All posts tagged "backdoor"
-
 356Video Tutorials
356Video TutorialsHow to Generate a PHP Backdoor using Weevely – Kali Linux
Weevely is a web shell designed for post-exploitation purposes that can be extended over the network at runtime. Upload weevely PHP agent...
-
 359Video Tutorials
359Video TutorialsEvilOSX – Evil Remote Administration Tool (RAT) for macOS/OS X – Kali Linux 2018.2
Evil Remote Administration Tool (RAT) for macOS/OS X Features Emulate a terminal instance Simple extendable module system No bot dependencies (pure python) Undetected by...
-
 199Malware
199MalwareNecurs Botnet Malware Attack Create a FlawedAMMYY Backdoor on Compromised Windows PC
Necurs botnet malware emerging again with new set of futures to create a backdoor on victims machine to steal sensitive data and...
-
 285Malware
285MalwareIron Cybercrime Group Distributing New Powerful Backdoor with Strong Evasion Techniques
Newly discovered powerful & previously unknown backdoor using HackingTeam’s leaked Remote Control System (RCS) code to infect the thousands of victim around...
-

 318Data Security
318Data SecurityMalicious Chrome & Edge extension drops backdoor and spy on users
Trend Micro researchers have identified malicious Google Chrome and Microsoft Edge browser extension that is distributing backdoor to steal information from the...
-
 245Cryptocurrency
245CryptocurrencyMalicious Chrome and Edge Browser Extension Deliver Powerful Backdoor & RAT to Spy Victims PC
A malicious Chrome and Edge Browser Extension delivers powerful backdoor to stealing information from the browsers and monitor the victim’s activities. A downloader...
-
 270Malware
270MalwareTurla Mosquito Hacking Group Exploiting Backdoor Using Metasploit To Compromise the Target System
Turla cyber espionage group leveraging Powerful Mosquito backdoor using open source exploitation framework Metasploit for an initial stage of the attack on the target...
-
 297Malware
297MalwareResearchers Found Backdoor in Python Library That Steal SSH Credentials
Recently we saw an attempt to hide a back door in a code library, and today there is a new case. This...
-

 316Video Tutorials
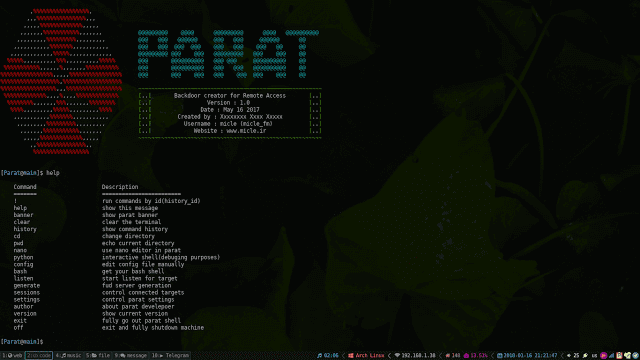
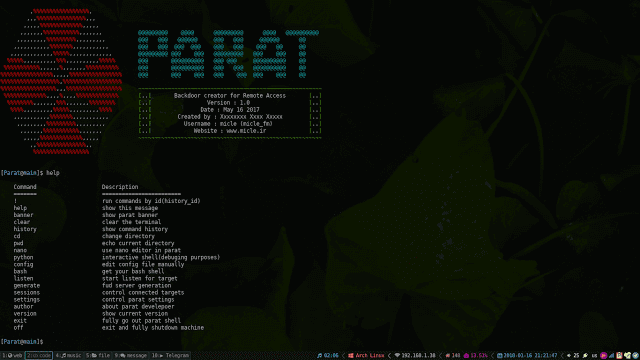
316Video TutorialsParat – Undetectable Python Payloads – Remote Administration Tool – Kali Linux 2018.1
Parat is a simple remote administration tool(RAT) written in python. Features Fully UnDetectable(FUD) Compatible with Telegram messanger Bypass windows User Account Control(UAC)...
-

 346Data Security
346Data SecurityNew macOS malware aims at infecting devices with malicious macros
The general perception about Apple devices is that they are protected from malware attacks by default which is not true at all...
-

 223Malware
223MalwarePowershell-RAT backdoor that uses Gmail to exfiltrate data
Python based backdoor that uses Gmail to exfiltrate data as an e-mail attachment. This RAT will help someone during red team engagements...
-

 356Hacked
356Hacked“Backdoor” Found In AMD CPUs, Researchers Discover 13 Critical Vulnerabilities In RYZEN And EPYC
CTS Labs’ researchers have warned that if you’re running an AMD Ryzen, Ryzen Pro, Ryzen Mobile or EPYC processor on your computer...
-

