Featured News
-
 73Malware
73MalwareAggressive Android ransomware spreading in the USA
The latest ESET discovery of the first known Android lock-screen-type ransomware that spreads in the wild and sets the phone's PIN lock...
-

 154Hacked
154HackedThis Fake Baby Car Seat is Made to Help Governments Spy on You
Short Bytes: A recent report from the Privacy International reveals a fake baby car sear that is being used by the Columbian...
-

 187Data Security
187Data SecurityOnce seen as bulletproof, 11 million+ Ashley Madison passwords already cracked
Programming errors make 15.26 million accounts orders of magnitude faster to crack. When the Ashley Madison hackers leaked close to 100 gigabytes...
-

 168Vulnerabilities
168VulnerabilitiesAndroid Stagefright Exploit Code Released to Public
Joshua Drake, the researcher who found the so-called Stagefright vulnerability in Android, today released exploit code to the public, which he hopes...
-
 259Incidents
259IncidentsDD4BC Hacker Group Blackmails Companies for Bitcoin Using DDOS Attacks
A group of hackers that goes under the name of DD4BC, first spotted in September 2014, has recently intensified its activity, launching...
-

 197Data Security
197Data SecurityTurla APT Group Abusing Satellite Internet Links
Poorly secured satellite-based Internet links are being abused by nation-state hackers, most notably by the Turla APT group, to hide command-and-control operations,...
-

 207Geek
207GeekMugShot Program Provides You Picture of Culprit Trying to Hack You
If you feel continually threatened by hackers then this program will help in tracking the culprit and definitely offer you some relief. You...
-

 267Geek
267GeekLearn it Faster: The Entire JavaScript Language in a Single Image
Short Bytes: A developer named Yusheng has created an amazing infographic that shows the entire JavaScript language syntax into one single image. Take...
-

 244Hacked
244HackedMicrosoft Is Fighting the US Government to Protect YOUR Data. Surprised?
Short Bytes: Microsoft is heading to the court to battle the U.S. Department of Justice to protect a user’s data stored in the...
-

 189Data Security
189Data SecurityPolice develop MAC-sniffing software to track stolen devices
The L8NT could help law enforcement track and find Wi-Fi enabled gadgets. On Tuesday, local media reported that David Schwindt, a 14-year...
-

 372Data Security
372Data SecuritySecurity Flaw in Millions of Websites Leave Users Vulnerable to Ransomware
Potential Security Flaw In Obsolete CMS and Plugins Left Millions of Users Vulnerable To Ransomware. More than 142 million websites have been...
-

 293Geek
293GeekSecurity Tips by the Expert: How Linux Foundation Protects its Computers
Short Bytes: Today, we’ve brought some security tips from the Linux Creators. Read the article that describes The Linux Foundation recommendations for...
-

 259Malware
259MalwareAndroid Malware Secretly Subscribes Victims to Premium SMS Services
The Android.Trojan.MKero.A malware is making a comeback in Androidland, and this time around, hackers found a method to bundle it with legitimate...
-

 110Vulnerabilities
110VulnerabilitiesiOS 8.4.1 Kernel Vulnerabilities in AppleHDQGasGaugeControl
When auditing iOS kernel executable, we found that the code quality ofcom.apple.driver.AppleHDQGasGaugeControl is very bad. In this blog, we will disclose 3...
-

 153Vulnerabilities
153VulnerabilitiesMicrosoft Patches Graphics Component Flaw Under Attack
Microsoft today patched a vulnerability in its graphics component present in Windows, Office and Lync that has been publicly attacked, and is...
-

 174Malware
174MalwareCyberespionage group caught borrowing banking malware code
Russia’s Pawn Storm group uses a malware dropper based on the leaked Carberp source code. A group of hackers that target military...
-

 299Geek
299GeekDude exposes Windows 10 Spying tactics in a beautiful song
A YouTube user ‘Sir.O’ wants you to understand clearly what the Microsoft Service Agreement’s Section 7B tries to convey.. and he did...
-

 206Geek
206GeekAndroid Ransomware Hidden Behind Fake Pornography App
Android is one of the most vulnerable OS in the world — If you are an Android user you need to be...
-
 313News
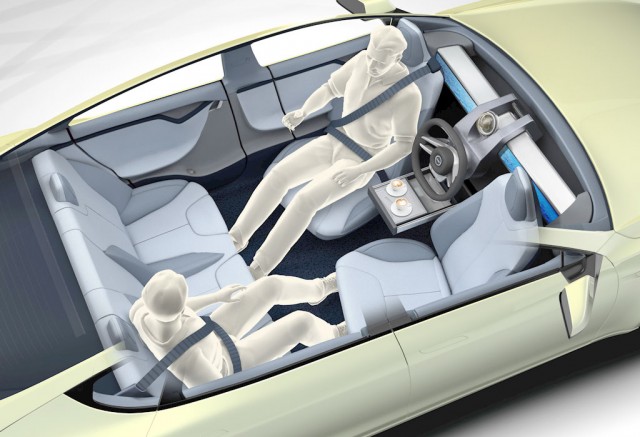
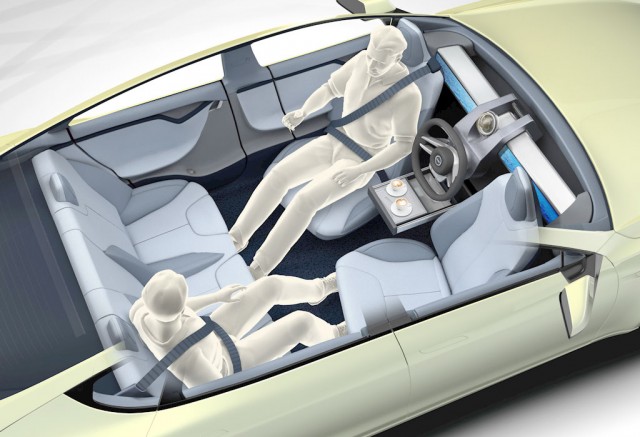
313NewsDriverless Cars Can Be Hacked by Compromising 3D Imaging System
The laser navigation system and sensors of driverless cars can be easily exploited by hackers as they can trick them into getting...
-

 124Vulnerabilities
124VulnerabilitiesWhatsApp “MaliciousCard” Vulnerabilities Allowed Attackers to Compromise Hundreds of Millions of WhatsApp Users
WhatsApp Web is a web-based extension of the WhatsApp application on your phone. The web application mirrors all messages sent and received,...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




