Featured News
-
 191Malware
191MalwareBitTorrent kills bug that turns networks into a website-slaying weapon
Reflective technique would let attacker amplify traffic and flood targets. BitTorrent has fixed a flaw in its technology that quietly turns file-sharing...
-

 358Cyber Crime
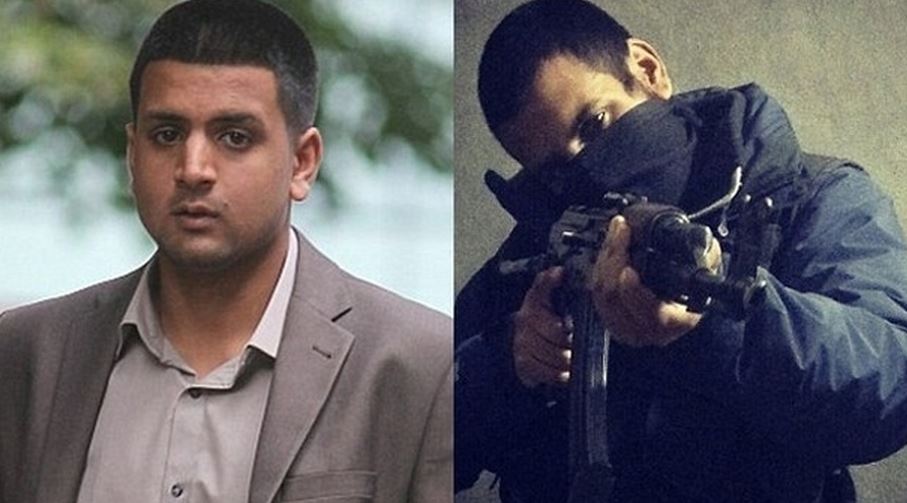
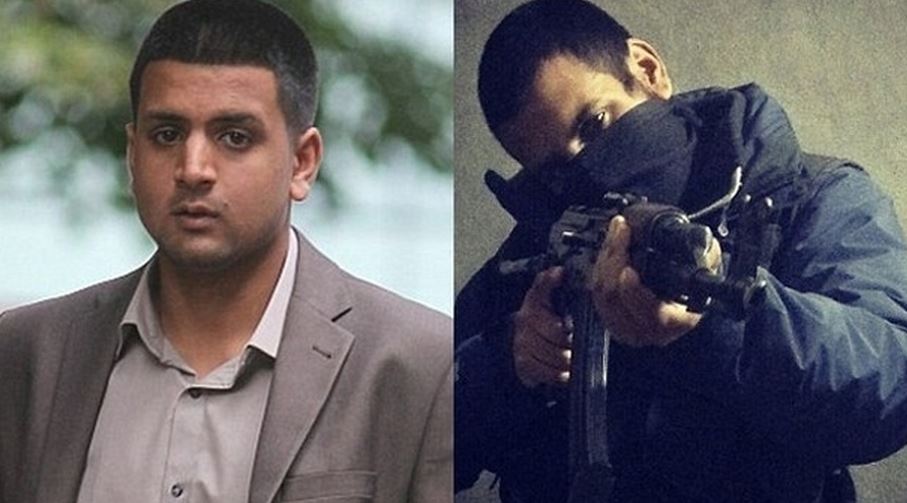
358Cyber CrimeTop British Hacker For ISIS Junaid Hussain Killed in US Drone Strike
A British computer hacker, an ex-TeaMp0isoN member and a member of the so-called Islamic State (IS, previously ISIS/ISIL) believed to be killed in a recent drone...
-

 175News
175NewsIBM’s Security Report Suggests Users To Avoid TOR
Security researchers have suggested that corporations and enterprises should block all of the encrypted and anonymised traffic that they are receiving through...
-

