Search results for "Exploits"
-

 196News
196NewsHacker Exploits Remote Code Execution Bug to Breach Facebook Security
Andrew Leonov, a security researcher, discovered a critical remote execution bug on Facebook allowing him to breach the security of social media...
-

 244How To
244How ToDAVScan – Fingerprints Servers, Finds Exploits & Scans WebDAV
DAVScan is a quick and lightweight webdav scanner designed to discover hidden files and folders on DAV enabled webservers. The scanner works...
-

 193Vulnerabilities
193VulnerabilitiesNewly Uncovered Site Suggests NSA Exploits for Direct Sale
The Shadow Brokers—a hacker or group of hackers that stole computer exploits from the National Security Agency—has been quiet for some time....
-

 136Malware
136MalwareLocky ransomware campaign exploits fears of data stolen in OPM hack
Emails tell victims they need to download an attachment to view “suspicious activity” – then infects them with ransomware. In the immediate...
-
 103Vulnerabilities
103VulnerabilitiesSundown Is Just a Bunch of Exploits Stolen from Other Exploit Kits
Sundown EK fails to improve market share among fellow EKs. The Sundown exploit kit (EK), which has been trying to fill the void...
-

 215Data Security
215Data SecurityWeb Scripting Language PHP-7 Vulnerable to Remote Exploits
Exploiting server side bugs is a jackpot for hackers. Users tend to keep their data in one big pot – the server....
-

 91Data Security
91Data SecurityGroup claims to hack NSA-tied hackers, posts exploits as proof
Extraordinary claim gets attention of security experts everywhere. In what security experts say is either a one-of-a-kind breach or an elaborate hoax, an...
-
 166Vulnerabilities
166VulnerabilitiesHackers brew Intel chip defence kit to neuter budding exploits
Researchers claim they can stop malware before it executes. Black Hat EndGame vulnerability researchers Cody Pierce, Matt Spisak, and Kenneth Fitch have created...
-
 133Data Security
133Data SecurityCVE-2015-1641 and CVE-2015-2545 Are Today’s Most Popular Microsoft Word Exploits
Office exploit kits updates drop support for CVE-2012-0158. Two newer vulnerabilities targeting the Microsoft Office suite have become very popular in recent months,...
-

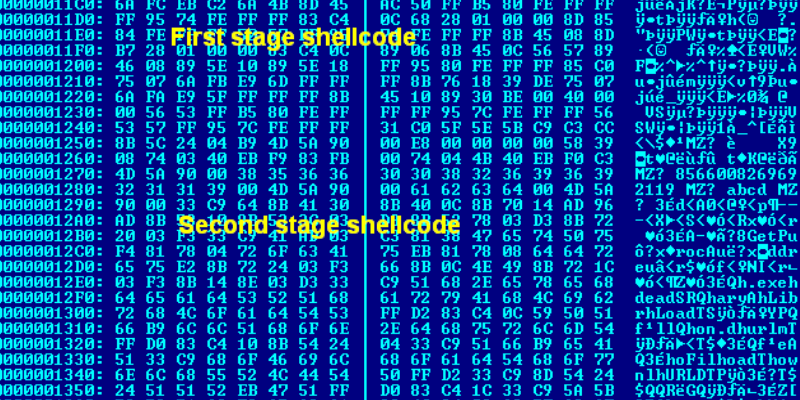
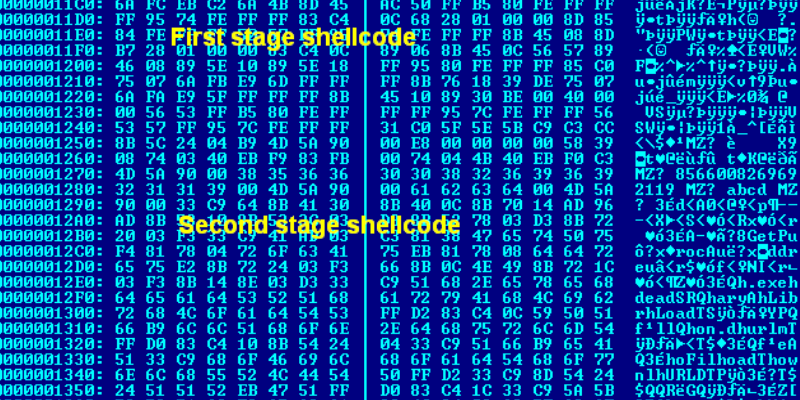
 216Vulnerabilities
216VulnerabilitiesWriting Exploits for Win32 Systems from Scratch
This post is aimed at those new to exploit development and wanting to understand the end-to-end process and types of techniques that...
-
 170Data Security
170Data Security‘GODLESS’ Mobile Malware Uses Multiple Exploits to Root Devices
We came across a family of mobile malware called Godless (detected as ANDROIDOS_GODLESS.HRX) that has a set of rooting exploits in its...
-
 174Data Security
174Data SecurityTor Browser Integrates Tool to Fend Off Deanonymization Exploits
Selfrando is an alternative to ASLR memory randomization. At the start of June, the Tor Project released version 6.5a1 of the Tor Browser,...
-

