Featured News
-

 130Scams
130ScamsMicrosoft advises ‘spoofed’ Skype users to change passwords
Skype users have been advised by Microsoft to change their passwords following reports that 'spoofed' messages are being sent without user permission.
-

 183Hacked
183HackedInstagram Can Totally Hijack Your Account And Give To Some Celebrity
How cool would it be if somehow your parents were Pitt’s and ended up to name you Brad, or a simple Messi...
-

 103Cyber Crime
103Cyber Crime37 million relationship cheats could be exposed by Ashley Madison hack
The 37 million users of hacked infidelity site Ashley Madison are at risk of having their names and private details leaked, reports...
-
 386Hacked
386HackedMicrosoft: Free Windows 10 Upgrade Comes With 10 Years of Free Updates
Windows 10 is one of most talked about topics on various online forums. Microsoft is leaving no stone unturned to achieve its...
-
 265Hacked
265Hacked37 Million Adulterers Exposed, Online “Cheating” Site Ashley Madison Hacked
Online cheating website AshleyMadison.com has been hacked, and as a result, large chunks of data has been stolen. The compromised data has...
-
 197Hacked
197HackedCyberGhost Privacy Accelerator Program Offers €100,000 if You Can Make Web a Secure Place
“How Government secretly read your e-mails with this insane law?“ “Snowden’s Revelations: XKEYSCORE is NSA’s search engine.” “Real-Time Cyber Attacks across the globe. ““NSA’s...
-

 278Geek
278GeekTop Netflix Open Source Projects You Must Know
This is the 3rd post in the series covering top open source projects by most popular companies in the world. Today, we...
-
 331News
331NewsCyberwar: Pakistani President’s Website Hacked by Bangladeshi Hackers
Pakistani President Mamnoon Hussain’s website has been hacked by Bangladeshi hackers — 72 other Pakistani government websites have been hacked as well....
-

 230Data Security
230Data SecurityWindows XP Anti-Malware Support Terminated – 180 Million Users Left Vulnerable
Millions of Windows XP users are now left vulnerable to malware attacks as Microsoft has decided to terminate support and security updates...
-

 312Hacked
312HackedThis Hacked Gun Mounted Drone Shoots Bullet in Terrifying Video
The world is getting scarier each day. And I don’t mean the terrorist attacks or cyber threats or global warming, or least...
-
 339Hacked
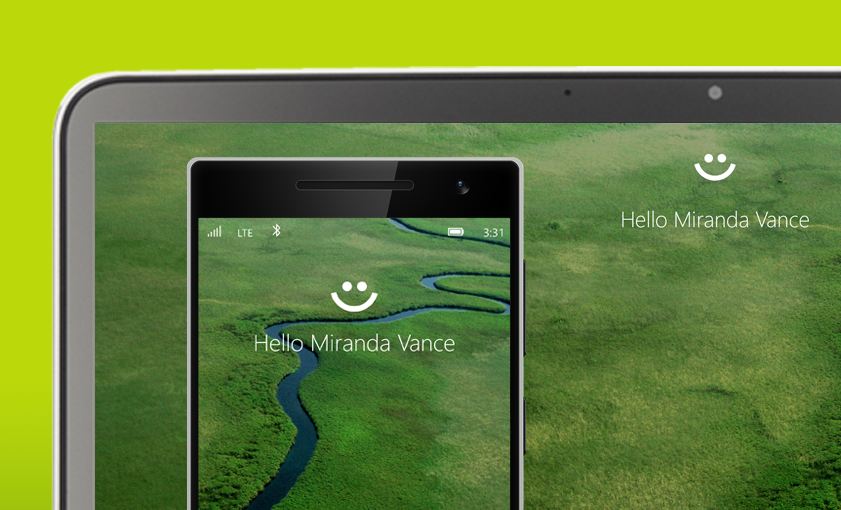
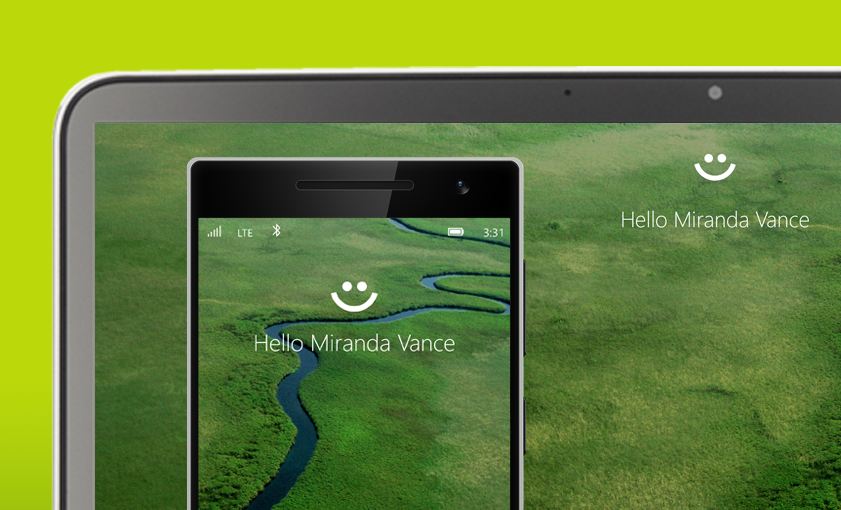
339HackedComplete List of PCs Supporting Windows Hello, the Password Killer Feature of Windows 10
With Windows 10’s Windows Hello feature, you will be able to log into your PCs without any password. Windows Hello users to...
-

