Search results for "Exploits"
-

 218Malware
218MalwareNew sophisticated Malware campaign Leveraging NSA Exploits to Mine Monero on Windows and Linux Systems
A new sophisticated malware campaign dubbed “Zealot” leveraging NSA exploits targeting Windows and Linux systems to mine Monero on Internal Networks. Security...
-
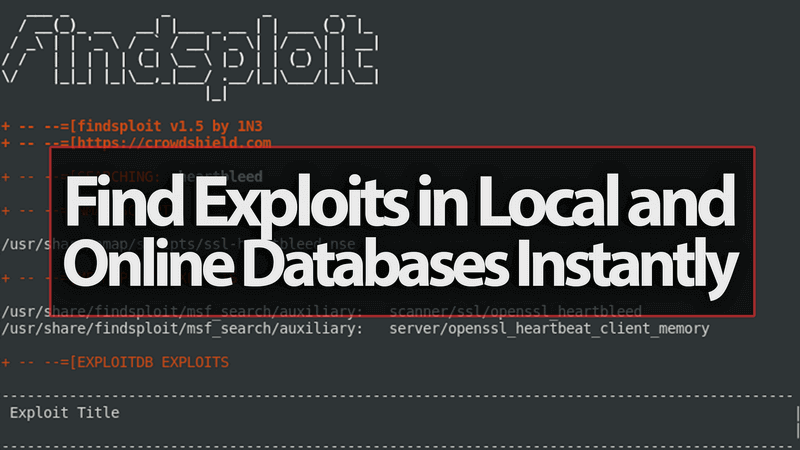
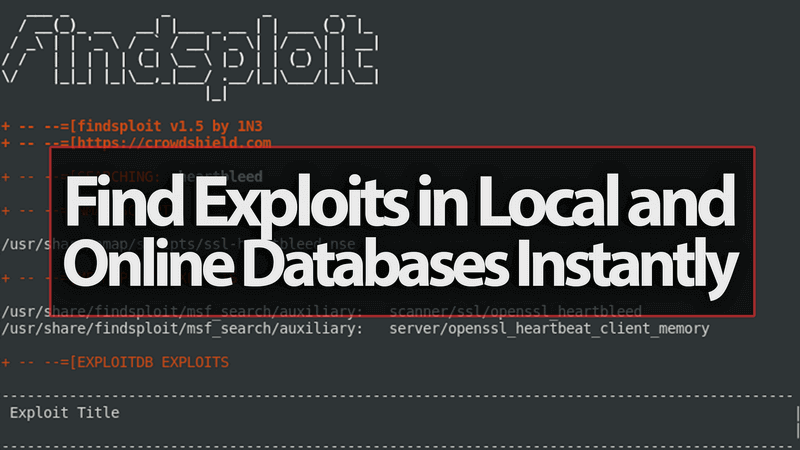 249Video Tutorials
249Video TutorialsFindsploit – Find Exploits in Local and Online Databases Instantly – Kali Linux 2017.3
Findsploit is a simple bash script to quickly and easily search both local and online exploit databases. Findsploit:https://github.com/1N3/Findsploit Installation: git clone https://github.com/1N3/Findsploit.git...
-
 457Data Security
457Data SecurityNew Vulnerability Exploits Antivirus Programs to Install Malware
It is common notion that antivirus software keeps our computers safe from all types of bugs and malware. However, it seems that...
-

 340Cyber Crime
340Cyber CrimeRussian Hacker Exploits GTA 5 PC Mod to Install Cryptocurrency Miner
Gamers were delighted with the release of world’s second most popular video game Grand Theft Auto V (GTA 5) released by Rockstar...
-

 355News
355NewsIsrael hacked Kaspersky to inform US about Russia stealing NSA exploits
Israeli Spies Hacked Kaspersky and Found Russian Hackers Exploiting the Antivirus software to Obtain US Intelligence Secrets. We earlier reported that Russian...
-
 301Malware
301MalwareFirst Android Malware Family Called “ZNIU” that Exploits Dangerous Dirty COW Vulnerability
An Android Malware Family called “ZNIU” Discovered that Exploits the Dirty COW Vulnerability into Android Platform and it performs silent Attacks in...
-

