All posts tagged "IP address"
-

 4.8KSurveillance
4.8KSurveillanceProtonMail logged, shared activist’s IP address with Swiss police
ProtonMail is being criticized for sharing French activist’s IP address with Swiss authorities while claiming it does not save logs. End-to-end encrypted...
-

 593Data Security
593Data SecurityWhy a VPN is Compulsory for Torrent Users
The boundaries of VPN use cases are continuously expanding. Today, VPNs are heavily used by fans of torrent trackers. A hidden IP...
-

 2.3KPrivacy
2.3KPrivacyThe Five Incident Response Steps
It is important to remember that implementing incident response steps is a process and not an isolated event. For a truly successful...
-

 509Geek
509GeekTop 10 VPN Services For 2019
VPN is a billion dollar industry and lately, it has become a vital part of users conscious about their online privacy – Here are the...
-

 304Data Security
304Data SecurityIs Flawless Anonymity Possible?
The condition of being anonymous is called anonymity – Let’s suppose you want to post the most anonymous comment on a social...
-

 294News
294NewsWhat If Your VPN Keeps Logs and Why You Should Care
Have you ever asked yourself the question: “So what if my VPN keeps logs?” Don’t worry. It’s a good question to ask....
-

 385Data Security
385Data SecurityIP Protection in 2019: Cope with Weak Points
Before we investigate familiar techniques of hiding an IP address, a person is to know what his or her IP is. Besides,...
-
 247Data Security
247Data SecurityStart hacking with browser extension
Pentester always uses various tools to gather information of the target. And it is most crucial part before creating any further scenarios....
-
 353Tutorials
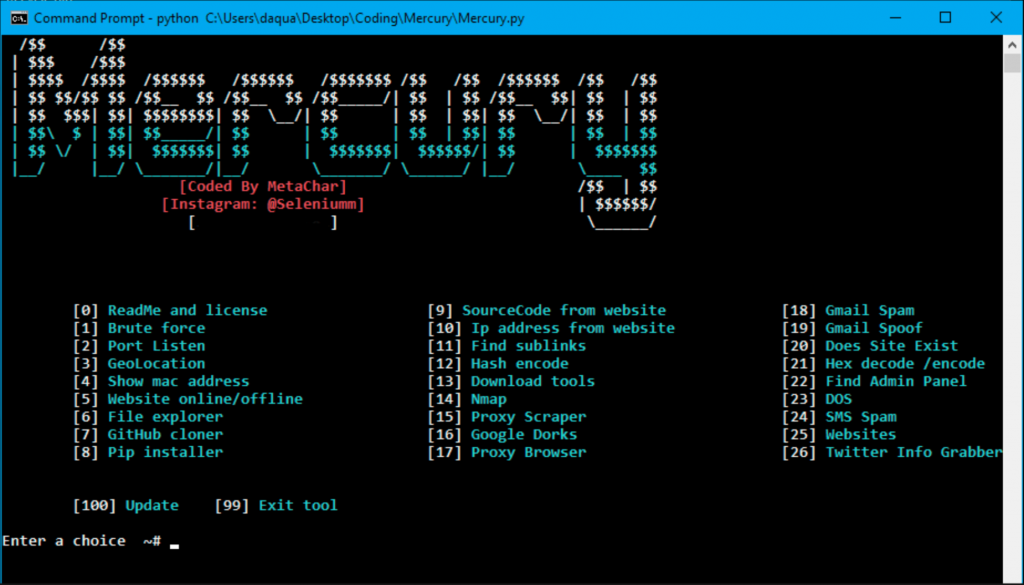
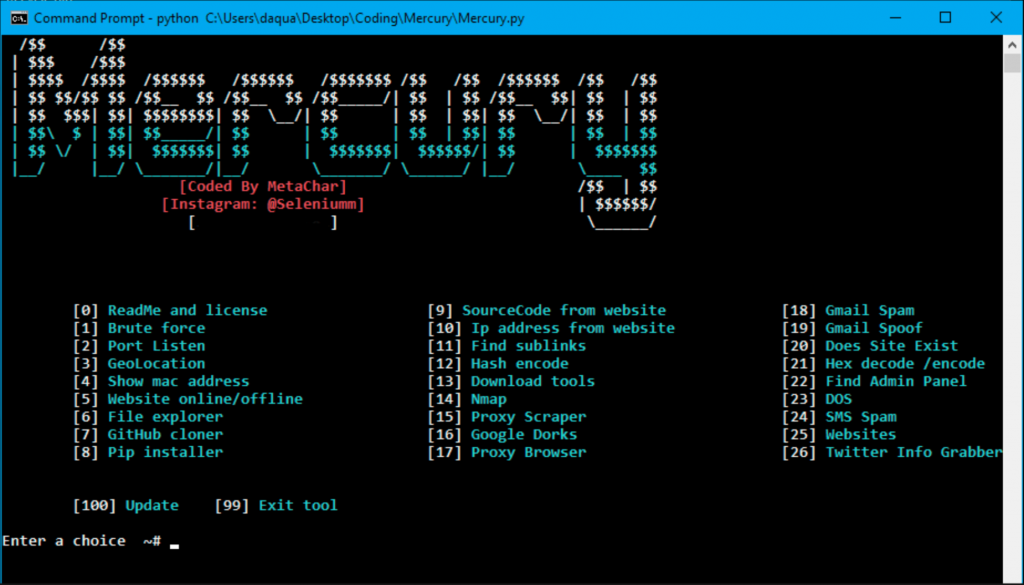
353TutorialsHack any website with All in One Tool
Internet is the hub of web applications. Many past developers has made numerous web applications to use internet more effectively. Internet has...
-
 301Exploitation Tools
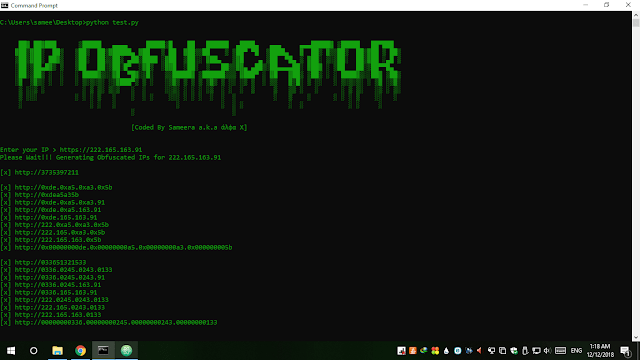
301Exploitation ToolsIP Obfuscator – Simple Tool To Convert An IP Into Integer, Hexadecimal Or Octal Form
IP Obfuscator is a simple tool written in python to convert an IP into different obfuscated forms. This tool will help you...
-

