Search results for "Exploits"
-
 4.8KVulnerabilities
4.8KVulnerabilitiesNew Ransomware Strain ‘CACTUS’ Exploits VPN Flaws to Infiltrate Networks
Cybersecurity researchers have shed light on a new ransomware strain called CACTUS that has been found to leverage known flaws in VPN...
-
 623Vulnerabilities
623VulnerabilitiesNSO Group Used 3 Zero-Click iPhone Exploits Against Human Rights Defenders
Israeli spyware maker NSO Group deployed at least three novel “zero-click” exploits against iPhones in 2022 to infiltrate defenses erected by Apple...
-
 5.1KMalware
5.1KMalwareIceFire Ransomware Exploits IBM Aspera Faspex to Attack Linux-Powered Enterprise Networks
A previously known Windows-based ransomware strain known as IceFire has expanded its focus to target Linux enterprise networks belonging to several media...
-

 4.9KCyber Attack
4.9KCyber AttackZerobot Botnet Emerges as a Growing Threat with New Exploits and Capabilities
The Zerobot DDoS botnet has received substantial updates that expand on its ability to target more internet-connected devices and scale its network....
-
 3.5KVulnerabilities
3.5KVulnerabilitiesFix these Windows vulnerabilities before someone exploits them
On many occasions, security flaws appear that can compromise our devices. They can affect operating systems like Windows, applications, drivers. It is...
-

 3.3KMalware
3.3KMalwareMicrosoft Uncovers Austrian Company Exploiting Windows and Adobe Zero-Day Exploits
A cyber mercenary that “ostensibly sells general security and information analysis services to commercial customers” used several Windows and Adobe zero-day exploits...
-

 4.3KMalware
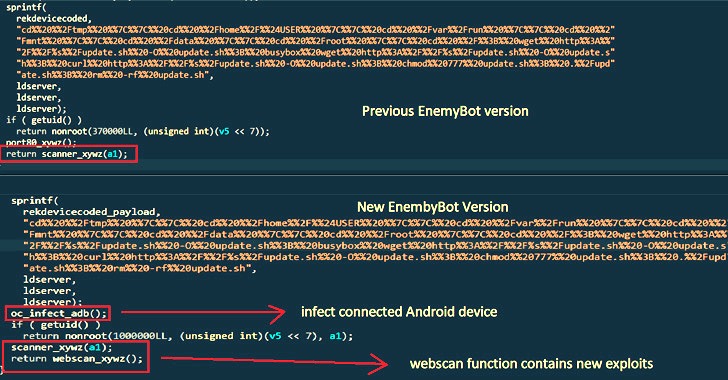
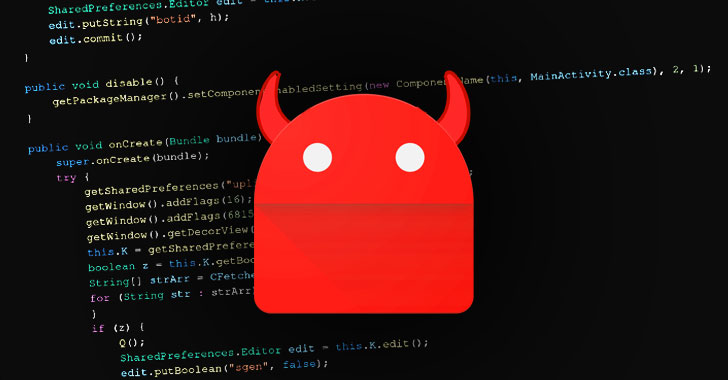
4.3KMalwareEnemyBot: New IoT malware exploits one-day vulnerabilities to hack thousands of devices
Cybersecurity specialists from AT&T Alien Labs report the detection of an Internet of Things (IoT) malware variant targeting content management systems (CMS),...
-
 2.6KMalware
2.6KMalwareEnemyBot Linux Botnet Now Exploits Web Server, Android and CMS Vulnerabilities
A nascent Linux-based botnet named Enemybot has expanded its capabilities to include recently disclosed security vulnerabilities in its arsenal to target web...
-
 4.9KMalware
4.9KMalwareCytrox’s Predator Spyware Targeted Android Users with Zero-Day Exploits
Google’s Threat Analysis Group (TAG) on Thursday pointed fingers at a North Macedonian spyware developer named Cytrox for developing exploits against five...
-
 3.4KMalware
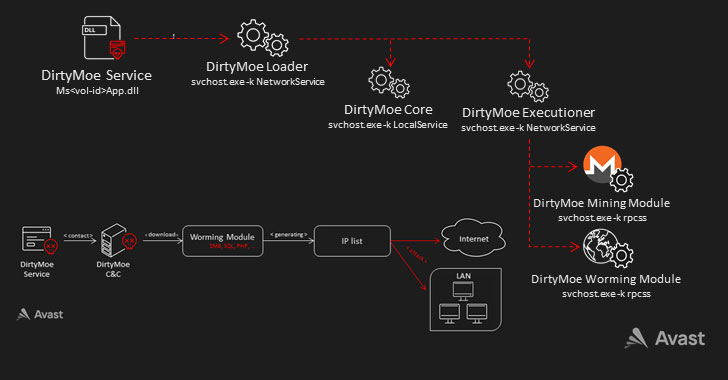
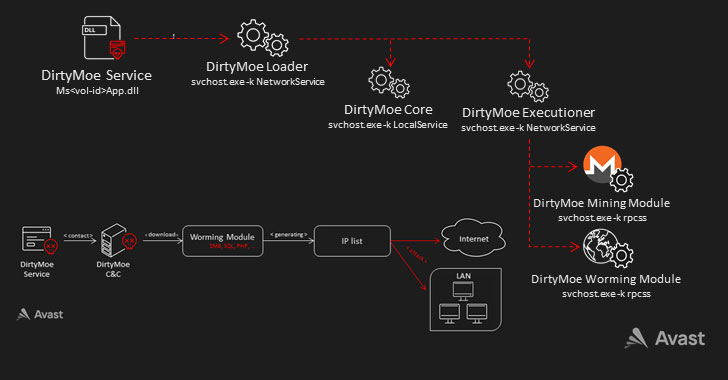
3.4KMalwareDirtyMoe Botnet Gains New Exploits in Wormable Module to Spread Rapidly
The malware known as DirtyMoe has gained new worm-like propagation capabilities that allow it to expand its reach without requiring any user...
-

