All posts tagged "backdoor"
-

 367Data Security
367Data SecurityLenovo removes backdoor present in networking switches since 2004
Engineers at Chinese firm Lenovo have identified a backdoor in the networking switched namely Rackswitch and BladeCenter firmware. The company stated that...
-
 330Geek
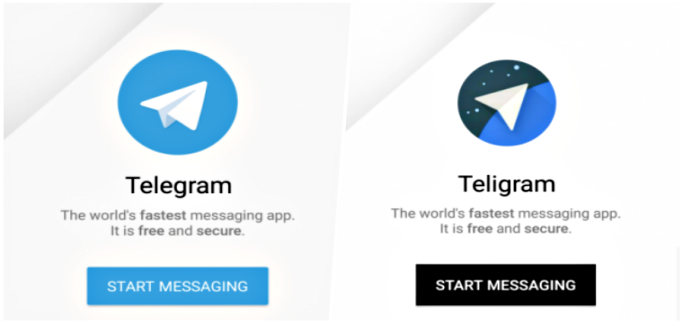
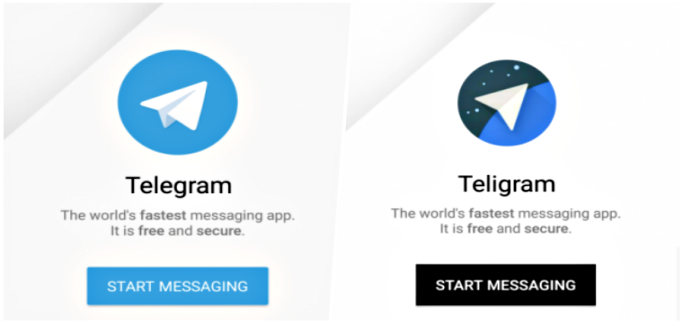
330GeekMalware infected fake Telegram Messenger app found in Play Store
The Google Play Store is home to more than 3.5 million apps but at the same time, there are tons of apps...
-

 229Malware
229MalwareESET research: Appearances are deceiving with Turla’s backdoor-laced Flash Player installer
ESET researchers have found that Turla, the notorious state-sponsored cyberespionage group, has added a fresh weapon to its arsenal that is being...
-

 410Hacked
410HackedHardcoded Backdoor Found In WD My Cloud NAS With Username “MyDlink”
In yet another revelation of severe loopholes, a security researcher James Bercegay from Gulftech has discovered a backdoor in some models of...
-
 301Data Security
301Data SecuritySoftware used in FBI’s biometric database contains Russian code: Report
The allegations that Russia hacked the 2016 elections in the United States are known to many but now biometric data of millions...
-

 294Data Security
294Data SecurityWordPress Captcha Plugin Contains Backdoor- 300,000 Websites at Risk
A warning has been issued by researchers disclosing the identification of a backdoor in yet another WordPress plugin called Captcha. This plugin...
-

 358Geek
358GeekAnother preinstalled app found on OnePlus that could collect user data
A couple of days ago it was reported that an IT security researcher Robert Baptiste who goes by the handle of Elliot Alderson on Twitter...
-

 289Geek
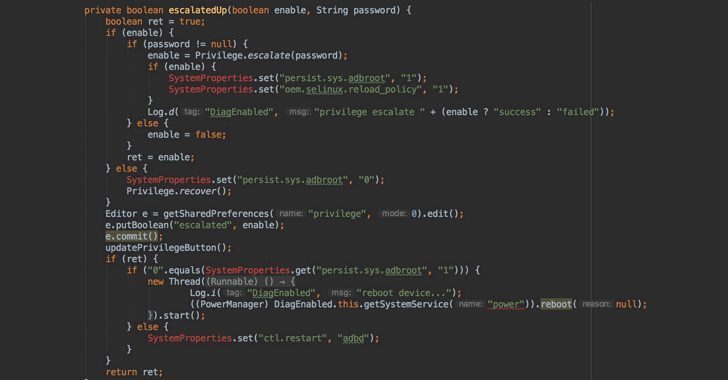
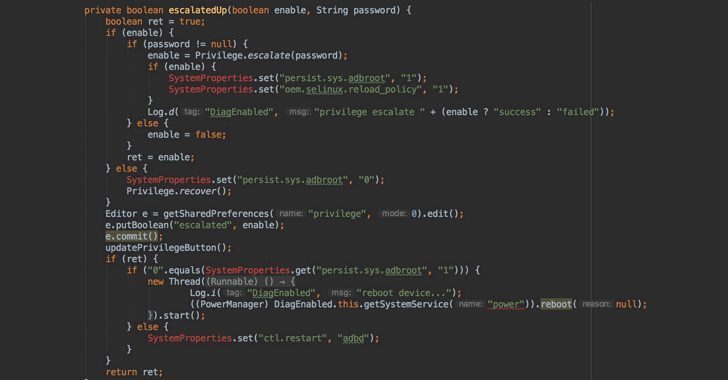
289GeekThere is a Pre-Installed Backdoor in OnePlus 5, 3 and 3T Devices
If you are using OnePlus 5, 3 or its 3T model, an IT security researcher Elliot Alderson (whose real name is Robert Baptiste) has bad...
-

