Search results for "Intelligence"
-

 2.3KMalware
2.3KMalwareRiding the AI Waves: The Rise of Artificial Intelligence to Combat Cyber Threats
In nearly every segment of our lives, AI (artificial intelligence) now makes a significant impact: It can deliver better healthcare diagnoses and...
-
 945Vulnerabilities
945VulnerabilitiesGoogle Expands Its Bug Bounty Program to Tackle Artificial Intelligence Threats
Google has announced that it’s expanding its Vulnerability Rewards Program (VRP) to compensate researchers for finding attack scenarios tailored to generative artificial...
-

 2.0KTutorials
2.0KTutorialsHow to Use Advanced Network Intelligence Toolkit for Pentesting: badKarma
Searching vulnerabilities on the host (the host can be a website, web server, network device (router and others), end-user computer) begins with...
-

 4.4KIncidents
4.4KIncidentsMajor Russian cyberattack globally halted by intelligence agencies in the Netherlands
Thousands of routers owned by small businesses and homes in the Netherlands were hacked in what appears to be a botnet operation...
-
 1.5KCyber Attack
1.5KCyber AttackUS Cyber Command Links ‘MuddyWater’ Hacking Group to Iranian Intelligence
The U.S. Cyber Command (USCYBERCOM) on Wednesday officially confirmed MuddyWater’s ties to the Iranian intelligence apparatus, while simultaneously detailing the various tools...
-
 2.4KGeek
2.4KGeekFields of application of artificial intelligence
At present, it is difficult to find a field of work for people in which different mechanisms and machines are not used...
-

 4.8KGeek
4.8KGeekDevelopment of Corporate Applications Based on Artificial Intelligence
Technologies based on Artificial intelligence can be used in corporate management since the indisputable advantage of these technologies is the ability to...
-
 4.9KHow To
4.9KHow ToHow Artificial intelligence (AI) Stops Cybercriminals
Newer AI algorithms are extremely good at analyzing data traffic, access, and transfer, as well as detecting outliers or anomalies in data...
-
 3.7KCyber Attack
3.7KCyber AttackFBI, CISA Uncover Tactics Employed by Russian Intelligence Hackers
The U.S. Cybersecurity and Infrastructure Security Agency (CISA), Department of Homeland Security (DHS), and the Federal Bureau of Investigation (FBI) on Monday...
-

 1.2KLeaks
1.2KLeaksMastercard Opens New Center and Intelligence in Canada
New Vancouver Space Becomes One of Six Regional Mastercard Innovation Centers on Thursday unveiled a new computer hub situated in Vancouver, Canada...
-

 796Hack Tools
796Hack ToolsFileintel – A Modular Python Application To Pull Intelligence About Malicious Files
This is a tool used to collect various intelligence sources for a given file. Fileintel is written in a modular fashion so...
-

 5.0KNews
5.0KNewsAventura Pays No Security Vulnerabilities for Flogging Chinese Intelligence Devices on the US government 100%
Accusations of fraud were brought against Aventura Technologies and its owner following the suspected selling of monitoring equipment to the US Government...
-
 3.7KInformation Gathering
3.7KInformation GatheringACT Platform – Collection And Exchange Of Threat Intelligence Information
Semi-Automated Cyber Threat Intelligence (ACT) is a research project led by mnemonic as with contributions from the University of Oslo, NTNU,...
-

