Featured News
-

 125Opinion
125OpinionThe ABC of information security
There are three fundamental elements that must not be overlooked when starting out in corporate security, summarized as the 'ABC of information...
-

 230How To
230How ToDeveloper Makes Tool to Play GTA V in Any Web Browser
Short Bytes: A developer has developed a program called jsmped-vnc. If your PC isn’t powerful enough to run GTA V, you can...
-
 284How To
284How ToHow to Get Windows 10 at the Lowest Price
Short Bytes : Many of you would be wondering- why I’m writing this “how to get Windows 10 at the lowest price”...
-

 272Data Security
272Data SecurityPakistan to Shut Down BlackBerry Services Amid Security Concerns
Pakistan Telecommunication Authority has ordered the local cellular operators to completely shut down Canadian smartphone maker’s BlackBerry Enterprise Services (BES) by the...
-

 391Lists
391ListsEverything You Need to Know About Windows 10 Upgrade – FAQs
Short Bytes: Now, Windows 10 is launched and Microsoft is convincing as much as users to take the advantage of its free Windows...
-

 84Cyber Crime
84Cyber CrimeValve Steam bug sees accounts hacked
A serious bug in Valve’s Steam engine has allowed a series of user credentials to be stolen over the past week, according...
-

 107Privacy
107PrivacyAccidental pocket dials can be used in evidence, says US court
Accidental ‘pocket dials’ are now admissible in evidence against you, the US Appeals court has ruled.
-

 77Cyber Crime
77Cyber CrimeCybercrime update: take downs, arrests, convictions, and sentences
Information security could use some good news right now, something to offset the string of bad news about data breaches and system...
-
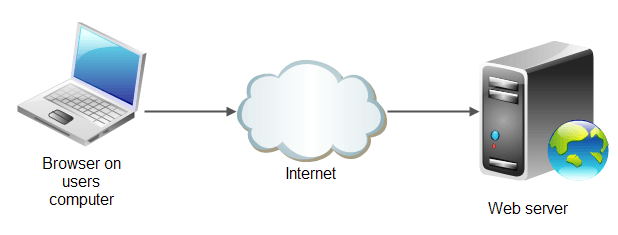
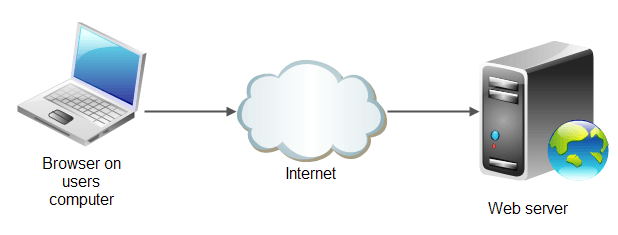 195Geek
195Geekrwasa High Performance Web Server Claiming to be Better than nginx and lighttpd
2 Ton Digital – a company which provides products, services and support for any company or individual that is interested in security, network...
-

 284Geek
284GeekTop Airbnb Open Source Projects You Must Know
This is the 4th post in the series covering top open source projects by most popular companies in the world. Today, we...
-
 186Hacked
186HackedOne in Every 600 Websites Has .git Exposed, How to Check Yours and Hide It
Recently, I read about an innocent mistake committed often by web developers and thought it’d be nice to share it on fossBytes....
-

