Featured News
-

 275Hacked
275HackedIntel Makes Automotive Security Review Board to Save Your Cars From Getting Hacked
Short Bytes: In the wake of recent car hacks and security breaches, Intel has planned to establish an Automotive Security Review Board (ASRB)...
-
 81Data Security
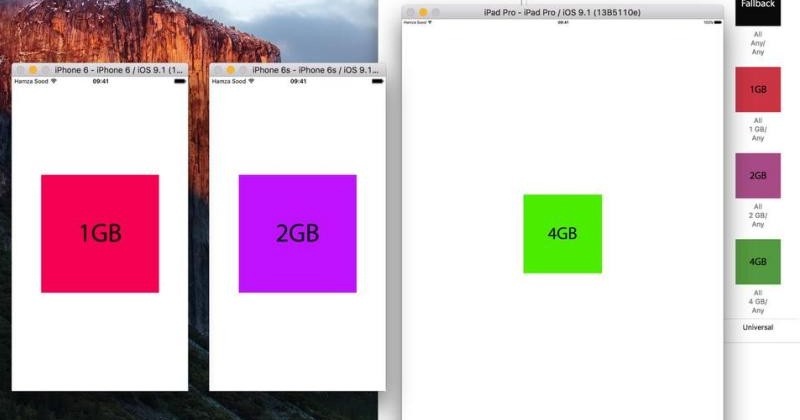
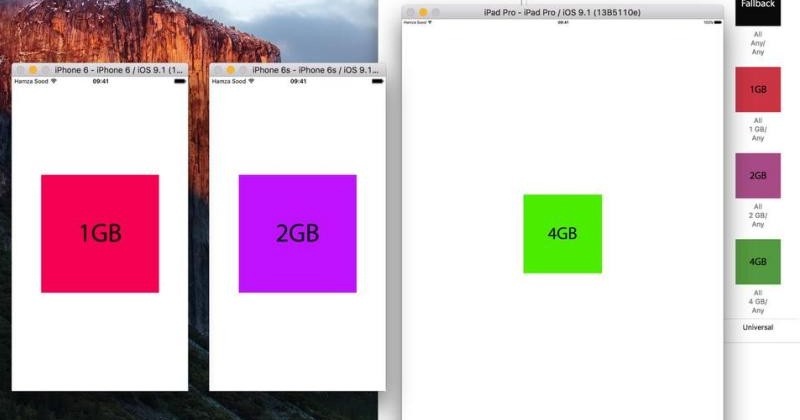
81Data SecurityXcode hack confirms 2GB RAM on iPhone 6s, 4GB on iPad Pro
Apple is traditionally mum on some details of its devices’ hardware, preferring to talk about how “B is X times faster than...
-

 72Data Security
72Data SecurityHow did jihadists hack into top UK ministerial emails if no security breach took place?
Answers on a postcard from Syria, please. GCHQ has declined to comment on a report in the Daily Telegraph this weekend, which...
-

 168Vulnerabilities
168VulnerabilitiesYokogawa patches widespread SCADA vulnerability
Networking process crashed by crafted packets. One of the world’s major suppliers of industrial networking kit, Japanese company Yokogawa, has alerted the...
-
 200Malware
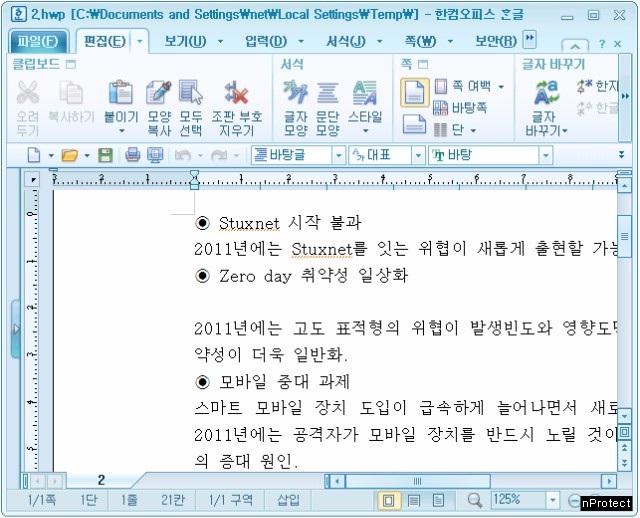
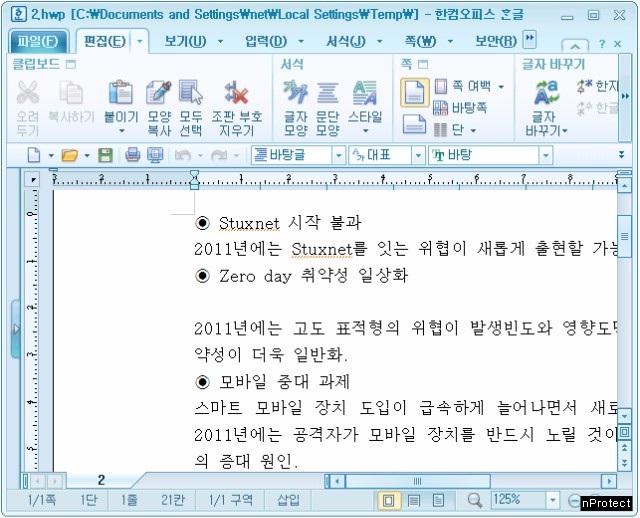
200MalwareNorth Korea Installs Backdoor in South Korea’s Favorite Word Processor
Hackers linked to known North Korean attack points and methods exploited a zero-day vulnerability in the Hangul Word Processor (HWP), widely deployed...
-
Firewall
GlassWire – Best Firewall Software
GlassWire is a lot more than just a great firewall. The free firewall software monitors your network in an easy to understand...
-