 440Exploitation Tools
440Exploitation ToolsRITA – Real Intelligence Threat Analytics
RITA is an open source framework for network traffic analysis. The framework ingests Bro/Zeek Logs in TSV format, and currently supports...
-
 482Information Gathering
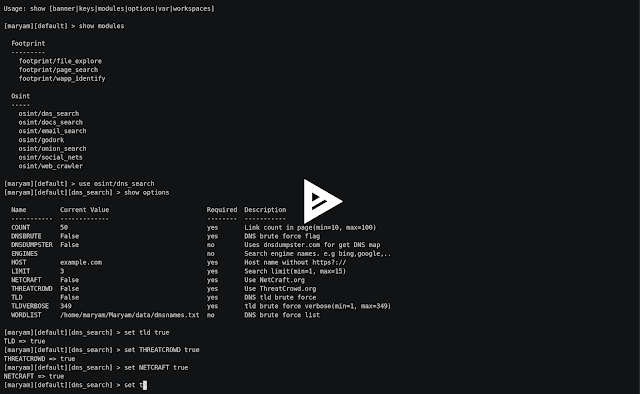
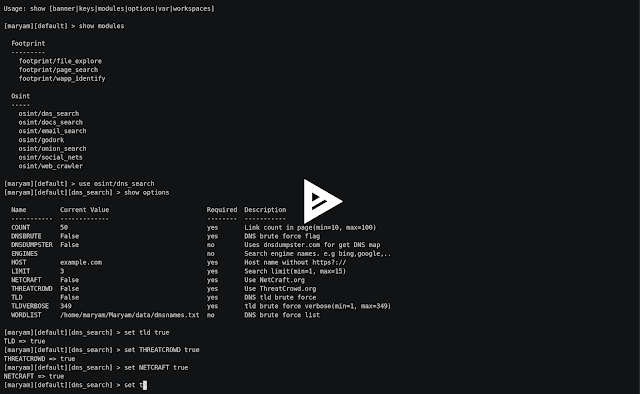
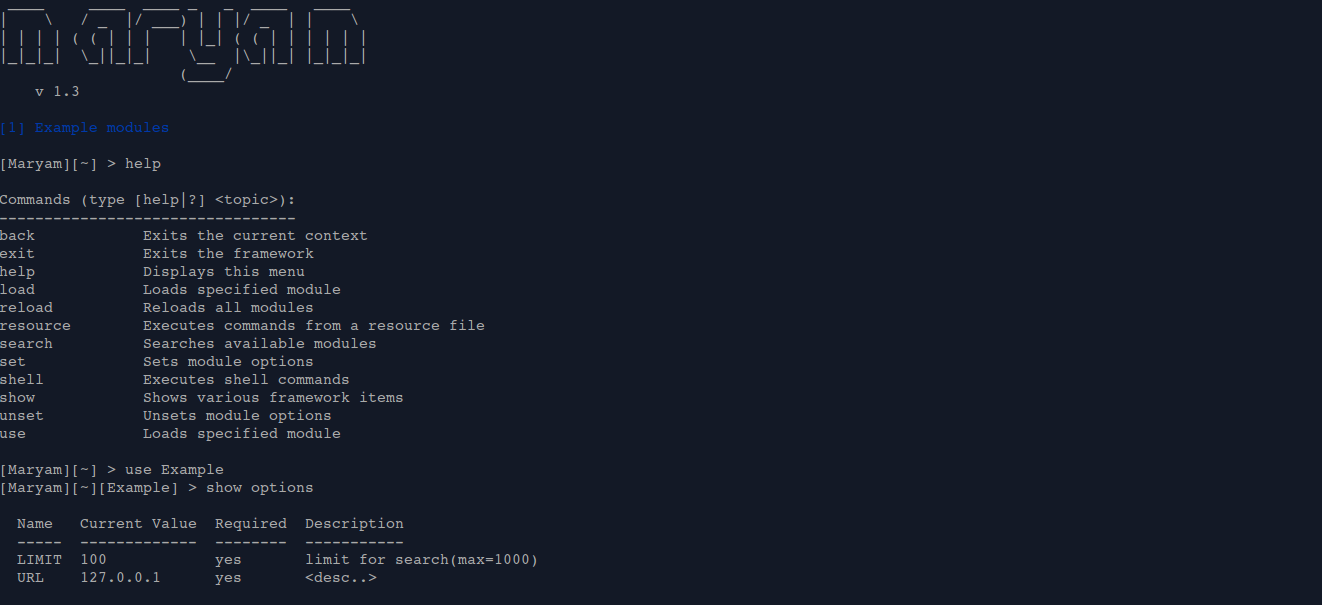
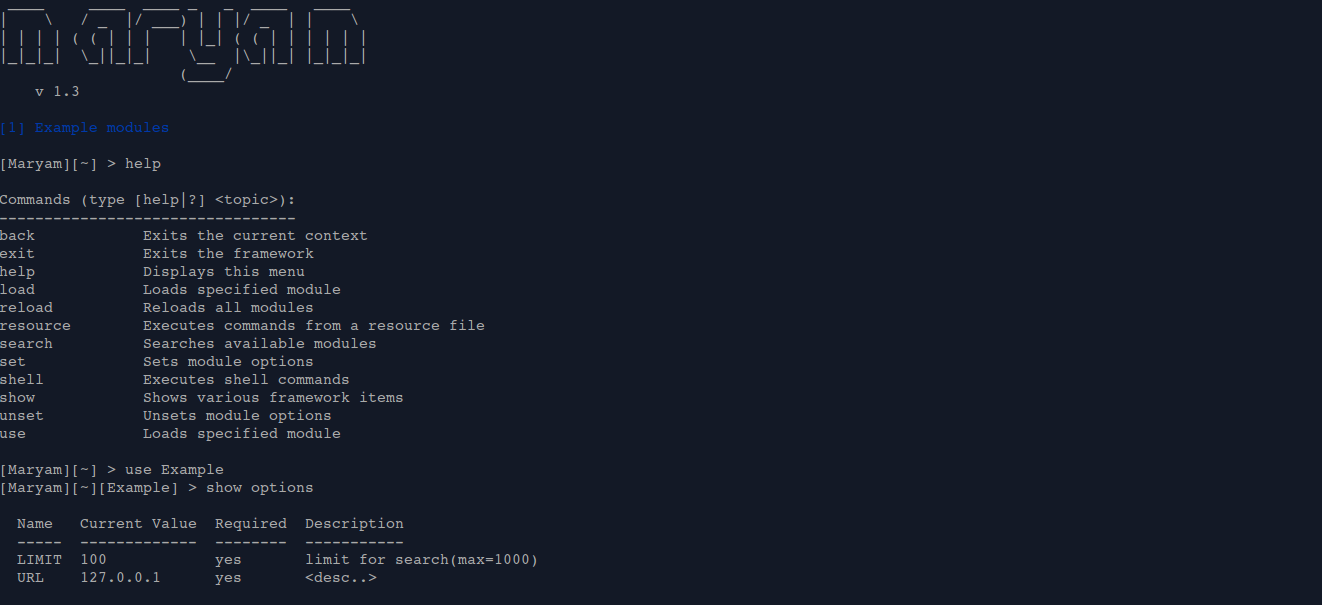
482Information GatheringMaryam – Open-source intelligence (OSINT) Framework
Maryam is a full-featured open-source intelligence (OSINT) framework written in Python. Complete with independent modules, built in functions, interactive help, and...
-
 689OSINT
689OSINTOWASP Maryam – Framework for Open-Source Intelligence
