Search results for "Exploits"
-

 5.1KTutorials
5.1KTutorialsTop 6 illegal darknet markets to find hackers, stolen data, vulnerabilities, exploits, malwares & ransomware
The dark web is mainly known for the idea that in this sector of the Internet you can find all kinds of...
-

 1.0KVulnerabilities
1.0KVulnerabilities3 Zero-Day Exploits Hit SonicWall Enterprise Email Security Appliances
SonicWall has addressed three critical security vulnerabilities in its hosted and on-premises email security (ES) product that are being actively exploited in...
-

 883Cyber Attack
883Cyber AttackGoogle Play App Recent Android Exploits Zero-Day
A malicious code exploited a newly fixed zero-day flaw in the Google Play store that affects multiple Android devices, including Pixel phones...
-

 4.0KMalware
4.0KMalwareTrump.exe; the fake ransomware that exploits the image of President Donald Trump
US President Donald Trump always resorts to the term ‘fake news’ to refer to news reports that are not favorable to him,...
-
 380Exploitation
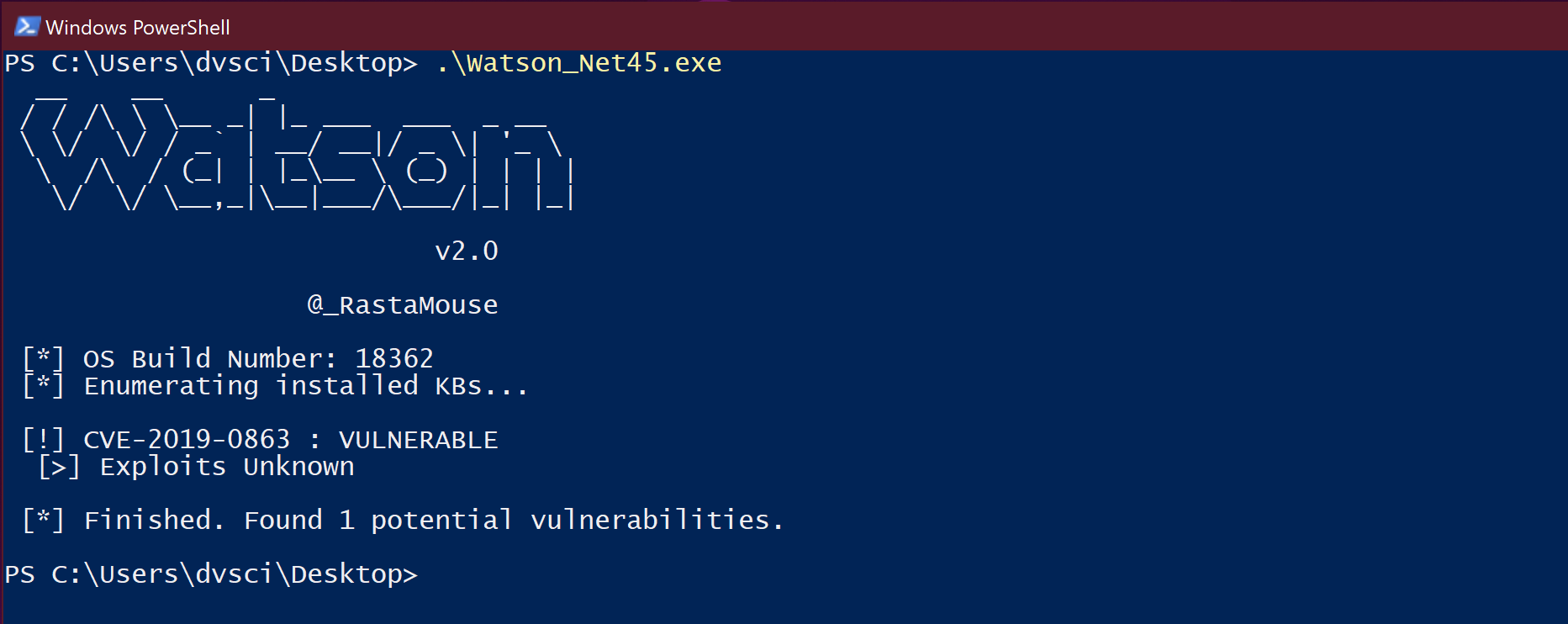
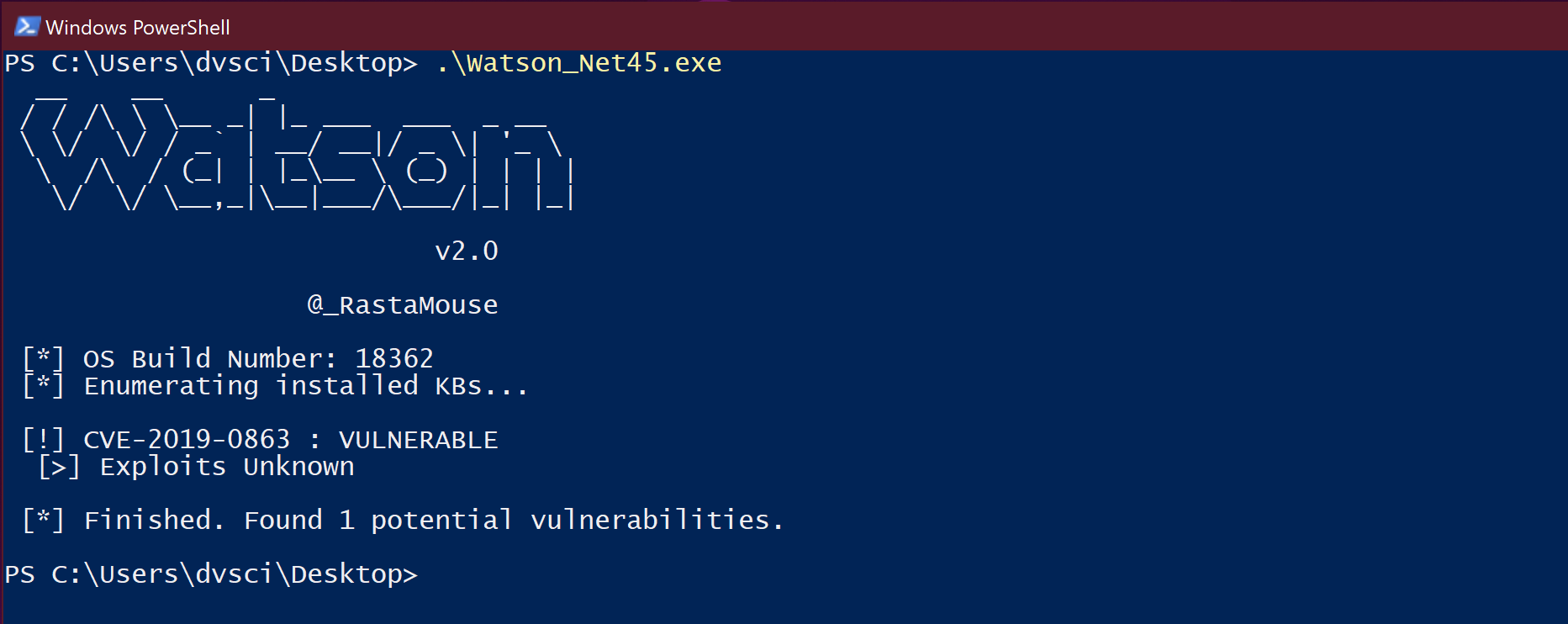
380ExploitationWatson – Enumerate missing KBs and suggest exploits for useful Privilege Escalation vulnerabilities
Watson is a .NET tool designed to enumerate missing KBs and suggest exploits for useful Privilege Escalation vulnerabilities. My focus is on...
-
 482Malware
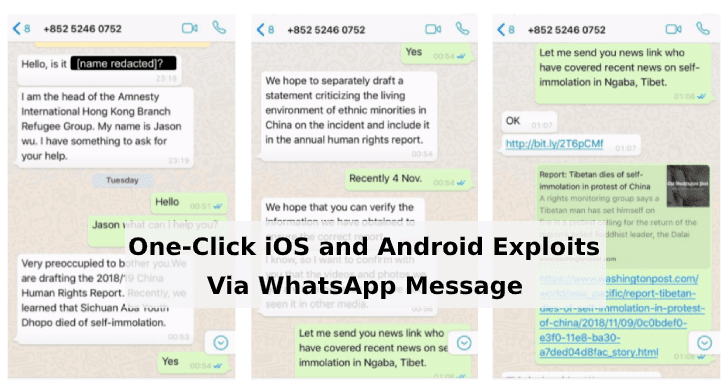
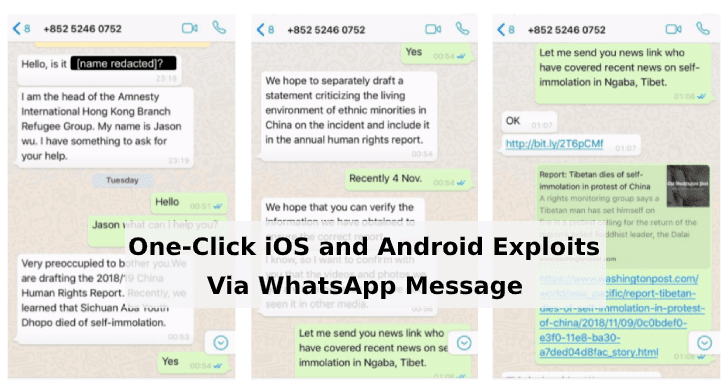
482MalwareOne-Click iOS and Android Exploits Targets Tibetan Users Via WhatsApp Message to Deliver Malware
A new highly sophisticated malware campaign targets Tibetan groups to exploit and install spyware on their iPhone and Android devices. The spyware...
-