 251Hacked
251HackedUS Police Will Now Use Armed Drones, Weaponized With Tasers and Tear Gas
Short Bytes: In a surprising development, Police in North Dakota are now authorised to use armed drones equipped with tasers, rubber bullets,...
-
 199Hacked
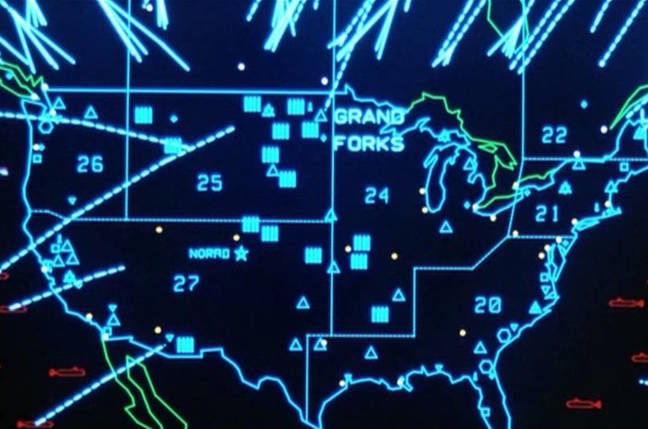
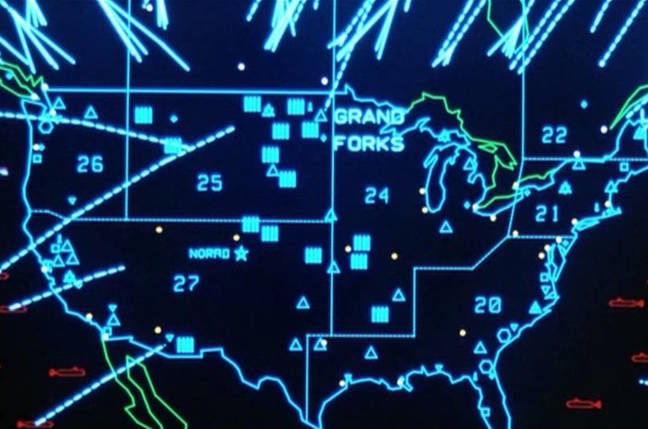
199HackedTop ISIS Hacker And Recruiter Reportedly Killed In U.S. Airstrike
Short Bytes: In the latest reports by CNN, the top ISIS hacker and recruiter was reportedly killed in the U.S. air strike...
-

 307Geek
307GeekOnline Child Predator Charged with ‘Revenge Porn’ Against Underage Girls
The city of Los Angeles arrested a young man on almost 150 charges – 109 felonies and 42 misdemeanors – related to...
-

 209Data Security
209Data SecurityAutoIt Used in Targeted Attacks to Move RATs
Hackers, months ago, revived macros as an attack vector to primarily hide banking malware spread by spam campaigns. Not be left out,...
-

 194Vulnerabilities
194VulnerabilitiesDolphin and Mercury Android browsers have major vulnerabilities
Major vulnerabilities have been detected in Dolphin and Mercury Android browsers that could have provided cybercriminals with the opportunity to launch zero-day...
-

 143Vulnerabilities
143VulnerabilitiesConcerns new Tor weakness is being exploited prompt dark market shutdown
Agora dark market suspends operations after finding “suspicious activity.” A dark market website that relies on the Tor privacy network to keep...
-

 129Malware
129MalwareMalware menaces poison ads as Google, Yahoo! look away
Booming attack vector offers mass malware distribution, stealthy targeting. Feature Online advertising has become an increasingly potent threat to end-user security on...
-

 179Vulnerabilities
179VulnerabilitiesPatched Ins0mnia Vulnerability Keeps Malicious iOS Apps Hidden
Apple’s monster security update of Aug. 13 included a patch for an iOS vulnerability that could beacon out location data and other...
-

 305Geek
305GeekAndroid Devices Vulnerable to Certifi-Gate Flaw Exploited By Remote Support Apps
Officials at Check Point, the IT security vendor, have discovered a rogue app on the Google Play Store that is exploiting the...
-
 334Geek
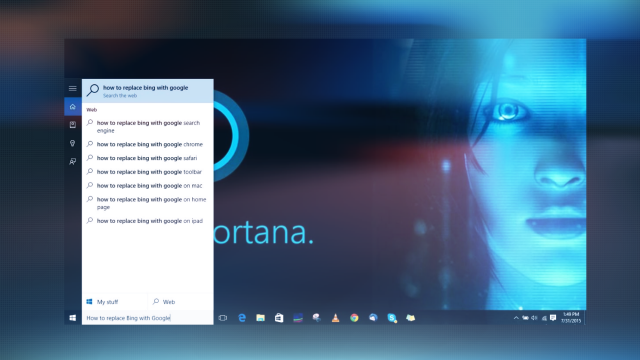
334GeekPrevent Windows 10 From Spying On Your Search Data
In the beginning of this month, Microsoft released the public version of their latest operating system Windows 10, which has already been...
-

 291News
291NewsiOS Jailbreak Backdoor Tweak Compromised 220,000 iCloud Accounts
The recent security breach on iOS platform left 220,000 iCloud user accounts vulnerable due to a backdoor privacy attack caused by the...
-