 281Cyber Crime
281Cyber CrimeDisguised as Citrix Utility, Kedi RAT Exploits Gmail to Transfer Data
A Remote Access Trojan (RAT) is one of the most used malicious software used by cybercriminals to target unsuspecting users. Based on its...
-
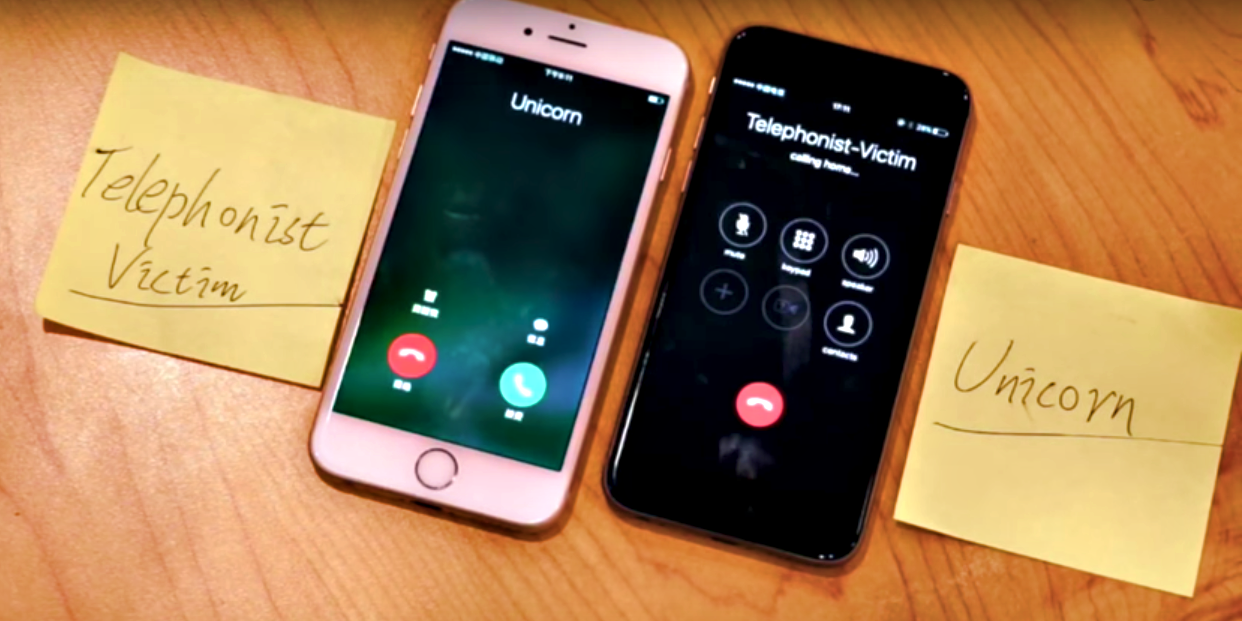
 282News
282News‘Ghost Telephonist’ Attack Exploits 4G LTE Flaw to Hijack Phone Numbers
According to UnicornTeam, a group of Chinese researchers from country’s leading security firm 360 Technology, there is a dangerous vulnerability in 4G...
-

 235Cyber Attack
235Cyber AttackLatest SMB Worm Is Out On The Loose and Uses 7 NSA Tools Exploits
The Researchers have detected a new trojan horse this is spreading via SMB, but not like the malicious program additives of the...
-
 162Vulnerabilities
162VulnerabilitiesNew Shadow Brokers Message Teases Data From Nuke Programs, Windows 10 Exploits
Today, the Shadow Brokers have published a new message teasing new exploits for people who register for a new membership program the...
-

 222Vulnerabilities
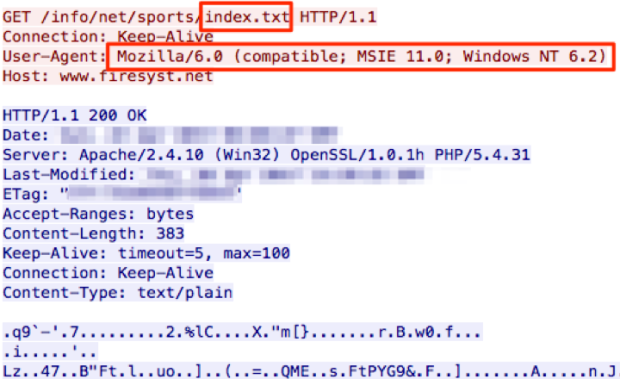
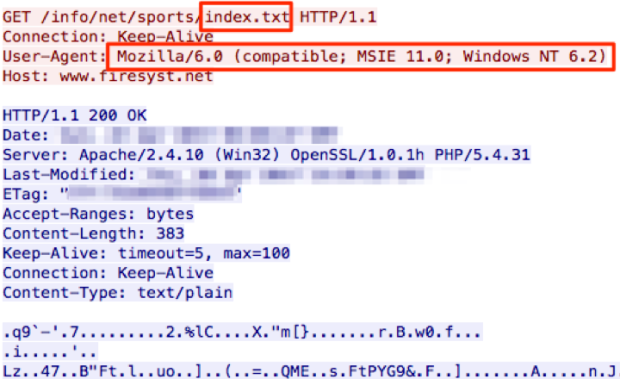
222VulnerabilitiesSednit adds two zero-day exploits using ‘Trump’s attack on Syria’ as a decoy
The Sednit group, also known as APT28, Fancy Bear and Sofacy, is a group of attackers operating since at least 2004 and...
-