 187Incidents
187IncidentsSee How- One Click Mobile Exploits Targets Tibetans
A Senior staff oficial group was contacted on Whatsapp from a unknown number. The caller claim to be Jason Mu, Head of...
-
 500Data Security
500Data SecurityZerodium to pay up to $2.5 million for reporting 0-day Android exploits
Zero-Day Android exploits are now more valuable then iOS exploits. The infosec and premium zero-day acquisition platform Zerodium known for selling zero-day...
-
 335Ransomware
335RansomwareNew Sodin Ransomware Exploits Windows Vulnerability to Elevate Privilege and Lock All the Files
Researchers discovered a new Sodin Ransomware (also known as Sodinokibi) that exploits the Windows Elevation privilege vulnerability resides in the Win32k component....
-
 307Malware
307MalwareNew Mac Malware Exploits GateKeeper Bypass Bug that Apple Left Unpatched
Cybersecurity researchers from Intego are warning about possible active exploitation of an unpatched security vulnerability in Apple’s macOS Gatekeeper security feature details...
-

 322Malware
322MalwareIranian MuddyWater APT Hackers Adds New Exploits in Their Hacking Arsenal to Attack Government Networks
Threat actors from MuddyWater APT groups now add a new set of latest exploits to their hacking arsenal and tactics, techniques and...
-
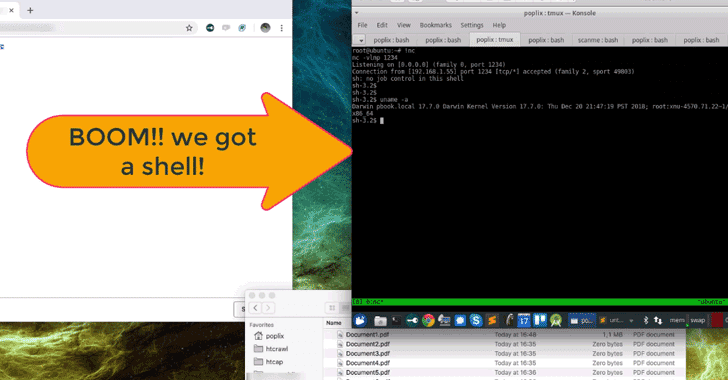
 216Malware
216MalwareBlackSquid Malware Uses Eight Exploits to Attack Web Servers, Network Drives, and Removable Drives
A new malware dubbed BlackSquid bags eight notorious exploits to drop XMRig Monero cryptocurrency miner targeting web servers, network drives, and removable...
-
 365Malware
365MalwareNew Variant of Mirai Malware Using 13 Different Exploits to Hack Routers Including D-Link, Linksys, GPON, Netgear, Huawei
Researchers discovered a new wave of Mirai Variant that used 13 different exploits to attack various router models and other network devices....
-

