Featured News
-

 368Cyber Crime
368Cyber CrimeOnline democracy by 2020? University reveals e‑voting security breakthrough
A breakthrough in e-voting from the University of Birmingham suggests that the old ballot box tradition may come to an end in...
-
 328Hacked
328HackedUSBkill – Code That Turns USB Drives Into PC Killing Weapon
Here’s a news that will cheer up all the activists, criminals, activists and whistle blowers. Now they have got a new tool...
-
 308Data Security
308Data SecuritySimple Tips to manage and Prevent Social Engineering Attacks
The web is an interconnected maze consisting of people, organization and computers. The easiest way to hack into such a system is...
-

 235Hacked
235HackedWorld Trade Organization Hacked by Anonymous
The hacktivists of Anonymous are once again back in the news with their latest attack. A hacker claiming to be affiliated with...
-

 280News
280NewsUber USA customers hacked – Change your username and password ASAP
In March, Motherboard reported Uber accounts had been stolen by hackers who were selling them on public forums for as low as...
-
 426Hacked
426HackedHow To Make Incognito Mode the Default Browsing Mode In Chrome?
Today privacy is the greatest concern in our world dictated by our online presence. Those who are aware of the consequences of...
-
 228Geek
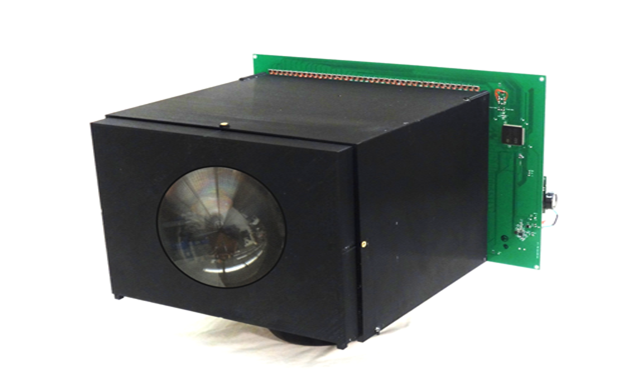
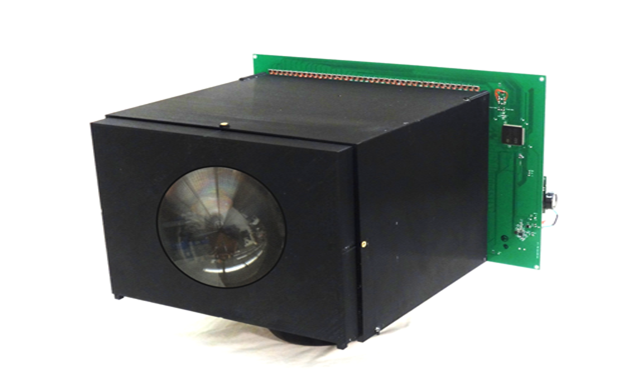
228GeekNo Battery required – Self-Powered Video Camera runs, records forever
Researchers have developed a video camera which can record non-stop — The camera is one of its kind. Columbia University researchers have developed...
-

 284Cyber Events
284Cyber EventsStatues of Snowden, Assange, Manning unveiled in Berlin’s Alexanderplatz square
Famous whistleblowers Chelsea Manning, Edward Snowden and Julian Assange can be seen standing in Berlin now as their life-size bronze statutes were...
-

 316Interview
316InterviewDavid Harley: “New scams are difficult to spot even for a trained eye”
Harley says that scams and social engineering have been a constant in cybercrime - but in the past few years, some scams...
-

 77How To
77How ToNational Small Business Week: a cybersecurity survival guide
It's National Small Business Week in the U.S. and, because properly protecting the digital assets of your small business could be vital...
-

 114Cyber Crime
114Cyber CrimeThe world’s most wanted hackers
The FBI is taking cybercrime seriously. Here are some of the most wanted hackers in the world, and what they're wanted for...
-

 262Hacked
262HackedHow To Become An Ethical Hacker? [Infographic]
Cyber-security is one of the major concerns of online users these days and hackers are an inevitable part of this discussion. Every...
-

 276Data Security
276Data SecurityBoeing 787s can lose control while flying due to Software bug
A warning has been issued by the FAA regarding the software glitch in the system of Boeing’s 787 Dreamliner — This glitch...
-

 333News
333NewsAnonymous Hacks World Trade Organization, leaks personal data of thousands of officials
Keeping Anonymous hackers out from news is simply impossible, the hacktivist movement is active 24 x 7 and you can always expect them...
-

