Featured News
-
 151Data Security
151Data SecurityFBI: We unmasked and collared child porn creep on Tor with spy tool
Dark-web deadbeats may not be as anonymous as they think. A bloke in the US was charged on Friday after FBI spyware...
-
 305Geek
305GeekLearn to Code Windows 10 Apps: Microsoft’s Free Course for Beginners
Short Bytes: Microsoft has launched a free course to teach you how to code Windows 10 Universal Apps using C#. Take a...
-

 105Data Security
105Data SecurityCyber-Criminals Throw Molotov Cocktails at Dr.Web Antivirus Headquarters After Being Exposed
Cyber-crime syndicate tried to intimidate antivirus vendor. In some cases, cyber-security work can turn really dangerous, and even deadly, if you manage to...
-

 188Hacked
188HackedTesla Model X Has A Crazy Bio-weapon Defence Mode Button
Short Bytes: New Tesla Model X has a bio-weapon defense air mode that will give you a hospital level air quality inside...
-

 173Vulnerabilities
173VulnerabilitiesApple Gatekeeper Bypass Opens Door for Malicious Code
Gatekeeper is Mac OS X’s guardian against rogue applications and malware sneaking into Apple’s famous walled garden. It’s also been a favorite...
-

 333News
333NewsDonald Trump Hotels Data Breach Incident Confirmed
In a previous article, we brought you news of Trump Hotels being breached by hackers. To update, we can now report that...
-

 348Geek
348GeekHow to Protect Your Wi-Fi Router From Hacking Using Simple Tricks
Short Bytes: The humble wireless router in your home, as you might not think, could be the biggest loophole in your personal...
-

 117Geek
117GeekDon’t Fall for Stupid Scam, Facebook Won’t Charge You any Privacy Fee
Last week, news spread across the web (appearing in newsfeeds of many users) that Facebook is about to assign a fee for...
-
 166Hacked
166HackedWinRAR Exposed to Dangerous Vulnerability: Attack Just by Unzipping Files
Short Bytes: The latest WinRAR SFX v5.21 update has a serious vulnerability that allows remote attackers to execute any malicious code on your...
-

 177Vulnerabilities
177VulnerabilitiesMicrosoft Exchange Server Fixed Against Information Disclosure Bug
Vulnerability allowed hackers to hijack active user sessions.Microsoft Exchange Server has been recently patched to fix an important security vulnerability which would...
-

 204Data Security
204Data SecurityXOR DDoS Attack Tool Being Used to Launch Over 20 Daily Attacks
Threat actors are using a previously discovered distributed denial-of-service (DDoS) attack tool dubbed XOR DDoS to launch upwards of 20 DoS attacks...
-

 285Hacked
285HackedThis New Linux Trojan Launches Deadly DDoS Attacks at 150+ Gpbs
Short Bytes: As more and more Linux systems are going online, the threat to the once-secure Linux systems is increasing. In a...
-

 301Geek
301GeekEdward Snowden Joins Twitter, Stays Classy, Follows the NSA
The NSA whistleblower Edward Snowden has finally joined Twitter and within a few hours he has earned a verified badge along with...
-

 161Vulnerabilities
161VulnerabilitiesSAP Patches 12 SQL Injection, XSS Vulnerabilities in HANA
SAP patched a dozen holes in its in-memory management system, HANA, that could have led to SQL injection attacks, cross-site scripting (XSS)...
-

 98Kids Online
98Kids OnlineUK parents ‘want minimum age for smartphone ownership’
A survey has found that most parents in the UK are keen to see a minimum age introduced for smartphone ownership.
-

 222News
222NewsIntended crucifixion of Ali Mohammed al-Nimr Compels Anonymous to Target Saudi Websites
Saudi Arabia’s Government’s decision to crucify Mohammed al-Nimr has prompted a strong response from the Hacktivist group Anonymous when various significant Saudi government websites were hacked...
-