Maryam is a full-featured open-source intelligence(OSINT) framework written in Python. Complete with independent modules, built in functions, interactive help, and command completion,...
-
 309News
309NewsIntel Introduces ‘Springhill’ – Its First Artificial Intelligence Chip
At HotChips 2019, Intel was all about AI and one of the major announcements at the event was its first artificial intelligence...
-
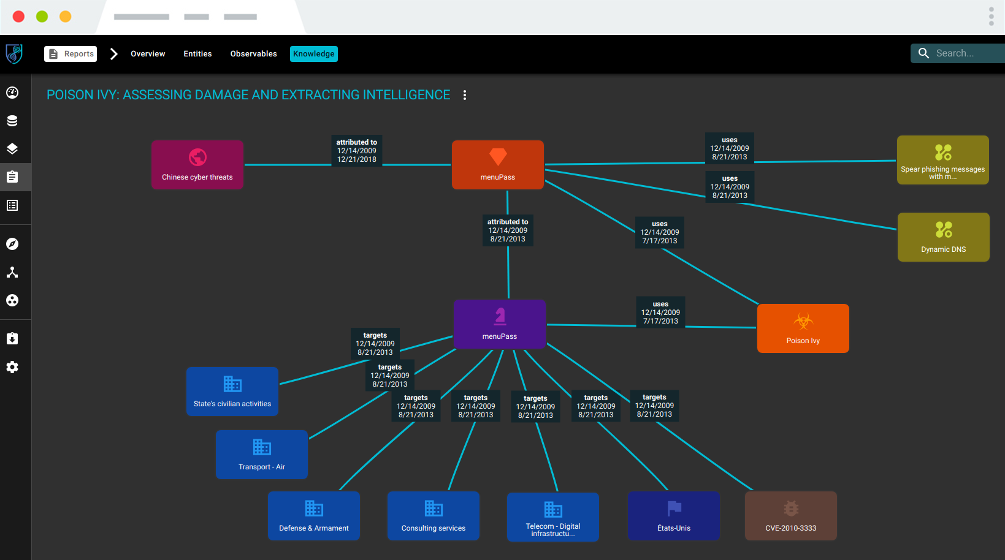
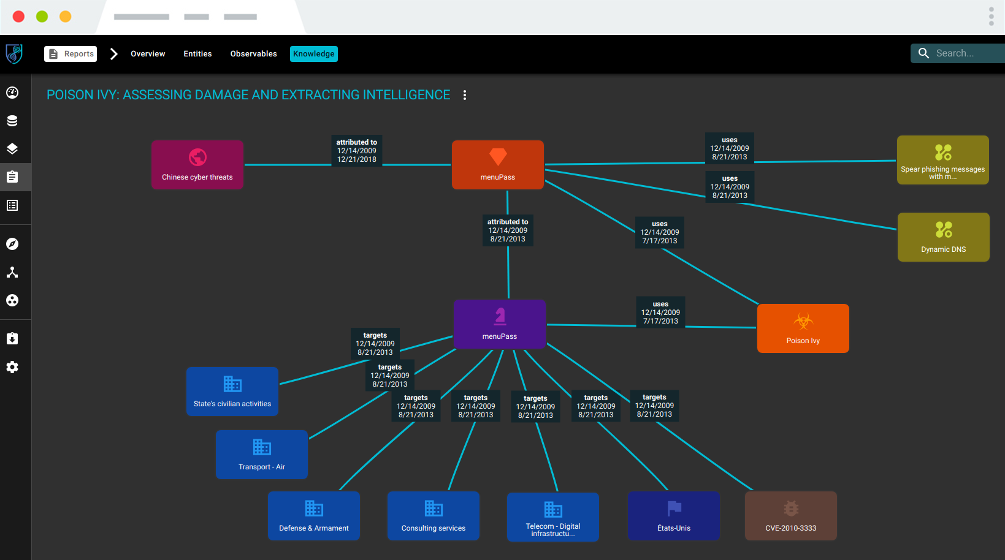 378Threat Intelligence
378Threat IntelligenceOpenCTI – Open Cyber Threat Intelligence Platform
OpenCTI is an open source platform allowing organizations to manage their cyber threat intelligence knowledge and observables. It has been created in...
-
 316News
316NewsHackers Stole 7.5TB Of Secret Data From Russia’s Intelligence Agency
It appears that the hackers got hacked this time! According to BBC Russia, hackers have managed to steal data from Russia’s Federal...
-

 215News
215NewsRussia’s Secret Intelligence Agency Hacked – 7.5 Terabytes of Data Extracted
Hackers compromised the Russian Federal Security Service (FSB) servers where they gained access to 7.5 terabytes of data from a major FSB...
-

 294Data Breach
294Data BreachRussia’s Secret Intelligence Agency Hacked – One of the Largest Hack in the Russian Secret Service History
Hackers compromised the Russian Federal Security Service (FSB) servers where they gained access to 7.5 terabytes of data from a major FSB contractor named...