 112Data Security
112Data SecurityRIP ROP: Intel’s cunning plot to kill stack-hopping exploits at CPU level
How Chipzilla and Microsoft hope to get one step ahead of hackers. Intel is pushing a neat technique that could block malware infections...
-
 291Data Security
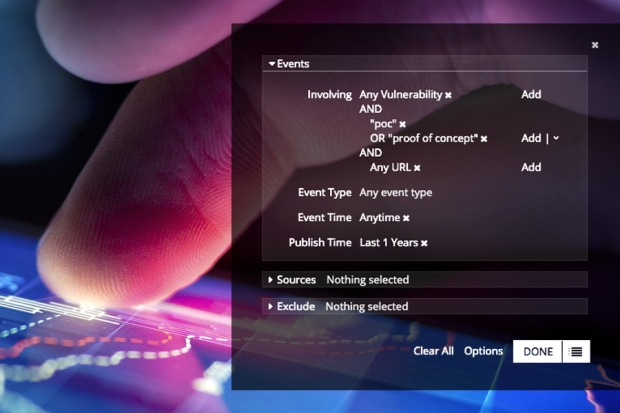
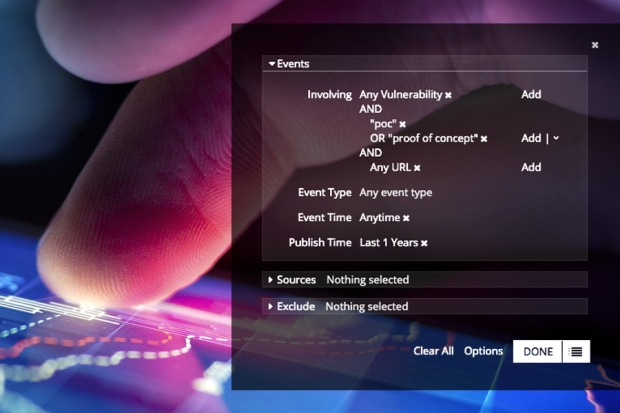
291Data SecurityProve It: The Rapid Rise of 12,000 Shared Proof-of-Concept Exploits
Recorded Future’s real-time threat intelligence product allows analysts access to hundreds of thousands of sources that are normalized, organized, and searchable for...
-

 180Vulnerabilities
180VulnerabilitiesActive drive-by exploits critical Android bugs, care of Hacking Team
Hostile JavaScript delivered through ads installs ransomware on older Android phones. An ongoing drive-by attack is forcing ransomware onto Android smartphones by exploiting...
-

 173Data Security
173Data SecurityDRAM bitflipping exploits that hijack computers just got easier
Approach relies on already installed code, including widely used glibc library. New research into the “Rowhammer” bug that resides in certain types of...
-

 244Cyber Crime
244Cyber CrimeVulnerabilities, exploits and patches
David Harley, a senior research fellow at ESET, offers expert answers to six important questions that concern vulnerabilities, exploits and patches.
-

 90Data Security
90Data SecurityYahoo’s “crypto witch” exploits web security feature, learns your site history
Timing attacks are an interesting part of computer security. As an extreme example, imagine that your computer took one second to verify...
-
 159Vulnerabilities
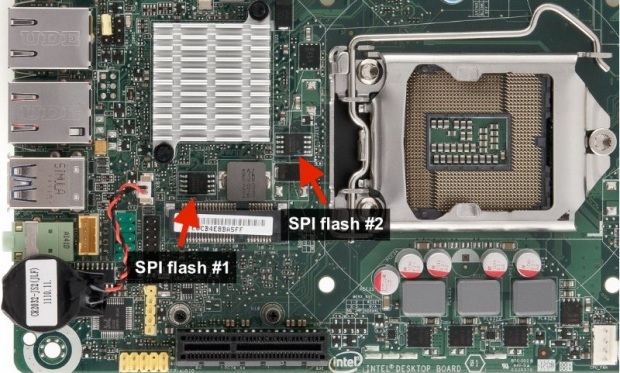
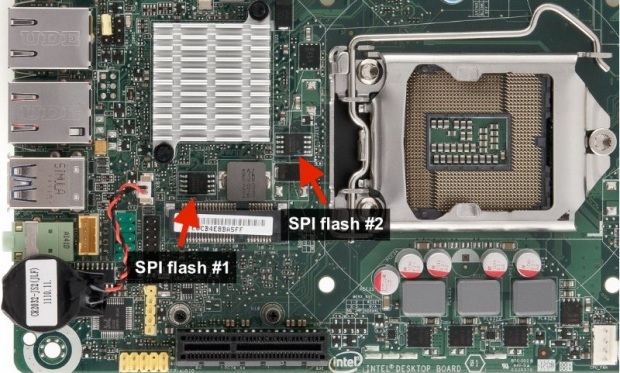
159VulnerabilitiesCHIPSEC Module That Exploits UEFI Boot Script Table Vulnerability
This vulnerability was discovered by Rafal Wojtczuk and Corey Kallenberg, check original white paper. Around one month ago, at 31-st Chaos Communication...
-
 252Data Security
252Data SecurityZero-Day, Angler kit exploits help drive up malvertising by 325%
A massive uptick in malvertising has taken place over the last few years and is becoming so popular that it may become...
-

 136Opinion
136OpinionOperating System Vulnerabilities, Exploits and Insecurity
iOS and OS X the most vulnerable operating systems? Don't confuse vulnerabilities with exploits, or patch frequency with insecurity.