 337How To
337How ToGetting Started With Raspberry Pi – Knowing Your Pi (Part – 1)
Short Bytes: The credit-card-sized Raspberry Pi was released long back in 2012 and it has grown to become one of the most...
-

 210Geek
210GeekWhat’s New in iOS 9 SDK?
Short Bytes: iOS 9 SDK includes new APIs and services that are enabling new categories of apps and features. Multitasking and gaming APIs...
-

 204News
204NewsSmartwatch Users Beware – Report Identifies Vulnerabilities in Wearable Devices
In the past, we reported how your wearable fitness trackers can be hacked. Now, The university of Illinois at Urbana-Champaign’s associate professor Romit Roy Choudhry...
-
 123Data Security
123Data SecuritySurvey Shows Most Americans are Fine with Backdoor in Their Devices
A recent survey from Vormetric revealed that people in the United States are OK with the addition of backdoors in their devices/software....
-

 208News
208NewsTop British Ministers Hacked by ISIS in Sophisticated Espionage Operation
Crucial information held by some of the most senior ministers of David Cameron (including Home Secretary Theresa May) has possibly landed in...
-

 298Cyber Crime
298Cyber CrimeSearching For Hacking Software Leads to Vulnerable Spammy Sites
Thousands of legit websites’ security has been compromised to secretly redirect the visitors, coming through specific search terms, to prospective fraudulent websites...
-
 119Geek
119GeekWordPress High CPU Load Bug After 4.3 “Billie” Upgrade and How to Fix it
Short Bytes: WordPress high CPU load bug – We faced it and I am guessing thousands of other blogs hosted on WordPress faced it too, when...
-
 323Geek
323GeekMicrosoft is Force-Downloading Windows 10 on Windows 7 and 8 Machines
