Featured News
-

 113Incidents
113IncidentsWebsite hackers hijack Google webmaster tools to prolong infections
Webmasters should regularly check the list of verified owners for their websites in the Google Search Console. Hackers who compromise websites are...
-

 227Vulnerabilities
227VulnerabilitiesResearchers Outline Vulnerabilities in Yahoo, PayPal, Magento Apps
Researchers recently discovered a smattering of vulnerabilities in web applications and mobile applications belonging to companies like Yahoo, PayPal, Magento, and Shopify that...
-

 102Malware
102MalwareCoreBot malware evolves overnight into virulent banking Trojan
It didn’t take long for hackers to take advantage of the malware’s bolt-on structure and transform it into something dangerous. The modular...
-

 206News
206NewsAndroid Users Beware: Verified Apps on Play Store can Spread MKero malware
If you think that all the Android apps currently available on the legitimate Google Play Store are reliable and free-of-malware, then you...
-

 279Geek
279GeekFlying a Drone via JavaScript and Bluetooth in Your Browser
Short Bytes: Mozilla and Google are actively working to combine the Physical Web and WebBluetooth. Using a new Bluetooth API, Mozilla developers...
-

 88Geek
88GeekWindows 10 Spying Controversy—Canadian Authorities Start Investigation
Windows 10 comes with some hard to believe terms and conditions which openly announces how the OS will spy on its users...
-

 240Cyber Events
240Cyber EventsPakistan Government Bans Online Political Forum Siasat.pk
If you want to silence someone’s voice; welcome to Pakistan where the government puts a ban on platforms like YouTube, Pastebin or...
-

 223Hacked
223HackedThe Dark Web is No More “Dark”, .Onion Websites Get Official Recognition
Short Bytes: The Dark Web sites running with .onion domain are now much safer to visit. Now, .onion has got a Special...
-

 348Lists
348Lists12 Surprising Facts About Google That You Don’t Know
Short Bytes: For most of the people, Google has become the definition of Internet. It has been more than 15 years since...
-
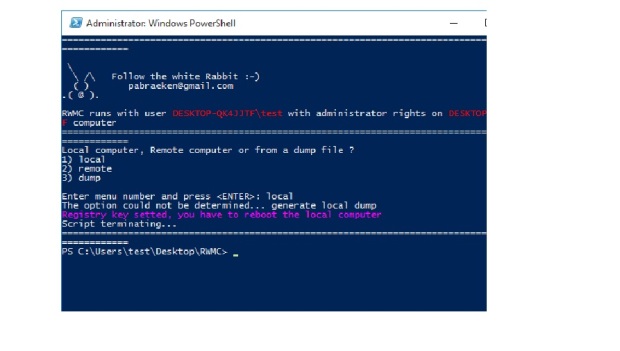
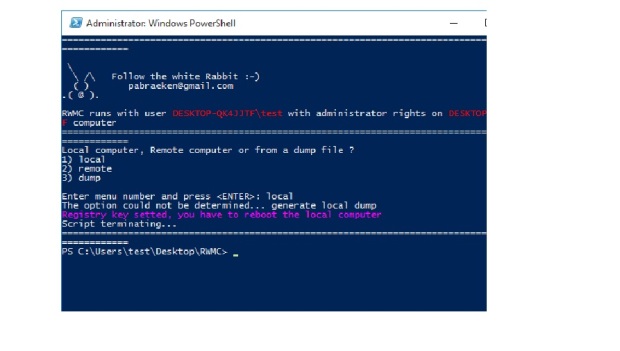 138Data Security
138Data SecurityExtracting Hashes & Plaintext Passwords from Windows 10
Windows 10 is here. Well… it’s sort of been here for some time, but it’s fully rolled out now and soon we...
-

 165Incidents
165IncidentsUS Department of Energy Hacked 159 Times in 4 Years
Between 2010 and 2014, the US Department of Energy (DoE) was attacked by unknown parties 159 times, as USA Today is reporting...
-