 316Video Tutorials
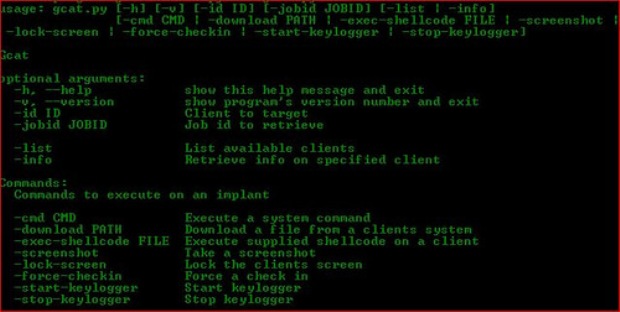
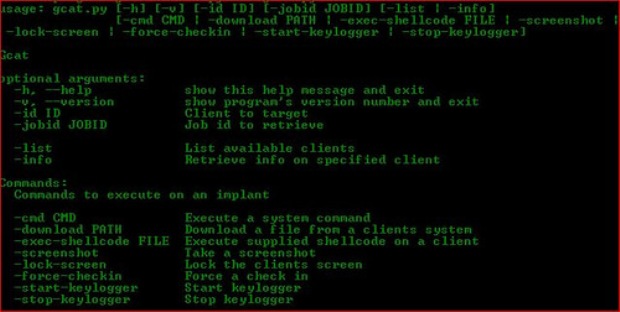
316Video TutorialsFully Undetected Backdoor with RSA Encrypted Shell using TopHat – Kali Linux 2018.1
TopHat is inspired by metasploit’s capabilties of meterpreter however it was coded to generate a undetected encrypted backdoor using python. Usage: python...
-
 281Exploitation Tools
281Exploitation ToolsParat – Python Based Remote Administration Tool (RAT)
Parat is a simple remote administration tool (RAT) written in python. Also you can read wiki! Change log: Compatible with both python...
-

 174Malware
174MalwareRaw sockets backdoor gives attackers complete control of some Linux servers
“Chaos” gives attackers, and follow-on attackers, full control over infected boxes. A stealthy backdoor undetected by antimalware providers is giving unknown attackers complete...
-
 413Video Tutorials
413Video TutorialsHow to Find Vulnerable Webcams Across the Globe Using Shodan and Google – Kali Linux 2018.1
Shodan is a search engine that lets the user find specific types of computers (webcams, routers, servers, etc.) connected to the internet...
-

 322Data Security
322Data SecurityNew IoT Botnet DoubleDoor Bypass Firewall to Drop Backdoor
A new Internet of Things (IoT) botnet campaign dubbed as DoubleDoor has been discovered by NewSky Security, which uses two exploits for...
-

 292Data Security
292Data SecurityFlaw in Telegram Windows App Used for Cryptomining & Backdoor
Another day, another popular app compromised to drop backdoor and conduct cryptomining. Telegram Messenger’s critical zero-day flaw that according to Kaspersky Labs researchers...
-
 210Exploitation Tools
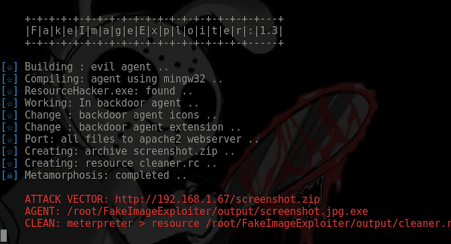
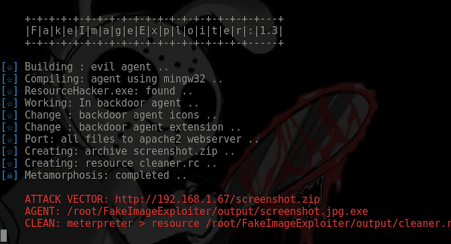
210Exploitation ToolsFakeImageExploiter – Use a Fake image.jpg (hide known file extensions) to exploit targets
This module takes one existing image.jpg and one payload.ps1 (input by user) and builds a new payload (agent.jpg.exe) that if executed it...
-

 234Data Security
234Data SecurityAttackers can Bypass Fingerprint Authentication in Lenovo devices
Vulnerability in Lenovo Devices Allows Attacker to Bypass Fingerprint Authentication and Gain Higher Privileges. In case you own a ThinkCentre, ThinkPad or...
-
 255Data Security
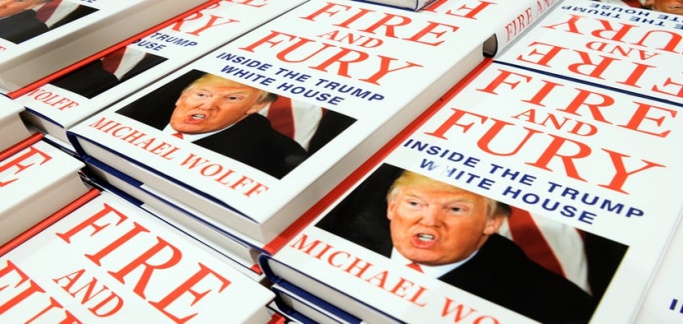
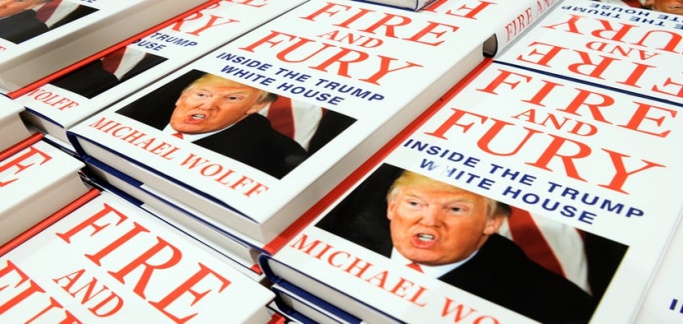
255Data SecurityPirated Version of Fire and Fury Book Loaded with Malware
Another day, another malware scam – This time, the pirated version of Fire and Fury book has been found infecting devices with...






