Featured News
-
 268Cyber Events
268Cyber EventsAnonymous stands true to its words, leaks more data on alleged KKK members
The online hacktivist Anonymous released what they called a list of Ku Klux Klan members and sympathizers on Thursday. As reported earlier, the Anonymous...
-

 338Data Security
338Data SecuritySDK Security Flaw Puts 100 Million Android Users Vulnerable to Backdoor Attack
A software development kit that has been provided by Baidu (A Chinese search engine) can easily be exploited for installing backdoors on...
-

 164Data Security
164Data SecurityLinux Servers to Blame for 45 Percent of All DDoS Attacks in the Past 3 Months
Cyber-security vendors are revealing their statistics for the third quarter (Q3) of 2015, and a popular topic is DDoS attacks, a tactic...
-

 185Data Security
185Data SecurityUK cyber-spy law takes Snowden’s revelations of mass surveillance – and sets them in stone
IPB The encryption bothering parts of the UK’s Investigatory Powers Bill have left IT security experts flabbergasted. Introducing the draft internet surveillance...
-
 427How To
427How ToTop 10 Coolest Notepad Tricks and Hacks for Your PC
Short Bytes: The humble Notepad of your laptop goes unappreciated many times. This little tool is capable of doing some amazing tricks...
-

 328Data Security
328Data SecurityTeen Hackers Who Doxed CIA Chief Are Targeting More Government Officials
A cybersecurity expert once told me something I’ll never forget: “don’t underestimate what bored teenagers can do.” A group teenagers that call...
-

 97Cyber Crime
97Cyber CrimeUK and US banks to face transatlantic cyberattack test
Banks in the UK and US will be tested on how capable they are in coordinating a transatlantic response to a cyberattack.
-

 370How To
370How ToWhat is DNS (Domain Name System) and How it Works ?
What is the definition of DNS? DNS, which stands for Domain Name System, is used as the medium to translate domain names...
-

 109Data Security
109Data SecurityRussian Banks Under Attack from Tinba Banking Botnet
Customers of Russia’s biggest banks are under attack.Dell SecureWorks has detected an ongoing campaign that is targeting users of several Russian banks...
-

 250Malware
250MalwareNew type of auto-rooting Android adware is nearly impossible to remove
20,000 samples found impersonating apps from Twitter, Facebook, and others. Researchers have uncovered a new type of Android adware that’s virtually impossible...
-

 314Hacked
314HackedMan Hires “Hacker” to Erase $16,000 Fine, Actually Hires Undercover Cop and Goes to Prison
Short Bytes: What is the worst thing that could happen when you hire a hacker to conduct some criminal activity? Yes, police...
-

 82Malware
82MalwareSchrödinger’s antivirus: The immortality of antivirus software
The question of antivirus software being dead is one that doesn't seem to go away. Why is that? Distinguished ESET researcher Aryeh...
-

 192Data Security
192Data SecurityStuxnet-style code signing of malware becomes darknet cottage industry
Even reports of crims offering signing-as-a-service. Underground cybercrooks are selling digital certificates that allow code signing of malicious instructions, creating a lucrative...
-
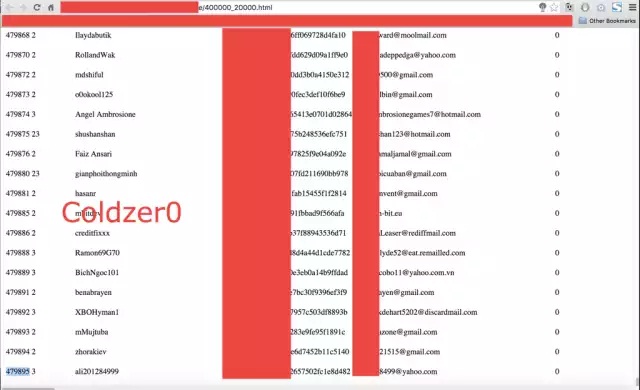
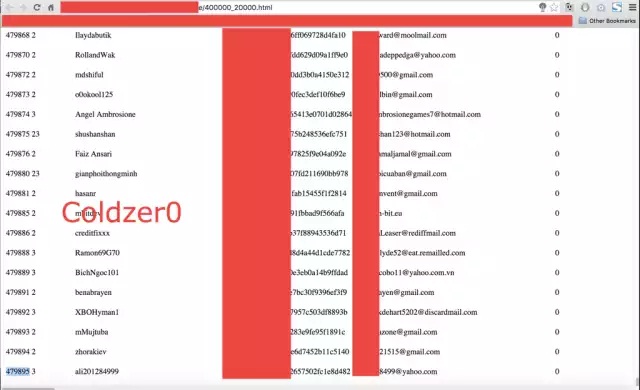
 237Data Security
237Data SecurityReturn of the EXIF PHP Joomla Backdoor
Our Remediation and Research teams are in constant communication and collaboration. It’s how we stay ahead of the latest threats, but it...
-

 174Vulnerabilities
174VulnerabilitiesGoogle Project Zero Turns Over 11 Bugs in Galaxy S6 Edge
Google’s Nexus Android devices are considered the most secure by default since they’re guaranteed to receive all security patches for vulnerabilities found...
-

 214Data Security
214Data SecuritySecurity Researcher Creates Tool to Extract Passwords from KeePass Databases
Denis Andzakovic, a security researcher for Security Assessment, has created a tool that can fool the KeePass password manager into exporting its...
-
 270Vulnerabilities
270VulnerabilitiesvBulletin password hack fuels fears of serious Internet-wide 0-day attacks
Software maker issued security patch hours after reports surfaced it was breached. Developers of the vBulletin software package for website forums released...
-

 74Cyber Crime
74Cyber CrimeUS man jailed for attempting to hire cybercriminal to wipe fines
A US man who posted an advert on Craigslist requesting the services of a cybercriminal has been handed a two-year prison sentence....
-

 429Cyber Crime
429Cyber CrimeGermany’s Industrie 4.0 – the challenges in IT‑Security
Time after time we have experienced revolutions in our societies, in the way we work and thus in the Industry. In the...
-

 252Hacked
252HackedKim Dotcom Is Building His Own Private Internet Called Meganet
Short Bytes: Kim Dotcom, the founder of notorious file-sharing website Megaupload, has said that he is working on an internet alternative called...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