 207Surveillance
207SurveillanceHere’s A Mobile Spy App That Fulfills All Your Monitoring Needs
Mobile spy apps are available at the handful, but you don’t need them that way at all, one good spy app would...
-
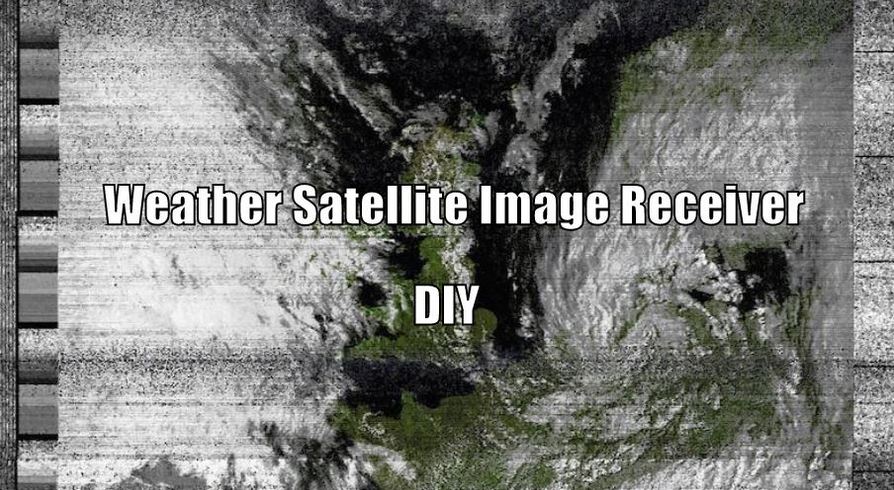
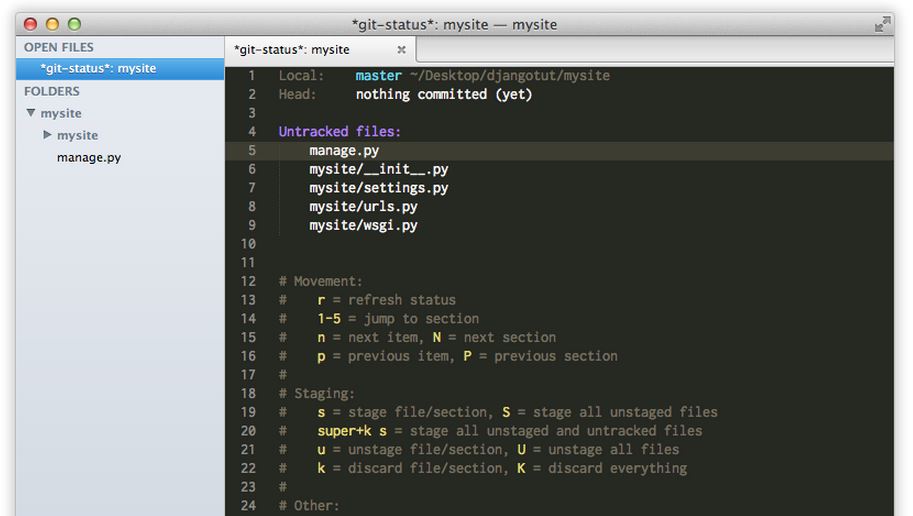
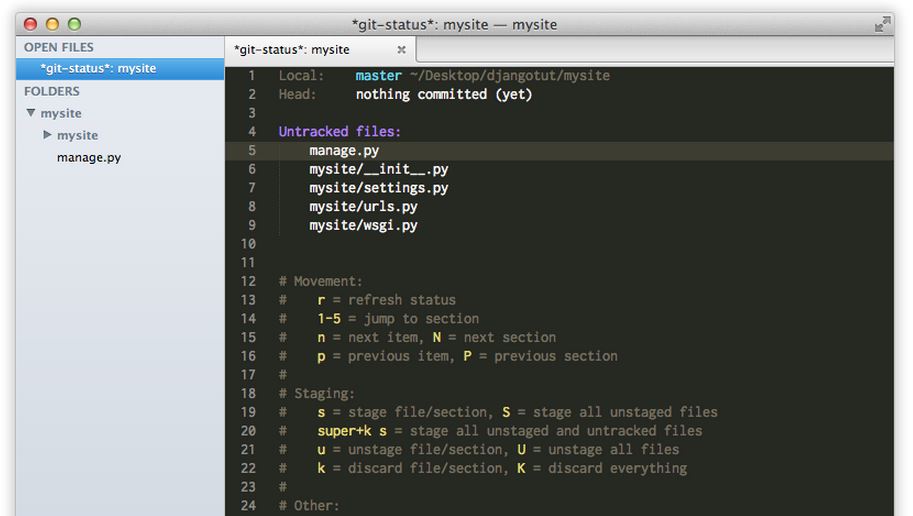
 258How To
258How ToHow to Build Weather Satellite Images Receiver With $20 Dongle
This “how-to build weather satellite images reciever” is based upon Matt Gray’s project on receiving weather satellite image with £8 dongle. Matt Gray is...
-