As reported previously how Microsoft released updates to spy on Windows 7, 8 and 8.1 Users just like it does on Windows 10. Now...
-
 221How To
221How ToCrack WPA & WPA2 with Aircrack-ng on Kali Linux
Aircrack-ng best WiFi penetration testing tool used by hackers. In this tutorial we are going to teach you How to Crack WPA &...
-
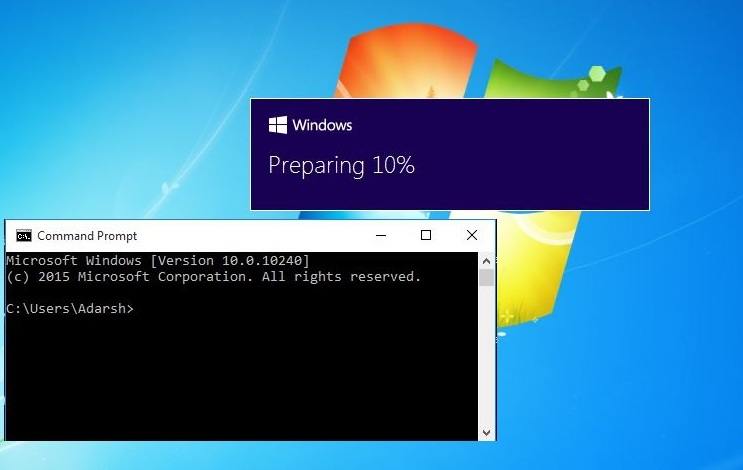
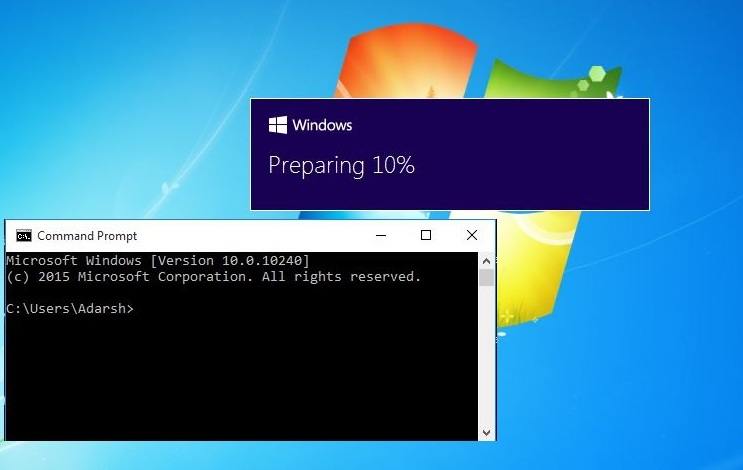 374How To
374How ToHow to Stop Windows 10 Automatic Downloading on Your Windows 7 and 8.1 PC
Short Bytes: It’s reported that some Windows 7 and 8.1 PCs are downloading Windows 10 automatically- even if the users haven’t reserved the...
-
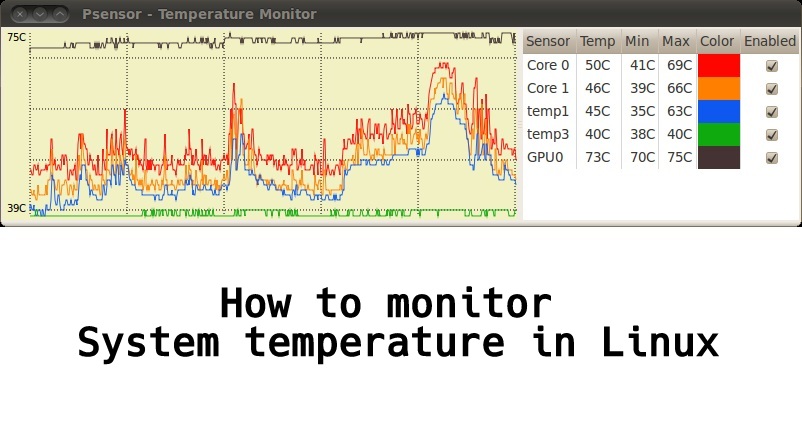
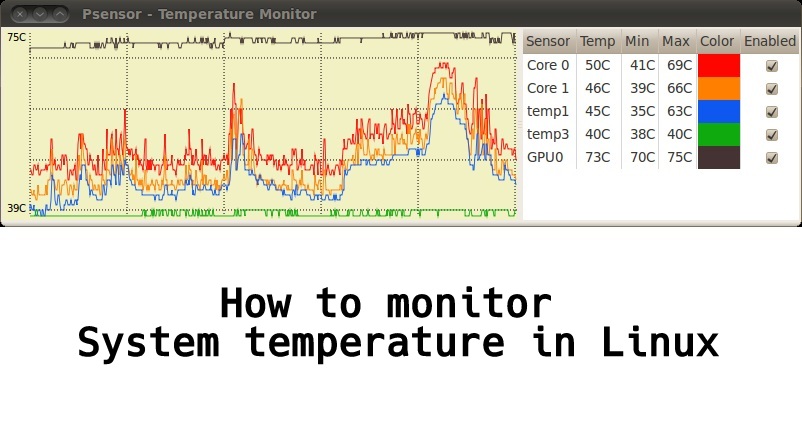 284Geek
284GeekHow to Monitor System Temperature in Linux – GUI Based Temperature Monitoring Tool
Short Bytes: Psensor is a graphical hardware temperature monitor for Linux. It is a GTK+ application for monitoring hardware sensors, including temperatures and fan...
-

 172Vulnerabilities
172VulnerabilitiesiOS 9 Jailbreak: Yes, Apple’s latest version of iOS has already been cracked
Apple will release iOS 9 next week, and some iOS 8 users who rely on unofficial apps installed on their iPhones and...
-
 226Hacked
226HackedMIT is the Most Insecure University in the US
Short Bytes: MIT may boast of having one of the smartest bunch of people under one roof, but when it comes to...
-
 151Data Security
151Data SecurityFirst library to support anonymous Internet browsing effort stops after DHS e-mail
Since Edward Snowden exposed the extent of online surveillance by the US government, there has been a surge of initiatives to protect...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




