of recent exploits and Malware such as Lokibot, Formbook and tracking kit...
-

 237Incidents
237Incidentsrop-tool v2.4.1 A tool to help you writing binary exploits
rop-tool v2.4.1 A tool to help you writing binary exploits. An information security training expert gives a small explication about output of...
-

 358Incidents
358IncidentsSgxSpectre Exploits Recent Intel CPU Flaw And Leaks “Enclave” Secrets
In modern Intel processors, there’s a hardware extension available named Software Guard Extension (SGX) to improve the security aspects. It provides a...
-

 182Exploitation
182ExploitationFindsploit – Find Exploits In Local And Online Databases Instantly
Findsploit is a simple bash script to quickly and easily search both local and online exploit databases. This repository also includes “copysploit”...
-
 290Vulnerabilities
290VulnerabilitiesDoubleDoor – An IoT Botnet Bypasses Firewall Using Backdoor Exploits
IoT Backdoor exploits called Doubledoor have been discovered which allows bypassing an IoT layered security that leads to taking complete control of...
-
 410Vulnerabilities
410VulnerabilitiesAndroRAT – A Remote Access Trojan Compromise Android Devices and Inject Root Exploits
A Newly discovered Android Remote Access Trojan called AndroRAT targeting unpatched Android Devices that exploit the publicly disclosed critical privilege escalation vulnerability and...
-

 300Hacked
300HackedLeaked NSA Exploits Modified To Attack Every Windows Version Since 2000
Probably, the most famous of the NSA tools leaked by the hacker group Shadow Brokers was EnternalBlue which gave birth to dangerous malware...
-
 182Incidents
182IncidentsLeaked NSA Exploits Can Now Hack Any Windows Version
Security researcher tweaks exploits stolen from the NSA last year to affect nearly all versions of Windows. Exploits that were stolen from...
-
 361Data Security
361Data SecurityNew Monero mining malware infected 500K PCs by using 2 NSA exploits
Another day, another Monero mining malware – This one uses two NSA exploits and so far it has mined over 8,900 Monero. It looks...
-
 354Data Security
354Data SecurityNew Cryptocurrency Mining Scheme Uses NSA Exploits EternalBlue & EternalSynergy
Due to the unprecedented and unexpected increase in the value of cryptocurrencies like Bitcoin, there has been a sudden rise in cyber-attacks...
-

 398News
398News“Zealot” Campaign Uses NSA Exploits to Mine Monero on Windows and Linux Servers
A new sophisticated malware campaign dubbed “Zealot” leveraging NSA exploits targeting Windows and Linux systems to mine Monero on Internal Networks. Security...