 395Malware
395MalwareNew “B1txor20” Linux Botnet Uses DNS Tunnel and Exploits Log4J Flaw
A previously undocumented backdoor has been observed targeting Linux systems with the goal of corralling the machines into a botnet and acting...
-

 1.7KNews
1.7KNewsCISA Warns of Imminent Exploits on Zabbix Monitoring Tool’s Recent Vulnerabilities
This week, CISA updated Known Exploited Vulnerabilities Catalog by adding two flaws emanating from Zabbix monitoring solution. The two vulnerabilities, CVE-2022-23134 and...
-

 4.9KVulnerabilities
4.9KVulnerabilitiesNew ransomware exploits vulnerabilities in Log4j to encrypt VMware servers
A ransomware operation identified as Night Sky has been infecting multiple VMware Horizon deployments thanks to the exploitation of the critical vulnerability...
-
 537Malware
537MalwareHackers Attack MS Exchange Servers Using ProxyShell & ProxyLogon Exploits to Distribute Malware
Hackers are Targeting Microsoft Exchange servers using exploits to distribute malware. The vulnerabilities allow hackers to bypass detection by sending emails with...
-
 1.2KRansomware
1.2KRansomwareCring Ransomware Gang Exploits 11 Years Old Adobe Bug & Take Over ColdFusion Server Remotely
Sophos researchers has uncovered an unusually clever ransomware gang, that is named as “Cring Ransomware” that Exploits Ancient ColdFusion Server. Here, the...
-
 2.6KCyber Events
2.6KCyber EventsConti ransomware affiliates hit Exchange Servers with ProxyShell exploits
According to researchers, threat actors including Conti ransomware affiliates are exploiting 3 unpatched vulnerabilities that allow unauthenticated, remote code execution on MS...
-
 3.5KVulnerabilities
3.5KVulnerabilitiesConti Ransomware Gang Hacking Microsoft Exchange Servers Using ProxyShell Exploits
Researchers uncovered a new ongoing attack by Conti Ransomware Gang that utilized the ProxyShell to target the organization networks. ProxySell is an...
-

 1.5KMalware
1.5KMalwareNorth Korean Hacker Group Uses Browser Exploits to Deliver a Custom Malware
The security experts of the cybersecurity firm, Volexity have recently reported an attack through which the North Korean Hacker Group using browser...
-

 1.7KMalware
1.7KMalwareGitHub Updated Policies For Actively Used Exploits, Malware & Vulnerability Research
A set of all-new updates were being released by GitHub on Friday, all the updates pronounce that how the company will deal...
-
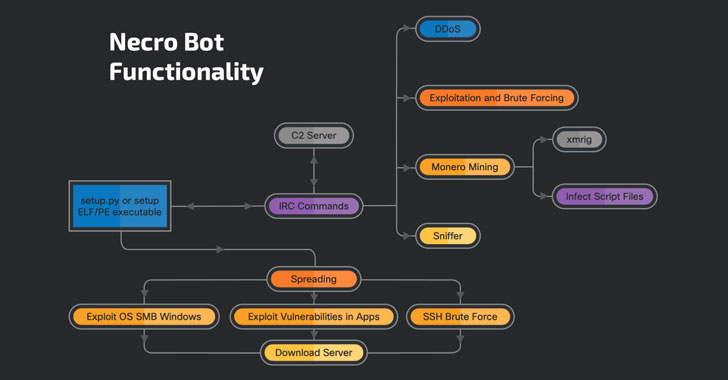
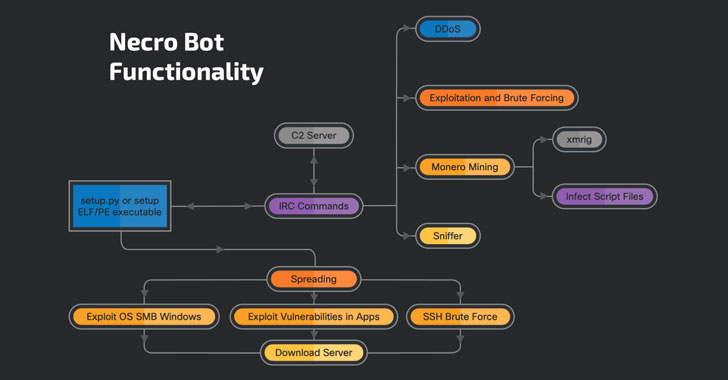 3.8KMalware
3.8KMalwareNecro Python Malware Upgrades With New Exploits and Crypto Mining Capabilities
New upgrades have been made to a Python-based “self-replicating, polymorphic bot” called Necro in what’s seen as an attempt to improve its...
-

 3.1KData Security
3.1KData SecurityZerodium offers up to $100kUSD for zero-day exploits on Pidgin messaging platform
Zerodium operators announced a plan to pay up to $100,000 USD for zero-day flaws in Pidgin, the popular instant messaging client for...






