Featured News
-

 277Hacked
277HackedHow New Zealand and NSA Plotted Hack on China
China’s foreign ministry has expressed serious concerns over the reports of hacking attacks on China planned by New Zealand and NSA in recent...
-

 422Mobile Security
422Mobile Security1,500 iOS apps open to simple man‑in‑the‑middle attacks
Around 1,500 apps for iPhone and iPad contain an HTTPS vulnerability making it 'trivial' for hackers to perform man-in-the-middle attacks to steal...
-

 286News
286NewsAnonymous Hacks Israeli Arms Importer Site, Leaks Massive Client Login Data
Online hacktivist Anonymous has breached into the website of an Israeli arm importer and manufacture Fab-Defanse (fab-defense.com) and leaked login credentials plus personal...
-

 277Data Security
277Data SecurityFlash Player Bug Records Audio and Video without User Permission
Researchers have identified a vulnerability in some Adobe Flash Player versions that can be exploited by attackers for spying on users having...
-

 544How To
544How ToGoogle Now Lets You Download Your Entire Search History, Here is How To Do This
image: Lifehacker Google now allows you to export and download your entire search history in no time. Last year Google tested a...
-
 284Cyber Events
284Cyber EventsBrazil will sue Facebook for blocking picture of indigenous woman
Brazilian Ministry of Culture is planning to sue Facebook on blocking the picture of an Indian woman from 1909 just because her...
-
 325Geek
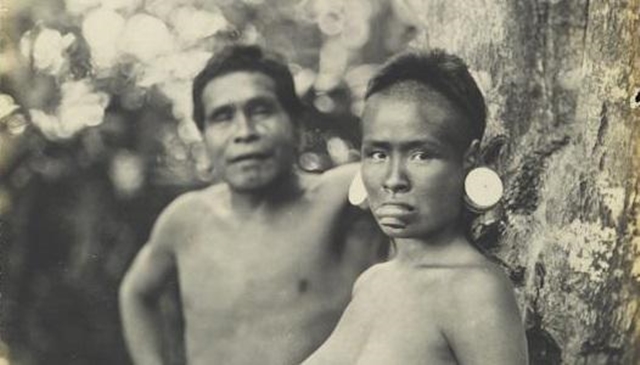
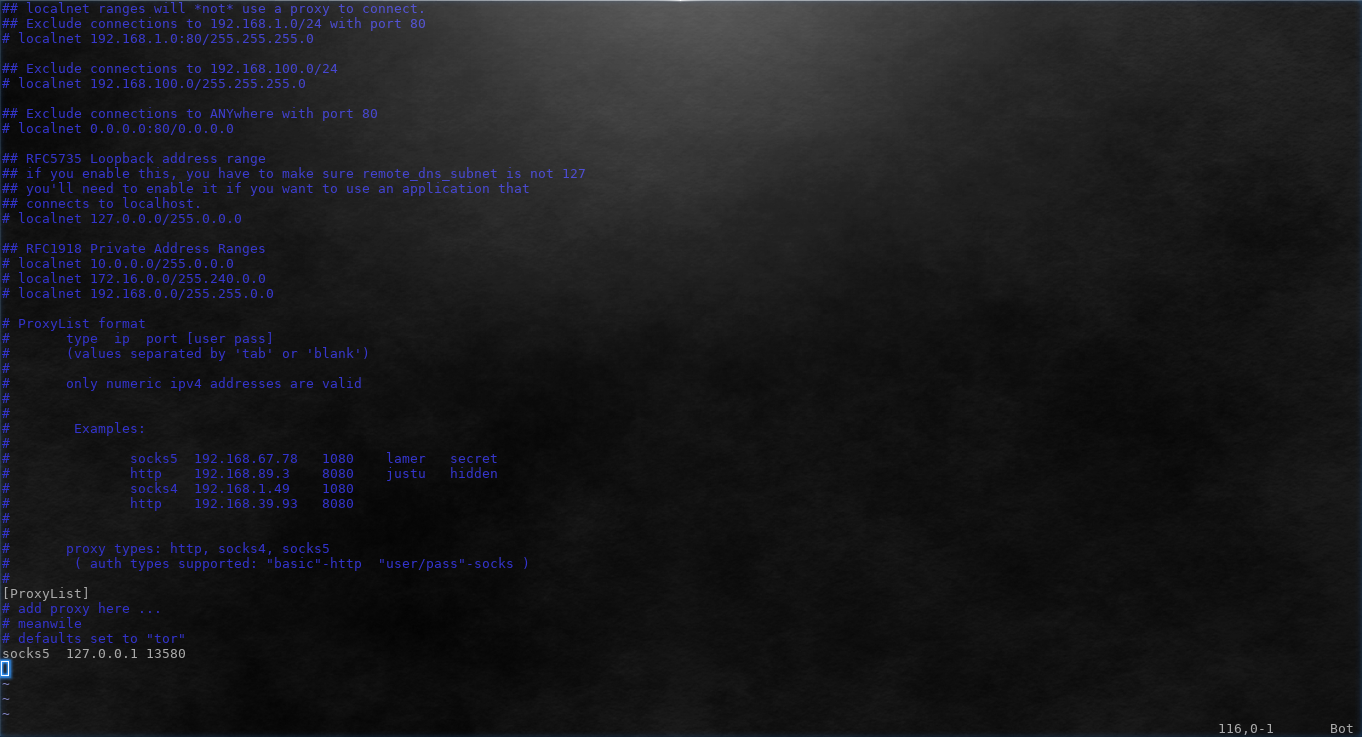
325GeekHow to Use Proxychains to Run Applications Behind Proxy
Some applications do not support proxy by default. Other applications might support HTTP proxy but fail when using SOCKS. As Tor provides...
-