 189Data Security
189Data Security3D printer blueprints for TSA luggage-unlocking master keys leak online
That padlock on your bag? Easy to open by anyone now. The integrity of more than 300 million travel locks has been...
-
 221Incidents
221IncidentsExcellus healthcare hack puts 10m Americans at risk of identity theft
Miscreants infiltrated network in 2013 … discovered last month. Health insurance company Excellus said hackers broke into its servers and may have...
-
 193Malware
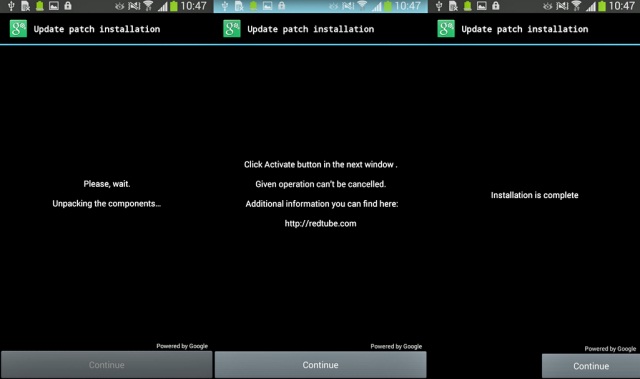
193MalwareNew Android ransomware locks out victims by changing lock screen PIN
Infected owners must choose between paying $500 and performing factory reset. Malicious apps that disable Android phones until owners pay a hefty...
-
 309News
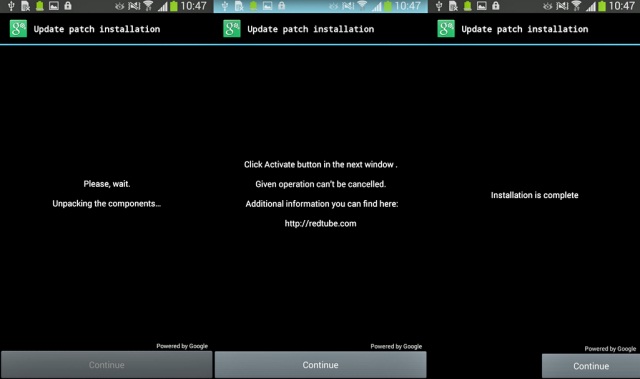
309NewsKaspersky Claims Russian Government Hacking Groups Hacked Satellites
One of the world’s most sophisticated hacking groups, linked to the Russian government, has been accused of hijacking vulnerable commercial satellite communications,...
-

 190Geek
190GeekTechnology Comes To Aid Stricken Refugees Fleeing War and Persecution
As many of the world’s leaders stand accused of shameful neglect and failure over the current refugee crisis, ordinary people have stepped...
-
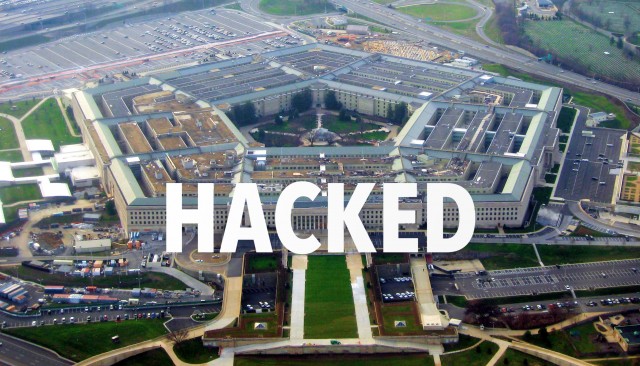
 210News
210NewsPentagon Hacked Again, Credit Card Data Stolen
In August, we reported how Pentagon had its unclassified emailing server hacked allegedly by Russian hackers with a sophisticated phishing attack. Now, reportedly...
-

 272Hacked
272HackedHackers Won’t Stop: 888 Data Breaches So Far In 2015 and 246 Million Records Lost
Short Bytes: The first half of 2015 has been rocked by 888 incidents data breaches so far, leading to 245.9 million records compromised...
-

 299News
299NewsUS Based Health Insurer Hacked, 10 million Customers Affected
10 million+ members’ data leaked after system breach of Rochester-based New York health insurer. Excellus BlueCross BlueShield, an upstate New York health...
-
 113Data Security
113Data SecurityMusical Chairs Campaign Found Deploying New Gh0st RAT Variant
Researchers have peeled back the layers on a new campaign that spans multiple years and involves a new variant of the ubiquitous Gh0st remote...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