 240Scams
240ScamsSupport scams, malware and mindgames without frontiers
Introduction It might not have escaped your notice that I write quite a lot about support scams, an issue in which most...
-
 319Geek
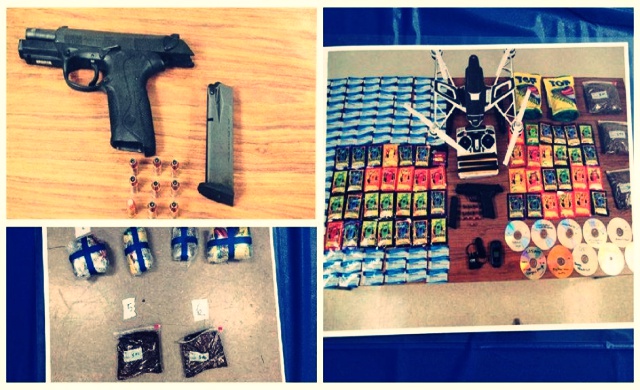
319GeekDrone Caught Delivering Drugs, X-Rated DVDs, Firearm at a High-Security Prison
The state of Maryland has witnessed an unusual case of package delivery; two individuals were found attempting to smuggle a few articles...
-
 285Hacked
285HackedIBM: Hackers are Using Tor Network More Frequently For Launching Hacking Attacks
Short Bytes: A report from IBM researchers has shown that the use of Tor network is on the rise. As a result, the growth...
-

 111Data Security
111Data SecurityHow hackers hijack the net’s phone books
Online services that charge to kick people out of games or bombard websites with data have been put out of action by...
-

 199Data Security
199Data SecurityHigh-heeled hacker builds pen-test kit into her skyscraper shoes
Social engineering with very obvious assets blinds you to techno-toolkit. MILDLY NSFW A Chinese hardware hacker has hidden a penetration-testing toolkit into her...
-

 200Data Security
200Data SecurityAshley Madison puts $377,000 bounty on hackers’ heads
Police suspect two suicides are related to the release of information stolen from the relationship-cheating website. Amid reports that the Ashley Madison...
The Latest
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover UEFI Vulnerability Affecting Multiple Intel CPUs
-
 Malware
MalwareChinese Cyber Espionage Targets Telecom Operators in Asia Since 2021
-
 Malware
MalwareNew Rust-based Fickle Malware Uses PowerShell for UAC Bypass and Data Exfiltration
-
 Malware
MalwareExperts Uncover New Evasive SquidLoader Malware Targeting Chinese Organizations
-
 Vulnerabilities
VulnerabilitiesKraken Crypto Exchange Hit by $3 Million Theft Exploiting Zero-Day Flaw
-
 Vulnerabilities
VulnerabilitiesUNC3886 Uses Fortinet, VMware 0-Days and Stealth Tactics in Long-Term Spying
-
 Malware
MalwareNew Threat Actor ‘Void Arachne’ Targets Chinese Users with Malicious VPN Installers
-
 Malware
MalwareWarning: Markopolo’s Scam Targeting Crypto Users via Fake Meeting Software
-
 Vulnerabilities
VulnerabilitiesMailcow Mail Server Flaws Expose Servers to Remote Code Execution
-
 Malware
MalwareCybercriminals Exploit Free Software Lures to Deploy Hijack Loader and Vidar Stealer
-
 Vulnerabilities
VulnerabilitiesNew Malware Targets Exposed Docker APIs for Cryptocurrency Mining
-
 Vulnerabilities
VulnerabilitiesVMware Issues Patches for Cloud Foundation, vCenter Server, and vSphere ESXi
-
 Vulnerabilities
VulnerabilitiesASUS Patches Critical Authentication Bypass Flaw in Multiple Router Models
-
 Data Breach
Data BreachChina-Linked Hackers Infiltrate East Asian Firm for 3 Years Using F5 Devices
-
 Cyber Attack
Cyber AttackHackers Exploit Legitimate Websites to Deliver BadSpace Windows Backdoor
-
 Cyber Attack
Cyber AttackNiceRAT Malware Targets South Korean Users via Cracked Software
-
 Malware
MalwareGrandoreiro Banking Trojan Hits Brazil as Smishing Scams Surge in Pakistan
-
 Malware
MalwarePakistani Hackers Use DISGOMOJI Malware in Indian Government Cyber Attacks
-
 Data Breach
Data BreachZKTeco Biometric System Found Vulnerable to 24 Critical Security Flaws
-
 Malware
MalwareNorth Korean Hackers Target Brazilian Fintech with Sophisticated Phishing Tactics