 271Geek
271GeekMicrosoft Now Providing Support for Linux Users in Azure
Microsoft Azure cloud platform is very popular among Linux users and now Microsoft has announced that it will be offering limited support...
-
 165Hacked
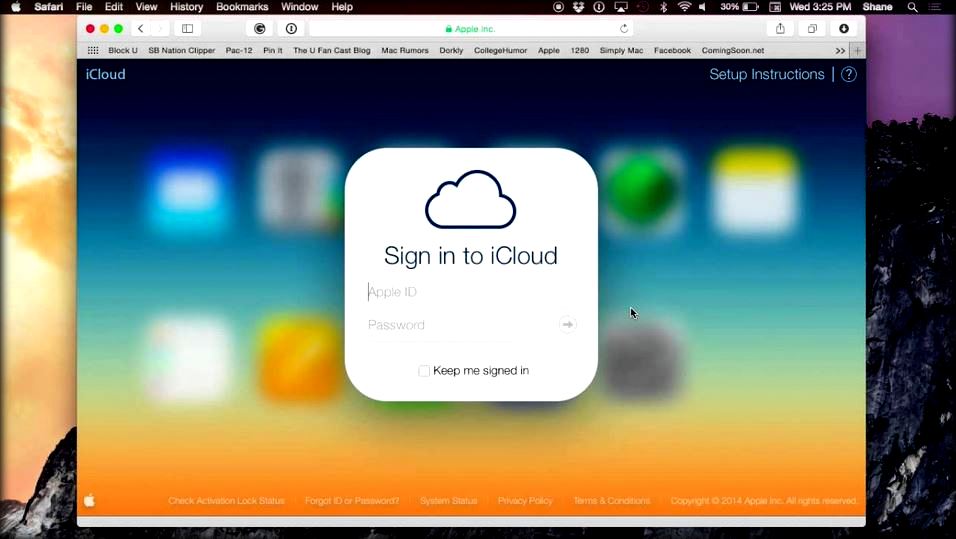
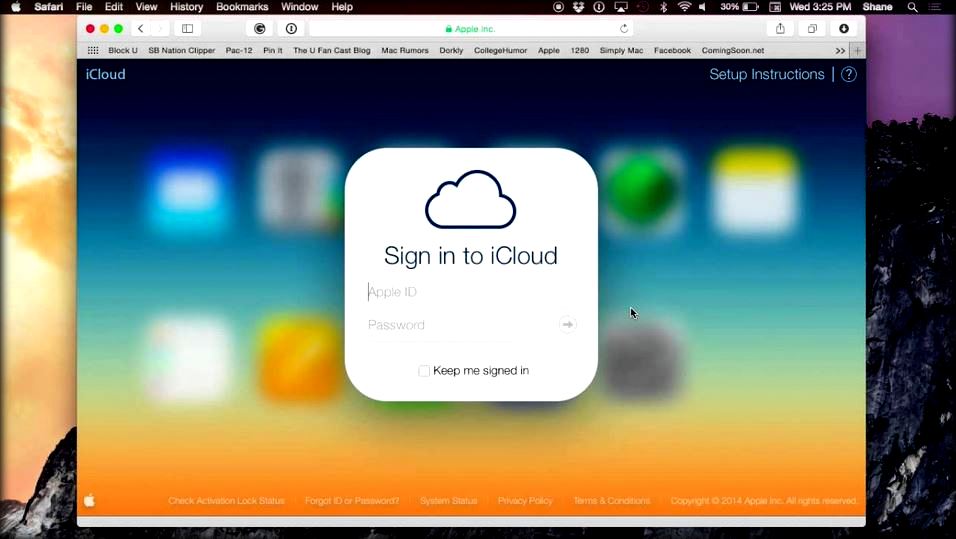
165HackedHow Apple’s iCloud Drive Deletes Your Files Without Any Warning
iCloud Drive is one of the most-used Apple services as it’s a Dropbox-like solution to keep all your devices’ data in sync....
-

 61Cyber Crime
61Cyber CrimeHuge Morrisons data breach due to employee with grudge, court hears
A Morrisons employee with a grudge was responsible for posting personal data of nearly 100,000 staff onto the internet, a court heard.
-

 315Hacked
315HackedFBI Used Hacking Team’s Help to Track Tor User
Earlier this month, as a part of the massive breach at the infamous Hacking Team, numerous documents were leaked. Since then, analysts...
-

 177Hacked
177HackedAfter ProxyHam’s Disappearance, Here’s How to Make Your Own ProxyHam for Anonymous Browsing
About two weeks ago, we reported about the Raspberry Pi 2 based WiFi router that provided anonymous WiFi by putting you 2.5...
-

 67Cyber Crime
67Cyber CrimeBritish teenager sentenced for massive Spamhaus attack
British teen Seth Nolan Mcdonagh, aka "narko" has been sentenced for his role in a 2013 attack which slowed the internet around...
-

 185Malware
185MalwareUnited Airlines pays out 2 million flight miles for security bugs
United Airlines has paid out two million flight miles to two security researchers who uncovered 14 separate vulnerabilities in the company’s operation.
-

 257Geek
257GeekTop Twitter Open Source Projects You Must Know
Welcome to the second post of the series covering top open source projects by most popular companies in the world. Last time,...
-
 269Hacked
269HackedNSA Open Sources its Linux-based Cyber Security Tool
The American security Agency NSA is infamous for its mass surveillance programs. Every alternate day, we are greeted with new revelations regarding...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




