Featured News
-

 232Geek
232GeekMicrosoft Launches .NET Core Preview For Linux and Mac Users
Source: TechCrunch From Last November, Microsoft was teasing its developers by saying that some of the key features for Microsoft .NET platform...
-
 302Geek
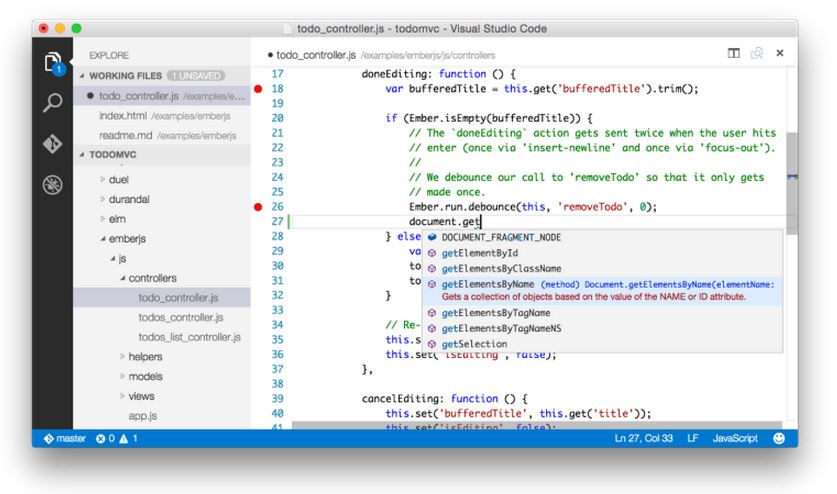
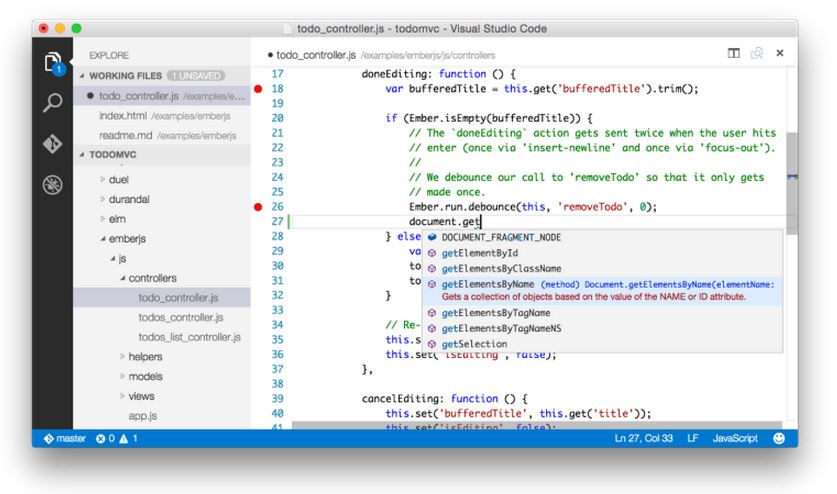
302GeekMicrosoft Releases Free Visual Studio Code for Windows, Mac and Linux
Microsoft released a new development tool – Visual Studio Code – that works Windows, Linux, and Mac. This is being seen as...
-
 162Surveillance
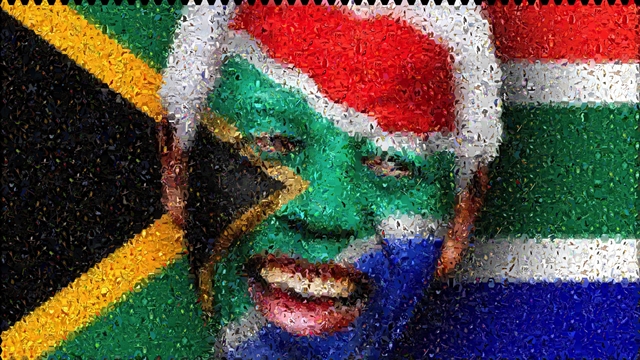
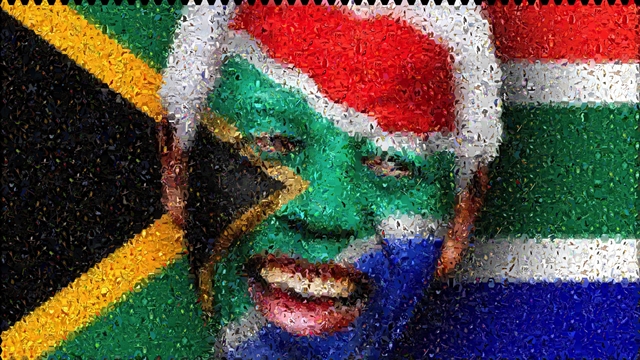
162SurveillanceSouth African Government Spying on its Citizens- Report
The South African Right2Know campaign has released its “Big Brother Exposed” report. The report revealed details about the way activists and community leaders...
-