 382Data Security
382Data SecurityBanking Malware Delivered via Macro in PDF Embedded Word Document
Delivering banking malware through Microsoft Word documents has been a less common method. However, it is currently being used for spreading malicious...
-

 127Hacked
127HackedNew Firefox Features Will Only Support Secure Websites
In a recent blog post, Mozilla has showed its intent to phase out the non-secure websites i.e. the HTTP. Earlier this week,...
-

 191Cyber Crime
191Cyber CrimeNigerians arrested for Laundering €2.5 Million through Online Scam
Ten individuals of Nigerian origin have been arrested by Guardia di Finanza for laundering millions of pounds acquired from frauds causing loss...
-

 239News
239NewsRed Bull Malaysia Website Hacked by Pro-Palestinian Hackers
After successful OpIsrael, AnonGhost is now targeting random but high-profile websites around the world. The latest in line is Red Bull Malaysia. The...
-
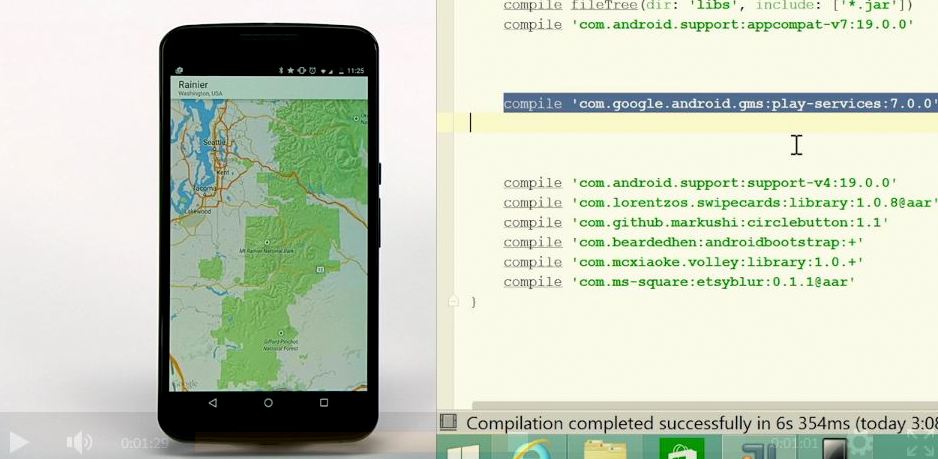
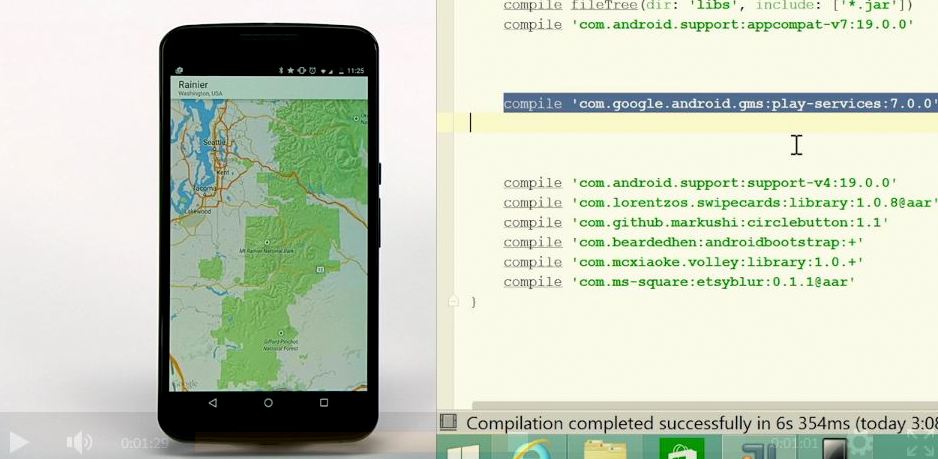 234Geek
234GeekHow Android and iOS Apps Could be Ported to Windows for Mobile – Everything Detailed
Microsoft’s Build 2015 conference is now over and we were greeted with many pleasant surprises. According to me, one of the biggest...
-

 268Data Security
268Data SecurityWikiLeaks’ Anonymous Leak Submission Website Relaunched after 6 years
Expect exposure of confidential news pieces and government/corporate classified documents every now and then because WikiLeaks, the anti-secrecy group has re-launched its...
The Latest
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareMalicious Google Ads Pushing Fake IP Scanner Software with Hidden Backdoor
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesGenAI: A New Headache for SaaS Security Teams