 322Malware
322MalwareOnePlus includes Qualcomm engineering app in phones, exposes root backdoor
OnePlus says it’s “looking into” the report. A Twitter user by the name “Elliot Alderson” has discovered a root backdoor in OnePlus...
-
 177Articles
177ArticlesOnePlus Left A Backdoor That Allows Root Access Without Unlocking Bootloader
Just over a month after OnePlus was caught collecting personally identifiable information on its users, the Chinese smartphone company has been found...
-
 305Data Security
305Data SecurityIntel’ Management Engine Tech Just Got Exposed Through USB Ports
Back in September 2017, Positive Technologies’ experts had expressed interest in the development of a technique that can attack the yet secretive...
-

 148Malware
148MalwareHack the hackers. Watcha out the NEW IPCAM EXPLOIT, it is a scam!
Security experts have discovered a new hacking tool dubbed NEW IPCAM EXPLOIT containing a backdoor that is offered on several underground hacking...
-

 262News
262NewsVerticalScope hacked again; 2.7 million user accounts affected
In June 2016 we reported that the well-known Toronto, Canada-based Internet Media firm VerticalScope became a victim of a huge data breach,...
-

 331News
331NewsShips Are Vulnerable to Cyber Attacks Due To Maritime Platform Flaw
Previously it was reported that hackers can take over ships by exploiting critical vulnerabilities in VSAT communication system. Now, security consulting firm...
-
 1.7KHow To
1.7KHow ToHow To Create Backdoor In Kali Linux
What is backdoor? A backdoor is a method, often secret, to bypass normal authentication or encryption in an integrated computer system, product,...
-

 216Exploitation Tools
216Exploitation ToolsReptile – LKM Linux Rootkit
Reptile is a LKM rootkit for evil purposes. If you are searching stuff only for study purposes, see the demonstration codes. Features...
-

 328Data Security
328Data Security3 vulnerable WordPress plugins affecting 21,000 websites
21,000 Websites Affected after Exploiting of Three WordPress Plugins Zero-day – Solution: Update Those Plugins ASAP. Zero-day vulnerabilities are blessing for cybercriminals...
-
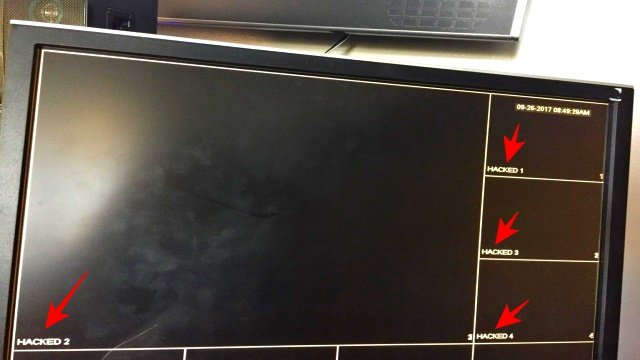
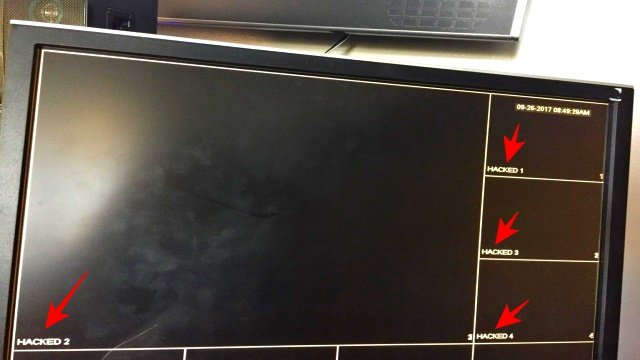 215News
215NewsHikvision Security Cams Compromised to Display “HACKED”
If you own Hikvision security cameras you would have noticed the sudden change in the live feed display where the normal footages...
-

 285Geek
285GeekCCleaner Malware: Here is the Full List of Affected Companies
Last week news came out that CCleaner software was infected with a backdoor. An initial investigation showed it was a state-sponsored attack. Now,...
-

 268Cyber Crime
268Cyber CrimeCCleaner Backdoor Attack: A State-sponsored Espionage Campaign
Infected CCleaner Software Attack that Affected 700,000 Customers is part of a Wide-scale State-sponsored Cyber-espionage Campaign. Previously we informed you about hacking...
-

 100Malware
100MalwareWhatsApp refused to add a backdoor for the UK government
The UK government has made no secret of its dislike of encrypted messaging tools, and it has made frequent reference to the...