 267News
267News‘Sodinokibi’ Is A New Ransomware That Exploits Oracle Zero Day Flaw
A couple of weeks back, a zero-day vulnerability was discovered in Oracle WebLogic Servers that can trigger the deserialization of malicious code and allow...
-

 302Infosec
302InfosecFLASHMINGO – Free Threat Intelligence Tool for Malware Analysts’ to Analyse Flash Exploits
FireEye released a Free automated analysis tool FLASHMINGO, which enables malware analysts to detect suspicious flash samples and to investigate them. The...
-
 300Articles
300ArticlesMirai Variant Adds Dozen New Exploits to Target Enterprise IoT Devices
Security researchers have uncovered a new variant of the infamous Mirai Internet of Things botnet, this time targeting embedded devices intended for...
-

 256Ransomware
256RansomwareAlert !! Hackers Launching New JNEC.a Ransomware via WinRAR Exploits – Do not Pay
A brand new JNEC.a ransomware spreading via recently discovered WinRAR vulnerability exploit to compromise windows computer & demand the ransom amount. This...
-
 224Malware
224MalwareFirst Malware Campaign Exploits WinRAR ACE vulnerability To Hack Windows Computer
Researchers have detected the first malspam campaign that delivers a malicious RAR archive to infect victim’s computer exploiting the WinRAR ACE vulnerability....
-

 307News
307NewsWhat Can We Learn From The Spear Phishing Exploits Against Telstra
Cybersecurity researchers have warned the public that there is a convincing phishing email pretending to be coming from Telstra, the Telco giant....
-

 317Ransomware
317RansomwareHackers Launching Fallout Exploit Kit with New Flash Exploits That Delivers GandCrab Ransomware
One of the dangerous Fallout exploit kit now back to form with various new futures and delivering one of the widely distributed...
-
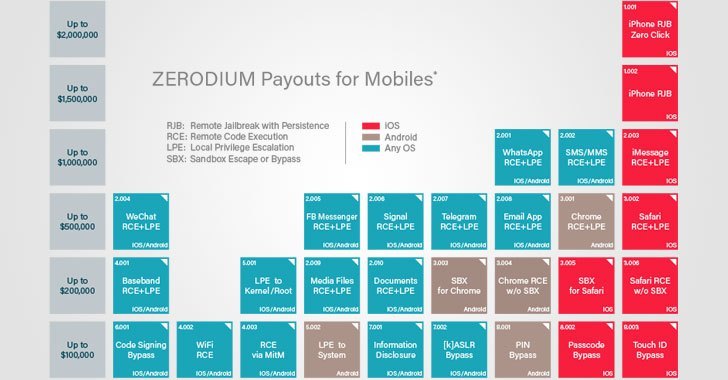
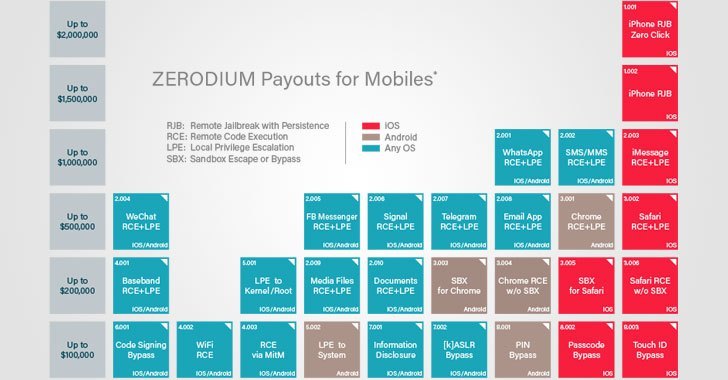 160Articles
160ArticlesZerodium Offers to Buy Zero-Day Exploits at Higher Prices Than Ever
Well, there’s some good news for hackers and vulnerability hunters, though terrible news for tech manufacturers! Exploit vendor Zerodium is now willing...