 279Hacked
279HackedGoogle Tells You How To Stay Safe Online
When most of your Facebook timeline is flooded with news like cyber threats and security, how cyber criminals steal your money, and...
-

 280Surveillance
280SurveillanceHORNET – Faster and Secure Anonymity Network Than Tor
Most of you must have heard about Tor, which is one of the renowned network based on onion router, delivers a good...
-

 187Hacked
187Hacked500 Million Devices at Risk Due to Leaked “Easy to Use” RCSAndroid Malware
The massive data breach at the Hacking Team has resulted in tons of revelations regarding different kinds of spyware and the potential security...
-

 290Surveillance
290SurveillancePakistan’s ISI Plans to Tap International Undersea Cables, Rivals the NSA, GCHQ
The most powerful intelligence and spy agency of Pakistan, specifically Inter-Services Intelligence (ISI), has now planned to tap all the Internet traffic...
-
 317Hacked
317HackedMovie Studios Repeatedly Report Their Own 127.0.0.1 Localhost for Piracy
The torrent pirates that keep hurting the million-dollar movie studios by uploading the data using their torrent clients are their biggest enemies...
-

 269News
269NewsGoogle, Microsoft, Kaspersky Labs, NIC For Morocco Domains Hacked
Who says high-profile websites are unhackable? We just witnessed Moroccan hackers taking over websites of tech giants and those claiming to protect...
-
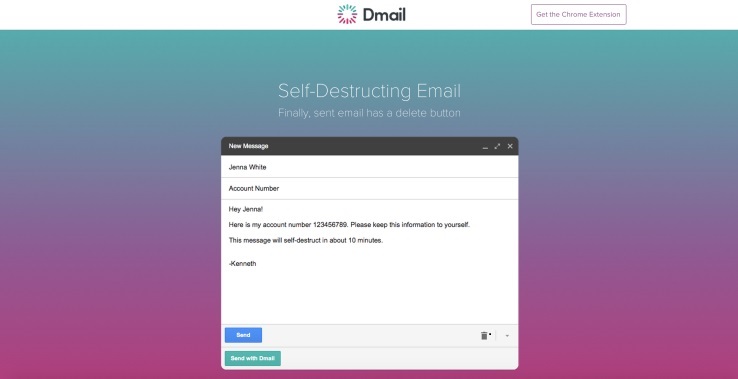
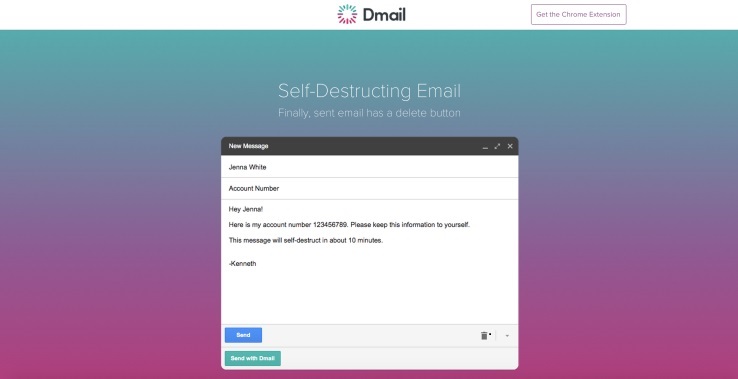 222Hacked
222HackedHow To Self Destruct Email With Dmail
Admit it, you have wanted this for a long time. There must have been instances when you regretted sending an email with...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