 488Malware
488MalwareSednit adds two zero‑day exploits using ‘Trump’s attack on Syria’ as a decoy
Sednit is back - this time with two more zero-day exploits embedded in a phishing email titled Trump's_Attack_on_Syria_English.docx.
-
 142Vulnerabilities
142VulnerabilitiesChinese TA459 APT exploits CVE-2017-0199 flaw to target Financial firms
Malware researchers at security firm ProofPoint reported the Chinese TA459 APT has exploited the CVE-2017-0199 vulnerability to target Financial firms. The notorious...
-
 166Vulnerabilities
166VulnerabilitiesAES-NI Ransomware Dev Claims He’s Using Shadow Brokers Exploits
The developer of the AES-NI ransomware claims that the recent “success” he’s been enjoying is due to the NSA exploits leaked last...
-
 174Vulnerabilities
174VulnerabilitiesShadow Brokers Release New Batch of Files Containing Windows and SWIFT Exploits
On Good Friday and ahead of the Easter holiday, the Shadow Brokers have dumped a new collection of files, containing what appears...
-

 173Hackers Repository
173Hackers RepositoryNSA’s Hacking Tools and Exploits revealed by Shadow Brokers Group
Hot topics now trending is the leak of thousands of documents from CIA’s vault 7 series of documents, these leaks are continuously exposing...
-

 108Hackers Repository
108Hackers RepositoryEaST – Exploits and Security Tools Framework 2.0.0
Exploits and Security Tools Framework 2.0.0 (Credits C0reL0ader) http://eastfw.com/ «EAST» – «Exploits And Security Tools» penetration testing framework. Overview Pentest framework environment...
-
Hackers Repository
RCE Finder – Scan For Remote Code Execution Exploits
RCE_FINDER How to use root@kali:/rce_finder # python scan_rce.py # LOGO ########################################## #| By Rudra Sarkar - @rudr4_sarkar # #| Loaded Modules :...
-
 169Vulnerabilities
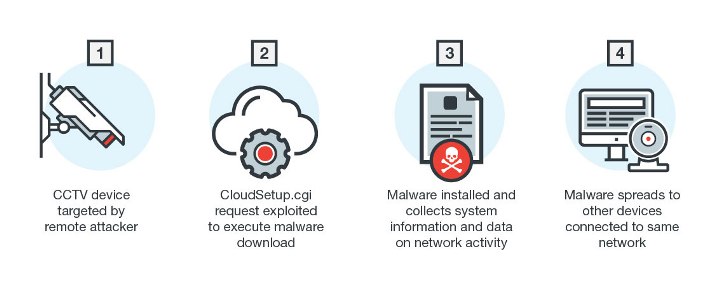
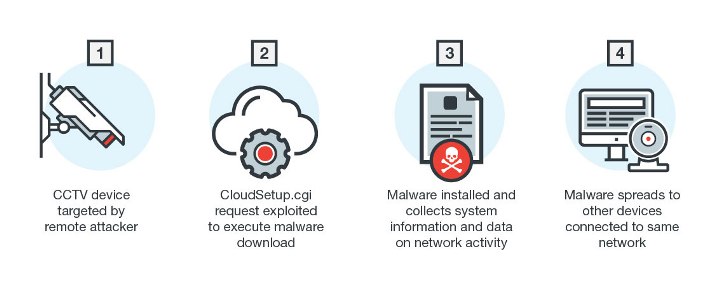
169VulnerabilitiesNew Linux Malware Exploits CGI Vulnerability
Linux has long been the preferred operating system for enterprise platforms and Internet of Things (IoT) manufacturers. Linux-based devices are continually being...
-

 100News
100NewsUsers Who Use Google And Apple Are Safe Against CIA Exploits
Yesterday WikiLeaks printed thousands of documents revealing prime United States intelligence agency CIA Cyber Security hacking secrets, as well as the agency’s...
-
Hackers Repository
Davscan – A Tool That Fingerprints servers, finds exploits, scans WebDAV
DAVScan Credits: Graph-X Download Davscan DAVScan is a quick and lightweight webdav scanner designed to discover hidden files and folders on DAV...