 81Cyber Crime
81Cyber CrimeAustralian infosec body lobbies for mandatory security baseline
Australia's infosec industry is lobbying for a mandatory security baseline to ensure basic IT standards are met across the country, with penalties...
-

 188Cyber Crime
188Cyber CrimeTarget agrees to $19 million data breach settlement with MasterCard
Target has ended its dispute with MasterCard over the retail giant's 2013 data breach by agreeing to a $19 million reimbursement to...
-
 219Tricks & How To's
219Tricks & How To'sHow to find out if you’ve been HACKED with CMD
There are numerous methods to see if you have been hacked. Using the Command Prompt, you can run a command which will...
-

 237Data Security
237Data SecurityMan who revealed plane can be hacked offloaded for the second time
Earlier this week the FBI denied air travel to Chris Roberts due to his sarcastic tweets about United Airlines’ security system on...
-
 313Cyber Crime
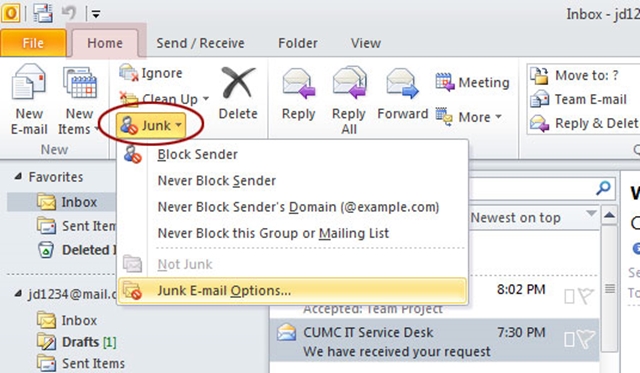
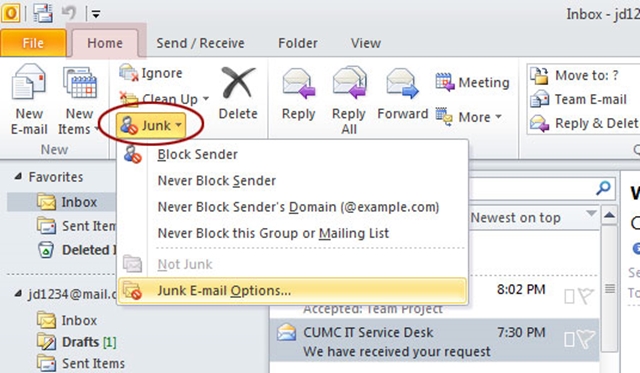
313Cyber CrimeMicrosoft Outlook Users Hit with ‘Discontinue Support’ Phishing Scam
‘Discontinue Support’—Latest Phishing Scam Targeting Microsoft Outlook Users. An email is being circulated by cybercriminals that appears to be sent by Outlook.com...
-