 177Hacked
177HackedHow a Hacker Hacked PayPal by Remote Code Execution Vulnerability
Today even the big financial players like PayPal, who are expected to deliver secured services to its users, aren’t safe from the...
-

 130Geek
130GeekNew Samsung App Assists Alzheimer’s Patients Remember Their Loved Ones
The importance of a Smartphone was redefined when Azer Jaafoura along with his team members thought about helping Alzheimer’s patients a year...
-
 203Hacked
203HackedChina Attacks on Facebook Using The Great Cannon
For the past few days, we have been hearing about the Great Cannon. This Great firewall system developed by China is terrorizing the...
-

 354News
354NewsMasterCard Website Hacked by Indonesian Hackers
On 25th April, 2015, Indonesian hackers going with the group handle of Gantengers Crew hacked and defaced the Online Resources domain of US based Financial Services...
-
 105Hacked
105HackedYahoo’s Bodyprint Can Unlock Your Smartphone Using Your Ear
You will not need your fingerprints or the face-detection feature of your phone very soon to ensure that your tablet or smartphone...
-

 247Data Security
247Data SecurityResearchers show how medical robots can be hacked during surgery
University of Washington in Seattle’s research team managed to hijack a tele-operated surgical robot. This exposed major security vulnerabilities in machines that...
-

 165Cyber Crime
165Cyber CrimePolice bust hackers who stole $15 million from 24 countries
Twenty five international cyber criminals (who were involved hacking into banking systems and making of clone payment cards) are arrested by the...
-

 331How To
331How ToHow To Run Android Apps In Chrome Browser Using Google ARC
Now Google lets you run your Android apps in Chrome with its ARC Welder app. They recently released the beta version of...
-

 113Cyber Crime
113Cyber CrimeOFAC! An acronym that cybersecurity professionals need to know
OFAC will soon be enforcing economic and trade sanctions against individuals and groups outside the United States that use cyber attacks to...
-

 365Cyber Crime
365Cyber CrimeThe curious case of the ex‑hacker “banned from the internet”
What kind of punishment best fits a convicted hacker? Jail time for serious computer crimes is almost a certainty, but for one...
-

 219How To
219How ToMake Your Own Simplest Electric Train
Have you ever thought of making some cool stuff at home? Well if not, you are about to learn how to make an electric...
-

 203Geek
203GeekGoogle wants to be your wireless carrier with encrypted connection
For all of you who want to know what currently Google is planning to work on, the answer is “Project Fi”— Now...
-
 450Hacked
450HackedHow to Stop Google From Tracking You in Few Simple Steps
Privacy is one of the biggest concern to everyone these days, and to respect your privacy, few days ago Google enabled the option...
-
 292Hacked
292HackedHow to Detect NSA’s Complex “Quantum Insert” Attacks
In the past, whistleblower Edward Snowden has exposed numerous hacking operations run by the US intelligence agency NSA. Out of all these...
-

 92Malware
92MalwareWattsUpDoc: US hospitals trial AC power probes to treat medical malware
Two major hospitals in the United States are trialling a new system for detecting malware on medical devices, using probes that monitor...
-

 210Hacking Tutorials
210Hacking TutorialsHow to protect yourself against Phishing
Phishing is the method of stealing login info(usernames and passwords) by directing the victim to a clone(fake) login page, that logs the...
-

 91Cyber Crime
91Cyber CrimeThirty Meter Telescope website falls over in hacktivist DDoS attack
Hacktivists have launched a distributed denial-of-service attack against the website of TMT (Thirty Meter Telescope), which is planned to be the Northern...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