 319Vulnerabilities
319VulnerabilitiesTelegram vulnerability causes IP address leaking
A security investigator discovered the flaw Dhiraj Mishra, researcher on cybersecurity and ethical hacking discovered a default configuration in Telegram that could expose the IP address of...
-
 419News
419NewsTelegram leaked IP addresses of its desktop app users
The vulnerability affected Telegram’s desktop app for Windows, Mac, and Linux OS. Telegram, a popular privacy-focused instant messaging application, reportedly contained a...
-

 268Mobile Security
268Mobile SecurityWiFi Broadcasts in All Version of Android OS Leaking Sensitive Data Including IP Addresses, BSSID, WiFi Network Name
WiFi Broadcasts in Android OS Leaking sensitive data from a user’s Android device and the details about all the application that running...
-
 260Vulnerabilities
260VulnerabilitiesCritical Tor flaw leaks users’ real IP address—update now
TorMoil threatens Mac and Linux versions of Tor browser; Windows and Tails not affected. Mac and Linux versions of the Tor anonymity...
-

 453Hacked
453HackedHow To Download Torrents Anonymously And Hide Your IP Address?
Short Bytes: BitTorrent is an easy method of sharing and downloading the content of our choice. But, the increase in illegal downloads...
-

 257Incidents
257IncidentsHow do hackers hide their IP address?
How do hackers hide their IP address from prying eyes. Hackers are known for breaking into most impregnable web servers around the...
-

 273How To
273How ToWhat To Do If A Particular Website Is Not Opening On The Internet?
Short Bytes: There can be many reasons why you aren’t able to access a particular website on the internet. These include the...
-
 241Hacked
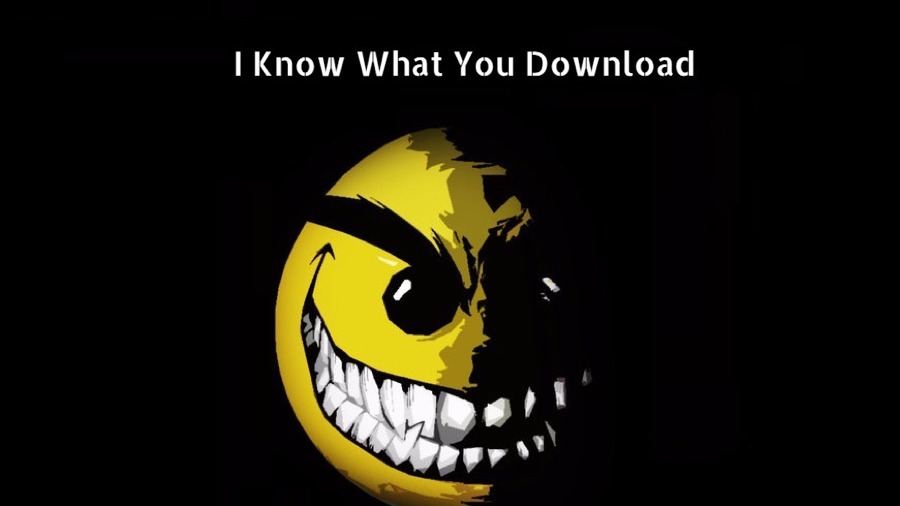
241HackedThis Website Claims To Have The List Of Every Torrent You Have Downloaded In Your Life
Short Bytes: If you’re a regular torrent downloader, you should know that your torrent download history is publically available on the website...
-

 245Hacking Tutorials
245Hacking TutorialsBypass Internet Censorship
Internet censorship is the control or suppression of what can be accessed, published, or viewed on the Internet. It may be carried...
-
 307Hacking Tutorials
307Hacking TutorialsHow to hack a Hotel’s Wifi
Firstly, i would ask you whether or not you have had this situation before? Where for instance ,your phone is connected to...
-

 355Information Gathering
355Information GatheringSniffing someone’s IP from Steam
Here’s a tutorial on finding someone’s IP on Steam the easy way. Step 1: Downloading the programs CommView: Download below...