 396How To
396How ToHow To Enable YouTube’s Transparent Player
I think we all agree that YouTube is the best place to watch online videos, and this is why it is world...
-
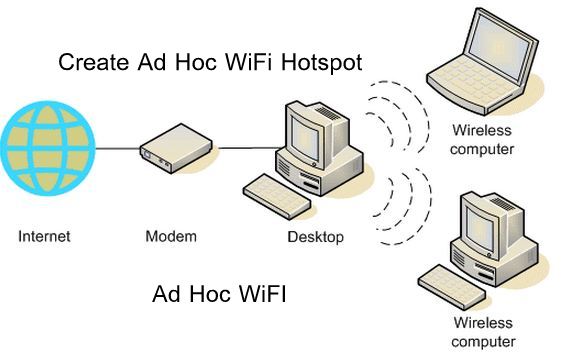
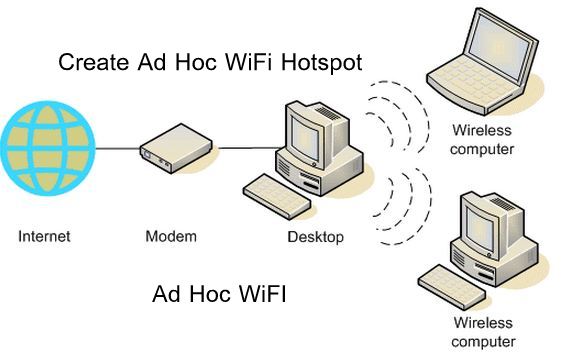 172How To
172How ToHow to Connect to Ad Hoc WiFi Network in Windows 8.1
Having Windows 8.1 and then connecting to a wireless network, sometimes it may create some problems. Well I use Ubuntu most of...
-

 282News
282NewsTOP 100 Unique sites
These sites solve at least one problem really well and they all have simple web addresses(URLs) that you can easily memorize thus...
-

 235IOS Hacking
235IOS HackingHow to Check If A Used iPhone Is Stolen
Apple attempted to address this issue with the Find My iPhone service in 2010, but that could be defeated by turning the...
-

 327Cyber Events
327Cyber EventsAnonymous Hacks and Removes X-Rated Animal Abuse Websites
Anonymous hackers have started a new operation under the banner of #OpNullDenmark and #OpBEAST. The purpose of this operation is to raise awareness...
-

 125Cyber Events
125Cyber EventsU.S Military to hire civilian cybersecurity specialists
If you are a cybersecurity specialist then U.S Military is ready to hire you. Lt. Gen Cordon announced that U.S Military is planning...
-

 205News
205NewsPro-Israeli Jewish Press Website Hacked by ‘Gaza Team’ Hackers
Gaza Team, a Palestinian-friendly group of hackers, hacked The Jewish Press — The site displayed a black backdrop with a man holding...
-

 215Secure Coding
215Secure CodingReveal Asterix Symbols with Javascript
How to do it 1) Open the Login Page of any website. E.g http://www.gmail.com 2) Type your ‘Username’ and ‘Password’. (DONT CLICK...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