 214Hacked
214HackedBlackphone 2 Could Be the Most Secure Android Phone Ever, And It’s Now On Sale
Short Bytes: To address your privacy concerns, Silent Circle has tried to create the super-secure Android phone and its newest model Blackphone...
-
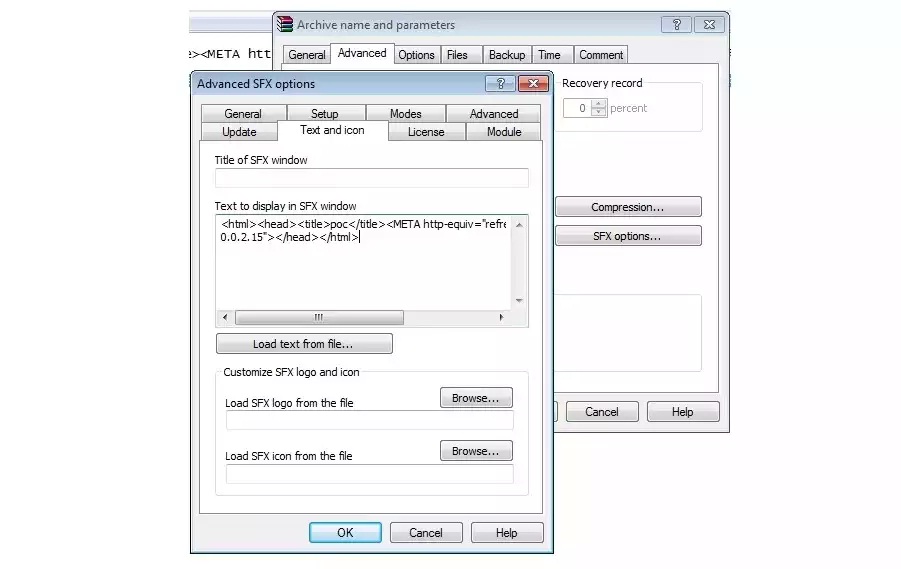
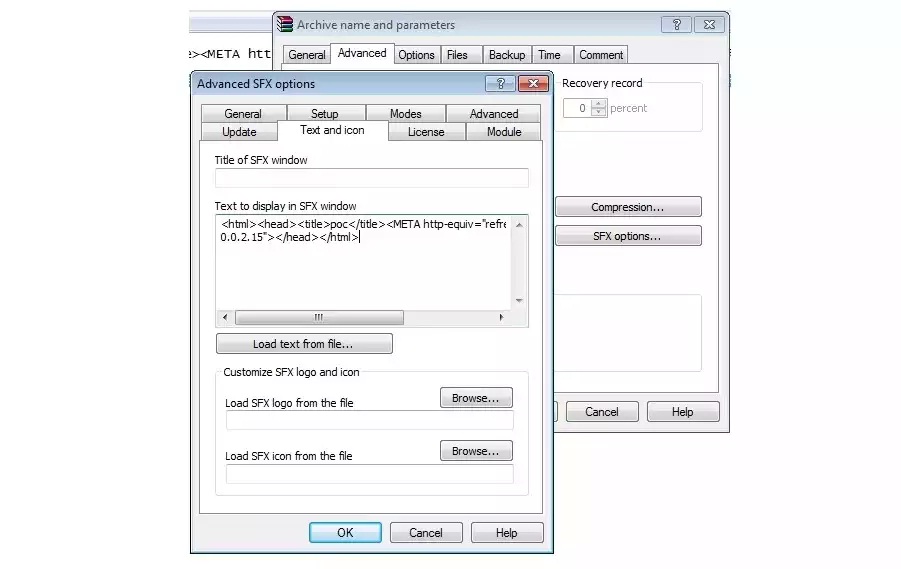 250Vulnerabilities
250VulnerabilitiesLatest Version of WinRAR Plagued by Dangerous Security Bug
WinRAR, the popular file compression and decompression utility, has a security vulnerability that allows attackers to remotely execute code on the user’s...
-

 289Geek
289GeekWindows Registry now Providing Shelter to Destructive Kovter Malware
Kovter Trojan can hide in Windows registry and does not need to be stored on the computer’s hard drive- claims Symantec —...
-

 98Malware
98MalwareDyreza Trojan Targeting IT Supply Chain Credentials
The Dyreza Trojan long ago ceased its exclusive focus on stealing banking credentials, and has been blamed for its part in attacks...
The Latest
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareMalicious Google Ads Pushing Fake IP Scanner Software with Hidden Backdoor
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesGenAI: A New Headache for SaaS Security Teams




